EU Cyber Resilience Act Compliance
The EU Cyber Resilience Act (CRA) is a regulation that sets mandatory cybersecurity requirements for connected
products and software throughout their lifecycle to enhance digital security, reduce
vulnerabilities, and strengthen resilience against cyber threats.

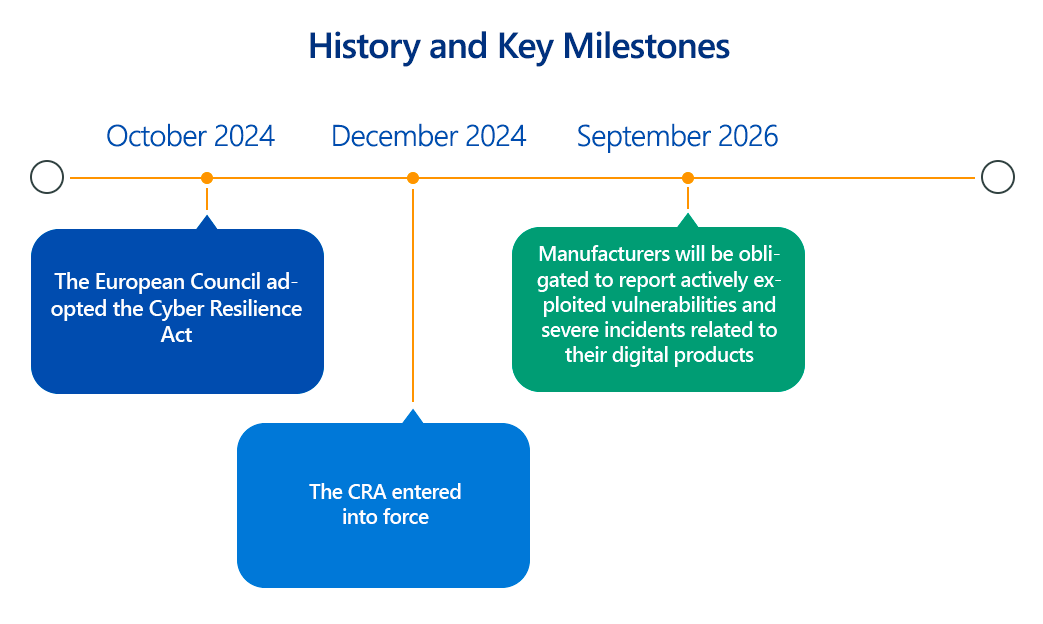
The European Union's Cyber Resilience Act (CRA), which officially entered into force in December 2024 with most obligations applying from December 2027, marks a significant legislative effort to bolster cybersecurity across the vast landscape of connected products.
As cyber threats grow in sophistication and frequency, the CRA aims to ensure that hardware and software products entering the EU market are "secure by design" and maintain that security throughout their lifecycle. This article provides a technical deep dive into the CRA, outlining its key compliance aspects, the importance of adherence, and practical steps for organizations.
Overview of the EU Cyber Resilience Act
The CRA establishes a horizontal cybersecurity framework for "products with digital elements." This broadly covers any software or hardware product and its remote data processing solutions whose intended or foreseeable use involves a direct or indirect logical or physical data connection to a device or network. Examples range from smart home devices and wearables to industrial control systems and operating systems.
The Act introduces mandatory cybersecurity requirements for economic operators involved in the design, development, production, and distribution of these products. It aims to address:
- Inadequate cybersecurity in many products: Many products are launched with insufficient security measures or lack timely updates.
- Lack of consumer information: Users often struggle to assess the cybersecurity of products or configure them securely.
- Limited manufacturer accountability: Responsibility for security often falls on users rather than manufacturers throughout the product lifecycle.
The CRA categorizes products with digital elements into different risk classes, influencing the conformity assessment procedures:
- Default Category: The vast majority (around 90%) of products fall here. Manufacturers can self-assess their compliance and issue an EU Declaration of Conformity.
