EU Digital Operational Resilience Act (DORA) Compliance
The EU Digital Operational Resilience Act (DORA) establishes uniform cybersecurity and operational resilience
requirements for financial entities and their critical third-party providers to ensure
they can withstand, respond to, and recover from ICT-related disruptions and threats.

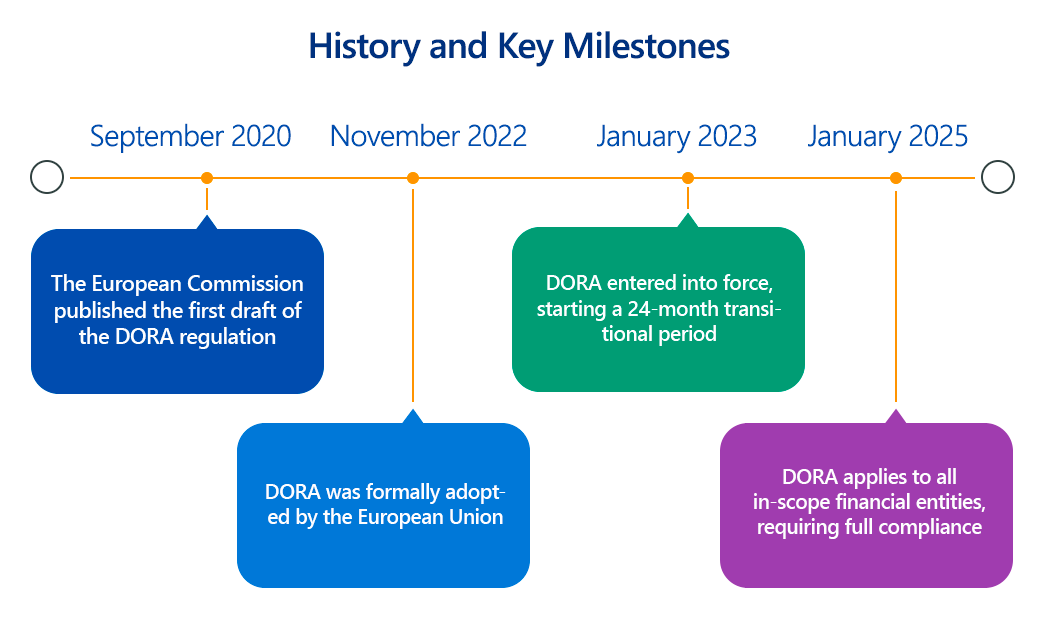
The European Union's Digital Operational Resilience Act (DORA), which entered into force on January 16, 2023, and will apply from January 17, 2025, represents a landmark regulation aimed at fortifying the digital operational resilience of the financial sector.
Recognizing the increasing reliance of financial entities on Information and Communication Technology (ICT) and the interconnectedness of the digital landscape, DORA introduces a unified and comprehensive framework to ensure that financial institutions can withstand, respond to, and recover from ICT-related disruptions.
This article delves into the technical requirements of DORA, its importance, scope, and practical steps for compliance.
Overview of the EU Digital Operational Resilience Act (DORA)
DORA is a direct regulation, meaning it is directly applicable in all EU Member States without the need for national transposition. Its core objective is to harmonize and strengthen the digital operational resilience of financial entities, ensuring the continuity and stability of financial services even in the face of severe ICT incidents, including cyberattacks, system failures, and third-party disruptions.
DORA addresses critical aspects of ICT risk management that were previously fragmented across various national laws and regulations. It introduces five key pillars:
- ICT Risk Management: Establishes a comprehensive framework for financial entities to identify, protect, detect, respond to, and recover from ICT risks.
- ICT-related Incident Management, Classification, and Reporting: Sets out clear rules for managing ICT-related incidents, including their classification based on materiality and a standardized reporting framework to competent authorities.
- Digital Operational Resilience Testing: Mandates regular and comprehensive testing of ICT systems, including threat-led penetration testing (TLPT) for certain entities, to identify weaknesses and assess resilience.
- ICT Third-Party Risk Management: Introduces a robust framework for managing the risks associated with third-party ICT service providers, including critical ICT third-party providers (CTPPs) who will be subject to direct oversight by EU supervisory authorities.
- Information Sharing Arrangements: Encourages financial entities to share cyber threat intelligence and information on vulnerabilities within trusted communities.
By unifying these areas, DORA aims to reduce fragmentation, enhance oversight, and promote a consistent, high level of digital operational resilience across the EU financial sector.
Key Aspects of EU Digital Operational Resilience Act (DORA) Compliance
DORA imposes detailed technical and organizational requirements across its five pillars, demanding a robust approach from financial entities and their critical ICT third-party providers:
- ICT Risk Management Framework (Chapter II):
- Technical Detail: Financial entities must establish a comprehensive and well-documented ICT risk management framework. This includes:
- Identification: Systematically identifying all ICT assets, critical functions, and dependencies, including those within the supply chain. This requires detailed inventories of hardware, software, network components, data flows, and third-party services.
