What Is Attack Surface Management?
These days, things are complex online, and it's harder than ever to nail down the edge of a company's IT stuff. It's not a clear line anymore, but a huge area that keeps getting bigger. This attack surface is basically every possible way a bad guy could try to hack into a company's computers, networks, apps, or steal data. It's everything from web servers to employee laptops, and even those sneaky shadow IT things – apps and devices people are using without permission. As companies go more digital, this attack surface grows too, opening up new chances for hackers.
Attack Surface Management (ASM) is like a constant, forward-thinking way to handle this. It's more than just checking for weaknesses. It's about finding, figuring out, and fixing all the possible ways someone could break in, and keeping an eye on them all the time. ASM wants to give companies a view of their whole digital thing from a hacker's point of view so they can see the risks and fix them before anything bad happens. It's about getting ready for problems instead of just reacting to them after they happen.
By mapping things out and checking on them, ASM helps companies really see where they're at risk. This means they can make smarter choices and put their security money where it matters most to guard their important stuff and data from the ever-changing threats out there.
What's Important About Attack Surface Management?
There are a few things that make Attack Surface Management stand out from regular security stuff and make it super important now. First off, it keeps finding and watching. Unlike checking every once in a while, ASM always scans inside networks to spot new or changed things, systems people forgot about, and even fake-looking domain names. This means that as a company's online stuff changes, its security stays up-to-date.
Also, ASM thinks like a hacker. Instead of just looking at how things are set up inside, ASM tools try to see a company's online stuff like a bad guy would. This means finding open connections, cloud services that aren't set up right, or weak apps that are easy to get online. Seeing things from the outside is key because hackers often go for weaknesses they can see from the internet, no matter how good the internal security is. Knowing what a hacker can see helps companies block those entry points ahead of time.
Lastly, ASM is all about fixing the important stuff first. It's not enough to just find weaknesses. You have to see how bad they could be and how likely they are to be used. ASM helps companies rank the risks so they can fix the worst ones first – the ones that are easy to use and could cause big problems. Fixing things before they're used, instead of just reacting to a break-in, is how you lower your overall risk and make your security stronger. All these things help companies keep their security strong in a digital world that's always changing.
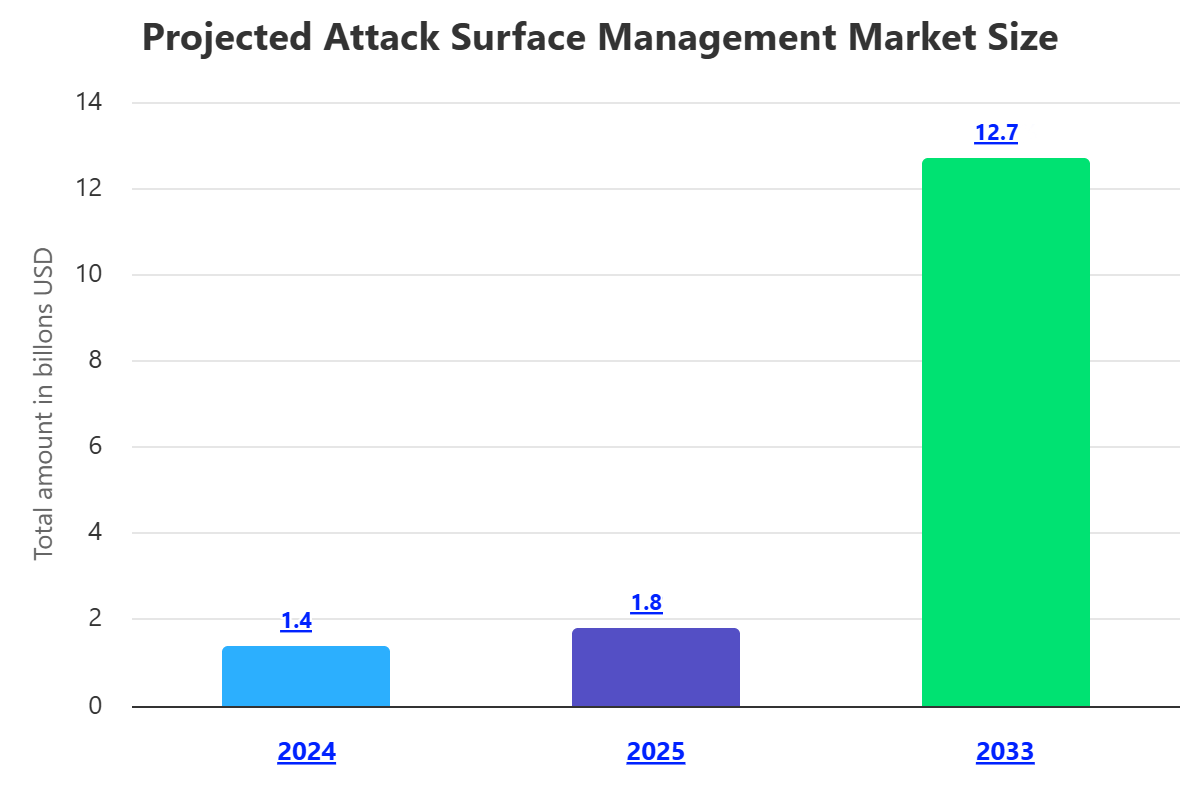
Why Attack Surface Management Is a Big Deal?
