A Comprehensive Guide to Secure Software Development Life Cycle (S-SDLC)
A Secure Software Development Life Cycle (S-SDLC) is a holistic framework that integrates security practices and considerations into every phase of the software development process, from initial design and coding to testing, deployment, and maintenance, to proactively build security into applications rather than addressing it as an afterthought.

In an era defined by digital transformation and escalating cyber threats, the traditional approach to application security—bolstering defenses after a product is built—is both inefficient and dangerously obsolete. The Secure Software Development Life Cycle (S-SDLC) represents a fundamental paradigm shift, integrating security as a core, continuous concern throughout the entire journey of software creation.
It is a holistic framework of processes, tools, and best practices that ensures security is "baked in, not bolted on." By moving security activities left in the development timeline, the S-SDLC aims to proactively identify and mitigate vulnerabilities at the earliest possible stage, when they are easiest and least expensive to fix, ultimately building more resilient and trustworthy software from the ground up.
How S-SDLC Works
The S-SDLC operates by weaving security activities into each distinct phase of a traditional development lifecycle, such as the Waterfall or Agile methodology. While various models exist (like Microsoft's Security Development Lifecycle), they generally follow a phased approach. It begins at the requirements and design phase, where security requirements are defined alongside functional ones. This involves establishing security standards, conducting threat modeling to identify potential threats and attack vectors, and defining security architecture. By considering security before a single line of code is written, teams can architect a fundamentally more secure system and avoid costly design-level flaws that are difficult to remediate later.
The process then continues into the implementation phase, where developers write code. Here, security is enforced through secure coding standards, peer code reviews with a security focus, and the use of integrated security tools. Static Application Security Testing (SAST) tools are typically run at this stage, scanning the source code automatically to find vulnerabilities like SQL injection or buffer overflows directly within the developers' integrated development environment (IDE). This provides immediate feedback, allowing developers to fix issues as they code, which is far more efficient than addressing them weeks or months later during a dedicated testing phase.
Following implementation, the verification phase involves rigorous testing of the assembled application. This is where Dynamic Application Security Testing (DAST) tools scan the running application for vulnerabilities, Software Composition Analysis (SCA) tools check for vulnerable third-party components, and penetration testers simulate real-world attacks. Finally, the S-SDLC extends into the release and operations phase. This includes conducting final security reviews before deployment, having a robust incident response plan, and establishing processes for monitoring the application in production for new threats, along with a secure patch management process to address any vulnerabilities discovered post-launch. This creates a continuous cycle of improvement, where lessons from one release inform the security posture of the next.
Key Characteristics of S-SDLC
A mature S-SDLC process is defined by several core characteristics that distinguish it from ad-hoc security efforts. The most fundamental is its proactive and preventive nature. Instead of reacting to vulnerabilities after they are discovered in production, the S-SDLC focuses on preventing them from being introduced in the first place. This is achieved through early-stage activities like threat modeling, secure design, and developer training, shifting the security burden left and reducing the reliance on finding flaws at the end of the cycle.
Another critical characteristic is its continuous and integrated approach. Security is not a one-time event or a single gate before release; it is a continuous thread woven throughout the entire lifecycle. In modern DevOps environments, this manifests as DevSecOps, where security tools and checks are automated and integrated into the Continuous Integration/Continuous Deployment (CI/CD) pipeline. This ensures that every code commit triggers automated security tests, making security a seamless part of the daily workflow for developers, QA, and operations teams.
Furthermore, the S-SDLC is holistic and collaborative. It involves multiple teams across the organization, breaking down the traditional silos between development, security, and operations. Security teams provide expertise and tools, development teams write secure code and fix flaws, and operations teams deploy and monitor securely. This collaboration is formalized through defined processes and shared responsibilities. Finally, a true S-SDLC is metrics-driven and governed. It relies on measurable key performance indicators (KPIs)—such as time to remediate vulnerabilities, percentage of code covered by SAST, or number of security bugs found post-release—to track effectiveness, demonstrate value to management, and continuously refine the security program.
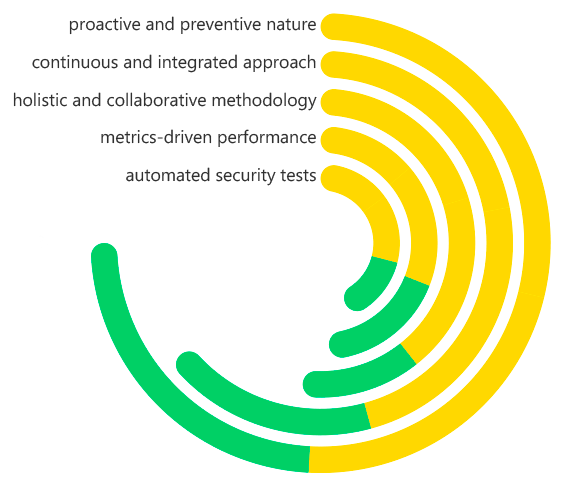
Secure Software Development Life Cycle (S-SDLC) Key Characteristics
What Problems Does S-SDLC Solve?
