Canada Personal Information Protection and Electronic Documents Act (PIPEDA) Compliance
The Canadian Personal Information Protection and Electronic Documents Act (PIPEDA) governs how private-sector
organizations collect, use, and disclose personal data, requiring consent, safeguards,
and accountability while granting individuals access and correction rights.
Canada's Personal Information Protection and Electronic Documents Act (PIPEDA), enacted in 2000, serves as the primary federal law governing the collection, use, and disclosure of personal information in the course of commercial activities by private sector organizations. Its fundamental purpose is to balance an individual's right to privacy with the need of organizations to collect, use, and disclose personal information for legitimate business purposes.
While often compared to its European counterpart, GDPR, PIPEDA operates within a uniquely Canadian legal and regulatory framework, continually evolving to address new technological challenges.
Overview of Canada Personal Information Protection and Electronic Documents Act (PIPEDA)
PIPEDA is based on 10 Fair Information Principles, which are essentially a code of conduct for how organizations should handle personal information. These principles emphasize transparency, accountability, and individual control:
- Accountability: Organizations are responsible for personal information under their control and must designate an individual accountable for compliance.
- Identifying Purposes: The purposes for which personal information is collected must be identified at or before the time of collection.
- Consent: The knowledge and consent of the individual are required for the collection, use, or disclosure of personal information, with some exceptions.
- Limiting Collection: The collection of personal information must be limited to that which is necessary for the purposes identified by the organization.
- Limiting Use, Disclosure, and Retention: Personal information can only be used or disclosed for the purposes for which it was collected, except with consent or as required by law, and must be retained only as long as necessary.
- Accuracy: Personal information must be as accurate, complete, and up-to-date as is necessary for the purposes for which it is to be used.
- Safeguards: Personal information must be protected by security safeguards appropriate to the sensitivity of the information.
- Openness: Organizations must make readily available to individuals specific information about their policies and practices relating to the management of personal information.
- Individual Access: Upon request, an individual must be informed of the existence, use, and disclosure of their personal information and given access to that information. Individuals can also challenge the accuracy and completeness of the information and have it amended.
- Challenging Compliance: An individual can challenge an organization's compliance with these principles.
PIPEDA also includes provisions for electronic documents, facilitating the use of electronic means to communicate or record information or transactions.
Key Aspects of Canada Personal Information Protection and Electronic Documents Act (PIPEDA) Compliance?
PIPEDA compliance is rooted in the 10 Fair Information Principles, with specific technical considerations for each.
- Personal Information Definition:
- Technical Details: "Personal information" is broadly defined as information about an "identifiable individual." This includes factual or subjective information, recorded or not, such as name, age, income, ethnic origin, blood type, opinions, evaluations, comments, disciplinary actions, employee files, credit records, loan records, medical records, IP addresses, cookie data, and device identifiers. It's crucial to understand that even seemingly innocuous data, when combined, can become personal information.
- Technical Implementation: Organizations need robust data discovery and classification systems to identify where all personal information resides across their IT infrastructure (databases, file shares, cloud services, web applications, mobile apps, logs). This includes data mapping to understand data flows and the purpose of collection for each type of data.
- Consent (Principle 3):
- Technical Details: PIPEDA requires "meaningful consent," meaning individuals must understand what they are consenting to. Consent can be express (e.g., ticking a box) or implied (e.g., providing an address for delivery). The Office of the Privacy Commissioner of Canada (OPC) emphasizes that consent must be obtained at or before the time of collection. For sensitive information, express consent is usually required. Individuals must also be able to withdraw consent.
- Technical Implementation:
- Consent Management Platforms (CMPs): For websites and mobile applications, CMPs are essential to present clear, understandable consent requests (e.g., cookie banners, privacy policy links), capture consent choices (opt-in/opt-out for various data uses), and record those choices.
- User Preference Centers: Providing users with dashboards or settings where they can review and modify their consent preferences.
