In cybersecurity, doing penetration tests once a year (or even every few months) isn't good enough anymore to stay safe. IT systems change all the time, with new code, infrastructure updates, and constant new threats. That means we need to check our security more often and in a more flexible way. That's where Continuous Penetration Testing comes in.
What Is Continuous Penetration Testing?
Continuous Penetration Testing (CPT) means checking your security regularly and putting those checks right into how you build and run your systems. Unlike old-fashioned penetration tests that just happen once in a while, CPT is ongoing and changes as your system changes. The main idea is to find and fix problems as soon as they appear, so attackers have less time to cause trouble.
CPT uses both automatic tools and security experts. Automated tools watch your system for new things, changes, and known problems. Then, the experts look closely at the things the tools find, trying to break into the system in complex ways and find problems that the tools can't see.
By making security testing part of how you build software and run your IT, CPT turns security into something that's always happening, not just a reaction to problems. It makes sure your security is always up-to-date, which is important for keeping your business safe.
Why Is Continuous Penetration Testing Important?
CPT is all about being flexible and changing with your system. It's not just a one-time check. Systems are always changing because of new code, infrastructure updates, and cloud services. So, CPT keeps looking for new problems and making sure old problems don't come back.
It's also important to use both automatic and manual testing. Automatic tools are fast and can check for common problems, but they can't find everything. Real people are needed to find complex problems and come up with creative ways to break into the system. CPT brings these two things together.
CPT also focuses on giving you quick, useful advice on how to fix problems. It's not enough to just find problems. You need to fix them fast. CPT systems give you alerts and reports with clear steps on how to fix the problems. This helps you fix problems early, which saves time and money.
Why Is Continuous Penetration Testing Important?
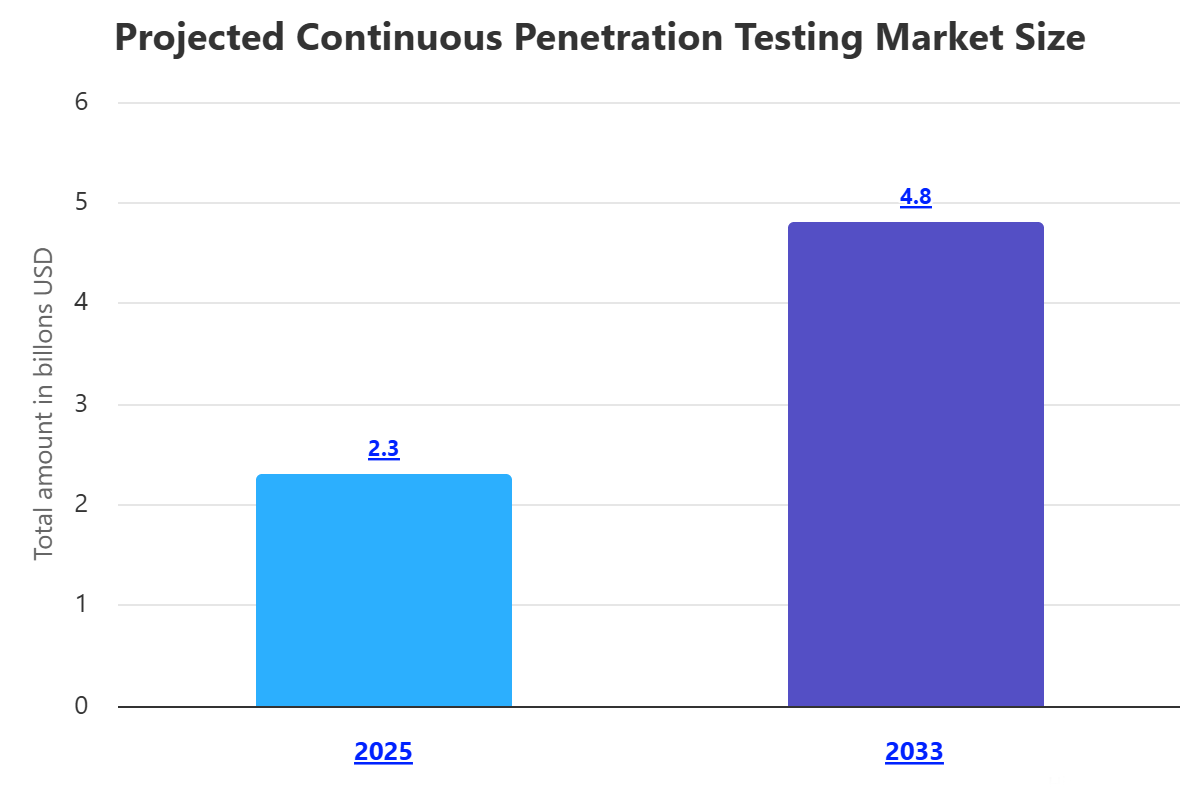
Continuous Penetration Testing matters a lot now because things are changing so fast in the digital world and cyber threats are getting worse. Before, you might test your security once or twice a year. But now, companies are updating their systems all the time. That means a security test from a few months ago might be useless. Attackers could find and use new problems before you even know they're there. CPT fixes this by constantly checking your security.
