In today's world, everything is connected, and cybercrime is a big problem. So, it's super important to understand and deal with threats from the dark web. Monitoring the dark web is a key way to keep your personal and business info safe from the wrong people. By checking out what's happening on the dark web, you can defend yourself against bad stuff.
The dark web is like a hidden part of the internet that regular search engines can't find. It's a place where people can stay anonymous, which makes it attractive for bad activities. Stolen information, like passwords and personal details, is often traded there, and cyberattacks are even planned on it. Dark web monitoring is like an early warning, so you can act fast and fix any damage before criminals use your information.
What Is Dark Web Monitoring?
p>Dark web monitoring is a way to look for your info on the dark web. Think of it as a search engine that goes into the hidden parts of the internet, like secret websites and forums, where stolen data is sold or discussed. The goal is to find out if your important info, like passwords or bank details, has been stolen and is available there.This is a way to get ahead of cyber threats and data leaks. Unlike security tools that try to stop attacks from happening, dark web monitoring helps you deal with what happens after a leak. By constantly looking for mentions of your company or personal info, these tools can find any exposed data.
It’s not just about personal data. For companies, it means protecting things like email addresses, company secrets, and important documents. By watching out for these things, businesses can understand the threats they face and take steps to protect themselves and their reputation.
Key Aspects of Dark Web Monitoring
One important thing about dark web monitoring is that it looks for all kinds of stolen data. This includes usernames, passwords, personal info like addresses and Social Security numbers, bank details, security question answers, health info, and even login details for services you subscribe to. Criminals often use this data for things like stealing identities, fraud, or getting into computer networks without permission.
Another key aspect is that it's always watching in real-time. Dark web monitoring uses special tools and automated systems to scan the dark web every day. This way, when your info shows up, you get an alert right away. This quick notice is super important to stop criminals from using your stolen information.
Also, dark web monitoring does more than just find stolen data. It also tries to understand the threats and what they mean. Security teams can learn about new dangers, how attacks might happen, and what criminals are doing. Some services even have people who go into secret forums or figure out coded messages to better understand the threats and make sure the information is real.
Why Is Dark Web Monitoring Important?
Dark web monitoring is very important today because it warns you about possible cyberattacks and data leaks. Often, stolen passwords, important data, or even plans for attacks are talked about or sold on the dark web before they're used against you. If you don't monitor the dark web, you might not know about these problems until an attack happens, which can cause a lot more damage.
Plus, many people reuse the same passwords on different sites, which makes dark web monitoring even more important. If a password from one site is leaked, criminals can use it to try to get into other important systems. By finding these leaked passwords early, you can take action, like changing passwords, to prevent criminals from taking over accounts.
Besides preventing attacks, dark web monitoring also helps protect your reputation and follow the rules. Data leaks can make customers lose trust in you, give you a bad image, and lead to big fines. By watching the dark web, you can show that you're serious about security, fix leaks quickly, and keep your customers happy. This helps you avoid the money, legal trouble, and bad reputation that can come with a data leak.
How Does Dark Web Monitoring Work?
Dark web monitoring usually works in a few steps using special tools and sometimes human experts. First, it involves constant scanning and collecting data. Dark web monitoring systems use automated tools to search the hidden parts of the internet. These tools look for certain words or phrases related to your company or personal info, like domain names, employee emails, or brand names.
If they find something that might be a problem, the next step is to figure out what it is. The collected data is analyzed using computer programs. These programs help find real threats, understand what they mean, and avoid false alarms. For example, they can tell if a password is real and recent or if a discussion about your company's problems is serious. Human experts might also be involved, especially to get into secret forums or understand coded messages from criminals.
The most important step is to send alerts and fix the problem. If a real data leak or threat is found, the dark web monitoring system sends alerts to the right people. These alerts usually include details about what data was stolen, where it was found, and how dangerous it is. This lets you take quick action, like changing passwords or contacting the police. Because the monitoring is constant, you can stay ahead of criminals and fix problems before they cause major damage.
Types of Dark Web Monitoring
Dark web monitoring can be grouped by what it covers, how deep it goes, and who it's for. One type is personal dark web monitoring, which protects individuals. This means looking for things like email addresses, phone numbers, Social Security numbers, and credit card details that might have been stolen in data leaks. If your data shows up on the dark web, these services will warn you so you can take steps like freezing your credit or changing passwords.