- Important Products (Class I and Class II): These products, due to their higher cybersecurity relevance (e.g., browsers, password managers, antiviruses, firewalls, hypervisors), require adherence to harmonized standards, common specifications, or third-party assessment.
- Critical Products: These are highly sensitive products (e.g., tamper-resistant microprocessors, smart meter gateways). They require a mandatory third-party conformity assessment by a notified body.
A key aspect is the requirement for products to bear the CE marking, indicating compliance with the CRA's essential cybersecurity requirements.
Key Aspects of EU Cyber Resilience Act Compliance
For manufacturers, importers, and distributors of products with digital elements, CRA compliance involves a range of technical and organizational requirements:
- Cybersecurity Risk Assessment:
- Technical Detail: Manufacturers must conduct a thorough cybersecurity risk assessment for each product. This involves identifying potential cybersecurity risks, assessing their likelihood and impact (e.g., unauthorized access, data compromise, denial of service), and considering the product's intended purpose, foreseeable misuse, and operational environment. This assessment must be continuously updated throughout the product's lifecycle.
- Essential Cybersecurity Requirements (Annex I, Part I): Products must be designed, developed, and produced to ensure a level of cybersecurity appropriate to the identified risks. This includes:
- Secure by Design and Default: Products must be placed on the market with secure default configurations and be designed to protect against unauthorized access. This entails implementing strong authentication mechanisms, access controls, and minimizing attack surfaces.
- Data Protection: Ensuring confidentiality, integrity, and availability of data, both personal and other, stored, processed, or transmitted by the product. This often involves state-of-the-art encryption for data at rest and in transit, and robust integrity checks.
- Availability and Resilience: Designing products to withstand cyber incidents, including denial-of-service attacks, and ensuring the availability of essential functions. This involves implementing robust error handling, redundancy, and incident recovery capabilities.
- Minimizing Attack Surface: Products should be designed to limit attack vectors and reduce the potential for exploitation of vulnerabilities. This includes minimizing unnecessary open ports, services, and software components.
- Vulnerability Handling Requirements (Annex I, Part II): Manufacturers must establish and implement robust processes for identifying, documenting, and remediating vulnerabilities.
- Vulnerability Disclosure Policy: A clear policy for reporting and disclosing vulnerabilities, including a contact address for reporting.
- Security Updates: Mechanisms for providing timely and free security updates for identified vulnerabilities, ideally with automatic update capabilities enabled by default (with a clear opt-out). Updates for security issues should ideally be separated from feature updates.
- Software Bill of Materials (SBOM): Manufacturers must identify and document all components, including third-party and open-source software, in a machine-readable SBOM format (e.g., SPDX, CycloneDX) to facilitate vulnerability management and supply chain transparency.
- Post-Market Surveillance: Continuous monitoring of cybersecurity performance and vulnerabilities throughout the product's lifecycle.
- Technical Documentation: Comprehensive technical documentation (as specified in Annex VII) is required, detailing the product's design, development, production, and vulnerability handling processes, including the cybersecurity risk assessment and SBOM. This documentation is crucial for conformity assessment.
- EU Declaration of Conformity and CE Marking: Manufacturers must issue an EU Declaration of Conformity and affix the CE marking to compliant products, signifying their adherence to CRA requirements.
- Support Period: Manufacturers must define and adhere to a support period for their products, ensuring security updates are available for a reasonable duration (at least 5 years, or the expected product lifetime if longer, and security updates for a minimum of 10 years).
- Reporting Obligations: Manufacturers must report actively exploited vulnerabilities and severe incidents impacting their products to ENISA (European Union Agency for Cybersecurity) within 24 hours of becoming aware.
Why Is EU Cyber Resilience Act Compliance Important?