Also, data breaches are costing more and hurting companies' reputations. Cyberattacks can lead to fines, lawsuits, lost customers, and downtime. CPT helps you defend against these attacks by finding and fixing security problems before attackers can use them. By making your system safer, CPT lowers the chance of an attack and reduces the damage if one happens.
Finally, CPT helps you follow the rules and prove that you're doing your best to protect your system. Many rules and standards require regular security checks. CPT gives you a way to meet these requirements and show that you're serious about security. It builds trust with customers, partners, and auditors by showing that you're taking steps to manage cyber risks.
How Does Continuous Penetration Testing Work?
CPT usually works in a loop. First, it constantly looks for new things in your system. Instead of just checking once, CPT tools watch your system for new parts, changes, open ports, and leaked passwords. These tools scan your networks, watch code websites, and check DNS records and SSL certificates. This makes sure that the testing covers everything.
Once it finds new things and changes, it automatically scans for problems and decides what's most important. The automated tools quickly check for known problems and common mistakes. Then, they sort the problems by how serious they are and how much damage they could cause. This helps you focus on the most urgent issues.
The key part of CPT is that it also involves real people doing manual penetration testing. Experts look at the high-priority problems and new changes and try to break into the system. They look for complex problems that the automated tools can't find. This makes sure that nothing gets missed.
Finally, CPT gives you reports and advice in real time so you can fix problems quickly. The reports tell you exactly what the problems are and how to fix them. This creates a loop of finding problems, fixing them, and testing again to make sure they're really gone.
Types of Continuous Penetration Testing
Continuous Penetration Testing can focus on different parts of your system. Here are some common types:
Continuous Web Application and API Penetration Testing: This checks the security of your websites and the APIs they use. It involves automated scans for common web problems, plus manual testing by security experts who look for complex issues as you add new features or update code.
Continuous Network Penetration Testing: This focuses on your network, both inside and outside your company. It watches for new devices, open ports, and problems in network protocols. Experts try to move around inside the network and break through the defenses to find new attack paths.
Continuous Cloud Penetration Testing: If you use cloud services, this type of CPT is important. It checks for mistakes in how your cloud is set up, problems in cloud services, and insecure settings. It makes sure that you're keeping your part of the cloud secure.
What Makes Up Continuous Penetration Testing?
A good CPT program has several parts that work together:
Continuous Attack Surface Management (ASM) and Discovery Engine: This part constantly scans your system to find everything that's connected to it, even things you might not know about. It finds new domains, IPs, cloud instances, and leaked passwords.
Automated Vulnerability Scanning and Analysis Platform: This uses tools to automatically scan your system for known problems and mistakes. These tools are fast and can cover a lot of ground. They also sort the problems to help you focus on the most important ones.
Human-Driven Penetration Testing and Expert Validation: This is what makes CPT better than just automated scanning. Skilled security experts do manual testing to find complex problems and explore potential attacks. They also check the results of the automated scans to make sure they're accurate.
Integrated Reporting and Remediation Workflows: This gives you clear, useful reports and helps you fix problems quickly. It often includes ways to re-test after you've fixed something to make sure it's really gone.
What Are the Benefits of Continuous Penetration Testing?
