Singapore Personal Data Protection Act (PDPA) Compliance
Personal Data Protection Act (PDPA) of 2012 is a privacy and data protection law in Singapore that
imposes a broad set of duties on companies in Singapore and foreign entities that
process personal data of Singaporean residents.

In an increasingly data-driven world, the protection of personal data has become paramount. Singapore, as a global financial and technological hub, recognizes this imperative through its robust Personal Data Protection Act (PDPA). This article provides a comprehensive overview of PDPA compliance, emphasizing the technical aspects organizations must address to safeguard personal data and avoid significant repercussions.
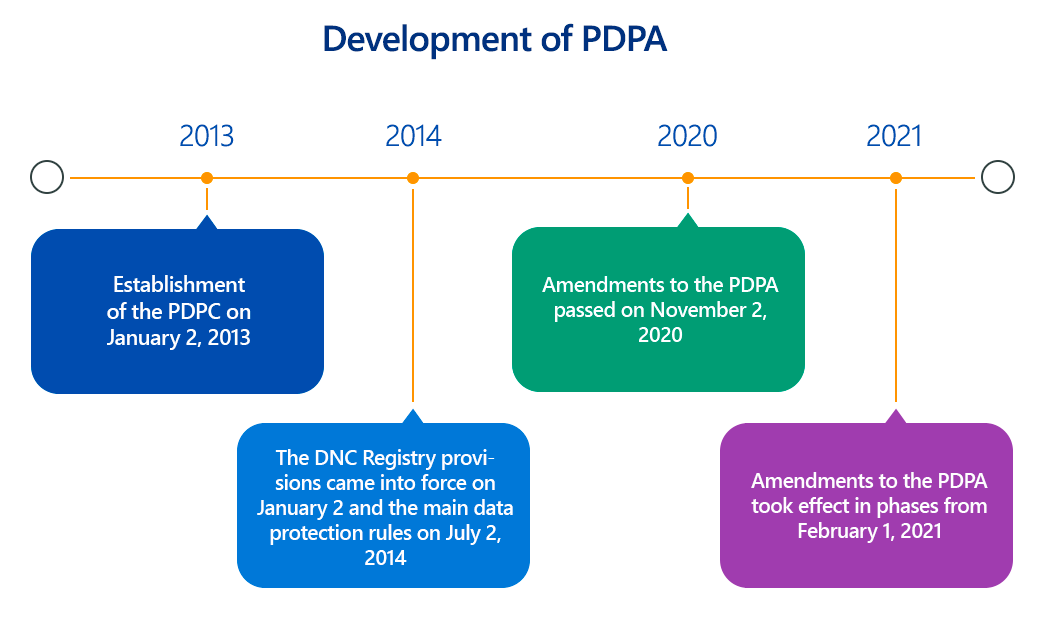
Overview of PDPA (Personal Data Protection Act)
The Personal Data Protection Act 2012 (PDPA) is Singapore's primary data protection law, designed to govern the collection, use, and disclosure of personal data by organizations. It aims to strike a balance between safeguarding individuals' personal data and enabling organizations to leverage data for legitimate business purposes. The PDPA is enforced by the Personal Data Protection Commission (PDPC), which provides guidance, investigates complaints, and imposes penalties for non-compliance.
Key to the PDPA are its data protection obligations, which revolve around the concept of consent, purpose limitation, and reasonableness. Generally, organizations must obtain explicit and informed consent from individuals before collecting, using, or disclosing their personal data. Furthermore, data collected should only be used for the specific purposes for which consent was obtained, and organizations must make reasonable efforts to ensure the accuracy and security of the data they hold.
Key Aspects of Singapore Personal Data Protection Act (PDPA) Compliance
PDPA compliance extends beyond mere policy formulation; it demands a proactive and integrated approach to data governance. Here are the core obligations:
- Consent Obligation: Organizations must obtain clear, unambiguous, and informed consent before collecting, using, or disclosing personal data. This involves clearly stating the purposes for data collection and ensuring individuals understand what they are agreeing to. Technical implementations may involve:
- Granular Consent Mechanisms: Providing options for users to consent to specific types of data processing, rather than a blanket agreement.
- Audit Trails for Consent: Maintaining secure, timestamped records of when and how consent was obtained and withdrawn.
- Easy Withdrawal of Consent: Implementing user-friendly mechanisms for individuals to withdraw consent at any time, with clear communication of the consequences.
- Purpose Limitation Obligation: Personal data should only be collected, used, or disclosed for purposes that a reasonable person would consider appropriate in the circumstances and for which consent has been obtained. Technically, this implies:
- Data Minimization: Designing systems to collect only the data strictly necessary for the stated purpose. This reduces the risk surface.
- Data Mapping and Inventory: Maintaining a comprehensive inventory of all personal data collected, its purpose, where it's stored, and who has access. This is often achieved through data discovery and classification tools.