Attack Surface Management has gotten way more important because of how fast digital stuff is changing and how hackers are getting better. One big reason it matters is that companies have so much stuff online now. Using cloud computing, apps you rent, letting people work from anywhere, and more and more internet-connected devices has made the old network borders disappear. Now there are tons of different ways for a hacker to get in, so companies have to know what all their exposed things are.
Also, shadow IT makes the risk way bigger without companies even knowing it. This is when employees use devices, apps, and cloud services that the IT department doesn't know about or approve. Shadow IT often skips the usual security checks, making it an easy target for hackers. ASM helps find these hidden things and put them under the right security rules so you can close the security holes that might go unnoticed until there's a break-in.
Lastly, hackers keep coming up with new tricks, and there are more and more rules about keeping data safe, so ASM is super important. Hackers always find new ways to attack, use new weaknesses, and trick people into letting them in. Without a way to always see your whole attack surface, you're just reacting and always behind. Plus, rules like GDPR, HIPAA, and PCI DSS say you have to manage risks and protect data. ASM helps you follow these rules by finding and fixing security problems, protecting data, and showing that you're trying to manage digital risks. This protects not just your stuff, but your reputation and money, too.
How Attack Surface Management Works?
Attack Surface Management works by constantly going through the same steps to get a good, up-to-date view of a company's weak spots online. The first step is finding and listing everything. This means carefully scanning a company's whole digital world, both inside and out, to find everything that's active or not active. This is more than just finding the usual servers and apps. It's also looking for shadow IT (unapproved devices, cloud stuff, or apps), old systems that are still online, connections to other companies, and even fake domain names that look like the company's (used for phishing). Both quiet ways (like using web searches and checking domain records) and active ways (like scanning for open connections) are used to make a full, always-changing list.
Once you know what you have, the next step is checking for weaknesses and risks. This is when you look closely at everything you found to see where there might be problems, like things not set up right or known weaknesses. This means checking apps for common flaws like SQL injection or cross-site scripting (XSS), checking cloud settings against security rules, finding old software, open connections, weak passwords, and exposed data. This check often uses information about known threats and weaknesses to see how a hacker might use a problem they found. The result is a list of possible risks for each thing.
The last steps are deciding what to fix first, fixing it, and watching constantly. Since you can find a lot of weaknesses, ASM needs a good way to decide what's most important. Risks are ranked by how bad they could be, how easy they are to use, and what effect they could have on the business (like losing data, money, or reputation). This lets security teams fix the biggest problems first. Then, they take action to fix the problems, like installing security updates, fixing settings, getting rid of things that aren't needed, or making passwords stronger. ASM isn't a one-time thing. It's always watching because the digital world changes all the time. New things go online, settings change, and new weaknesses appear every day. Watching constantly keeps the attack surface map accurate and lets you quickly spot and fix new problems as they appear so you can stay secure.
Different Types of Attack Surface Management
While the main ideas of Attack Surface Management are the same, it can be used in different ways to focus on different parts of a company's online stuff. One common type is External Attack Surface Management (EASM). EASM looks at things that are online and can be reached from outside the company's network. This includes websites, apps, cloud stuff, connections, domain names, IP addresses, databases that are online, code, and email servers. EASM tools show how a company looks to an attacker and help find weaknesses that can be seen and used from the internet. This is super important for protecting a company's online presence and stopping hackers from breaking in through things that are exposed to the public.
Another important type is Internal Attack Surface Management (IASM). Instead of looking outside, IASM looks at weaknesses and possible attack paths inside the company's network. This includes internal apps, employee computers, servers, network devices (like routers and switches), internet-connected devices inside, and data that's stored inside. Even though these things aren't directly online, they can be used if a hacker gets inside, usually by tricking someone or using a weakness from outside. IASM helps secure the side-to-side movement of an attack, making it harder for a hacker to move around and break into more internal systems even if they get in at first.
Also, there are special kinds of ASM that focus on certain digital areas. Digital Supply Chain Attack Surface Management looks at the risks that come from other companies that you work with, like suppliers and software companies. This includes checking the security of connections they provide, open-source software that's used in apps, and cloud services that are managed by other companies. Weaknesses in these outside things can directly affect your company's security. Similarly, Cloud Attack Surface Management focuses on finding and managing cloud-specific risks, like cloud storage that's not set up right or weaknesses in virtual machines that run on cloud platforms. These special approaches let companies customize their ASM efforts to the specific things and risks in different parts of their complex digital world.
