Enhancing Cyber Defenses: A Comprehensive Guide to Static Application Security Testing (SAST)
Static Application Security Testing (SAST) is a testing methodology that analyzes an application's source code at rest to identify security vulnerabilities early in the development lifecycle.

Now, applications are super important for businesses in this digital world, but they're also a big target for attacks. Since cyber threats are getting smarter, old-school security isn't enough anymore. Static Application Security Testing (SAST) is a key way to spot security weaknesses in applications, acting like a real attacker to protect what the company cares about most.
How SAST Works
Static Application Security Testing (SAST) is a way to test software by looking at its code before it's up and running. It's like having someone check the blueprints of a house for problems before it's built, instead of waiting to inspect the finished house. The SAST tool needs access to all the code, so it can figure out how data moves around and how the program works.
Here’s how it works: First, the tool reads the code and turns it into a format it can understand, called an abstract syntax tree (AST). Then, it looks at how data flows through the application (especially user input) and maps out the different paths the program can take. By doing this, the tool can see if dangerous user input from a source (like a web form) ends up in a sensitive place (like a database query) without being checked or cleaned along the way.
In the end, the SAST tool checks the code for common problems based on a list of known vulnerabilities, such as the OWASP Top 10 or CWE. For instance, if the tool sees user data going straight into a SQL query, it will point this out as a possible SQL Injection vulnerability. The tool will give a report that lists what it found, how serious the problems are, the exact line of code where they happen, and advice on how to fix them. This gives developers a clear way to go from problem to fix.
Key Characteristics of SAST
Several fundamental characteristics define SAST and distinguish it from other application security testing methods. The most prominent is its white-box nature. SAST requires full access to the application's source code. This deep visibility allows it to uncover the root cause of vulnerabilities within the code itself, offering a level of insight that black-box testing methods simply cannot achieve. It can see every branch of logic, every function call, and every variable, enabling a comprehensive and early assessment.
Another critical characteristic is its shift-left capability. "Shifting left" refers to integrating security testing early in the Software Development Lifecycle (SDLC), ideally during the coding phase itself. SAST is uniquely suited for this, as it can scan code as soon as it is written, even before the application is compiled or deployed to a testing environment. This allows developers to find and fix security flaws in real-time, which is significantly faster and cheaper than remediating them after a QA test or, worse, in production.
SAST is also characterized by its language and framework specificity. A SAST tool must be explicitly configured to understand the programming languages, frameworks, and libraries used in the application. A tool optimized for scanning a .NET application written in C# will be ineffective for a mobile app written in Swift or a web service in Python. This means organizations often need to invest in tools that support their specific technology stack and keep them updated as new language versions and frameworks emerge.
Finally, a well-known characteristic of SAST is its potential for generating false positives. Because the tool performs a static, theoretical analysis without executing the code, it can sometimes flag code paths that look vulnerable in theory but are not exploitable in practice due to surrounding context or compensating controls. Tuning the tool to reduce noise and training developers to triage these results effectively are essential for a successful SAST program, ensuring that teams focus their efforts on genuine, critical security risks.
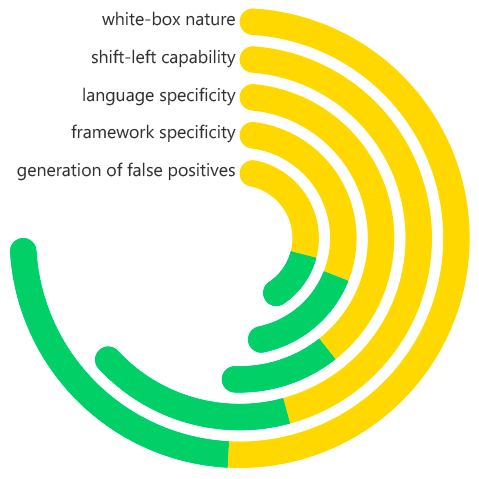
Static Application Security Testing (SAST) Key Characteristics
What Problems Does SAST Solve?
SAST is here to fix some big headaches in how we build software today. Mainly, it stops us from finding security issues super late in the game. Before, security testing was often the last thing we did before releasing something, and a special team handled it. If you found a major security problem then, it meant big delays and lots of extra work. SAST moves security checks earlier in the process. It finds issues when they're cheapest and easiest to correct—right in the developer's coding area, saving a ton of time and money.