- Notification Obligation: Individuals must be informed of the purposes for which their data is being collected, used, or disclosed at the time of collection. This often translates to:
- Clear Privacy Policies: Easily accessible and understandable privacy policies on websites and applications.
- Just-in-Time Notifications: Providing contextual notices to users at the point of data collection (e.g., when signing up for a service, or before location data is accessed).
- Access and Correction Obligation: Individuals have the right to request access to their personal data and to request corrections to any inaccuracies. Technical considerations include:
- Secure Access Portals: Providing secure, authenticated portals for individuals to view and update their data.
- Streamlined Request Handling: Implementing automated or semi-automated workflows to manage data access and correction requests promptly (e.g., within the stipulated 30 days).
- Data Synchronization: Ensuring corrected data is propagated across all relevant systems and, where applicable, to third parties who received the incorrect data.
- Accuracy Obligation: Organizations must make reasonable efforts to ensure the personal data they collect is accurate and complete, especially if it will be used for decision-making or disclosed to other organizations. Technical measures include:
- Data Validation: Implementing data validation rules at the point of entry.
- Regular Data Audits: Periodically reviewing and verifying the accuracy of stored personal data.
- Protection Obligation: Organizations are required to implement reasonable security arrangements to protect personal data from unauthorized access, collection, use, disclosure, copying, modification, disposal, or similar risks. This is where technical details become critical:
- Encryption: Implementing strong encryption for data at rest (databases, storage) and in transit (SSL/TLS for web traffic, secure protocols for data transfer).
- Access Controls (RBAC/ABAC): Implementing role-based access control (RBAC) or attribute-based access control (ABAC) to ensure only authorized personnel can access specific types of personal data.
- Network Security: Deploying firewalls, intrusion detection/prevention systems (IDS/IPS), and maintaining secure network configurations.
- Vulnerability Management: Regularly conducting vulnerability assessments and penetration testing (VAPT) to identify and remediate security weaknesses.
- Secure Software Development Life Cycle (SSDLC): Integrating security practices into every stage of software development, from design to deployment.
- Regular Security Audits: Conducting periodic security audits of systems and applications handling personal data.
- Retention Limitation Obligation: Personal data should not be retained longer than necessary for the fulfillment of the purposes for which it was collected, or for legal or business purposes. Technical implementation requires:
- Data Lifecycle Management: Implementing policies and automated processes for data retention, archival, and secure disposal (e.g., shredding, secure wiping of digital media).
- Data Anonymization/Pseudonymization: Where data is no longer needed in its identifiable form, exploring techniques to anonymize or pseudonymize it to reduce privacy risks while still allowing for analytical use.
- Transfer Limitation Obligation: Personal data transferred outside Singapore must be protected to a standard comparable to that under the PDPA. This necessitates:
- Binding Corporate Rules (BCRs) or Standard Contractual Clauses (SCCs): Implementing legal frameworks for international data transfers.
- Secure Data Transfer Protocols: Using encrypted and secure channels for cross-border data transmission.
- Due Diligence on Data Intermediaries: Thoroughly vetting third-party vendors and cloud service providers to ensure their data protection practices align with PDPA requirements.
- Data Breach Notification Obligation: Organizations must notify the PDPC and affected individuals of data breaches that are likely to result in significant harm or are of significant scale. Technical aspects include:
- Breach Detection Systems: Implementing tools for continuous monitoring of security incidents and data exfiltration attempts (e.g., SIEM, DLP).
- Incident Response Plan: Developing and regularly testing a comprehensive incident response plan for data breaches, including communication protocols.
- Forensic Capabilities: Having the technical capability to investigate the root cause and scope of a data breach.
- Accountability Obligation: Organizations must undertake measures to ensure compliance, including appointing a Data Protection Officer (DPO) and making their contact details available. The DPO plays a crucial role in overseeing technical compliance.
Why is Singapore Personal Data Protection Act (PDPA) Compliance Important?
