Data is the most important thing a company has these days. It powers what they do, helps them come up with new ideas, and guides how they make choices. This includes everything from customer info to secret company plans, money records, and ways to get ahead of the competition.
Keeping this data safe is a big task because there's so much of it, it's kept in many different places (like clouds, apps, and computer systems), and lots of people need to get to it. Old ways of protecting data aren't enough because they don't give a full view of the risks in real time.
That's where Data Security Posture Management (DSPM) comes in. It's a new way to keep an eye on a company's data security, making sure sensitive info is safe no matter where it is.
What is Data Security Posture Management (DSPM)?
DSPM is all about knowing what sensitive data a company has, where it is, who can see it, and how secure it is across all its systems. It's better than older tools because it gives a complete, up-to-date view of data risks. It finds data, sorts it, checks who can get to it, looks for weak spots, and makes sure everything follows the rules in clouds, regular computer systems, and everything in between. DSPM wants to answer questions like: Where's our data? What kind of data is it? Who can use it? How well are we protecting it?
DSPM helps make sense of data that's spread all over the place. Companies use many clouds and apps, and have tons of data that isn't organized, so it's hard to keep track of everything and know the risks. DSPM pulls data from different spots – like cloud programs, computer settings, and security tools – to create a list of all data and its risks. This helps security teams spot hidden data (stuff they didn't know they had), poorly set up systems, too much access, and unusual activity that could mean there's a problem.
In the end, DSPM lets companies stop just reacting to problems and start focusing on protecting their data first. By always watching data security, teams can find and fix risks before they cause trouble. This means spotting data that could be exposed, keeping up with privacy rules, and getting ideas on how to beef up data protection. This keeps the company's most important info safe and keeps customers trusting them.
Key Aspects of DSPM
DSPM has a few important parts that make it a good way to protect data. First, it's always finding and sorting data. DSPM programs automatically check and find all data in a company's different systems (clouds, apps, computers). Then, they sort the data based on how sensitive it is and what rules apply to it. This constant checking and sorting is key to knowing what data you have and where it is, which is the first step in protecting it.
Next, controlling who can get to data and spotting anything unusual are very important. DSPM doesn't just look at access lists. It checks who can get to what data, how they got access, and if they're really using it. It finds things like open storage, too much access, old access, and strange data activity that could mean someone inside is causing trouble or an account has been hacked. By knowing who really has access to data, DSPM helps companies make sure only the right people have access and find suspicious activity fast.
Finally, knowing what risks are most important and how to fix them is a big part of what DSPM offers. DSPM tools don't just show a list of problems. They connect the problems to how sensitive the data is, how exposed it is, and what rules apply to it to figure out the real risk. This helps security teams fix the most important problems first. DSPM also gives clear advice on how to fix things, like changing settings, taking away access, and making data protection stronger. This helps fix risks quickly and in the right places.
Why is DSPM Important?
DSPM is very important now because there's so much data, it's in so many places, and there are more and more data breaches. Old security methods don't work when data is everywhere. DSPM is key because it gives the full view and constant checking needed to know and handle data risks across all these different places. This makes sure sensitive info is safe no matter where it is.
DSPM also helps make sure companies follow all the new data privacy rules. There are laws that say how sensitive data must be handled. DSPM helps find where this data is, who can see it, and if it's being protected the right way. This helps companies find and fix problems before they lead to big fines or legal trouble.
Besides following rules and protecting data, DSPM also helps companies handle problems better and reduce the harm from data breaches. By knowing what data they have and the risks, security teams can quickly find out what data was exposed in a breach, who had access, and where it is. This helps them stop the breach, tell the right people, and get things back to normal faster, which reduces the money lost, the problems caused, and the damage to the company's reputation.
How Does DSPM Work?
DSPM works by using a step-by-step plan to give a full view of data risks and how to handle them.
First, it finds and lists all data across all systems. DSPM programs connect to different data spots, like clouds, apps, databases, and computer files. They automatically check these systems to find all data storage, how they're set up, and the data inside them. This creates a full and up-to-date list of all data, including data that's often missed.
Next, the data is sorted into sensitive types, and access is checked. DSPM tools use smart ways to find and tag sensitive data, like personal info, payment card data, health info, company secrets, and private business info. At the same time, DSPM checks who can get to what data, how they got access, and if the access is too much or not set up right.
Finally, DSPM figures out the risks, decides what's most important, and gives advice on how to fix things. By connecting data sensitivity, access settings, and known weak spots, DSPM comes up with a risk score for each piece of data. This helps security teams focus on the most important risks. The program then gives clear advice on how to fix things, like taking away too much access, fixing storage that isn't secure, or using better encryption. DSPM often works with other security and computer programs to make it easier to fix things and keep improving data security.
