A Comprehensive Guide to Mobile Application Security Testing (MAST)
Mobile Application Security Testing (MAST) is a specialized security process that combines static analysis, dynamic analysis, and behavioral testing to identify and remediate vulnerabilities unique to mobile apps, addressing risks from insecure data storage, third-party libraries, and the inherent threats of the mobile environment.

Mobile devices are everywhere now, and they've really changed how we do things – from work to how we use services. Phone apps deal with a lot of personal and money info, like when we bank, see a doctor, use social media, or shop. Because they're so important, criminals really want to get to them.
That's where Mobile Application Security Testing (MAST) comes in. It's all about finding and fixing security problems in apps before those criminals can cause harm. MAST uses different tools and ways to keep user info and companies safe.
How MAST Works
Mobile app security testing, or MAST, uses a few ways to get the job done: static, dynamic, and behavior checks all together.
It usually starts with Static Application Security Testing, called SAST. This means looking at the app's code without running it. For mobile apps, they check the code (like Kotlin for Android or Swift for iOS) or the app files (APK for Android, IPA for iOS). This helps find coding mistakes, insecure ways of using APIs, and breaking security rules. SAST is really good at spotting things like passwords written directly in the code, bad encryption, and weak spots in the code early when the app is being made.
The next key is Dynamic Application Security Testing, known as DAST. This checks the app while it’s running. MAST tools run the app on a device or a fake device and test it automatically or by hand, acting like attackers. They test the app’s parts, like the user interface and any online APIs, to find problems that happen while the app is running. These could include sending data insecurely (not using SSL pinning), handling sessions poorly, and showing sensitive data in logs. DAST gives a practical idea of how the app acts and protects data when it’s being used.
A special piece of MAST is checking how the app behaves, or Runtime Application Self-Protection (RASP). This watches the app while it’s running to catch bad activity. This can involve looking for common threats like checking if the device is rooted or jailbroken, seeing how the app interacts with other apps (like through intents or custom URL schemes), and finding any tries to steal data. MAST also has Software Composition Analysis (SCA), which scans the app's add-ons such as third-party libraries and SDKs, for known problems. Since a lot of an app’s code comes from these outside parts, SCA is super important for keeping track of supply chain risks.
Key Characteristics of MAST
MAST is defined by several core characteristics that distinguish it from traditional application security testing. First is its platform-specific focus. A robust MAST solution must account for the distinct security models, programming languages, and operating system APIs of both Android and iOS. For example, testing an Android app involves analyzing permissions, intents, and the security of activities and services, while iOS testing focuses on plist configurations, Keychain security, and IPC mechanisms. A one-size-fits-all approach is ineffective in the fragmented mobile landscape.
Another fundamental characteristic is its emphasis on the client-side environment. Unlike web applications that rely on server-side security, mobile apps are distributed to and run on untrusted devices. Therefore, MAST must rigorously assess the app's resilience against client-side threats, including insecure data storage (on the device's file system, databases, or SharedPreferences/Keychain), reverse engineering, and code tampering. MAST tools often include capabilities to assess the app's resistance to decompilation and obfuscation techniques.
Furthermore, MAST is inherently comprehensive and integrated, combining multiple testing methodologies (SAST, DAST, SCA, Behavioral) into a unified process. This is essential because mobile app vulnerabilities often span the client, the network, and the server-side API. A MAST solution provides a holistic view of this entire attack surface. Finally, MAST is characterized by its focus on compliance and privacy regulations. With regulations like GDPR, CCPA, and the PCI DSS for mobile, MAST tools are designed to automatically check for compliance with data protection rules, such as unauthorized data collection or transmission of personal information to third-party analytics servers.
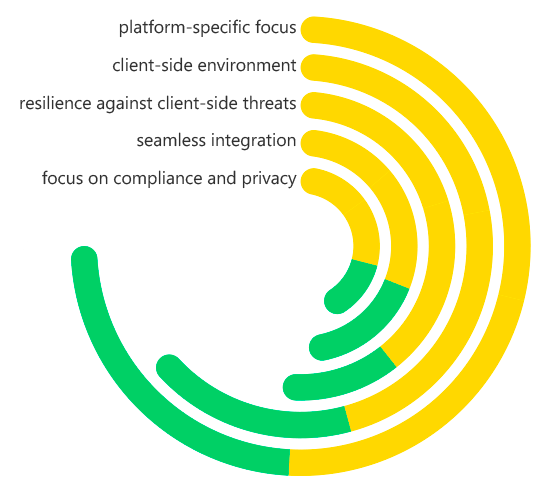
Mobile Application Security Testing (MAST) Key Characteristics
What Problems Does MAST Solve?