- Integration with Data Processing Systems: Ensuring that consent preferences are technically enforced by backend systems, preventing the use or disclosure of personal information for purposes for which consent has not been given or has been withdrawn.
- Safeguards (Principle 7):
- Technical Details: This is the most technically demanding principle. PIPEDA requires organizations to protect personal information with "security safeguards appropriate to the sensitivity of the information." This implies a risk-based approach, meaning more sensitive information requires stronger safeguards. The OPC recommends:
- Physical measures: Restricted access to offices and filing cabinets.
- Organizational measures: Security clearances, limiting access on a "need-to-know" basis, employee training.
- Technological measures: Passwords, encryption, firewalls, up-to-date security patches.
- Technical Implementation:
- Encryption: Implement strong encryption at rest (e.g., database encryption, file system encryption, cloud storage encryption like AES-256) and in transit (e.g., TLS 1.2+ for all web and API communications, secure VPNs for remote access). Secure key management is critical.
- Access Controls: Enforce Role-Based Access Control (RBAC) to ensure least privilege. Implement Multi-Factor Authentication (MFA) for all internal and external access to systems containing personal information, especially privileged accounts. Utilize Privileged Access Management (PAM) solutions.
- Vulnerability Management & Penetration Testing: Conduct regular (e.g., quarterly) vulnerability scans and annual penetration tests of web applications, mobile applications, APIs, and network infrastructure that collect, process, or store personal information. This identifies technical weaknesses.
- Secure Development Lifecycle (SSDLC): Integrate security into the software development process, including Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) for custom applications.
- Logging and Monitoring: Implement comprehensive logging across all systems that interact with personal information. Utilize Security Information and Event Management (SIEM) systems for real-time analysis, anomaly detection, and alerting on suspicious activities.
- Secure Disposal: Implement technical procedures for the secure erasure or destruction of electronic media containing personal information when it is no longer needed (e.g., NIST SP 800-88 guidelines for media sanitization).
- Technical Details: This is the most technically demanding principle. PIPEDA requires organizations to protect personal information with "security safeguards appropriate to the sensitivity of the information." This implies a risk-based approach, meaning more sensitive information requires stronger safeguards. The OPC recommends:
- Data Breach Notification (Mandatory since 2018):
- Technical Details: Organizations are required to report to the OPC and notify affected individuals about any breach of security safeguards involving personal information under their control if it is reasonable to believe that the breach creates a "real risk of significant harm" to an individual. They must also keep records of all data breaches.
- Technical Implementation: Requires robust incident detection and response capabilities, including Security Information and Event Management (SIEM) systems, Intrusion Detection/Prevention Systems (IDS/IPS), and endpoint detection and response (EDR) tools. An effective incident response plan must define technical steps for containment, eradication, recovery, and forensic analysis to determine the scope and impact of a breach.
- Individual Access (Principle 9):
- Technical Details: Organizations must provide individuals with access to their personal information and the ability to challenge its accuracy.
- Technical Implementation: Requires a Data Subject Access Request (DSAR) portal or equivalent mechanism. This system must be able to securely authenticate the individual, search across various data repositories, retrieve all relevant personal information, and present it in an intelligible format (e.g., PDF, CSV). Secure data transfer mechanisms must be used.
- Accountability and Openness (Principles 1 & 8):
- Technical Details: While primarily organizational, these principles have technical implications. Accountability requires designating a privacy officer and having policies and procedures in place, which often include technical guidelines. Openness requires transparent communication about data handling, including a readily available privacy policy on websites.
- Technical Implementation: Publishing a clear and accessible privacy policy on websites and in applications. Maintaining documentation of security controls, data inventories, and incident response procedures.
Why Is Canada Personal Information Protection and Electronic Documents Act (PIPEDA) Compliance Important?
