A Comprehensive Guide to Software Composition Analysis (SCA)
Software Composition Analysis (SCA) is a security methodology that automatically identifies and analyzes the open-source and third-party components within a software project to manage security vulnerabilities, license compliance, and operational risks associated with the software supply chain.

In today's software development world, instead of just build vs. buy, there's now a third way: assemble. Developers are using many open-source libraries and third-party parts to get things done faster. Open-source code often makes up most of an app's code. This helps people get more done, but it also brings hidden risks from the software supply chain.
Software Composition Analysis (SCA) is all about managing these risks. It gives you the tools to automatically find all the open-source parts in an app, spot any security problems, handle license issues, and keep the software's base secure.
How SCA Works
Software Composition Analysis operates through an automated process of discovery, analysis, and remediation. The first and most critical step is Component Discovery. SCA tools integrate directly into the development environment, typically by scanning manifest files such as package.json for Node.js, pom.xml for Java, or requirements.txt for Python. They also perform deeper binary and source code scanning to identify components that may have been included manually or are transitive dependencies—libraries that your direct dependencies rely on. This creates a complete, hierarchical inventory of the entire software bill of materials (SBOM).
Once the components are identified, the SCA tool moves to the Vulnerability Analysis phase. It compares the identified components, including their specific versions, against a continuously updated database of known security vulnerabilities. These databases aggregate information from sources like the National Vulnerability Database (NVD), security advisories from open-source projects, and proprietary research. The tool then correlates the findings, flagging any component version that has a known Common Vulnerability and Exposure (CVE) or other security advisory associated with it, and typically assigns a severity score based on standards like the Common Vulnerability Scoring System (CVSS).
The final and most crucial phase is Prioritization and Remediation. A mature SCA solution goes beyond simply listing vulnerabilities. It provides contextual risk analysis by prioritizing findings based on factors such as the severity of the vulnerability, whether the vulnerable component is actually callable in the application (reachability analysis), the age of the component, and the availability of a fixed version. The tool then provides actionable remediation guidance, often automatically suggesting an upgrade path to a patched version of the library or, if an upgrade isn't available, detailing potential workarounds or compensating controls to mitigate the risk.
Key Characteristics of SCA
A robust SCA tool is defined by several key characteristics that ensure its effectiveness and integration into the software development lifecycle. First is its comprehensive and deep dependency scanning. A basic SCA tool might only identify direct dependencies listed in a manifest file. However, a powerful SCA solution performs deep recursive scanning to uncover the entire tree of transitive dependencies, which often account for the majority of the open-source code and hidden vulnerabilities in an application. This provides a true, complete picture of the software's composition.
Another fundamental characteristic is accuracy and low false-positive rate. The tool must accurately map detected components to the correct vulnerabilities, minimizing noise for development teams. This involves sophisticated version matching and normalizing component names across different ecosystems (e.g., recognizing that lodash and Lodash are the same project). High-quality SCA tools reduce false positives by verifying that the vulnerable function is actually present in the version of the component being used, rather than relying solely on version ranges.
Furthermore, speed and seamless integration are non-negotiable. SCA must be fast enough to run within CI/CD pipelines without causing significant delays. It should integrate natively with developer tools like GitHub, GitLab, Azure DevOps, and Jira to provide feedback directly in the developers' workflow. Finally, a critical characteristic is proactive alerting and policy enforcement. The best SCA tools continuously monitor for newly disclosed vulnerabilities in an organization's inventory of components, even after a scan is complete, and can be configured with security policies to automatically fail a build if a critical vulnerability is introduced, enforcing security gates early in the development process.
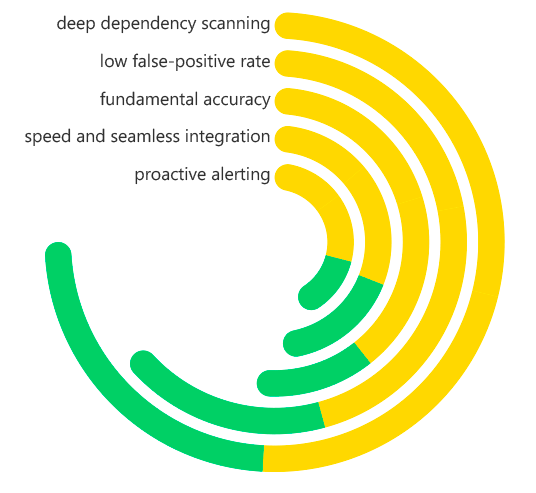
Software Composition Analysis (SCA) Key Characteristics
What Problems Does SCA Solve?
SCA gets right to the core of some big problems that are popping up more and more in how we build software these days. One of the biggest worries is not knowing what risks are hiding in the software we get from other places. If you don't have SCA, it's like trying to drive with your eyes closed – you have no idea what code is actually running in your stuff. That means you can't know if you're using software parts that have serious security holes that everyone knows about. SCA gets rid of this problem by giving you a clear, automatic list of what you're using and what dangers might be lurking.