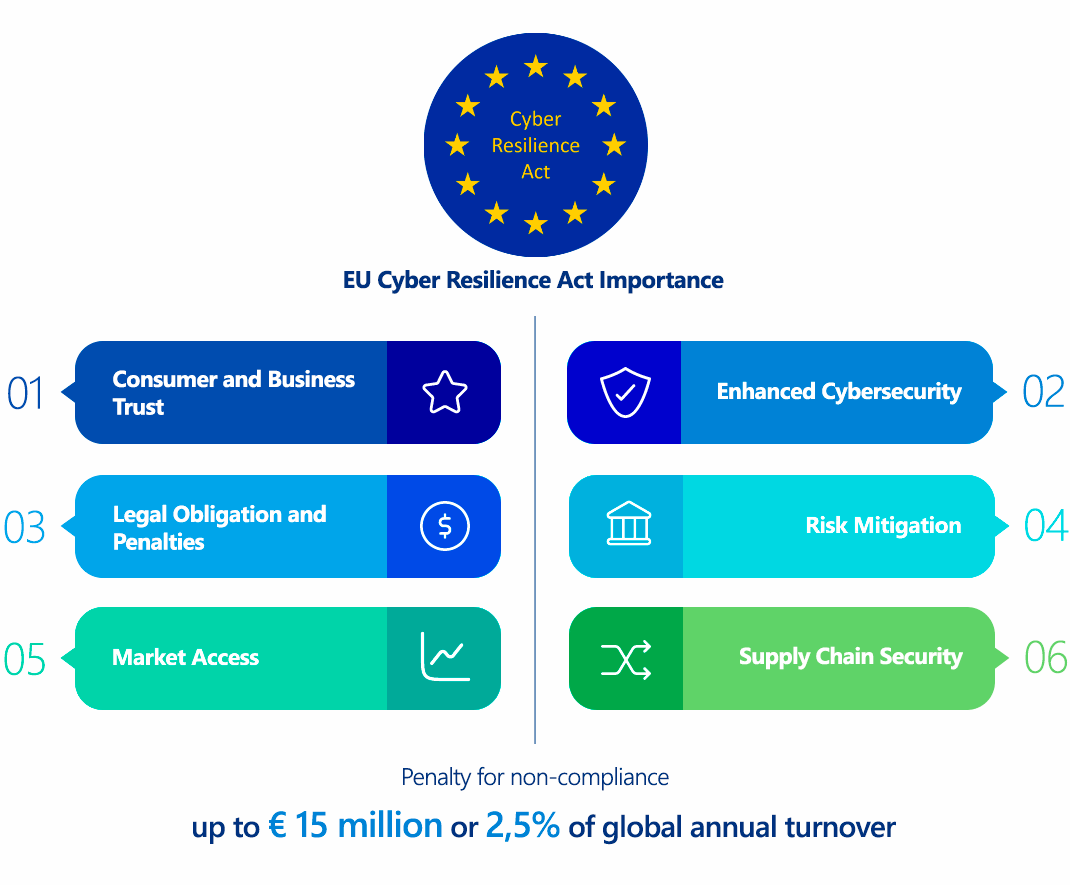
Compliance with the CRA is critical for several compelling reasons:
- Market Access: For any product with digital elements to be sold or made available on the EU market, compliance with the CRA is mandatory. Non-compliant products will face market restrictions, potential withdrawal, or recalls.
- Legal Obligation and Penalties: The Act carries significant financial penalties for non-compliance, creating a strong deterrent.
- Enhanced Cybersecurity: By mandating "security by design" and continuous vulnerability management, the CRA significantly raises the baseline cybersecurity posture of digital products, reducing the overall attack surface for consumers and businesses in the EU.
- Consumer and Business Trust: Compliance signals a commitment to product security, building trust among users and stakeholders. This can translate into a competitive advantage and stronger brand reputation.
- Risk Mitigation: Proactive adherence reduces the likelihood of costly security incidents, data breaches, and reputational damage. It also limits potential legal liabilities arising from product vulnerabilities.
- Supply Chain Security: The Act's focus on SBOMs and due diligence for third-party components enhances transparency and security throughout the digital product supply chain.
Who Needs to Comply with the EU Cyber Resilience Act?