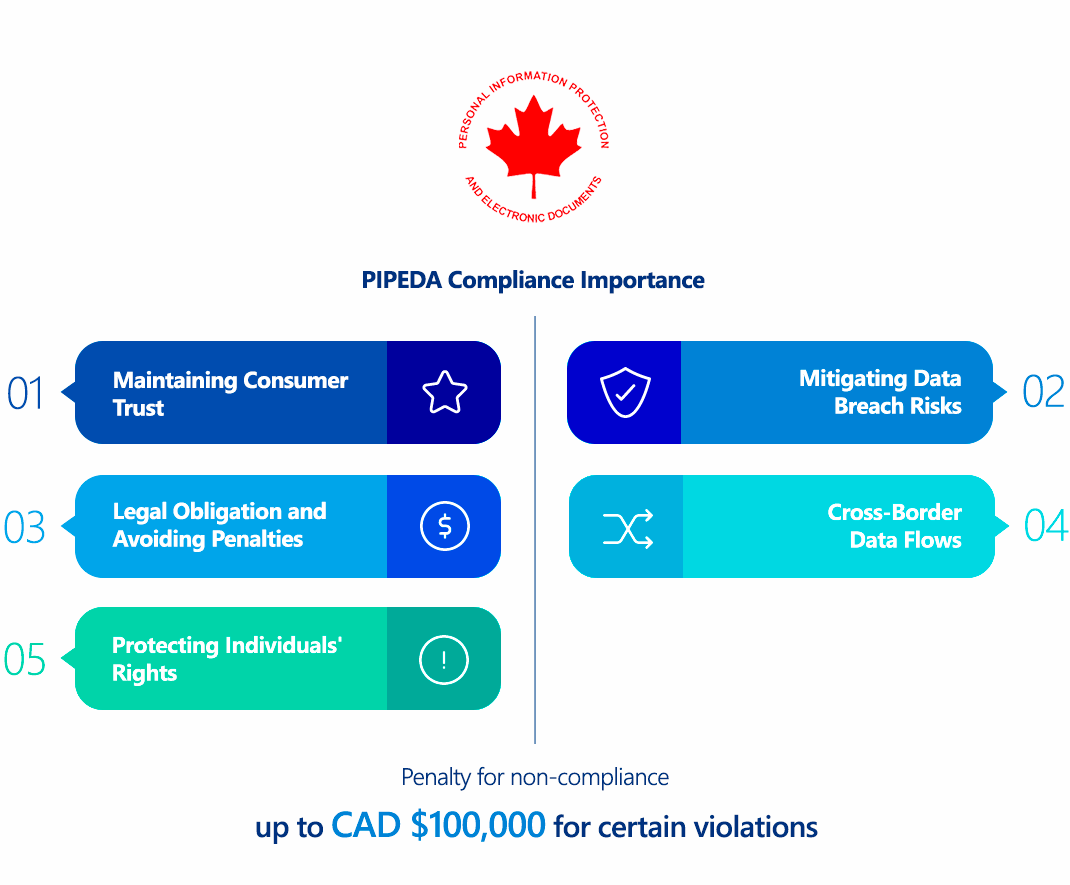
PIPEDA compliance is crucial for several reasons:
- Legal Obligation and Avoiding Penalties: It is a federal law. Non-compliance can lead to significant fines and public scrutiny from the Office of the Privacy Commissioner of Canada (OPC).
- Maintaining Consumer Trust: In an increasingly data-conscious world, adhering to privacy laws is essential for building and maintaining trust with Canadian consumers. Data breaches or misuse of personal information can severely damage an organization's reputation and lead to a loss of customers.
- Cross-Border Data Flows: PIPEDA is recognized by the European Union as providing an "adequate" level of protection for personal data, which facilitates the free flow of data between the EU and Canada. Non-compliance could jeopardize this adequacy status.
- Mitigating Data Breach Risks: The "safeguards" principle encourages organizations to adopt robust cybersecurity practices, which inherently reduces the likelihood and impact of costly data breaches.
