A Comprehensive Guide to Software Bill of Materials (SBOM)
A Software Bill of Materials (SBOM) is a formal, machine-readable inventory that identifies and lists the components, libraries, and dependencies used in a software application, providing transparency into its supply chain for security, compliance, and management purposes.

These days, it's rare for anyone to build software completely from the ground up. Modern apps are usually made by putting together things like open-source libraries, third-party parts, software development kits you can buy, and code that a company owns.
This speeds up how quickly we can make software, but it also means that the path software takes from being made to being used is complicated and not always easy to see.
That's why a Software Bill of Materials (SBOM) has become so important. It helps make things clear and keeps things safe. Think of it like a list of ingredients on food packaging. An SBOM is a detailed list of everything that makes up a piece of software. It gives us the basic information we need to handle risks, fix weaknesses, and make sure software is safe all the way from when it's first made to when it's used.
How SBOM Works
An SBOM is like a list that tells you what's inside a piece of software. It's made using automatic tools that look at the software's code and everything it depends on.
First, the tools find all the pieces by scanning the code and related files. They check things like package.json for JavaScript projects or pom.xml for Java projects to see which libraries the programmers used. Then, they look at what those libraries need, too. This gives a full picture of what the software is made of.
Next, the tool adds more info to the list, like the name, version, and a special ID for each part. These IDs, such as Package URLs (PURLs), make sure everyone knows exactly which piece is being talked about. The SBOM might also include the license, who made the piece, and a code to check if the piece has been changed.
Lastly, all the info is put into a standard format that computers can read. The main formats are SPDX, CycloneDX, and SWID tags. These formats make it easy for different tools to use and understand the SBOM. This means SBOMs can be used on many apps and parts without problems. The finished SBOM can be shared with customers, saved in a file, or used to check security and make sure everything is correct.
Key Characteristics of SBOM
A truly effective SBOM is defined by several key characteristics that ensure its utility and reliability. First and foremost is depth and completeness. A superficial list of top-level dependencies is insufficient. A robust SBOM provides a nested, hierarchical view that includes all transitive dependencies, often referred to as "dependencies of dependencies." This deep visibility is necessary to understand the full attack surface, as vulnerabilities often lurk in these indirectly included components.
Another fundamental characteristic is automation and machine-readability. SBOMs must be generated automatically as part of the build and Continuous Integration/Continuous Deployment (CI/CD) process to ensure accuracy and timeliness. Manual creation is error-prone and unsustainable. Furthermore, the output must be in a standardized, machine-readable format (like SPDX or CycloneDX) rather than a static PDF or document. This allows security tools to automatically ingest, parse, and correlate SBOM data against vulnerability databases, enabling rapid response to new threats.
Data freshness and accuracy are also critical. Software is dynamic; dependencies are constantly added, updated, or removed. An SBOM is not a one-time snapshot but a living artifact that must be updated with every new build of the software. An outdated SBOM can be misleading and provide a false sense of security. Finally, a comprehensive SBOM supports license compliance and component provenance. It clearly lists the licenses associated with each component, helping legal and compliance teams manage obligations, and it can include data about the component's origin and supplier, which is vital for assessing supply chain trust.