The S-SDLC directly addresses a host of critical and costly problems that plague traditional software development. The most significant is the "Late-Stage" security problem, where vulnerabilities are discovered only during final testing or, worse, after deployment. Fixing security flaws at this stage is exponentially more expensive and disruptive, often requiring major architectural changes, emergency patching, and potentially causing downtime or security incidents. The S-SDLC solves this by catching issues early when they are just lines of code.
It also tackles the pervasive issue of security as a "gate" or bottleneck. In traditional models, security is often involved only at the end for a pre-release audit, where a "fail" result can delay a launch for weeks. This creates an adversarial relationship between development and security teams. The S-SDLC reframes security as a facilitating partner throughout the process, eliminating the last-minute surprise and the associated schedule delays, thereby fostering a more collaborative and efficient culture.
Furthermore, the S-SDLC solves the problem of inconsistent and non-repeatable security practices. Relying on sporadic penetration tests or the individual expertise of certain developers leads to an inconsistent security posture across different projects and teams. The S-SDLC institutes a standardized, repeatable framework with mandatory security checkpoints, mandated tooling, and defined responsibilities. This ensures a predictable and baseline level of security quality for all software produced by the organization, effectively managing risk at an enterprise level.
Benefits of S-SDLC
The implementation of a robust S-SDLC framework yields profound and multi-faceted benefits. The most compelling advantage is significant cost reduction. By identifying and fixing vulnerabilities early in the development process, organizations avoid the massive costs associated with post-release patches, data breaches, system downtime, and reputational damage. The classic IBM System Sciences Institute finding that a bug found in production can cost 100 times more to fix than one identified in design is a core principle the S-SDLC leverages for financial efficiency.
From a business and competitive standpoint, the S-SDLC delivers faster and more secure time-to-market. By integrating security continuously and automating checks, it prevents major security-related delays at the end of the development cycle. This allows organizations to maintain rapid release velocities without compromising on security, a critical advantage in today's fast-paced digital economy. A secure product also becomes a key market differentiator, building enhanced customer trust and brand reputation.
Operationally, the S-SDLC fosters a positive security culture and improved developer expertise. As developers are equipped with the tools and training to write secure code from the start, they become active participants in the security process. This reduces burnout and friction between teams. Finally, the framework ensures improved compliance and risk management. The S-SDLC provides a structured process to consistently meet regulatory and industry standards (like PCI DSS, GDPR, HIPAA), provides clear audit trails, and gives management a clear view of the organization's software security risk posture.
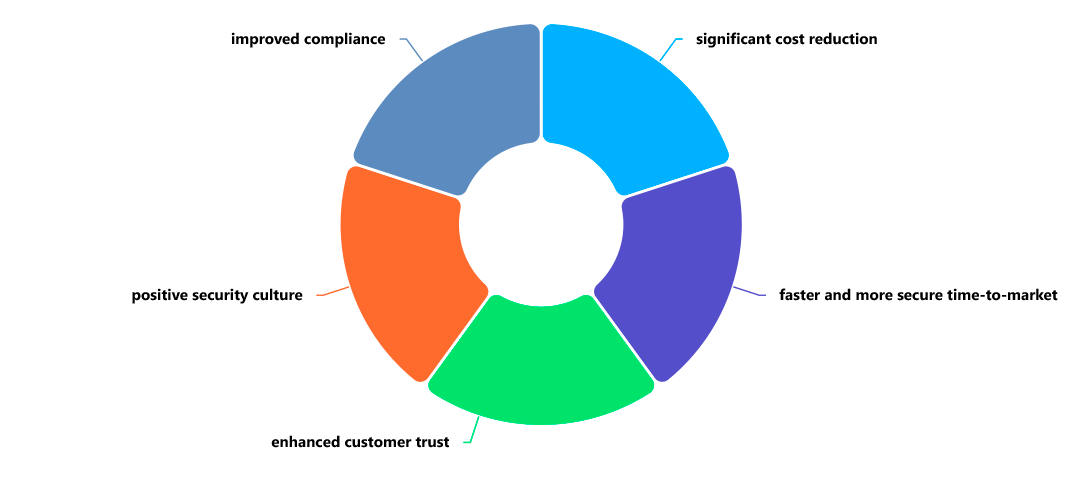
Secure Software Development Life Cycle (S-SDLC) Benefits
How Is S-SDLC Different from Azure DevOps?
It is crucial to understand that the S-SDLC and Azure DevOps are not competing concepts but exist at different levels of abstraction and serve complementary purposes. S-SDLC is a Strategic Security Framework, while Azure DevOps is a Tactical Toolset for Implementing Development Processes.
The S-SDLC is a methodology-agnostic framework of processes, policies, and best practices. It defines the what and when of application security—what security activities need to happen (e.g., threat modeling, SAST, DAST) and when in the lifecycle they should occur. It does not prescribe the specific tools to use; it can be implemented using a variety of technologies, including but not limited to the Microsoft ecosystem.