It also helps big time with fixing security problems faster and better. Doing it all by hand – trying to keep up with new security warnings and checking them against what you're using – takes forever, is boring, and people make mistakes. When something huge happens, like that Log4Shell mess, companies without SCA are running around like crazy, wasting tons of time. SCA makes it so you can automatically match the warnings to your software, so you know right away what's at risk and can fix it way quicker.
SCA is also a fix for the money and legal headaches that come with using open-source software. With open source, there are rules you have to follow, and if you don't (like using a library that makes you share your code when you don't want to), you can get sued, have to make your code public, and look bad. SCA tells you what licenses each piece of your software has and points out the ones that could cause trouble, so your legal and coding teams can handle things before they blow up. Lastly, it takes care of the issue of using old, unsupported software, which is a long-term security risk, by calling attention to pieces that aren't getting updates anymore.
Benefits of SCA
The implementation of a robust SCA program yields profound benefits across security, legal, and operational domains. The most significant advantage is the proactive management of supply chain risk. By providing continuous visibility into the open-source inventory, SCA allows organizations to shift from a reactive posture (responding to headlines about new vulnerabilities) to a proactive one (knowing their exposure and having a plan before a crisis hits). This fundamentally strengthens an organization's security resilience.
From a business and operational standpoint, SCA delivers substantial cost savings and operational efficiency. Finding and fixing a vulnerable component during development is exponentially cheaper than remediating it after a product has been deployed, where costs can include emergency patching, security incident response, potential regulatory fines, and brand damage. The automation provided by SCA also frees up valuable security and developer resources from manual audit tasks, allowing them to focus on higher-value work.
Another key benefit is accelerated and secure development velocity. By integrating SCA into the CI/CD pipeline, developers receive immediate feedback on the security of their code dependencies as they write it. This "shift-left" approach embeds security as a natural part of the development process, preventing vulnerabilities from being baked into releases and avoiding last-minute delays. This enables organizations to maintain both speed and security, a crucial competitive advantage. Finally, SCA ensures robust license compliance, protecting the organization from legal disputes and enabling the safe and ethical use of open-source software.
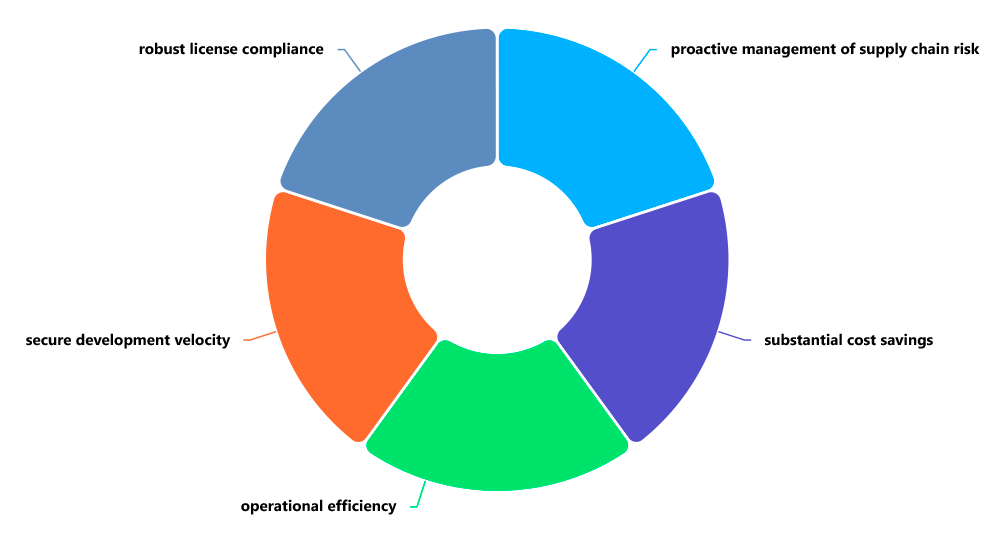
Software Composition Analysis (SCA) Benefits
How Is SCA Different from SAST?
It is crucial to distinguish Software Composition Analysis (SCA) from Static Application Security Testing (SAST), as they address complementary but distinct aspects of application security. The core difference lies in what they analyze and the origin of the code. SAST is designed to analyze an organization's proprietary, custom-written source code for coding errors and security flaws, such as SQL injection, buffer overflows, or insecure authentication logic. It looks for patterns and anti-patterns in the code that you wrote.
SCA, in contrast, is exclusively focused on analyzing third-party and open-source components—the code that you did not write but have incorporated into your application. Its primary function is to identify these components and check them against databases of known vulnerabilities. While SAST answers the question, "Are there bugs in our code?", SCA answers the question, "Are we using any vulnerable external libraries?"