MAST tackles some big mobile issues. One major thing is that sensitive info ends up on devices we might not trust. Phones and tablets get lost or stolen all the time and can be used on unsafe networks. MAST fixes data storage and sending problems by spotting where an app doesn't keep stuff safe while it's sitting still or moving around, which stops big data leaks.
Another thing is that many apps have problems because of outside parts. Mobile apps use things like open-source libraries and SDKs for ads or social media. These can have weaknesses or bad code. MAST uses Software Composition Analysis to show you what's in those parts, so companies can find and fix the weak things before the app goes live.
MAST also takes care of the problem of following rules and avoiding legal issues. A lot of companies have trouble showing that their apps follow data privacy laws. MAST can automatically find privacy problems, like an app looking at your contacts without asking or sending data without encryption. This can help companies avoid big fines and harm to their image. Last, it works on keeping apps safe from tampering. MAST tools check how well an app can stop hackers from reverse engineering it and messing with it. Hackers often do these things to steal software, skip license checks, or put in malware.
Benefits of MAST
The implementation of a robust MAST program yields significant and tangible benefits for any organization developing mobile applications. The most prominent advantage is the proactive protection of user data and brand reputation. By identifying and fixing security flaws before public release, organizations can prevent data breaches that lead to financial loss, regulatory penalties, and irreversible damage to customer trust. A secure app is a competitive differentiator in a market increasingly concerned with privacy.
From a business and operational perspective, MAST offers cost savings and accelerated time-to-market. Finding and remediating vulnerabilities during development is exponentially cheaper than dealing with a security incident post-release, which may involve emergency patching, app store re-submissions, customer notifications, and legal fees. Moreover, integrating MAST into the CI/CD pipeline (DevSecOps) ensures security is baked in, not bolted on, preventing last-minute delays and enabling faster, more secure release cycles.
Another key benefit is enhanced compliance posture. MAST tools provide automated reporting and evidence collection for various regulatory frameworks, significantly reducing the manual effort required for compliance audits. This ensures that applications are not only secure but also adhere to legal and industry standards from the outset. Finally, MAST provides a holistic security assurance that covers the entire mobile attack surface—from the client app and its data storage to its communication with backend APIs—giving organizations confidence that their mobile channel is resilient against modern threats.
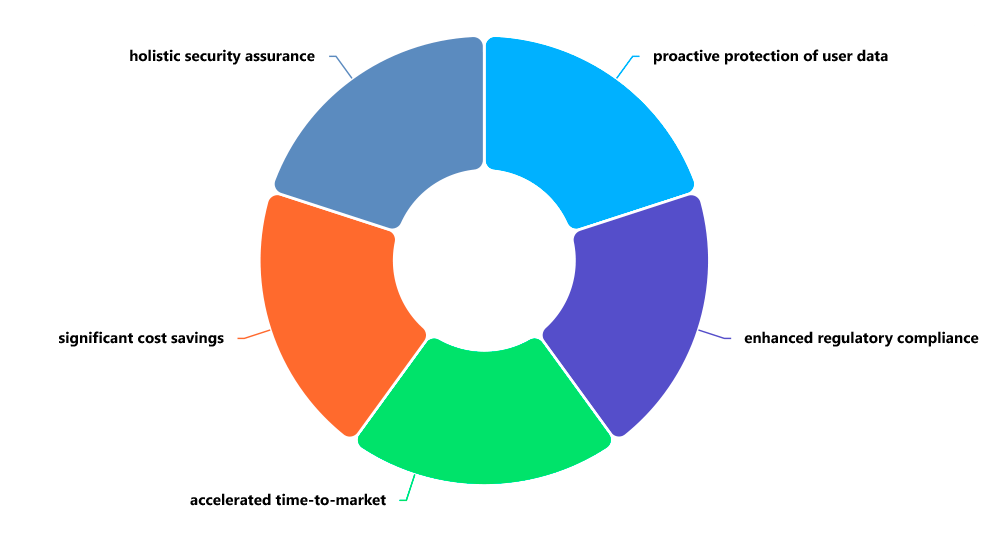
Mobile Application Security Testing (MAST) Benefits
How Is MAST Different from Web AST?
Mobile app security testing (MAST) and web app security testing both try to make sure software is secure, but they're pretty different because of their platforms.
Web apps sit on servers, and the browser doesn't keep much info. Security testing here looks checks server-side code and things. Mobile apps, are installed on different devices. So, MAST has to watch out for the client-side code, where data is stored, and how the app uses the device's features and other apps.
