A Comprehensive Guide to Interactive Application Security Testing (IAST)
IAST is a security testing method that uses agents embedded within a running application to analyze code, data flow, and execution in real-time during automated tests or normal operation to accurately identify and pinpoint vulnerabilities.

In cybersecurity, old-fashioned ways of testing app security often don't cut it. They either give results too late or don't give useful advice.
That's where Interactive Application Security Testing (IAST) comes in. It's a way to test security that mixes static and dynamic analysis to give real-time, spot-on security feedback from inside an app as it runs. IAST is a step up, helping developers find and fix weak spots as they code. It puts security right into how software is made.
How IAST Works
IAST works by putting little agents or sensors right into the app while it's running, like on a web server or in a container. These agents are small and become part of the app's code instead of running on their own. When the app runs – whether it's during tests, QA, or just regular use – the IAST agents keep an eye on everything that's going on: how data moves, interactions, and system calls, all in real-time. They can see everything about how the app is working, including the code, data flow, setup, and connections to the back end.
The cool thing about IAST is what happens while it's watching. When a test runs, like a Selenium script that logs in a user, the IAST agent watches the whole thing. It sees the user's input from the web request, follows it through the app's parts (like the controller, model, and database), and watches how it's handled and sent back in a response. By looking at all this data and comparing it to a list of security rules, the IAST tool can spot specific weaknesses when they happen. For example, if the app takes user input from a login form and uses it directly in a SQL query without cleaning it first, the IAST agent will call out a SQL Injection weakness right away, pointing to the exact line of code where the risky data was used without care.
This inside view lets IAST give very correct results. Unlike a scanner that guesses from the outside, IAST knows for sure if data was checked correctly or if sensitive info was exposed. The analysis is done as the app is running, so it's not just looking at the code (like SAST) or the outside (like DAST). Instead, it watches the app from the inside while it's working. Because of this, there are fewer false alarms, and developers get the info they need to fix problems fast.
Key Characteristics of IAST
IAST is defined by several core characteristics that distinguish it from other application security testing tools. First and foremost is its real-time analysis and feedback. Vulnerabilities are detected and reported the moment they are exercised during testing, often within the CI/CD pipeline itself. This immediacy is crucial for modern DevOps and Agile environments, where speed is paramount, and delays in security feedback can halt a deployment pipeline.
Another fundamental characteristic is its high accuracy and low false-positive rate. Because IAST has access to the complete context of the application—the code, the runtime state, the data flow, and the execution stacks—it can make definitive determinations about the exploitability of a vulnerability. It doesn't just report a potential issue; it confirms that under specific conditions, a malicious payload could successfully compromise the application. This context-aware analysis saves security and development teams countless hours that would otherwise be spent manually validating potential flaws.
Furthermore, IAST is celebrated for its seamless integration into the development workflow. It is designed to work alongside existing unit tests, integration tests, and QA automation suites. Developers and QA engineers do not need to change their behavior significantly; they simply run their existing tests, and the IAST tool passively collects security data in the background. This "shift-left" capability makes security a natural part of the development process rather than a separate, burdensome phase. Finally, IAST provides actionable remediation guidance. It doesn't just say, "There's a SQL Injection vulnerability." It reports, "SQL Injection on line 127 of UserController.java, where the parameter 'username' is used unsafely in the executeQuery method," allowing developers to fix the problem swiftly and effectively.
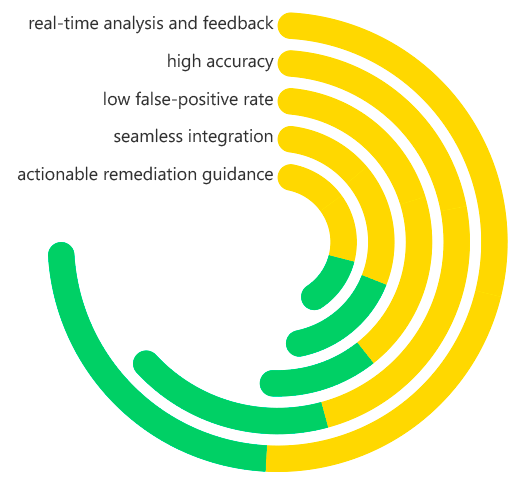
Interactive Application Security Testing (IAST) Key Characteristics
What Problems Does IAST Solve?