Another key difference is in their underlying technology and knowledge bases. SAST tools use complex rulesets and data flow analysis to reason about the potential behavior of custom code. SCA tools rely on massive, continuously updated databases of component metadata, version information, and associated CVEs. They are essentially specialized search and correlation engines. For a comprehensive application security program, both SAST and SCA are essential: SAST secures the code you create, while SCA secures the ecosystem you depend upon. Using one without the other leaves a critical gap in your security posture.
Why Is SCA Vital to Application Security?
SCA is vital because the attack surface of a modern application has expanded far beyond its custom code. The most devastating cybersecurity incidents in recent years, such as the breaches linked to vulnerabilities in Log4j, Apache Struts, and OpenSSL, have not been due to flaws in proprietary code, but in ubiquitous open-source components. Ignoring the security of this software supply chain is akin to fortifying the front door of a castle while leaving the rear gate wide open and unguarded.
Furthermore, the scale and complexity of open-source dependencies make manual management impossible. A single application can easily pull in hundreds of transitive dependencies, creating a vast and dynamic inventory that changes with every build. Human teams cannot realistically track this complexity or respond in a timely manner to the constant stream of new vulnerability disclosures. SCA provides the necessary automation and scalability to manage this problem, making it a non-negotiable component of any modern DevSecOps practice.
Ultimately, SCA is vital due to the escalating demands of regulators, customers, and the market. Cybersecurity frameworks, software procurement contracts, and government mandates are increasingly requiring software producers to demonstrate control over their supply chain. Providing a Software Bill of Materials (SBOM), which is a direct output of SCA, is becoming a standard expectation. In this new reality, having an SCA program is not just a technical best practice; it is a fundamental requirement for demonstrating due diligence, maintaining customer trust, and preserving the license to operate.
Real-World Examples of How SCA Is Used
SCA tools are applied in numerous practical scenarios to prevent security incidents and streamline development. A prime example is its use in CI/CD pipeline gating. A development team configures their SCA tool to break the build in their Jenkins or GitHub Actions pipeline if a new dependency introduces a critical or high-severity vulnerability. When a developer submits a pull request that adds a new feature using an outdated library with a known security flaw, the SCA scan fails the build automatically. The developer is immediately notified and provided with a link to the patched version of the library, ensuring that vulnerabilities are prevented from ever entering the codebase.
Another powerful use case is emergency response to critical vulnerabilities. When a widespread vulnerability like the Log4Shell (CVE-2021-44228) is disclosed, organizations without SCA descend into chaos, with teams manually searching codebases. An organization with a mature SCA program simply runs a query against their centralized SCA platform for the component "log4j-core" version 2.0-beta9 through 2.15.0. Within minutes, they have a precise list of every application, microservice, and environment that is affected, allowing them to assign remediation tasks with precision and provide accurate status reports to leadership.
SCA is also critical for merger and acquisition (M&A) due diligence. Before a large enterprise acquires a startup, the acquiring company's security team uses SCA to perform a deep scan of the startup's primary software products. The SCA report reveals a heavy use of outdated dependencies with high-severity vulnerabilities and several components with restrictive, non-compliant licenses. This objective data allows the acquirer to accurately quantify the technical debt and potential liability, negotiate a lower purchase price, or mandate a remediation plan as a condition of the sale.
How ImmuniWeb Helps with SCA
ImmuniWeb leverages its AI-powered platform to deliver comprehensive and deeply integrated Software Composition Analysis as a core component of its application security suite. ImmuniWeb’s SCA capability automatically discovers and inventories all open-source and third-party components across web and mobile applications, providing organizations with complete visibility into their software supply chain. It performs deep, recursive scanning to uncover not just direct dependencies but also the often-overlooked transitive dependencies that constitute the majority of security risk.
A key strength of ImmuniWeb’s approach is the seamless correlation of SCA findings with other application security data. The platform doesn't just list vulnerable components; it enriches these findings with contextual intelligence from its dynamic (DAST) and static (SAST) testing. This can help prioritize vulnerabilities that are not only present but also actually exploitable based on the application's specific configuration and code paths. Furthermore, ImmuniWeb continuously monitors its extensive vulnerability intelligence feeds, providing proactive alerts when a new CVE affects a component in an organization's inventory, turning the SCA solution from a scanning tool into an early-warning system.
ImmuniWeb enhances SCA management with a strong focus on actionable remediation and compliance. The platform provides clear, developer-friendly guidance on how to fix identified issues, including direct upgrade paths. It also meticulously tracks open-source licenses, flagging potential compliance conflicts and helping legal teams manage obligations. By integrating SCA into a unified platform that includes threat-aware monitoring and compliance reporting, ImmuniWeb empowers organizations to not only find and fix supply chain risks but also to demonstrate compliance and build a mature, resilient software security practice.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










