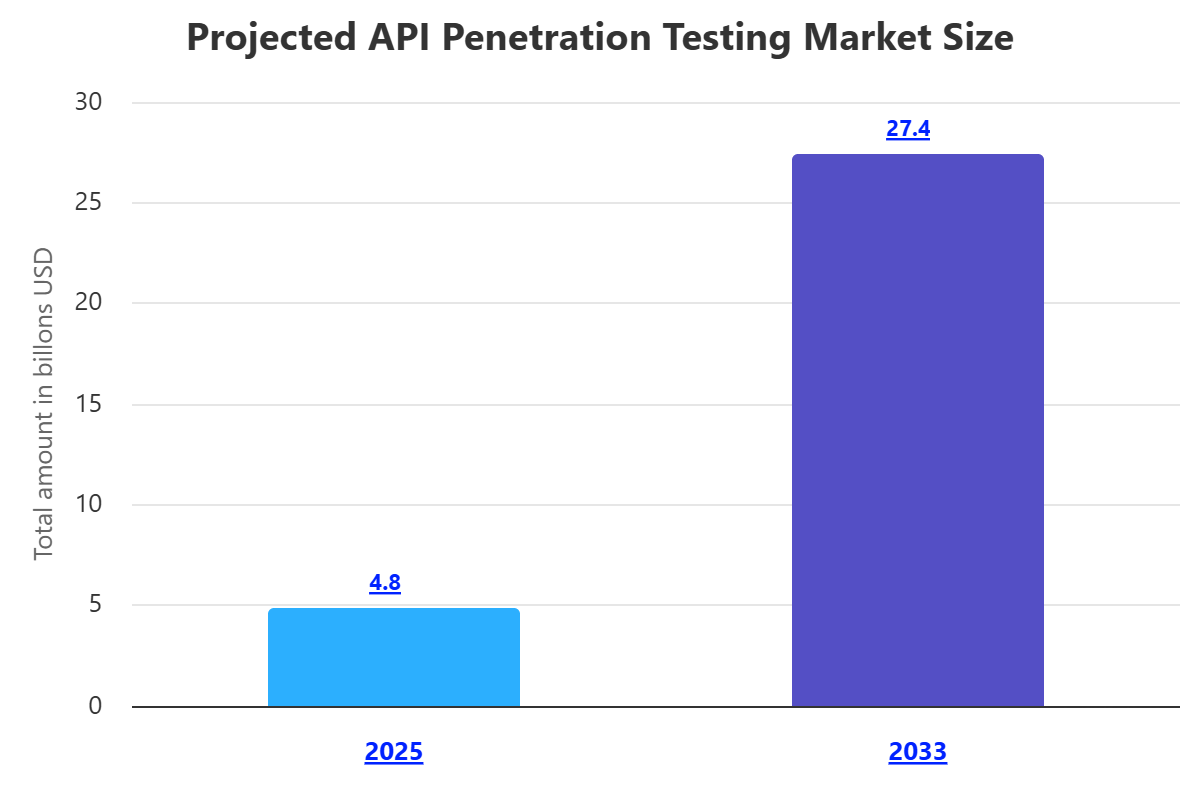
An increasing number of organizations are using APIs (Application Programming Interfaces) to connect services and transfer data. This has created a new attack surface that needs to be secured. API penetration testing is a specialized type of security testing that focuses on identifying vulnerabilities in APIs.
What Is API Penetration Testing?
API pen testing is like a special type of security test that checks for weak spots in APIs (Application Programming Interfaces). APIs are what apps use to talk to each other. Unlike normal web app pen testing, which looks at websites and how people use them, API pen testing goes deeper into how apps communicate, the way data is set up, and the logic behind how things work. It's like a pretend attack to see if someone could mess with data, stop services from running, or sneak into the system using an API. The point is to find problems before real bad guys do.
This process isn't just running a quick computer scan. It takes a mix of hands-on testing, special programs, and knowing a lot about how APIs work and where they're usually weak. Testers look closely at API instructions, the messages being sent back and forth, and how the API responds to figure out how it works and where someone could break in. They check things like login systems, permissions, how the API handles bad info, how it deals with errors, and what kind of data it shows. By finding these problems early, companies can fix them and be safer overall.
Basically, API pen testing gives a good look at how safe an API is. It helps companies see the real risks, not just the technical stuff, but also problems in how the API works that could cost them money or mess up their reputation. Doing this early is super important now because APIs are used for almost everything. They handle important info and keep businesses running.
What Are the Key Objectives of API Penetration Testing?
One big thing in API pen testing is checking the ways APIs talk to each other and the formats they use, like REST, SOAP, and GraphQL. Testers need to know how it works, how data is put together and taken apart, and what the dangers are with each one. This means looking at things like HTTP methods, headers, settings, and the info being sent to see if there are common weaknesses, like ways to inject bad code, problems with how data is handled, or easy ways to get to things they shouldn't. The goal is to make sure the API's communication is strong and can't be tricked.