Types of DSPM
DSPM usually focuses on the main purpose or how the program is set up, depending on what the company needs and what its data looks like.
One type focuses on Cloud Data Security. Since many companies use cloud services, some DSPM programs focus on finding, sorting, and securing data in cloud systems. These programs work closely with cloud services to watch settings, find problems, spot too much access, and track data as it moves in the cloud.
Another type focuses on SaaS Data Security. Companies use apps for important work, so a lot of sensitive data is in these programs. This type of DSPM focuses on seeing the data in these apps, knowing who can get to it, spotting data leaks, and following data rules in these systems.
Some DSPM programs offer Hybrid/Multi-Environment Data Security. These programs try to give a full view of data risks across all systems, including clouds, apps, and computer centers. They work with many data sources and security tools to offer a complete list of data, how it's sorted, and how risky it is, no matter where the data is.
Components of DSPM
A good DSPM system has a few important parts that work together to give a full view of data security.
The first part is the Data Finding and Sorting Tool. This tool constantly checks and finds all data storage in a company's systems. Then, it uses smart ways to automatically sort data based on how sensitive it is, what rules apply to it, and how important it is to the business. This part creates and keeps an up-to-date list of sensitive data, which is the base of any data security plan.
Next, a strong Data Access Control and Activity Watching Tool is key. This tool checks who can get to what data, how they got access, and if the access is too much. It also watches how data is used, spotting strange activity, unauthorized data moves, or suspicious searches that could mean there's a breach or a problem inside. By knowing who can access and who is accessing data, this tool helps make sure only the right people have access and gives important info about possible data exposure.
Finally, the Risk Check, Priority, and Fixing Plan is the result of DSPM. This part connects data sensitivity, access settings, and weak spots to come up with a risk score for each piece of data. Then, it gives easy-to-understand reports that show the highest-risk data, along with clear advice on how to fix things. This part often works with other computer and security tools to make it easier to fix problems and keep improving data security.
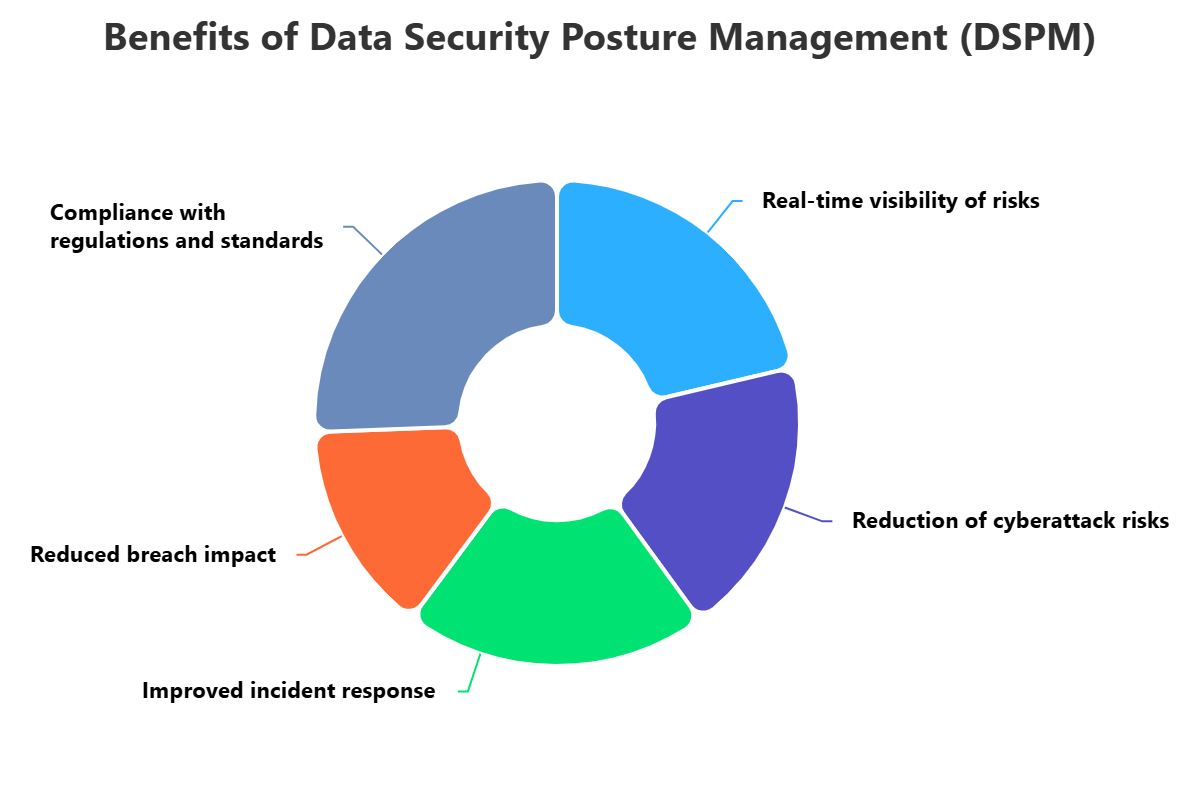
Benefits of DSPM
Using a good DSPM program offers many benefits for companies dealing with complex data. A main benefit is a full, real-time view of sensitive data risks. By automatically finding, sorting, and constantly watching data in all systems, DSPM gets rid of blind spots. This helps security teams know where their sensitive data is, who can get to it, and what problems it has, which helps them handle risks before problems happen.