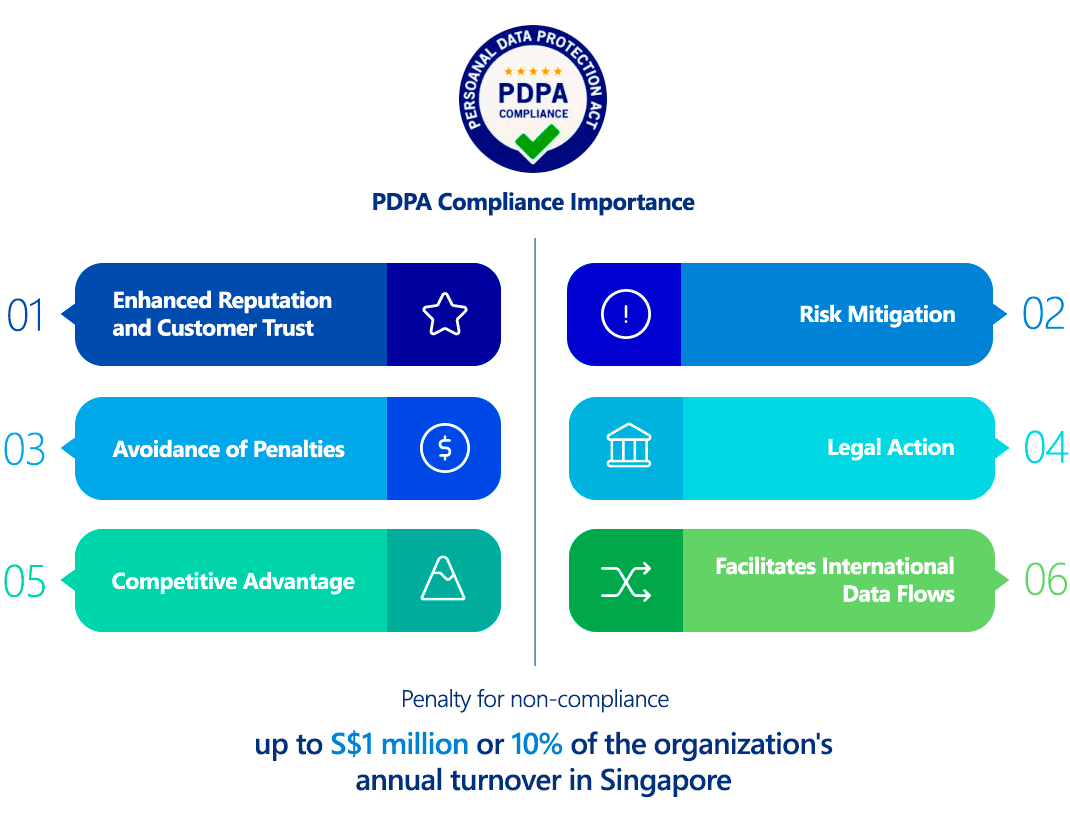
PDPA compliance is not merely a legal formality; it's a strategic imperative with tangible benefits and severe consequences for non-compliance:
- Enhanced Reputation and Customer Trust: Demonstrating a commitment to data privacy builds trust with customers, partners, and stakeholders, strengthening brand reputation.
- Risk Mitigation: Compliance significantly reduces the risk of data breaches, which can lead to financial losses, operational disruption, and reputational damage.
- Avoidance of Penalties: Non-compliance can result in substantial financial penalties. The PDPC has the power to impose fines of up to S$1 million or 10% of the organization's annual turnover in Singapore, whichever is higher, for serious breaches.
- Legal Action: Individuals who suffer direct loss or damage due to a breach of the PDPA can seek civil recourse.
- Competitive Advantage: Organizations with strong data protection practices can differentiate themselves in the market, particularly in industries where data sensitivity is high.
- Facilitates International Data Flows: Adherence to robust data protection standards, like the PDPA, facilitates seamless and secure cross-border data transfers, crucial for global businesses.
Who Needs to Comply with Singapore Personal Data Protection Act (PDPA)?
The PDPA applies to all private sector organizations in Singapore that collect, use, or disclose personal data. This includes:
- All private organizations, regardless of size or industry, that handle personal data of individuals in Singapore.
- Organizations located outside Singapore if they collect, use, or disclose personal data of individuals in Singapore.
- Data intermediaries (organizations that process personal data on behalf of another organization) are also subject to certain obligations, particularly the Protection and Retention Limitation Obligations, and the Data Breach Notification Obligation.
There are certain exemptions for individuals acting in a personal or domestic capacity, and public agencies are generally governed by different legislation.
Singapore Personal Data Protection Act (PDPA) vs GDPR Comparison
Here’s a comparison table between Singapore’s PDPA (Personal Data Protection Act) and the EU’s GDPR (General Data Protection Regulation):
| Aspect | PDPA (Singapore) | GDPR (EU) |
|---|---|---|
| Scope | Applies to private-sector organizations in Singapore processing personal data. | Applies to all organizations (globally) processing EU residents’ data. |
| Extraterritoriality | Limited (mainly Singapore-based organizations). | Yes (applies worldwide if processing EU data). |
| Consent Requirement | Explicit or deemed consent allowed (opt-out possible in some cases). | Explicit consent required (opt-in only, with clear affirmative action). |
| Data Subject Rights | Access, correction, and withdrawal of consent. No explicit "right to be forgotten." | Broader rights: Access, rectification, erasure ("right to be forgotten"), portability, and objection. |
| Data Protection Officer (DPO) | Required only if organization’s core activities involve large-scale data processing. | Mandatory for public authorities or organizations processing large-scale sensitive data. |
| Data Breach Notification | Mandatory only if likely to cause significant harm (within 3 days). | Mandatory within 72 hours if risk to rights/freedoms. |
| Penalties | Up to S$1 million(≈ €690k) or 10% of annual turnover (whichever higher). | Up to €20 million or 4% of global turnover (whichever higher). |
| Data Localization | No strict requirement (cross-border transfers allowed with safeguards). | No restriction, but transfers outside EU require adequacy decisions (e.g., SCCs). |
| Sensitive Data | No special category (but stricter rules for NRIC numbers). | Special categories (e.g., health, biometrics) require higher protection. |
| Purpose Limitation | Data must be used only for the stated purpose. | Same, but stricter enforcement under "purpose limitation" principle. |
| Legitimate Interest | Recognized but less defined than GDPR. | Explicitly allowed as a legal basis (with balancing test). |
Key Differences Summary
- GDPR is stricter (higher fines, broader rights, extraterritorial reach).