Another type is for companies or organizations. This goes beyond personal data and protects the company's digital info. It involves watching for leaked company passwords, business secrets, important documents, customer info, and discussions about the company's problems or upcoming attacks. These systems often work with existing security tools and provide reports to help understand threats. This is important for keeping the business running, protecting its reputation, and following the rules.
Also, dark web monitoring can be divided by how it works: automated and human-driven. Automated monitoring uses computer programs to scan lots of dark web data. While it's fast, it might miss some more complex threats. Human-driven monitoring involves security experts who go into dark web communities to understand coded messages and get exclusive information. The best dark web monitoring often uses both methods to provide full coverage and find threats accurately.
Components of Dark Web Monitoring
Good dark web monitoring systems are made of different parts that work together to give a full picture of threats. The first part is collecting data. This involves special tools that can get into the hidden parts of the dark web, like secret websites, forums, and chat rooms. These tools are designed to collect lots of data, like text, leaked databases, images, and documents.
After collecting data, the next step is to analyze it. The data is often messy and might contain false alarms. This is where computer programs come. These programs process the data to find patterns, pick out important info (like email addresses or company names), and connect the dots to find real threats. Human experts also help by checking the findings and understanding complicated messages that computers might miss. This step turns the raw data into useful info about threats.
Finally, it's important to send alerts and let people take action. When a real threat is found, the system needs to send alerts to the right people. These alerts can be customized and sent through different ways, like email.
Reports help organizations understand the scope of the problem and see trends. Also, many systems help users fix the problem, like resetting passwords, ensuring a quick response to threats.
Benefits of Dark Web Monitoring
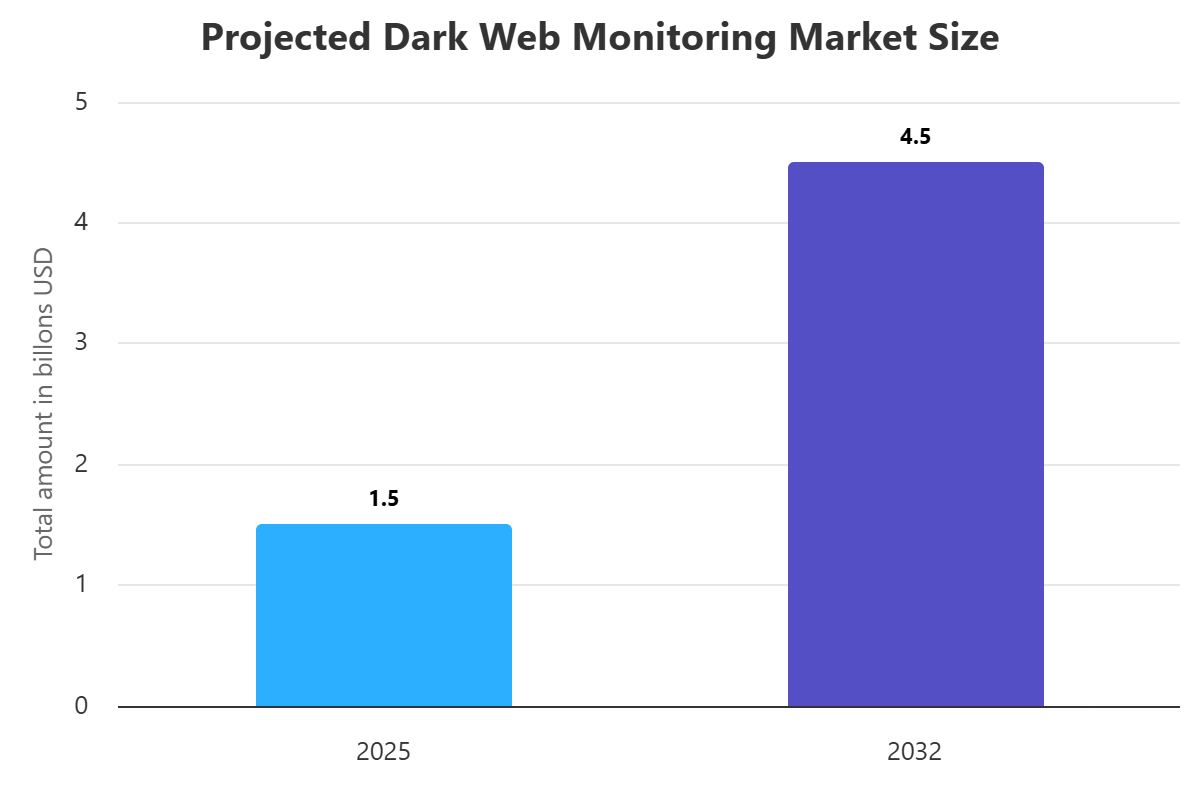
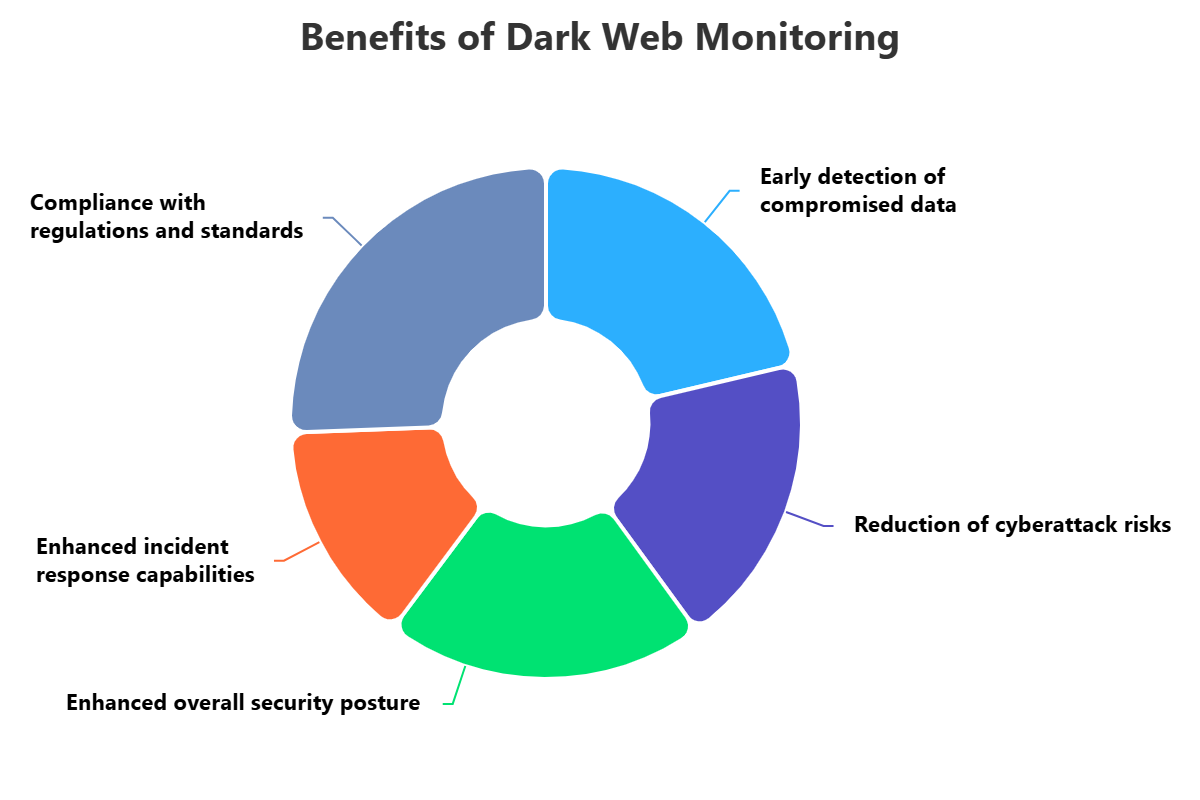
There are many benefits to using dark web monitoring for individuals and companies. The biggest one is finding stolen data and threats early. By watching the hidden parts of the internet, you can find leaked passwords or discussions about attacks before they're used against you. This gives you time to change passwords or take steps to protect your systems, reducing the damage from a leak.