SAST also helps with secure coding knowledge. Not all developers are security pros, and with pressure to put out features fast, security sometimes gets missed. SAST works like a security helper that's always on. It scans code for common mistakes and teaches developers as they go. If it spots a possible buffer overflow or cross-site scripting issue while the code is being written, it gives feedback right away. This helps developers learn and remember secure coding methods, which makes the whole team better at security over time.
SAST is also great for dealing with old code and the risks that come with it. A lot of companies have huge, older codebases that weren't built with today's security in mind. Checking millions of lines of code by hand is almost impossible. SAST can quickly scan all of this old code, giving a list of security holes and a plan for fixing them. This lets companies take control of the security risks hiding in their apps, preventing them from causing problems later on.
Benefits of SAST
The implementation of a robust SAST program yields a multitude of significant benefits. The most frequently cited is early and cost-effective vulnerability detection. Studies, including those from IBM System Sciences Institute, have consistently shown that the cost to fix a bug found during production can be up to 100 times more than if it were found during the coding phase. By catching flaws at the earliest possible stage, SAST drastically reduces remediation costs, effort, and project delays, providing an excellent return on investment.
Another major benefit is the acceleration of development and DevOps cycles. While this may seem counterintuitive—adding a step might slow things down—a well-integrated SAST tool actually speeds up the overall process. By automating code review for security issues, it frees up senior developers and security architects from manual code audits. When integrated into CI/CD pipelines, it provides fast, automated security gates, preventing vulnerable code from progressing and ensuring that security becomes a seamless, non-blocking part of the development workflow.
SAST also provides comprehensive and deep code coverage. Because it analyzes 100% of the codebase, including all possible execution paths (even those that are rarely triggered), it can find vulnerabilities that are hidden deep within the application logic. This is in stark contrast to manual testing or dynamic analysis, which can only test the code paths that are actually executed during the test. This comprehensive scrutiny is essential for achieving a high level of assurance in the security of business-critical applications.
Finally, SAST enhances regulatory compliance and risk management. Many industry standards and regulations, such as PCI DSS, HIPAA, and GDPR, implicitly or explicitly require secure development practices, including code review. A SAST program provides demonstrable evidence of due diligence in identifying and mitigating security vulnerabilities in custom application code. The detailed reports and audit trails generated by SAST tools are invaluable for proving compliance to auditors, regulators, and clients.
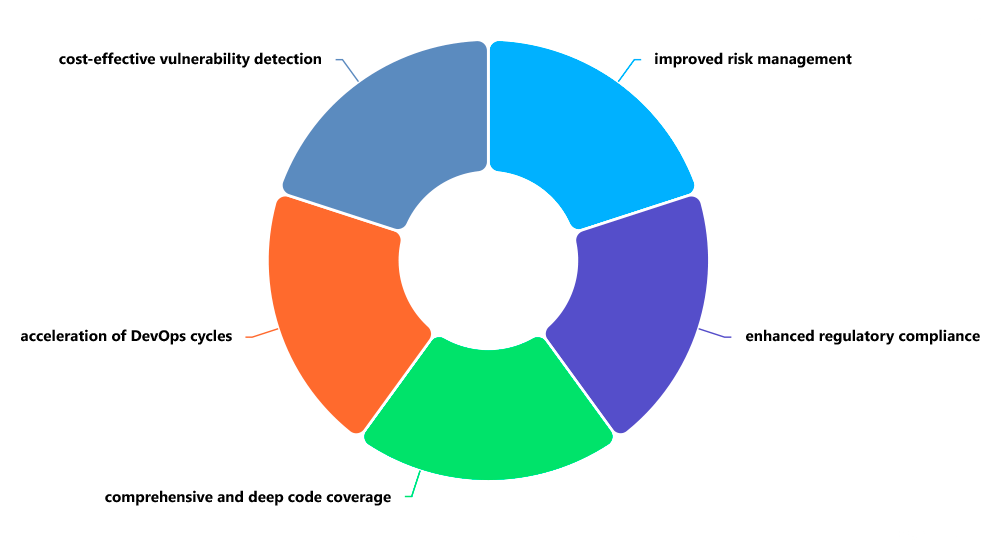
Static Application Security Testing (SAST) Benefits
How Are SAST and DAST Different?
SAST and DAST are different ways to check an app's security. You can think of SAST as white-box testing and DAST as black-box testing. SAST looks at the app's code without running it, while DAST tests the app while it's running, like a hacker trying to break in.