- PDPA is more flexible (allows deemed consent, fewer mandatory obligations).
- Breach reporting is faster under GDPR (72h vs. PDPA’s harm-based threshold).
- DPO requirements are narrower under PDPA.
How to Ensure Singapore Personal Data Protection Act (PDPA) Compliance?
Achieving and maintaining PDPA compliance requires a systematic and ongoing effort. Key steps include:
- Appoint a Data Protection Officer (DPO): Designate a DPO responsible for overseeing data protection strategy and implementation. While mandatory, registering the DPO with the PDPC is not legally required but encouraged.
- Conduct Data Protection Impact Assessments (DPIAs): Before embarking on new projects or initiatives involving personal data, conduct DPIAs to identify and mitigate potential privacy risks.
- Develop Comprehensive Data Protection Policies and Procedures: Document clear policies for data collection, use, disclosure, access, correction, retention, and security. These should cover technical controls.
- Implement Robust Security Measures: This is the most technically intensive aspect. Organizations must implement appropriate technical and organizational safeguards to protect personal data. This includes:
- Network Segmentation: Isolating systems that handle sensitive personal data.
- Multi-Factor Authentication (MFA): Implementing MFA for access to systems containing personal data.
- Security Information and Event Management (SIEM): Centralizing and analyzing security logs to detect and respond to threats.
- Data Loss Prevention (DLP): Deploying DLP solutions to prevent unauthorized exfiltration of sensitive data.
- Regular Software Updates and Patch Management: Ensuring all systems and applications are up-to-date with the latest security patches.
- Secure Configuration Management: Hardening operating systems, applications, and network devices to remove default credentials and insecure settings.
- Provide Employee Training and Awareness: Regularly train employees on data protection obligations, best practices for handling personal data, and their role in maintaining security.
- Establish Data Breach Response Mechanisms: Develop a detailed incident response plan for data breaches, including communication protocols for affected individuals and the PDPC.
- Conduct Regular Compliance Audits and Reviews: Periodically assess data protection practices, identify areas for improvement, and take corrective actions. This involves both internal audits and, for critical systems, external security assessments.
- Manage Third-Party Risks: Conduct due diligence on all third-party vendors and data intermediaries who process personal data on your behalf, ensuring they meet PDPA standards through contractual agreements and regular audits.
Consequences of Non-Compliance
The penalties for PDPA non-compliance in Singapore are significant and can include:
- Financial Penalties: As mentioned, fines can reach S$1 million or 10% of the organization's annual turnover in Singapore, whichever is higher, for serious breaches.
- Reputational Damage: Data breaches and privacy violations can severely damage an organization's reputation, leading to loss of customer trust and market share.
- Legal Action: Individuals can bring civil lawsuits against organizations for direct loss or damage suffered due to PDPA contraventions.
- Loss of Business Opportunities: Non-compliance can lead to restrictions on data processing activities, impacting business operations and potential partnerships.
- Increased Scrutiny and Audits: Organizations found in breach may face increased scrutiny from the PDPC, leading to more frequent audits and compliance requirements.
How ImmuniWeb Helps Comply with Singapore Personal Data Protection Act (PDPA)?
ImmuniWeb, with its AI-driven Application Security Testing and Attack Surface Management platform, offers valuable capabilities to help organizations achieve and maintain PDPA compliance, particularly concerning the technical obligations:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
ImmuniWeb’s AI-enhanced platform combines automation with expert validation for actionable, compliance-friendly security insights.
By leveraging ImmuniWeb's advanced security testing and monitoring capabilities, organizations can significantly strengthen their technical safeguards, identify and address vulnerabilities before they are exploited, and build a more robust defense against data privacy risks, thereby contributing significantly to their overall PDPA compliance posture.
List of Authoritative Singapore Personal Data Protection Act (PDPA) Resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