Components of Attack Surface Management
Good Attack Surface Management uses a mix of different tools, technologies, and methods that all work together. The main part of any good ASM system is automated tools for finding assets. These tools actively and quietly scan a company's digital stuff across different places. Active scanning might mean checking for open connections, mapping out the network, and checking for weaknesses to find live systems and services. Quiet finding means using online information (like domain records and certificates) and watching social media and the dark web to find things that were forgotten, shadow IT, or even fake domain names. These tools provide the basic, always-updated list of digital assets.
Besides finding things, checking for weaknesses with tools and human testers is important. While finding tools list assets, these checks deeply analyze them for specific weaknesses. This includes automated scanners that check for common software flaws, misconfigurations, and known problems. Also, having skilled ethical hackers test things can find complex flaws that automated tools might miss. These tests provide a detailed security check of each asset, showing specific weaknesses that hackers could use.
Finally, a complete ASM plan uses ways to decide what risks are most important and tools to automate security tasks and responses. With potentially thousands of weaknesses, ASM needs ways to focus on the most important ones based on how bad they could be, how easy they are to use, and how they could affect the business. Automation tools then tie everything together by automating tasks, connecting to existing security tools, and helping quickly respond to new threats or weaknesses. Combining this with always getting new threat information helps make a complete system for managing a company's attack surface and preparing for new attacks.
What Are the Benefits of Attack Surface Management?
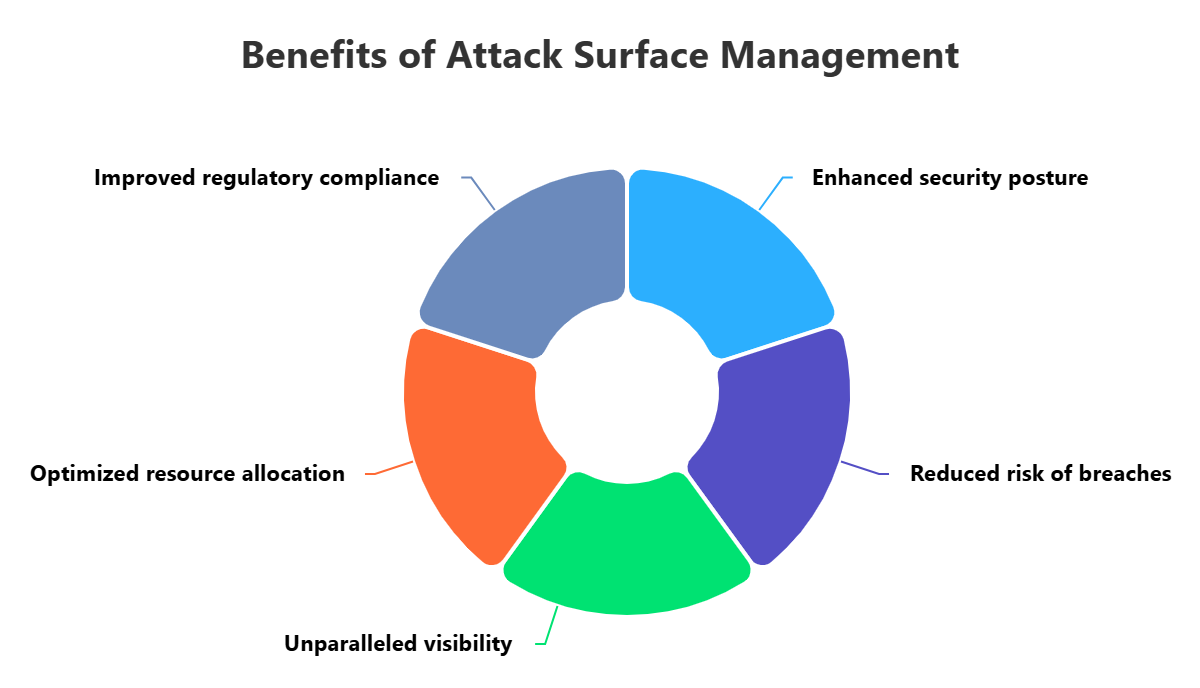
Having a good Attack Surface Management program gives a lot of big benefits that are super important for making a company's security stronger against the rising number of sophisticated threats. First of all, ASM makes security a lot better and lowers the risk of break-ins. By always finding and fixing weaknesses across the whole digital footprint, including the ones that are often missed, companies can stop hackers from getting in. This lowers the chances of successful attacks, data breaches, and unauthorized access, protecting important information and systems. Being ready for attacks means fixing problems before they can be used, turning security from a reactive thing into a preventative defense.