Using Continuous Penetration Testing has many benefits for your cybersecurity:
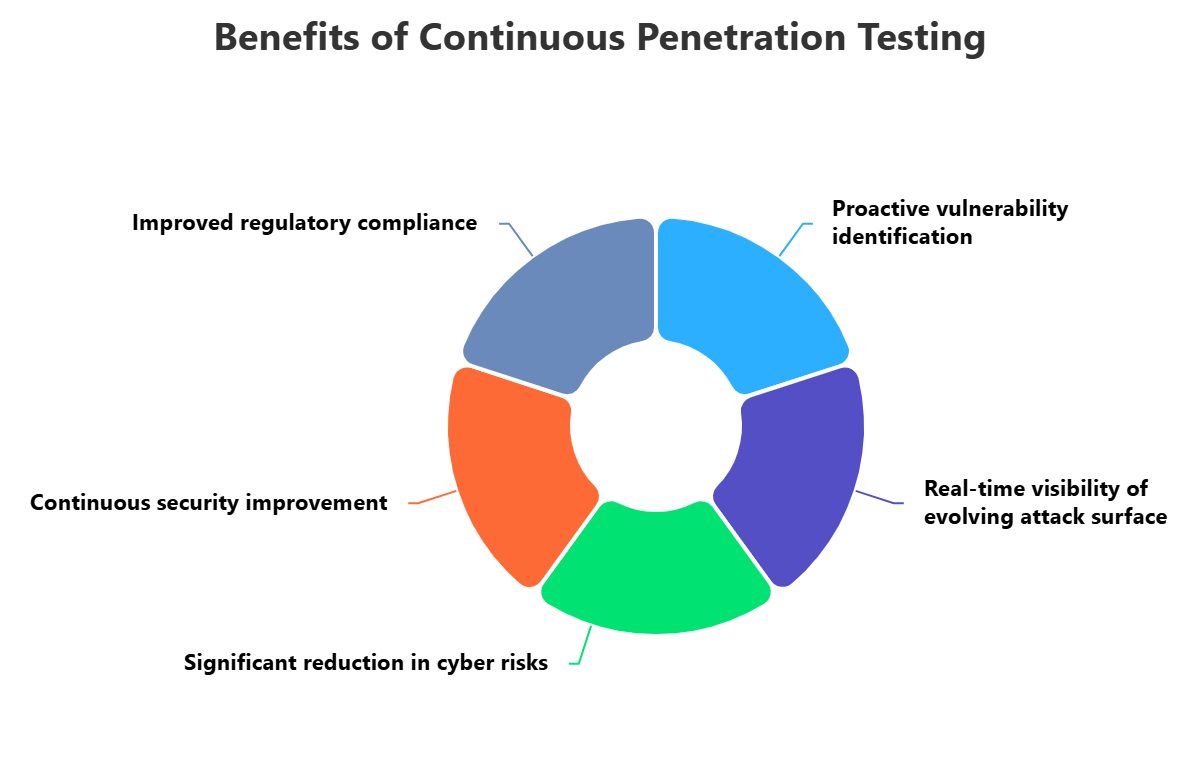
It gives you real-time visibility into your system and helps you find problems early. Traditional tests quickly become outdated, but CPT constantly watches for new things and changes. This lets you fix problems before attackers can use them.
It reduces cyber risks and the chance of successful attacks. By constantly checking for weaknesses and giving you quick advice, CPT helps you stay ahead of attackers. It makes your system stronger and protects your data.
It improves your security culture and makes it easier to meet compliance requirements. CPT helps you build security into your development processes, so you create more secure code from the start. It also gives you proof that you're checking your security regularly, which helps you meet rules like GDPR, HIPAA, and PCI DSS.
What Are the Challenges of Continuous Penetration Testing?
While CPT has many benefits, it also has some challenges:
It can be hard to fit CPT into your existing processes. Modern IT systems are always changing, so it takes planning and expertise to add continuous security testing without slowing things down.
It can be hard to manage all the findings and avoid alert fatigue. CPT can generate a lot of reports and alerts, so you need to be able to sort through them and focus on the most important ones.
It can be expensive and require specialized expertise. CPT requires experienced security professionals to set up, monitor, and do the manual testing. This can be a challenge for companies with limited resources or a shortage of skilled penetration testers.
What Are the Best Practices for Continuous Penetration Testing?
To get the most out of Continuous Penetration Testing, follow these best practices:
Clearly define what you're testing and how you're managing your system. Know which assets, applications, and networks are included in the testing, and keep this list updated. Have clear rules and get permission before testing to avoid causing problems.
Use a mix of automated tools and expert human testers. Automatic tools are good for finding common problems, but human testers are needed for complex issues.
Create a security-focused culture with continuous advice and clear steps for fixing problems. Add security testing to your development processes so you can find and fix problems early. Provide clear instructions on how to fix the problems, and re-test to make sure the fixes work.
How ImmuniWeb Can Help with Continuous Penetration Testing?
Outperform traditional penetration testing with 24/7 continuous penetration testing by ImmuniWeb® Continuous offering. We rapidly detect new code, functionalities or features in your web applications and APIs and then test the changes for security vulnerabilities, compliance or privacy issues in real time. Once a security issue is identified and confirmed, you will be immediately alerted by email, SMS or phone call in case of emergency.
For all customers of continuous penetration testing, we offer a contractual zero false positives SLA and money-back guarantee: if there is a single false positive on your continuous penetration testing dashboard, you get the money back. Our award-winning technology and experienced security experts reliably detect SANS Top 25 and OWASP Top 10 vulnerabilities, including the most sophisticated ones that may require chained or otherwise untrivial exploitation.
Leverage our integrations with the leading WAF providers for instant virtual patching of the discovered vulnerabilities. Request to re-test any finding with one click. Ask our security analysts your questions about exploitation or remediation of the findings at no additional cost. Get a customizable live dashboard with the findings, download vulnerabilities in a PDF or XLS file, or use our DevSecOps integrations to export the continuous penetration testing data into your bug trackers or SIEM.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