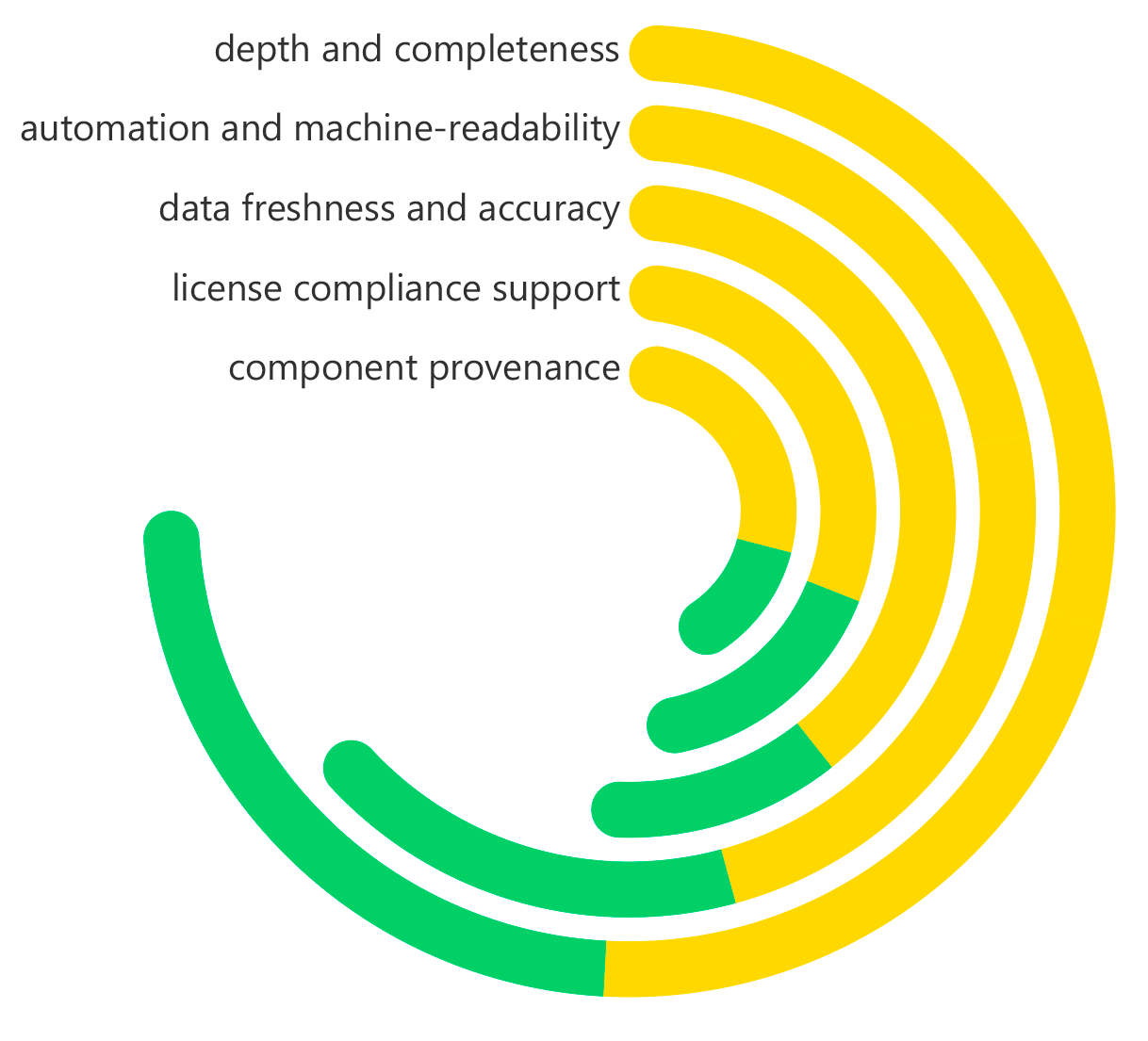
Software Bill of Materials (SBOM) Key Characteristics
What Problems Does SBOM Solve?
SBOMs directly address some big, growing problems in how we use software today. The main worry is that we can't see what's going on in the software supply chain. Companies often don't know what open-source and other outside parts are in their apps. This makes it hard to judge risks or quickly fix things when there's a new weakness, like those found in Log4j or Apache Struts. An SBOM fixes this by giving a clear list of everything inside.
It also helps with the huge trouble of fixing weaknesses slowly and badly. If you don't have an SBOM, when a new problem (CVE) is announced, security teams have to rush around and manually check if their apps are at risk. This takes time, effort, and often leads to mistakes. But with an SBOM, this can be automatic. Security programs can quickly check the list of parts in the SBOM against the latest threat info. This shows exactly which apps are weak, cutting the time to fix things from days to minutes.
Also, SBOMs fix licensing and audit issues. Keeping track of all the legal stuff for different open-source licenses across many apps is a big job. An SBOM gives a clear record of each license, which stops problems and fights about rules. Lastly, SBOMs meet the rising need for software to be open and clear, from both regulators and customers. Government orders and new computer security rules around the world are beginning to require SBOMs. This makes them vital for doing business, especially with the government and companies that care about security.