Each method finds different kinds of problems. SAST is good at spotting coding errors, like problems with how the code is written or how it handles input, insecure calls or not following security rules when coding. DAST is good at finding issues that show up when the app is running, like setup mistakes, server problems, login issues, and problems that arise when all parts of the app work together.
SAST and DAST are used at different times in the development process. SAST is used early on, as soon as the code is written. DAST is used later, after the app is up and running in a test environment. So, SAST helps developers catch problems early, while DAST helps testers and security people find issues in the finished product. The best security plans use both methods to find all sorts of weaknesses throughout the app's life.
Why Is SAST Vital to Application Security?
SAST is super important because it tackles security right where it starts: in the code itself. Most attacks on applications take advantage of weak spots that accidentally get into the software when it's being made. Things like network firewalls and WAFs are useful, but they're similar to guards protecting a building that has problems with its base. SAST gives you the technical breakdown to make sure the base—the application's code—is solid from the get-go, which makes for a safer product overall.
Now that we have DevSecOps and are constantly pushing out updates, SAST is how you keep security in step. Doing code checks by hand just can't keep up with today's fast-moving development and release schedules. SAST takes care of the first, time-consuming security check on its own, so your security pros can zero in on tricky logic problems and the big-picture design. Without SAST's help, it's almost impossible to be quick and secure at the same time, so it's a must-have for making software these days.
SAST is also a must for keeping your software supply chain secure. Today's applications are usually a mix of code you write and pieces you get from open-source. SCA tools check for known issues in open-source, but SAST is key for securing the code you write to connect everything. It makes sure that your unique business ideas and private code—the stuff that makes your company different and often handles your most important information—are created with security in mind. This keeps your company's important stuff safe and keeps your customers trusting you.
Real-World Examples of How SAST Is Used
SAST is employed in various practical scenarios throughout the software development lifecycle. A primary use case is IDE Integration for Real-Time Feedback. Developers use plugins that integrate SAST directly into their Integrated Development Environments (IDEs), such as Visual Studio or IntelliJ. As a developer writes code, the tool highlights potential security issues in real-time, underlining a vulnerable function call or a potentially unsanitized variable. This immediate feedback allows the developer to fix the flaw on the spot, preventing it from ever being committed to the code repository.
Another critical real-world application is within the Continuous Integration/Continuous Deployment (CI/CD) Pipeline. Here, SAST acts as an automated security gate. After a developer commits code to a shared repository like Git, the CI pipeline automatically triggers a SAST scan. If the scan discovers new vulnerabilities that exceed a predefined severity threshold (e.g., critical or high), it can "break the build," preventing the code from being merged and deployed. This enforces a policy that only secure code can progress, embedding security directly into the DevOps workflow.
SAST is also extensively used for Legacy Application Modernization and Compliance Audits. When an organization needs to assess the security of a large, inherited codebase or prepare for an audit like PCI DSS, they run a comprehensive SAST scan. The resulting report provides a prioritized list of vulnerabilities across the entire application, which the security team can use to create a remediation sprint plan. For example, they might focus first on all critical SQL Injection flaws before addressing medium-severity issues, providing a data-driven approach to reducing risk in legacy systems.
How ImmuniWeb Helps with SAST
ImmuniWeb provides a robust and AI-enhanced application security solution that includes powerful SAST capabilities designed for modern development environments. ImmuniWeb's SAST goes beyond traditional pattern matching by leveraging artificial intelligence to improve the accuracy of its findings, effectively reducing the noise of false positives that often plague development teams. This allows developers to focus their valuable time on fixing genuine security risks rather than triaging irrelevant alerts.
A key strength of ImmuniWeb is its deep integration into the DevSecOps pipeline. Its SAST tool can be seamlessly incorporated into popular CI/CD platforms like Jenkins, Azure DevOps, and GitHub Actions. This enables automated, continuous security testing with every code commit, ensuring that security is a continuous and measurable part of the software delivery process. The platform provides detailed, developer-friendly reports that pinpoint the exact location of the vulnerability in the code and offer actionable remediation guidance, streamlining the fix process.
Furthermore, ImmuniWeb combines its SAST findings with other testing methodologies, such as Dynamic Testing (DAST) and Software Composition Analysis (SCA), within a single, unified platform. This holistic approach provides a comprehensive view of an application's security posture, covering vulnerabilities in custom code, runtime behavior, and third-party dependencies. By offering SAST as part of an integrated application security suite, ImmuniWeb helps organizations build secure software from the inside out, efficiently and effectively managing risk throughout the entire application lifecycle.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