- Protecting Individuals' Rights: At its core, PIPEDA empowers individuals with control over their personal information, helping to prevent identity theft, fraud, and other harms associated with data misuse.
Who Needs to Comply with Canada Personal Information Protection and Electronic Documents Act (PIPEDA)?
PIPEDA generally applies to private sector organizations across Canada that collect, use, or disclose personal information in the course of commercial activities.
This includes:
- All federally regulated organizations that conduct business in Canada (e.g., banks, airlines, telecommunications companies, inter-provincial transportation companies) are always subject to PIPEDA, including in respect of their employee personal information.
- Organizations that conduct commercial activities involving personal information across provincial or national borders.
- Organizations that collect, use, or disclose personal information within a province that does not have its own privacy laws deemed "substantially similar" to PIPEDA.
- Even organizations located outside Canada must comply with PIPEDA if they collect, use, or disclose the personal information of individuals in Canada in the course of a commercial activity (e.g., an international e-commerce website selling to Canadian consumers).
Exceptions:
- Provincial Laws: PIPEDA generally does not apply to organizations that collect, use, or disclose personal information entirely within provinces that have their own private-sector privacy laws deemed "substantially similar" to PIPEDA (currently Quebec, Alberta, and British Columbia). However, if data crosses provincial or international borders, PIPEDA still applies.
- Not-for-profit organizations, political parties, and charitable organizations are generally exempt from PIPEDA as long as their activities are not considered "commercial."
- Government institutions are subject to the Privacy Act (federal) or provincial public sector privacy legislation, not PIPEDA.
- Personal Use: Individuals collecting, using, or disclosing personal information solely for personal, domestic, or household purposes are exempt.
- Journalistic, Artistic, or Literary Purposes: Collection, use, or disclosure of personal information solely for these purposes is exempt.
Canada Personal Information Protection and Electronic Documents Act (PIPEDA) vs GDPR Comparison
While PIPEDA and GDPR both aim to protect personal data, they have distinct origins, scopes, and technical nuances:
| Aspect | PIPEDA (Canada) | GDPR (EU) |
|---|---|---|
| Philosophical Basis | Principle-based (10 FIPs), emphasizing balancing privacy rights with business needs. | Rights-based, focusing on fundamental right to privacy for individuals. |
| Scope | Private sector, commercial activities, federal works/undertakings. Has extraterritorial reach for data of individuals in Canada. | Broader, applies to all entities processing "personal data" of EU residents globally. |
| Data Definition | "Personal information" about an identifiable individual (broad). | "Personal data" (broad, includes direct/indirect identifiers). |
| Sensitive Data | Not explicitly defined as a separate category, but "sensitivity" determines required safeguards. | "Special categories of personal data" (e.g., health, genetic, biometric) with stricter rules. |
| Legal Basis for Processing | Primarily consent for collection, use, disclosure. Exceptions for legal/security/emergency. | Requires a specific legal basis for all processing (consent, contract, legal obligation, vital interest, public task, legitimate interest). |
| Consent Model | Allows for both express and implied consent, depending on sensitivity and reasonable expectation. Explicit consent required for sensitive data or high-risk uses. | Generally requires explicit, unambiguous, opt-in consent for most processing, especially sensitive data. |
| Data Subject Rights | Access, Correction, Challenging compliance. (Limited right to data portability, not explicit "right to be forgotten"). | More extensive: Access, Rectification, Erasure (Right to be Forgotten), Restriction of Processing, Data Portability, Object, Rights re. Automated Decision-Making. |
| Data Breach Notification | Mandatory notification to OPC and individuals if "real risk of significant harm." Records of all breaches required. | Mandatory notification to supervisory authorities within 72 hours; individuals notified "without undue delay" if high risk. |
| Data Protection Officer (DPO) | Mandates designation of individual accountable for compliance (Privacy Officer), but not necessarily a formal DPO role. | Mandatory for specific organizations (public bodies, large-scale sensitive data, systematic monitoring). |