Azure DevOps, on the other hand, is a specific, commercial product suite from Microsoft that provides tools for source control (Repos), project planning (Boards), CI/CD pipelines (Pipelines), and package management (Artifacts). It is a platform that helps teams implement and automate development processes, which can include processes defined by the S-SDLC. For example, you can use Azure Pipelines to automate the SAST and SCA scans that the S-SDLC mandates in the implementation and verification phases.
In essence, the S-SDLC is the "blueprint" for building security into the software process. Azure DevOps is one of the potential "construction kits" you can use to execute that blueprint efficiently and at scale. You can have an S-SDLC without Azure DevOps (using Jenkins, GitLab, etc.), and you can use Azure DevOps without a mature S-SDLC (resulting in an insecure CI/CD pipeline). The goal is to use the toolset (Azure DevOps) to implement the strategy (S-SDLC) effectively.
Why Is S-SDLC Vital to Application Security?
The S-SDLC is vital because it is the only scalable and sustainable approach to managing application security risk in the face of modern development pressures and threat landscapes. As organizations adopt Agile and DevOps to release software faster, the window for traditional, slow security reviews disappears. The S-SDLC is the essential adaptation that allows security to "keep up" by integrating directly into these high-velocity workflows, making security a prerequisite for speed rather than an obstacle.
Furthermore, the complexity of modern software, built on a foundation of open-source components and interconnected microservices, has exploded the attack surface. Point-in-time security tools like a single annual penetration test are utterly inadequate to address the dynamic and continuous nature of this risk. The S-SDLC is vital because it establishes a continuous, holistic process that covers everything from first-party code and third-party dependencies to deployment configuration, providing comprehensive and ongoing protection.
Ultimately, the S-SDLC is vital for shifting the organizational culture from reactive to proactive. It moves application security from being solely the responsibility of a central security team to a shared responsibility owned by everyone involved in the software lifecycle, especially developers. This cultural shift is the most powerful defense an organization can build. It ensures that security is considered by default, leading to the production of inherently more resilient software that can withstand the evolving tactics of cyber adversaries, thereby protecting critical assets and maintaining business continuity.
Real-World Examples of How S-SDLC Is Used
The S-SDLC is applied in practical, impactful ways across the industry. A prime example is in preventing data breaches in a financial application. A bank developing a new mobile banking feature uses threat modeling in the design phase to identify a potential insecure direct object reference (IDOR) vulnerability in a new API endpoint. The security requirement to implement proper authorization checks is added to the user stories before coding begins. During development, the SAST tool integrated into the CI pipeline flags a piece of code that could be susceptible to SQL injection, and the developer fixes it immediately. This proactive approach prevents what could have been a massive data breach from ever occurring.
Another powerful use case is in managing open-source risk in a e-Commerce platform. A retail company's S-SDLC policy mandates that all software projects must use SCA tools. When a developer adds a new payment processing library, the SCA tool automatically scans it and discovers a critical vulnerability in a transitive dependency. The build is failed in the pipeline, and the developer is prompted to use a patched version. This automated governance prevents a known vulnerable component, which could have been exploited to steal credit card data, from being deployed to production.
The S-SDLC also proves its value in ensuring compliance for a healthcare application. A healthcare software provider must comply with HIPAA regulations. Their S-SDLC process includes specific security requirements for data encryption at rest and in transit, which are verified during the testing phase using DAST. Furthermore, their release process includes a formal security review and sign-off by the Chief Information Security Officer (CISO) to ensure all compliance gates have been met. This structured, repeatable process provides the audit trail needed to demonstrate due diligence to regulators and clients.
How ImmuniWeb Helps with S-SDLC
ImmuniWeb provides a robust, AI-powered platform that operationalizes and enforces the principles of the Secure Software Development Life Cycle. It does not merely provide point-in-time testing but offers a suite of integrated tools that support each phase of the S-SDLC, enabling organizations to implement a continuous and holistic application security program. From discovery and testing to monitoring and compliance, ImmuniWeb helps embed security into the entire software journey.
During the early phases of the S-SDLC, ImmuniWeb aids in Discovery and Inventory Management, helping organizations identify all their web and mobile assets—including forgotten or shadow IT applications—which is the foundational step for any security program. In the implementation and verification phases, ImmuniWeb's integrated SAST, DAST, IAST, and SCA capabilities provide comprehensive testing coverage. Its ability to correlate findings across these different methods reduces false positives and provides developers with highly accurate, prioritized vulnerability data, complete with actionable remediation guidance.
Furthermore, ImmuniWeb extends the S-SDLC into the post-deployment phase with its Continuous Security Monitoring. The platform monitors an organization's applications for changes, new vulnerabilities, and compliance drift, providing an ongoing assurance that the security posture is maintained. By offering a unified platform that combines deep security testing with monitoring and compliance mapping (to standards like PCI DSS, GDPR, HIPAA), ImmuniWeb empowers organizations to not only implement the S-SDLC but also to measure its effectiveness, demonstrate compliance, and continuously improve their application security maturity, turning the S-SDLC framework from an abstract concept into a tangible, operational reality.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