It also lowers the risk of cyberattacks and financial losses. Stolen data from the dark web is used for things like ransomware attacks and identity theft. By finding this data, you can take security measures to make it harder for criminals to succeed. This helps you avoid the costs of data leaks, like fines or damage to your reputation. Taking action early is cheaper than dealing with the aftermath.
Plus, dark web monitoring makes your security stronger. The info you get from the dark web can show you where your weaknesses are and help you improve your security plans. When a leak is found, you can respond faster and better. By showing that you're working to protect data and find leaks, you can also follow the rules and keep your customers' trust.
Challenges of Dark Web Monitoring
Challenges of Dark Web Monitoring
Even though it's helpful, dark web monitoring has its challenges. One problem is that the dark web is always changing. New sites appear and disappear often. Many forums are private or require special access, making it hard for tools to get in. Also, criminals use slang or codes to talk about their activities, which can make it hard to understand the threats.
Another challenge is the amount of data. There's so much info on the dark web, and much of it is useless. Finding the important stuff takes skill and resources. It can also be hard to know if sources are telling the truth, which makes it harder to judge the risk.
Finally, there are legal and ethical questions. Going into certain dark web sites or talking to criminals, even to gather info, can be tricky. You need to make sure your monitoring follows the rules, especially about data privacy. Also, dark web monitoring can only find data that's already been stolen. It can't stop the initial leak. That means you need a complete security plan that prevents data from reaching the dark web in the first place.
Best Practices for Dark Web Monitoring
To get the most out of dark web monitoring, here are some tips. First, know what you're trying to protect. Before using any tools, know what data is most important to your company or personal security. This could be email addresses, employee names, or financial info. Knowing what to look for helps you focus your efforts and avoid wasting time on irrelevant alerts.
Second, choose the right tools and use them with your existing security systems. There are different dark web monitoring tools available. Pick one that fits your needs and budget. Make sure it works well with your current security tools, like systems that manage security info. This lets you see the whole picture of your threats and respond faster.
Finally, have a plan for when you find a problem and keep improving your monitoring. Finding a leak is only the first step. You need to know what to do next. Have clear steps for checking alerts and fixing problems, like changing passwords. Also, the dark web changes all the time, so adjust your monitoring strategy regularly based on new threats and changes in your company's info.
How ImmuniWeb Can Help with Dark Web Monitoring?
ImmuniWeb offers a comprehensive Dark Web Monitoring solution as part of its AI Platform, designed to provide organizations with proactive intelligence on emerging cyber threats and silent data breaches. ImmuniWeb's approach to dark web monitoring is distinguished by its ability to crawl millions of new files and entries on the dark web daily, ensuring rapid detection of data leaks and exposed credentials impacting an organization or its trusted third-parties. This continuous scanning helps businesses stay ahead of cybercriminals by uncovering data that would otherwise remain invisible and unknown, giving them a critical advantage in incident response.
The ImmuniWeb Dark Web Monitoring solution is specifically tailored for enterprises, going beyond basic individual monitoring. It continuously analyzes gigabytes of data to detect mentions of an organization's digital assets that have been compromised, contain known vulnerabilities, or have attracted the attention of motivated threat actors. This includes not only logins and passwords of employees but also private messages, corporate documents, financial details, intellectual property, and even instances of brand impersonation, such as cybersquatted domains or malicious mobile apps usurping a corporate brand. ImmuniWeb's solution is designed to shine a light on data available for sale by threat actors on underground marketplaces, providing actionable insights into potential fraud, Business Email Compromise (BEC) attacks, and Intellectual Property infringements.
Furthermore, ImmuniWeb's Dark Web Monitoring is deeply integrated with its broader Cyber Threat Intelligence and Attack Surface Management platform. This allows for the automatic detection of all mentions of an organization's IT systems, domain names, servers, cloud instances, applications, or users on the dark web, without the need for manual input. The platform provides real-time alerts when sensitive data is detected, enabling immediate action to mitigate risks. Users benefit from a user-friendly, interactive, and customizable dashboard to browse risk-based security incidents, with options to export findings or synchronize data with existing SIEM systems via API. ImmuniWeb also offers a fixed monthly price per company, regardless of the volume of security incidents or leaks, coupled with the support of their security analysts for additional details or assistance, making it a robust and predictable solution for dark web vigilance.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