API pen testing also focuses on finding problems in how the API works. These aren't just technical issues you can find with a computer scan. They come from mistakes in how the API's rules and processes are set up. For example, an API might calculate prices wrong, let someone skip the checkout, or allow actions that shouldn't be allowed based on the order of API calls. Finding these sneaky problems means really understanding how the API should work and thinking creatively to find ways to mess with it for bad reasons.
Why Is API Penetration Testing Important?
Because we use APIs for almost everything these days, API pen testing is a must for security. APIs connect everything, from internal systems to outside services and apps. If one API is weak, it can put everything at risk, causing big problems like data leaks that affect tons of users and stop businesses from running. Without good API pen testing, companies are basically blind to security issues and leaving important stuff open to attack.
Also, rules like GDPR, HIPAA, PCI DSS, and CCPA are pushing for stronger security to protect sensitive data. Since APIs often handle this data, doing API pen testing shows you're serious about security, which is needed to meet these rules. If you don't, you could get big fines, legal trouble, and a bad reputation. So, being proactive about API security isn't just smart, it's the law and the right thing to do.
APIs are always changing, so new weaknesses can pop up fast. Things like CI/CD pipelines can accidentally add security holes if they're not set up right. Regular API pen testing helps keep up with these changes and stay safe over time. It turns security into something you do all the time, not just once in a while, to protect against both old and new attacks.
How Does API Penetration Testing Work?
API pen testing usually starts with getting info and planning. Testers collect all the info they can, like API specs (like OpenAPI/Swagger), diagrams, and security rules. They try to understand how the API works, who uses it, what kind of data it deals with, and how it fits into the bigger system. They also decide what parts to test, find the important spots, and set goals. If you don't know what the API is supposed to do, testing it is much harder.
Next, they start looking for weaknesses. Testers use both computer programs and hands-on methods to check the API for common problems. They use special tools to send bad requests and watch how the API responds, looking for error messages that give away details about the system. They also try different kinds of attacks (like SQL, command, or XML external entity injection). They mess with settings, headers, and the info being sent to test if the API handles bad inputs correctly, has secure logins, controls access properly, and doesn't show too much data. The point is to check every possible way to interact with the API and find potential weaknesses.
Finally, they try to break in and write a report. Once they find weaknesses, testers try to use them to show what could happen. This proves the weakness is real and lets them see the potential damage, like getting unauthorized data, getting more permissions, or stopping the service from running. Then, they write a detailed report with all the weaknesses they found, how serious they are, how to repeat the steps, and clear advice on how to fix them. This helps the developers know what to fix and improve the API's security.
Core Methodology of API Penetration Testing
There are different types of API pen testing, each with a slightly different angle, but they often mix together. One common type is Black Box API Pen Testing. Here, the testers don't know anything about the API's insides, like the code or setup. They only see it from the outside, like a real attacker. This shows how an attacker with no special info would try to find weaknesses using only what's publicly available. It's hard, but it's good for finding easy-to-spot problems and checking external security measures.
On the other hand, White Box API Pen Testing gives testers full access to the API's insides, like the code, design documents, and maybe even the development environment. This allows them to check the API's security much better. Testers can look at the code for weaknesses, spot design flaws, and understand how the different parts work together. White box testing is great for finding complex problems, logic flaws, and sneaky errors that might be missed in a black box test. It takes more setup and teamwork, but it often gives better results.
There's also Grey Box API Pen Testing, which is becoming more popular. This is a mix of black box and white box testing. Testers get some info about the API, like its documentation, access to a test environment, or even some login info. This partial info helps them test faster by focusing on certain areas or skipping the initial login checks. It still shows how a real attack might work, where attackers get some internal info. Grey box testing is often seen as the most practical because it balances being thorough with being efficient, like many real-world attacks where attackers eventually learn some inside info.
Components of API Penetration Testing
API Pen Testing means checking several important things to make sure the security is really good. One key part is checking API spots and methods. This means testing every API spot (like /users, /products, /orders) and every HTTP method (GET, POST, PUT, DELETE, PATCH). Testers try each spot with good and bad inputs, looking for problems with how the API handles settings, injection weaknesses, and unexpected actions. The goal is to see how each function of the API acts with different requests and find any security holes in how it works.
Another important part is checking how logins and permissions work. This means really looking at how users and apps prove who they are (authentication) and what they're allowed to do (authorization). Testers try to get around the login process (like trying lots of passwords, messing with sessions, or using default logins), get higher permissions, and access things they shouldn't be able to see. This part is super important because if the login or permissions are weak, attackers could get wide-open access to important data and actions in the app.