Benefits of SBOM
The widespread adoption of SBOMs delivers profound benefits across security, operational, and business functions. The most significant advantage is the dramatic acceleration of vulnerability remediation. By knowing precisely which components are in which applications, organizations can move from a reactive posture to a proactive one. When a critical CVE is published, teams can immediately identify all affected assets and prioritize patches, significantly reducing their mean time to repair (MTTR) and shrinking the window of exposure.
From an operational standpoint, SBOMs introduce unprecedented efficiency in software supply chain management. They eliminate the guesswork and manual toil associated with component tracking, freeing up valuable engineering and security resources. This efficiency extends to merger and acquisition activities, where the acquirer can perform precise technical due diligence by analyzing the target company's software inventory. It also streamlines software audits, both internal and external, by providing a single source of truth.
Another key benefit is enhanced license compliance and risk reduction. SBOMs provide legal and compliance teams with the data needed to avoid license violations that can lead to costly litigation or forced source code publication. This protects intellectual property and maintains business continuity. Finally, SBOMs foster stronger customer trust and regulatory adherence. By providing an SBOM to customers, a software vendor demonstrates a commitment to transparency and security, differentiating themselves in the marketplace and building stronger, more trusting partnerships.
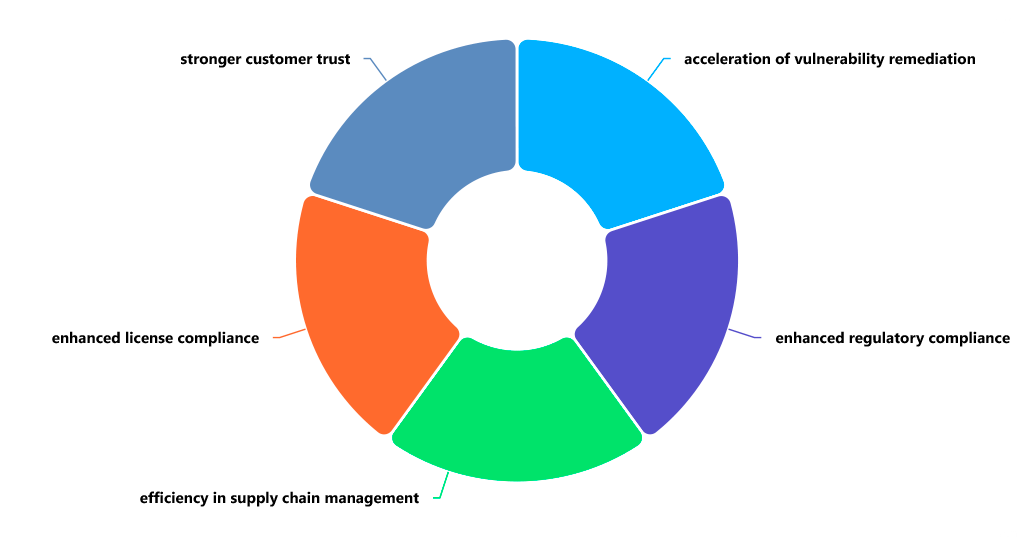
Software Bill of Materials (SBOM) Key Characteristics
How Is SBOM Different from SCA?
Software Composition Analysis (SCA) and SBOM are related but different. SCA is like the action, and SBOM is what you get from it.
SCA tools scan code to find problems like security weaknesses and license issues. They're the tech that does the work.
An SBOM is the list of all the stuff in your software. It's not just about security; it's a record of everything, which makes it useful for managing the software over its lifespan, proving you're following the rules, and being open about what's in your software.
Imagine making something: SCA is like checking the materials for problems. The SBOM is like the packing slip that says what's in the box. You need to check for problems, but you also need to know what you used. Both are important for doing software right.
Why Is SBOM Vital to Application Security?