DSPM also makes data privacy and following rules much easier. With many data protection laws, companies need to show they're following the rules. DSPM helps find where regulated data is stored, checks if it's being protected right, and finds any problems. This helps prevent fines, legal trouble, and damage to the company's reputation.
Besides following rules, DSPM also helps handle problems better and reduces the impact of breaches. If there's a security problem, knowing what sensitive data was affected is very important. DSPM's real-time list and access checks help security teams quickly find out the scope of the breach, what data was affected, and speed up getting things back to normal. This reduces the overall impact of a security problem, protecting money and customer trust.
Challenges of DSPM
Even though DSPM has many benefits, using and keeping a good DSPM program has its own challenges. One big problem is the amount of data that companies create and store. Connecting to, finding, and constantly sorting all this data across many clouds, apps, and computer systems can be hard, requiring strong and scalable DSPM programs.
Another problem is sorting data right and knowing what risks are most important. DSPM tools use AI, but finding and tagging all sensitive data, especially in data that isn't organized, can be wrong. Also, connecting data sensitivity with access, problems, and exposure to come up with a useful risk score takes deep knowledge of the company's work and data, which can be hard to do automatically.
Finally, working DSPM into current security and computer systems can be hard. DSPM uses data from different spots, and fixing problems often takes action from different teams. Making sure data flows right, work is automated, and teams work together can be hard. Getting people to accept change and setting clear ownership for data security is key to DSPM's success.
Best Practices for DSPM
To get the most out of DSPM, companies should follow a few best practices. First, start by knowing your data and what's most important to your business. Before using a DSPM program, find out what your most important data is, where it is, and how it helps your business. This will help you set up the DSPM tool right, focus its efforts, and make sure fixing problems focuses on the data that matters most.
Next, focus on always finding and sorting data across all systems. Manual data lists don't work. Use DSPM to constantly check and sort data in all your clouds, apps, and computer storage. Make sure the sorting tool is set up to find sensitive data types that are important to your business and the rules you need to follow. This constant view is key to finding hidden data and keeping an up-to-date list of your sensitive info.
Finally, focus on useful info, risk priority, and easy fixing plans. DSPM should do more than just find problems. Use the DSPM platform's risk scores to focus on the riskiest data first. Work DSPM findings into your current computer and security platforms to automate fixing tasks. Encourage teamwork between security, data owners, and operations teams to make sure data security problems are understood, prioritized, and fixed, leading to constant improvement in your data security.
How ImmuniWeb Can Help with Data Security Posture Management (DSPM)?
ImmuniWeb Discovery provides a powerful and complementary set of capabilities that significantly contribute to an organization's Data Security Posture Management (DSPM) efforts, particularly through its focus on external attack surface management and dark web intelligence. While not a standalone DSPM platform, ImmuniWeb's AI-powered External Attack Surface Management (EASM) continuously discovers and monitors an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services. This is crucial for DSPM as it helps identify publicly exposed data stores (e.g., misconfigured S3 buckets, open databases) that could contain sensitive information, providing a critical external view of data risk.
Furthermore, ImmuniWeb's Dark Web and Cyber Threat Intelligence (CTI) monitoring directly contributes to DSPM by identifying instances where an organization's sensitive data, credentials, or intellectual property may have already been compromised and leaked onto the dark web, hacker forums, or other illicit marketplaces. This proactive intelligence allows organizations to understand if their data is already at risk of exposure, enabling immediate incident response actions and helping to pinpoint potential internal or third-party data leakage points that DSPM can then help to secure.
ImmuniWeb's capabilities also extend to vulnerability assessment and penetration testing of applications and APIs that interact with sensitive data. By identifying security flaws in these interfaces, ImmuniWeb helps prevent unauthorized access to backend data stores. The insights gained from ImmuniWeb's continuous monitoring and security testing can be fed into a broader DSPM solution, enriching its understanding of data risk by providing context on external exposures and application-layer vulnerabilities. This combined approach empowers organizations to gain a more comprehensive and actionable understanding of their data security posture, from external threats to internal configurations.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