The CRA's scope is broad and impacts several key economic operators, regardless of their size or turnover:
- Manufacturers: These are the primary entities responsible for ensuring compliance. This includes any person or entity that designs, develops, manufactures, or has a product with digital elements designed, developed, or manufactured, and markets it under their own name or trademark. This also extends to those who make substantial modifications to a product already on the market.
- Importers: Any EU-based entity that places a product with digital elements from a third country on the EU market. Importers must verify that the manufacturer has met their obligations (e.g., conducted conformity assessment, provided technical documentation, affixed CE marking).
- Distributors: Any entity in the supply chain, other than the manufacturer or importer, that makes a product with digital elements available on the EU market. Distributors must ensure the product bears the CE marking, is accompanied by required documentation, and that the manufacturer and importer have complied with their respective obligations.
- Open-Source Software Stewards: While non-commercial open-source software is generally excluded, open-source software that is "monetized" by manufacturers or developers falls under the CRA's scope. Additionally, the Act introduces obligations for "open-source software stewards" regarding actively exploited vulnerabilities and severe incidents affecting their networks and information systems used in product development.
The Act applies to organizations both within and outside the EU if their products with digital elements are placed on the EU market.
EU Cyber Resilience Act vs. GDPR Comparison
While both the CRA and GDPR are foundational EU regulations aiming to protect fundamental rights in the digital space, they address distinct aspects:
| Feature | EU Cyber Resilience Act | GDPR |
|---|---|---|
| Primary Focus | Enhancing the cybersecurity of products with digital elements (hardware and software) throughout their lifecycle. | Protecting personal data and privacy for individuals, regardless of the technology used. |
| Scope | Applies to manufacturers, importers, and distributors of products with digital elements. Focuses on the security of the product itself. | Applies to anyone who processes personal data of individuals in the EU. Focuses on data subjects and their rights. |
| Technicalities | Mandatory "secure by design" principles, vulnerability handling processes (SBOMs, security updates), incident reporting for product vulnerabilities, robust cybersecurity measures (e.g., encryption, access control) within products. | Data minimization, purpose limitation, storage limitation, accuracy, integrity and confidentiality, and accountability through technical and organizational measures (e.g., encryption of personal data, access controls, pseudonymization). |
| Incident Reporting | Reporting of actively exploited vulnerabilities in products and severe incidents affecting product security to ENISA. | Reporting of personal data breaches to relevant Data Protection Authorities (DPAs) and, in high-risk cases, to affected individuals. |
| Overlaps | Secure products mandated by CRA are essential for protecting personal data processed by those products, thus supporting GDPR compliance. For instance, if a smart device (CRA scope) processes personal data, its security flaws could lead to a GDPR breach. | GDPR's requirements for data integrity and confidentiality necessitate robust cybersecurity, which the CRA directly addresses for products. A lack of CRA compliance could lead to GDPR violations if personal data is compromised due to product insecurity. |
| Penalties | Fines up to €15 million or 2.5% of global annual turnover. | Fines up to €20 million or 4% of global annual turnover. |
In essence, the CRA is about making the tools (digital products) secure, while the GDPR is about protecting the information (personal data) processed by any means. They are complementary regulations, with CRA providing the foundational product security necessary to uphold GDPR's data protection principles.
How to Ensure EU Cyber Resilience Act Compliance?
Achieving CRA compliance requires a systematic and integrated approach throughout the product lifecycle:
- Product Inventory and Classification:
- Technical Step: Identify all products with digital elements that are placed on or intended for the EU market.
- Technical Detail: Categorize each product based on the CRA's risk classification (default, important, critical) to determine the applicable conformity assessment procedure. This requires understanding the product's functionality, its potential impact on users and systems, and its criticality for cybersecurity.
- Conduct Comprehensive Cybersecurity Risk Assessments:
- Technical Step: Implement a repeatable and documented process for assessing cybersecurity risks.
- Technical Detail: This involves threat modeling, vulnerability analysis, and impact assessment for each product. Tools for automated vulnerability scanning, penetration testing, and code analysis (SAST/DAST) should be integrated into the development pipeline. Document the identified risks, their severity, and proposed mitigation strategies.