| Data Protection Impact Assessment (DPIA) | Not explicitly mandated, but implied by "accountability" and "safeguards" principles for high-risk activities. | Mandatory for high-risk processing activities. |
| Cross-Border Data Transfer | Emphasis on accountability, contractual obligations for transfers. Deemed "adequate" by EU. | Strict rules, requiring "adequacy decision" or specific safeguards (e.g., SCCs, BCRs). |
| Enforcement Body | Office of the Privacy Commissioner of Canada (OPC). | Data Protection Authorities (DPAs) in each EU member state. |
| Penalties | Up to CAD $100,000 for specific violations (e.g., failure to report breach, destroy records). OPC can issue compliance orders. Private right of action limited. | Higher, up to €20 million or 4% of annual global turnover, whichever is higher. |
| Reform (Bill C-27) | Bill C-27 (Digital Charter Implementation Act, 2022) proposed significant amendments to PIPEDA (CPPA, AIDA). While its future is uncertain, it aims to introduce a new privacy statute (CPPA) and an AI Act, aligning more closely with GDPR in some aspects (e.g., increased penalties, more detailed rights, DPA-like powers). As of current status, Bill C-27's CPPA provisions are not yet law, and PIPEDA remains the primary federal private-sector privacy law. | Ongoing revisions and guidance. |
While PIPEDA has similarities to GDPR, particularly in its principles, its enforcement mechanisms and the specifics of consent and individual rights differ. Organizations compliant with GDPR will have a strong foundation for PIPEDA, but must address Canadian nuances.
How to Ensure Canada Personal Information Protection and Electronic Documents Act (PIPEDA) Compliance?
Ensuring PIPEDA compliance requires a systematic and technically grounded approach, directly addressing the 10 Fair Information Principles:
- Data Inventory and Mapping (Principles 1, 2, 5):
- Technical Action: Implement data discovery and classification tools to identify all instances of personal information across your entire digital environment (databases, file servers, cloud storage, CRM, ERP, web/mobile applications, logs, backups). Map the entire lifecycle of this data: where it's collected, how it flows, how it's used, who accesses it, and when it's disposed of. This supports "identifying purposes," "limiting collection," and "limiting use, disclosure, and retention."
- Implement Robust Safeguards (Principle 7):
- Technical Action: This is arguably the most critical technical aspect.
- Encryption: Mandate end-to-end encryption for all personal information. This means encryption at rest (e.g., full disk encryption, database encryption, encrypted cloud storage) and in transit (e.g., using TLS 1.2+ for all web traffic, secure API calls, SFTP, VPNs for remote access). Implement a robust Cryptographic Key Management System (KMS).
- Access Controls: Implement Role-Based Access Control (RBAC) based on the principle of least privilege. Enforce Multi-Factor Authentication (MFA) for all accounts accessing personal information, especially privileged accounts and customer-facing portals. Utilize Privileged Access Management (PAM) solutions to manage and monitor elevated access.
- Vulnerability Management & Penetration Testing: Conduct regular (e.g., quarterly) vulnerability scans and annual penetration tests of your external and internal networks, web applications, mobile applications, and APIs that handle personal information. This helps identify exploitable weaknesses and validates the effectiveness of other safeguards.
- Secure Development Lifecycle (SSDLC): Integrate security into your software development processes. This includes secure coding practices, Static Application Security Testing (SAST) for source code analysis, and Dynamic Application Security Testing (DAST) for testing running applications, to prevent vulnerabilities in custom applications.
- Logging and Monitoring: Implement comprehensive logging across all systems that store or process personal information. Deploy a Security Information and Event Management (SIEM) system to aggregate, correlate, and analyze logs in real-time, enabling rapid detection of unauthorized access or suspicious activities.
- Network Security: Deploy and properly configure firewalls, Intrusion Detection/Prevention Systems (IDS/IPS). Implement network segmentation to isolate sensitive data environments. Use Web Application Firewalls (WAFs) to protect web-facing applications.