IAST helps with some of the big problems in today's application security setups. One big issue is that old SAST and DAST tools create a lot of false alarms. These fake warnings cause people to ignore real problems and waste time. IAST gives you accurate, confirmed vulnerabilities, so security teams can put their energy into actual dangers. This makes the whole AppSec program run better.
Also, IAST fixes the problem of security slowing things down. When you're trying to develop quickly, it can be a pain to wait for a long DAST scan or to sort through a SAST report. IAST gets rid of this wait by giving you instant feedback while you're testing. If there's a vulnerability, it's caught in minutes, not days or weeks. Fixing it is faster, cheaper, and less of a hassle than if it was found later.
IAST also takes care of the issue of limited testing and understanding. DAST tools, which work from the outside, have a tough time with new applications that use a lot of complex, client-side logic. They might miss vulnerabilities that only show up in certain user paths. IAST watches the server-side logic that handles all the data. Because of this, it doesn't matter what the front-end looks like, and it can find vulnerabilities no matter how the front-end is built. It fills in the gaps that other testing methods leave behind.
Benefits of IAST
The operational model of IAST translates into a compelling set of benefits for any organization developing software. The most significant advantage is the dramatic reduction in false positives, which streamlines the remediation process and builds trust between development and security teams. When developers receive clear, accurate, and context-rich vulnerability reports, they are more likely to embrace and act upon them, fostering a more positive and collaborative security culture.
Another major benefit is the acceleration of secure development cycles. By integrating security testing directly into the tools developers already use (their automated tests and CI/CD pipelines), IAST enables a true DevSecOps model. Security becomes a continuous and automated checkpoint, not a gate that impedes release velocity. This allows organizations to achieve both speed and security, a crucial competitive advantage in today's digital landscape.
From a financial and risk perspective, IAST offers significant cost savings. Finding and fixing a vulnerability during development is exponentially cheaper than remediating it after deployment, where costs include emergency patches, potential downtime, security incidents, and reputational damage. Additionally, IAST provides comprehensive coverage for a wide range of vulnerabilities from the OWASP Top 10, including SQL Injection, Cross-Site Scripting (XSS), insecure deserialization, and others, ensuring robust protection for your most critical applications.
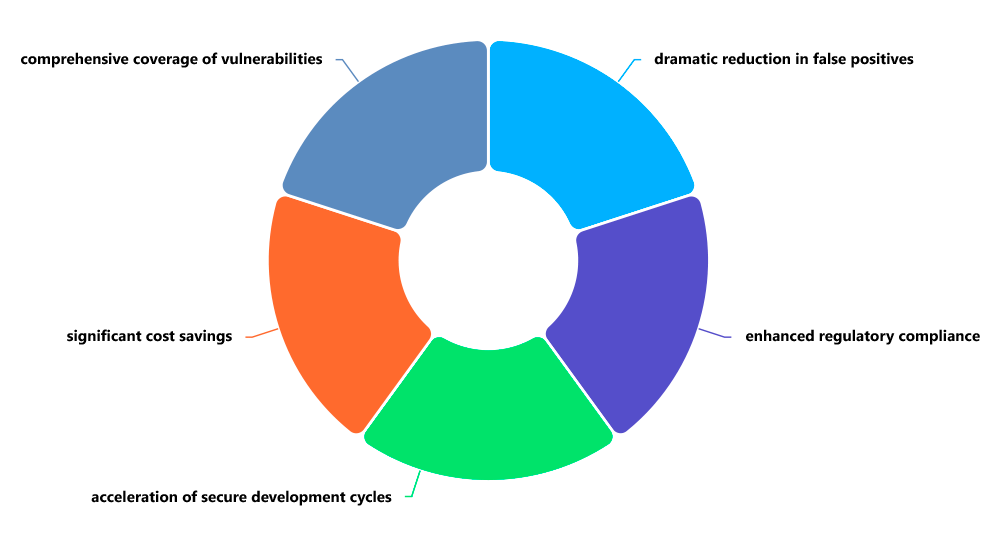
Interactive Application Security Testing (IAST) Benefits
How Are IAST and DAST Different?
IAST and Dynamic Application Security Testing (DAST) both check running applications, but they do it differently and can do different things. DAST is like testing from the outside. It acts like someone trying to attack the application, sending different things to it and watching how it responds to see if there are weaknesses. It doesn't need the source code and usually runs on a copy of the final version or the live version.