- Implement "Security by Design" Principles:
- Technical Step: Integrate cybersecurity considerations from the earliest stages of product design and development.
- Technical Detail: This means adopting secure coding practices, implementing robust authentication and authorization mechanisms, encrypting sensitive data at rest and in transit (using strong cryptographic algorithms like AES-256 for symmetric encryption, RSA for asymmetric encryption, and TLS 1.2+ for secure communication), minimizing attack surface by disabling unnecessary services/ports, and using secure communication protocols. Employ a secure software development lifecycle (SSDLC).
- Establish Robust Vulnerability Management Processes:
- Technical Step: Develop and implement a comprehensive vulnerability handling policy.
- Technical Detail: This includes systematic identification of vulnerabilities through internal testing, third-party audits, and bug bounty programs. Implement a system for tracking, prioritizing, and remediating vulnerabilities promptly. Crucially, generate and maintain a Software Bill of Materials (SBOM) in a machine-readable format (e.g., SPDX, CycloneDX) for all components, including open-source libraries, to enable proactive identification of vulnerabilities in dependencies. Define a clear process for releasing security updates, ideally with automated deployment mechanisms.
- Develop Technical Documentation and CE Marking Procedures:
- Technical Step: Prepare the required technical documentation.
- Technical Detail: This includes detailed descriptions of the product's design, architecture, security features, risk assessment results, vulnerability handling processes, and test reports. For "important" and "critical" products, engage with notified bodies for third-party conformity assessment well in advance of market entry. Ensure the correct application of the CE marking.
- Define and Communicate Support Period and Update Policies:
- Technical Step: Clearly define the product's support period and ensure capabilities for providing long-term security updates.
- Technical Detail: This involves setting up infrastructure for delivering security patches, providing clear advisory messages to users, and outlining the process for users to opt-out if automatic updates are enabled.
- Establish Incident Response and Reporting Mechanisms:
- Technical Step: Implement an incident response plan specifically for product vulnerabilities and security incidents.
- Technical Detail: This includes internal procedures for detection, analysis, containment, eradication, recovery, and post-incident review. Crucially, establish a clear process for reporting actively exploited vulnerabilities and severe incidents to ENISA within the 24-hour window.
- Supply Chain Due Diligence:
- Technical Step: Assess the cybersecurity practices of third-party component providers.
- Technical Detail: This involves contractual agreements, security audits, and ensuring that third-party components also comply with relevant security standards and contribute to the overall product's security.
Consequences of Non-Compliance with the EU Cyber Resilience Act
The CRA introduces significant penalties to ensure adherence:
- Financial Penalties:
- Up to €15 million or 2.5% of the company's total worldwide annual turnover for the preceding financial year, whichever is higher, for general non-compliance with the essential cybersecurity requirements or vulnerability handling processes.
- Lower fines for other administrative infringements (e.g., failure to provide correct information).
- Market Restrictions: Non-compliant products can be prohibited from being placed on the EU market, or withdrawn/recalled if already in circulation.
- Reputational Damage: Significant harm to brand image and loss of consumer trust, impacting sales and market share.
- Legal Liability: Increased risk of lawsuits from users or businesses harmed by security incidents stemming from non-compliant products.
- Operational Disruption: The costs and resources required for remediation, recalls, and re-certification can be substantial.
How ImmuniWeb Helps Comply with the EU Cyber Resilience Act
ImmuniWeb, with its AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform, can play a pivotal role in assisting organizations with their EU Cyber Resilience Act compliance, particularly concerning the technical requirements for security by design, vulnerability management, and robust technical documentation.
Here's how ImmuniWeb's capabilities align with CRA technical compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
In summary, ImmuniWeb's technical capabilities directly address several critical cybersecurity aspects mandated by the EU Cyber Resilience Act, helping organizations build more secure digital products and demonstrate their compliance with this landmark regulation.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