The dangers are also different. Some mobile threats aren't a problem for web apps:
- Jailbreaking/Rooting: Getting around the device's security.
- Insecure Data Storage: Problems with how data is saved on the device.
- Reverse Engineering: Taking apart an app to steal stuff or find weaknesses.
- Malicious Apps: A bad app tries to mess with another app on the same device.
MAST tools are made to test for these mobile-only problems.
Also, how network communication is tested is different. Web testing usually assumes a normal web connection. MAST needs to check security things, like Certificate Pinning. Mobile apps use this to stop Man-in-the-Middle attacks only by trusting a specific certificate or public key. Checking certificate pinning is important for MAST, but not for web apps in general.
Why Is MAST Vital to Application Security?
Mobile app security testing (MAST) is super important because phones and tablets are easy targets for attacks. People keep a lot of private stuff on their phones, and they're always online, which makes them attractive to hackers. If you don't pay attention to mobile security, your whole company is at risk. A hacked app can give attackers access to company info, passwords, and even your entire network.
App stores like Google Play and Apple's App Store have strict rules about security and privacy. If your app doesn't meet their standards, it won't get approved, which can be bad for your reputation and cause delays. A good MAST program makes sure your apps are ready for the app store, so you don't have any issues when you submit them.
Basically, MAST is a must if you care about security. It helps you deal with the specific risks of mobile apps. Since more and more companies are focusing on mobile, it's essential to develop, test, and release secure apps. This protects your customers, your brand, and keeps you ahead of the competition.
Real-World Examples of How MAST Is Used
MAST is applied in various practical scenarios throughout the mobile app development lifecycle. A common use case is in CI/CD Pipelines for Mobile DevSecOps. A financial institution, for example, can integrate MAST tools into their Jenkins or GitLab CI pipeline. Every time a developer commits code for their banking app, the pipeline automatically builds the APK and IPA files, and the MAST tool executes a SAST and SCA scan. If a critical vulnerability, such as a hardcoded API key or a vulnerable version of OkHttp library is found, the pipeline fails, preventing the vulnerable build from progressing and notifying the developer instantly.
Another powerful example is during the Pre-Release Security Audit. Before a retail company submits a new version of its e-commerce app to the app stores, its security team conducts a comprehensive assessment. They use a MAST tool to perform dynamic analysis, running the app on a jailbroken and a non-jailbroken device to test its resilience. The tool automatically probes the app's login and payment flows, checks for sensitive data in the file system, and validates that all communications use strong TLS with proper certificate pinning, ensuring the app is robust before it reaches millions of users.
MAST is also critical for Remediating Privacy Violations and Compliance Gaps. A health and fitness app collecting user data must comply with GDPR and HIPAA. A MAST tool can be used to perform behavioral analysis by monitoring all network traffic generated by the app during use. It can discover that the app is transmitting precise GPS location data to a third-party advertising network without proper anonymization or user consent—a clear compliance violation. The development team uses this specific finding to reconfigure the SDK and implement proper data anonymization, thus avoiding potential regulatory fines.
How ImmuniWeb Helps with MAST
ImmuniWeb provides a robust, AI-powered platform that seamlessly integrates comprehensive Mobile Application Security Testing into an organization's security posture. Leveraging a combination of advanced SAST, DAST, and SCA, ImmuniWeb delivers deep, accurate security testing tailored to the nuances of both Android and iOS applications. Its platform is designed to identify the complex vulnerabilities that plague mobile apps, from insecure data storage and broken cryptography to vulnerabilities in third-party components and API integrations.
A key strength of ImmuniWeb is its holistic and continuous approach to mobile security. It doesn't treat the mobile app as an isolated entity but assesses it as part of a larger system, including its communication with backend APIs and cloud services. This end-to-end visibility is crucial, as a vulnerability in the backend API can compromise an otherwise secure mobile client. Furthermore, ImmuniWeb’s platform is built for automation, enabling organizations to integrate mobile security testing directly into their CI/CD pipelines. This facilitates a true DevSecOps model, where security is a continuous process, not a point-in-time audit.
ImmuniWeb enhances its MAST offering with actionable intelligence and compliance mapping. The platform provides detailed, prioritized reports that not only list vulnerabilities but also offer clear, developer-friendly remediation guidance. It automatically maps findings to major regulatory and industry standards like OWASP MASVS (Mobile Application Security Verification Standard), GDPR, and PCI DSS, helping organizations demonstrate compliance efficiently. By offering a unified, intelligent, and scalable platform for mobile security, ImmuniWeb empowers organizations to build and maintain secure mobile applications that protect users, preserve trust, and meet the highest standards of security and privacy.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