SBOM is vital because application security can no longer be confined to an organization's own code. The vast majority of modern software risk originates from the supply chain. High-impact vulnerabilities like Log4Shell, Heartbleed, and the recent XZ Utils backdoor scare have starkly demonstrated that an attack on a single, ubiquitous open-source component can create a global crisis. Without an SBOM, organizations are flying blind into these storms, unable to quickly or confidently determine their exposure.
Furthermore, SBOM transforms application security from a reactive to a proactive and predictive discipline. It provides the foundational data layer that enables automation at scale. Security teams can build workflows where new vulnerability disclosures automatically trigger scans of all SBOMs in a repository, instantly generating tickets for the owners of affected applications. This moves the entire security program from a frantic, manual emergency response to a streamlined, orchestrated process, fundamentally improving an organization's resilience.
Ultimately, SBOM is vital due to the escalating demands of regulators and the market. Cybersecurity frameworks and government mandates, such as the U.S. Executive Order on Improving the Nation's Cybersecurity, are formalizing the requirement for SBOMs in software sold to the federal government. This trend is trickling down to the private sector, making SBOMs a baseline expectation for doing business. In this new reality, having an SBOM program is not just a best practice; it is a fundamental requirement for demonstrating due diligence and maintaining a license to operate.
Real-World Examples of How SBOM Is Used
SBOMs have moved from theory to practice, providing critical value in numerous real-world scenarios. A prime example is accelerated zero-day response. When a critical vulnerability like Log4Shell is announced, an organization with a centralized SBOM repository can immediately query it. Instead of days of panic and manual searches, a simple query for "log4j-core" instantly returns a list of every application, version, and server that contains the vulnerable component. This allows the security team to assign patches with precision and provide executive leadership with an accurate assessment of impact within hours, not days.
Another powerful use case is in procurement and vendor risk management. A large enterprise considering a new software vendor from a merger can request an SBOM as part of the security questionnaire. The enterprise's security team can then analyze the SBOM to check for a high volume of known vulnerable components, the use of restrictive or non-compliant licenses, or dependencies on poorly maintained or malicious open-source projects. This provides a data-driven method to assess technical risk before signing a contract, preventing a future security or compliance disaster.
SBOMs are also critical for devops and platform engineering teams managing large internal platforms. In a microservices architecture with hundreds of services, each with its own dependencies, tracking components manually is impossible. By mandating that every service build produces an SBOM, the platform team can maintain a live inventory of the entire software ecosystem. This allows them to proactively monitor for newly disclosed vulnerabilities across all services and automatically generate pull requests to update dependencies in a controlled, systematic manner, ensuring the overall platform's health and security.
How ImmuniWeb Helps with SBOM
ImmuniWeb leverages its AI-powered platform to provide comprehensive SBOM capabilities that are deeply integrated into a broader application security testing and monitoring framework. ImmuniWeb’s technology automatically generates accurate, detailed, and standards-compliant SBOMs (in formats like SPDX and CycloneDX) as part of its continuous discovery and testing processes. By scanning an organization's web and mobile applications, ImmuniWeb builds a complete inventory of software components, including open-source libraries, frameworks, and their transitive dependencies.
A key strength of ImmuniWeb’s approach is the seamless integration of SBOM generation with proactive security monitoring. The platform doesn't just create a static SBOM; it continuously monitors the components listed within it against global vulnerability databases and threat intelligence feeds. When a new vulnerability is discovered in a component, ImmuniWeb can immediately alert the organization, pinpoint the exact applications affected, and provide actionable remediation guidance. This turns the SBOM from a passive document into an active, early-warning system for the software supply chain.
Furthermore, ImmuniWeb enhances SBOM management with its focus on compliance and risk reduction. The platform helps organizations meet evolving regulatory requirements by providing the necessary transparency and audit trails. It also assesses the risk posture of each component, considering factors beyond just CVEs, such as the component's age, update frequency, and maintenance status. By offering a unified view that combines SBOM data with security testing results and compliance mapping, ImmuniWeb empowers organizations to master their software supply chain, making informed decisions that enhance security, ensure compliance, and build resilient software from the ground up.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