- Secure Disposal: Develop and technically enforce policies for the secure destruction or de-identification of personal information when it is no longer needed, using methods like cryptographic erasure, secure wiping, or degaussing.
- Technical Action: This is arguably the most critical technical aspect.
- Consent Management (Principle 3):
- Technical Action: Implement a Consent Management Platform (CMP) that provides transparent, granular options for individuals to give or withdraw consent for different types of data processing. Ensure this CMP integrates with your data processing systems to dynamically adjust data collection and usage based on consent choices./li>
- Individual Access Request Fulfillment (Principle 9):
- Technical Action: Develop a secure, verifiable Data Subject Access Request (DSAR) portal or similar mechanism. This system should authenticate the requestor's identity, enable searches across identified data repositories, and securely deliver the requested personal information in an accessible format. Implement workflows for corrections and challenges./li>
- Breach Preparedness and Notification (Mandatory since 2018):
- Technical Action: Develop and regularly test a comprehensive incident response plan that outlines technical steps for breach detection (e.g., through SIEM alerts, IDS/IPS), containment, eradication, recovery, and forensic analysis. This plan must include clear procedures for assessing the "real risk of significant harm" and preparing the required notifications for the OPC and affected individuals in a timely manner./li>
- Third-Party Vendor Management (Principle 1):
- Technical Action: Conduct thorough technical security assessments and due diligence of any third-party service providers or cloud vendors who process personal information on your behalf. Ensure that contracts include provisions requiring them to maintain appropriate security safeguards and comply with PIPEDA's principles./li>
- Employee Training (Principle 1):
- Technical Action: Provide mandatory and recurring security awareness training for all employees, with specific technical training for IT and security teams. This training should cover secure data handling practices, phishing awareness, and procedures for reporting security incidents./li>
Consequences of Non-Compliance with Canada Personal Information Protection and Electronic Documents Act (PIPEDA)
Non-compliance with PIPEDA can lead to significant penalties and repercussions:
- Financial Penalties: The Office of the Privacy Commissioner of Canada (OPC) can recommend that the Federal Court order an organization to pay fines of up to CAD $100,000 for certain violations, such as failing to report a data breach or failing to keep records of breaches.
- Public Scrutiny and Reputation Damage: The OPC has the power to publicly disclose the findings of investigations, naming organizations found in non-compliance. This can lead to severe reputational damage, loss of customer trust, and negative media coverage.
- Compliance Orders: The OPC can issue compliance orders, compelling organizations to implement specific measures to address violations.
- Audits: The OPC can conduct audits of an organization's privacy management practices if there are reasonable grounds to believe the organization is not complying with PIPEDA.
- Federal Court Action: The OPC can apply to the Federal Court for an order against an organization. Individuals who have filed complaints with the OPC can also apply to the Federal Court for a hearing if they are dissatisfied with the OPC's findings or if the Commissioner decides not to investigate. The Court can order the organization to cease its non-compliant practices, publish notices of its actions, or pay damages to the complainant.
- Criminal Offenses: It is a criminal offense under PIPEDA to knowingly contravene certain provisions, such as destroying personal information subject to an access request or obstructing an OPC investigation. Penalties for criminal offenses can include fines or imprisonment.
While PIPEDA's direct monetary penalties are lower than GDPR's, the reputational damage and the potential for court orders and civil actions from affected individuals can be substantial.
How ImmuniWeb Helps Comply with Canada Personal Information Protection and Electronic Documents Act (PIPEDA)?
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides robust technical capabilities that directly support organizations in achieving and maintaining compliance with PIPEDA's stringent requirements, particularly those related to "Safeguards" (Principle 7) and data breach preparedness.
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By leveraging ImmuniWeb's capabilities, organizations can systematically identify and mitigate technical risks, strengthen their data security posture, and demonstrate their proactive commitment to protecting the personal information of Canadian individuals, thereby achieving and maintaining PIPEDA compliance.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