Finally, it's important to check how the API handles data and deals with errors. APIs are supposed to handle different kinds of data, and it's important to check that data carefully to stop attacks (like SQL, NoSQL, or command injection), buffer overflows, and other data-related problems. Testers send bad data, very long inputs, and special characters to see how the API reacts. Also, good error handling is important. If error messages give away too much info about how the API works, it can help attackers. Testers look at error responses to make sure they don't show unnecessary details that could help someone attack.
Benefits of API Penetration Testing
There are lots of good things about doing API pen testing regularly for any company that uses APIs. The biggest thing is finding and fixing weaknesses before bad guys can use them. By pretending to be real attackers, pen testing finds security holes that computer scans might miss, including tricky logic problems and small errors. This lowers the chance of data leaks, service problems, and money losses, which protects the company's reputation and keeps customers happy.
Another big benefit is following rules and standards. Many rules, like GDPR, HIPAA, PCI DSS, and different cybersecurity laws, say you need strong security to protect sensitive data. Since APIs often handle this data, showing you're committed to API security with regular pen testing helps you meet these rules. This not only lowers the chance of getting big fines and legal problems but also shows auditors, partners, and customers that you care about security.
API pen testing also helps make your overall security stronger and improve how well your services work. By finding and fixing API weaknesses, you make the whole app system safer because APIs are often connected to everything. What you learn from pen testing can also help you write better code, design APIs more securely, and lower the chance of having new weaknesses in the future. This makes the whole team think about security, which leads to apps that are stronger and more trustworthy.

Challenges of API Penetration Testing
API pen testing is helpful, but it also has its challenges that testers and companies need to deal with. One big challenge is how complex and different APIs can be. APIs can have very different designs, protocols (REST, SOAP, GraphQL, gRPC), login methods (OAuth, JWT, API Keys), and data formats (JSON, XML, Protobuf). This means testers need to know a lot and change their methods for each API. There's no one-size-fits-all way to do it. Also, APIs that don't have good documentation or change quickly can make testing much harder and take more time.
Another common challenge is figuring out what to test and finding the most important attack spots. Apps often use lots of internal and external APIs, so it's not practical to test every single one the same way. Companies need to think about which APIs are most important, which ones handle sensitive data, and which ones are open to outside users. It's important to decide what to test, find all the important spots, and understand how APIs depend on each other. This makes sure the most important weaknesses are fixed without wasting time on less important areas.
Finally, fixing logic problems and making sure everything is covered can be hard. Unlike technical weaknesses that have clear signs, logic problems depend on how the app is supposed to work and can be hard to find. Testers need to understand the business side of the API and think creatively about how to mess with things to do things they shouldn't. Covering everything also takes a deep understanding of all the possible ways to use the API, including uncommon cases and error situations. This can take a lot of time and expertise from the pen testing team.
Best Practices for API Penetration Testing
To get the most out of API pen testing and make sure your security is strong, there are some good ways to do it. First, start by getting lots of info and thinking about threats. Before testing, really understand how the API works, what it does, how data moves, and what security it needs. Use the available documents (OpenAPI/Swagger specs), diagrams, and talk to the developers. Think about potential attacks and focus on the most important or exposed parts of the API. This helps guide the testing and makes it more effective.
Second, use both computer programs and hands-on testing. Computer scanners can quickly find common weaknesses and give a basic check, but they often miss logic problems, login bypasses, and chained attacks. Hands-on testing by skilled testers is important for finding these deeper problems. Testers can use special tools to make custom requests, mess with settings, and watch how the API acts, like real attackers. This mix of methods makes sure everything is covered and increases the chances of finding important problems.
Lastly, put API pen testing into the software development process and test regularly. Security shouldn't be an afterthought but a part of every step of API development. By testing early and often (like during development sprints, before big releases), companies can find and fix weaknesses more easily and cheaply. Also, retesting APIs often, especially after big changes or new releases, is important to stay safe against new threats and make the security last.
How ImmuniWeb Can Help with API Penetration Testing
Test your microservices and APIs for SANS Top 25 and OWASP API Security Top 10 vulnerabilities with ImmuniWeb® On-Demand API penetration testing. Just upload your API schema in a Postman, Swagger, GraphQL or another format, customize your API security testing requirements, schedule the penetration test date and get your pentest report.
We deliver every API penetration test with a contractual zero false positives SLA. If there is false positive in your API penetration testing report, you get the money back. Detect all vectors of privilege escalation, authentication bypass, improper access control, and other sophisticated business logic vulnerabilities in your APIs, both in a cloud environment and on-premise.
Our API penetration testing is provided with unlimited patch verification assessments, so your software developers can first fix the problems and then verify if the vulnerabilities have been properly remediated. Download your report in a PDF format or export the vulnerability data into your SIEM or WAF via our DevSecOps and CI/CD integrations. Enjoy 24/7 access to our security analysts may you have any questions or need assistance during the API penetration test.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.