Also, ASM shows everything that's out there and helps fight shadow IT. One of the ongoing problems for big companies is that there are unauthorized or forgotten assets that are outside the view of IT and security teams. These shadow IT things often don't have the right security, making them easy targets. ASM's finding tools are specifically made to uncover these hidden assets, bringing them to light so security teams can check the risks and manage them properly. This complete view makes sure that no part of the digital world is unmonitored or unprotected, closing the security holes that could lead to big problems.
Lastly, ASM helps use resources better and follows regulations. By ranking weaknesses based on how bad they are, how easy they are to use, and how they could affect the business, ASM lets security teams focus on the most important risks first. This makes sure that the most dangerous threats are fixed quickly, making security investments work better. Also, since there are more and more rules (like GDPR, HIPAA, or PCI DSS) that say companies have to protect data, ASM gives a system for finding and fixing security problems. This not only helps meet the rules but also shows that the company is committed to security, protecting its reputation and avoiding fines.
Challenges of Attack Surface Management
Even though Attack Surface Management has a lot of benefits, putting it in place and keeping it working can be tricky and requires careful planning. One of the main problems is managing how quickly things change in IT. Companies keep using new cloud services, putting in new apps, updating things, and working with other companies. Each change can bring new assets, change settings, or create new ways for hackers to attack. Keeping a list of this always-changing digital stuff is a huge task, making it hard to have a complete view of the attack surface.
Another big problem is the amount of information and the chance of missing real threats because of too many alerts or false alarms. ASM tools create a lot of information about assets, weaknesses, and risks. Looking through all this data to find real threats among the unimportant things or false alarms can be overwhelming for security teams. This can make them miss real threats because they're tired of all the alerts or waste time checking things that aren't really problems. Effectively ranking and understanding this data requires good analysis and often, human experts, which can be hard to find.
Finally, connecting different systems and not having enough resources can be a problem. Putting in a complete ASM program often means connecting to different tools across different security areas, like weakness scanners, cloud security tools, threat information, and systems for responding to break-ins. Making sure data flows smoothly between these different systems can be technically hard and take a lot of time. Also, many companies, especially small ones, might not have the staff, knowledge, or money to put in place, manage, and keep running a complex ASM program. Getting over these problems requires careful planning, investing wisely, and always trying to improve.
Best Practices of Attack Surface Management
To get the most out of an Attack Surface Management program and really make a company's security stronger, it's important to follow some key practices. First, always be thinking about and working on ASM. This isn't a one-time project. The digital world is always changing, so the way you manage weaknesses has to change too. Using automated tools to always find assets and check for weaknesses makes sure that as new systems go online, settings change, or new threats appear, they're quickly found and added to the ASM process. This is the key to being ready for attacks and not being caught off guard.
Also, deciding what risks are most important is key for using resources well. Instead of just finding flaws, try to understand how they could really affect things and how likely they are to be used. Using ways to rank risks, getting information about threats, and understanding the business context (like how important the affected asset is) lets security teams focus on the biggest threats that pose the most risk to the company. This makes sure that security resources are used where they'll have the most impact, fixing the critical weaknesses that could lead to big break-ins instead of getting stuck on small issues.
Finally, make security awareness a part of the culture and connect ASM to the rest of the security setup. While technology is important, people are still a big part of the attack surface and can be tricked. Regular security training for employees helps lower the risks from phishing and other attacks that trick people. Also, ASM shouldn't be separate. Its information has to be connected to other security tools like SIEM (Security Information and Event Management), EDR (Endpoint Detection and Response), and systems for responding to break-ins. This creates a complete security view, letting you be quicker to respond and understand a company's security health better. This turns raw data into useful information for always improving.
How ImmuniWeb Can Help with Attack Surface Management
Illuminate your entire external attack surface with ImmuniWeb® Discovery attack surface management just by entering your company name. The non-intrusive and production-safe discovery process will rapidly detect, classify and score the risks of all your external IT assets located both on-premise or in a multi-cloud environment. Find outdated or vulnerable software, expiring domains and SSL certificates, exposed or misconfigured systems, forgotten servers and shadow IT infrastructure including shadow cloud.
Detect leaked source code, container images or system snapshots available in third-party and local repositories. Visualize the geographical areas and countries where your data is physically stored for the compliance and data localization purposes. Moreover, all your IT assets are searched for mentions in the Dark Web to ensure risk-based and threat-aware attack surface management. Setup granular email alerts to your team for any newly discovered IT assets, misconfigurations, vulnerabilities or security incidents. Use groups and tags for fine-grained asset management and triage.
Our attack surface management solution is provided at a fixed monthly price per company regardless of the number of your IT assets, security events or incidents you have. Leverage our API to synchronize the attack surface management data flow directly with your SIEM or other internal systems, or export selected findings into a PDF or XLS file.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