IAST, on the other hand, is like testing from the inside. It needs to get into the application to work and uses that inside point of view to find problems. You can see the key difference in what they report. DAST might say, The 'id' thing on this page might let someone inject SQL code, but IAST will say, SQL injection is happening in this specific Java file, on this specific line. That extra detail makes a big difference when a programmer is trying to fix the problem.
DAST often runs later in the process, after the application is built and put in a test space. But IAST gets involved much earlier, during the coding and building stages. DAST is good at finding problems with how things are set up and running in an environment that's close to the real thing. IAST is good at finding specific code problems early on while the application is being actively tested. Because of this, IAST and DAST work well together. IAST handles the early security checks, and DAST gives a final check from the outside.
Why Is IAST Vital to Application Security?
IAST is super important for application security because it connects the idea of early security testing with how software is really made today. It changes security testing from a separate check done by a special team to an automatic part of how programmers work. This isn't just nice to have anymore; it's needed because application attacks are happening more often and are getting more advanced, and software is being released faster than ever.
With cloud software, microservices, and constant updates, old security tools can't keep up. IAST provides the speed, accuracy, and the ability to fit into these new ways of doing things. It helps programmers, who are writing the code, to be the first defense by giving them quick security information that they can use right away in their usual work area. This change means everyone shares the responsibility for security. This is key to making strong software that can grow.
IAST is basic for a good application security setup. It works with SAST (which checks a lot of code) and DAST (which checks the production environment) by adding the important runtime context that they are missing. By using all of these ways to test, companies can have a strong defense for their applications, lowering risk and making sure security doesn't slow down new ideas.
Real-World Examples of How IAST Is Used
The practical applications of IAST span various stages of the software development lifecycle, providing value from development to production. A common use case is within Continuous Integration (CI) Pipelines. Imagine a development team that uses Jenkins or GitLab CI. Every time a developer pushes a new commit, the pipeline automatically builds the application, deploys it to a test environment, and runs a suite of automated API and UI tests. With IAST instrumentation, these functional tests simultaneously become security tests. If a new code change introduces a vulnerability, the IAST tool immediately flags it, and the pipeline can be configured to "break the build," preventing the vulnerable code from progressing further.
Another powerful example is in QA and Security Testing Teams. Security analysts can use IAST to augment their manual penetration testing efforts. While the tester uses browser-based tools like Burp Suite to manually probe the application for weaknesses, the IAST tool runs in the background. It provides the tester with real-time, confirmed vulnerability data, effectively acting as an expert assistant that validates findings and points the tester toward potential blind spots they may have missed, thereby increasing the depth and efficiency of the manual test.
IAST is also invaluable for securing Microservices and APIs. In a complex microservices architecture, tracking data flow and identifying vulnerabilities through traditional DAST can be challenging due to the interconnected nature of the services. IAST can be deployed as an agent within each microservice container. As integration tests are run that simulate communication between services, the IAST tools in each service can track the data, identifying vulnerabilities like insecure deserialization or broken access control as the data moves through the entire ecosystem, providing a holistic view of security in a distributed system.
How ImmuniWeb Helps with IAST
ImmuniWeb, a global leader in application security, provides a robust and intelligent platform that seamlessly incorporates Interactive Application Security Testing into its suite of solutions. ImmuniWeb leverages IAST to deliver the high-fidelity, runtime security testing necessary for modern web applications and APIs. By deploying lightweight sensors within the application, ImmuniWeb's IAST capability continuously monitors interactions during testing, providing real-time visibility into vulnerabilities with minimal false positives, thus aligning perfectly with the needs of DevSecOps.
A key strength of ImmuniWeb's approach is its integration of IAST within a broader, AI-powered security platform. Findings from IAST are not viewed in isolation; they are correlated with results from ImmuniWeb's DAST, SAST, and software composition analysis (SCA) tools. This holistic view provides a comprehensive risk assessment, prioritizing issues based on their actual exploitability and business impact. This context is crucial for security teams who need to manage risk effectively across a large portfolio of applications.
Furthermore, ImmuniWeb enhances IAST with actionable intelligence and compliance mapping. The platform doesn't just identify a vulnerability; it provides detailed remediation guidance tailored to the specific technology stack and maps findings to regulatory standards like PCI DSS, GDPR, HIPAA, and others. This helps organizations not only fix security flaws but also demonstrate compliance efficiently. By offering IAST as part of a unified, intelligent, and scalable platform, ImmuniWeb empowers organizations to build security into their DNA, from code to cloud, ensuring they can develop software rapidly without compromising on security.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