- Protection & Prevention: Implementing appropriate and proportionate technical security controls to protect ICT systems and data. This includes strong authentication mechanisms (e.g., Multi-Factor Authentication - MFA, adaptive authentication), robust access controls (e.g., Role-Based Access Control - RBAC, principle of least privilege), data encryption (at rest and in transit using state-of-the-art algorithms like AES-256 and TLS 1.2+), network segmentation, firewalls, intrusion detection/prevention systems (IDS/IPS), and patch management processes for all software and firmware. Secure development lifecycles (SSDLC) must be integrated into software acquisition and development.
- Detection: Implementing mechanisms for continuous monitoring of network and information systems to detect anomalies, cyber incidents, and vulnerabilities. This involves deploying Security Information and Event Management (SIEM) systems, Endpoint Detection and Response (EDR) solutions, and real-time logging of security-relevant events.
- Response & Recovery: Developing and implementing robust incident response plans, business continuity plans, and disaster recovery plans. This includes defining clear Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) for critical functions and data, ensuring data backup and restoration capabilities (e.g., immutable backups, off-site storage), and having documented crisis communication procedures.
- Learning & Evolving: Post-incident reviews and analysis to identify root causes and implement lessons learned. Continuous improvement of ICT risk management processes based on new threats and vulnerabilities.
- Technical Detail: Financial entities must establish a comprehensive and well-documented ICT risk management framework. This includes:
- ICT-related Incident Management, Classification, and Reporting (Chapter III):
- Technical Detail: Entities must establish robust processes for managing all ICT-related incidents. This includes:
- Classification: Implementing technical criteria and materiality thresholds (to be specified in RTS) to classify incidents as minor or major, and to identify significant cyber threats. This will involve analyzing factors like the number of affected users, financial impact, data loss, geographical spread, and duration.
- Early Warning & Reporting: Strict timelines for notifying competent authorities:
- Initial Notification: Within 24 hours of becoming aware of a major ICT-related incident. This should be a preliminary report.
- Intermediate Report: Within 72 hours of becoming aware of a major incident, providing an update on the incident, its impact, and initial mitigation measures.
- Final Report: Within one month, a comprehensive report detailing the root cause, impact, and measures taken.
- Communication: Procedures for informing clients, service users, and the public about incidents that impact their services or data.
- Technical Detail: Entities must establish robust processes for managing all ICT-related incidents. This includes:
- Digital Operational Resilience Testing (Chapter IV):
- Technical Detail: A comprehensive testing program is mandatory, including:
- Basic Testing: Regular (at least annually) assessments of ICT tools and systems, including vulnerability assessments, open-source software security assessments, network security assessments, gap analyses, and scenario-based testing.
- Threat-Led Penetration Testing (TLPT): For financial entities deemed "critical" (e.g., those with a high level of ICT risk or systemic importance), TLPT based on the TIBER-EU framework is required every three years. This involves advanced red-teaming exercises simulating real-world cyberattacks, often requiring participation from critical ICT third-party providers. The technical scope of TLPT must cover critical functions, underlying ICT systems, and relevant third-party interfaces.
- Technical Detail: A comprehensive testing program is mandatory, including:
- ICT Third-Party Risk Management (Chapter V):
- Technical Detail: Entities must rigorously manage risks stemming from ICT third-party service providers. This includes:
- Due Diligence: Thorough pre-contractual assessments of providers' ICT risk management frameworks, security measures, and operational resilience capabilities.
- Contractual Provisions: Including specific contractual clauses covering ICT security, incident reporting, audit rights, and clear service level agreements (SLAs) regarding operational resilience.
- Register of Information: Maintaining a comprehensive register of all contractual arrangements with ICT third-party service providers, especially for critical or important functions. This register should include details on the services provided, data processed, and service locations.
- Exit Strategies: Developing and regularly testing exit strategies for critical ICT service contracts to ensure continuity of services in case of termination or failure of a provider.
- Oversight of Critical ICT Third-Party Providers (CTPPs): A new EU oversight framework for CTPPs will subject these providers (designated by European Supervisory Authorities - ESAs) to direct oversight and potential recommendations from Lead Overseers, which financial entities must consider.
- Technical Detail: Entities must rigorously manage risks stemming from ICT third-party service providers. This includes:
- Information Sharing Arrangements (Chapter VI):
- Technical Detail: Encourages the establishment of information sharing arrangements within trusted communities to exchange cyber threat intelligence (e.g., Indicators of Compromise - IoCs, TTPs), vulnerabilities, and defensive techniques. This requires secure platforms and protocols for information exchange.
Why Is EU Digital Operational Resilience Act (DORA) Compliance Important?
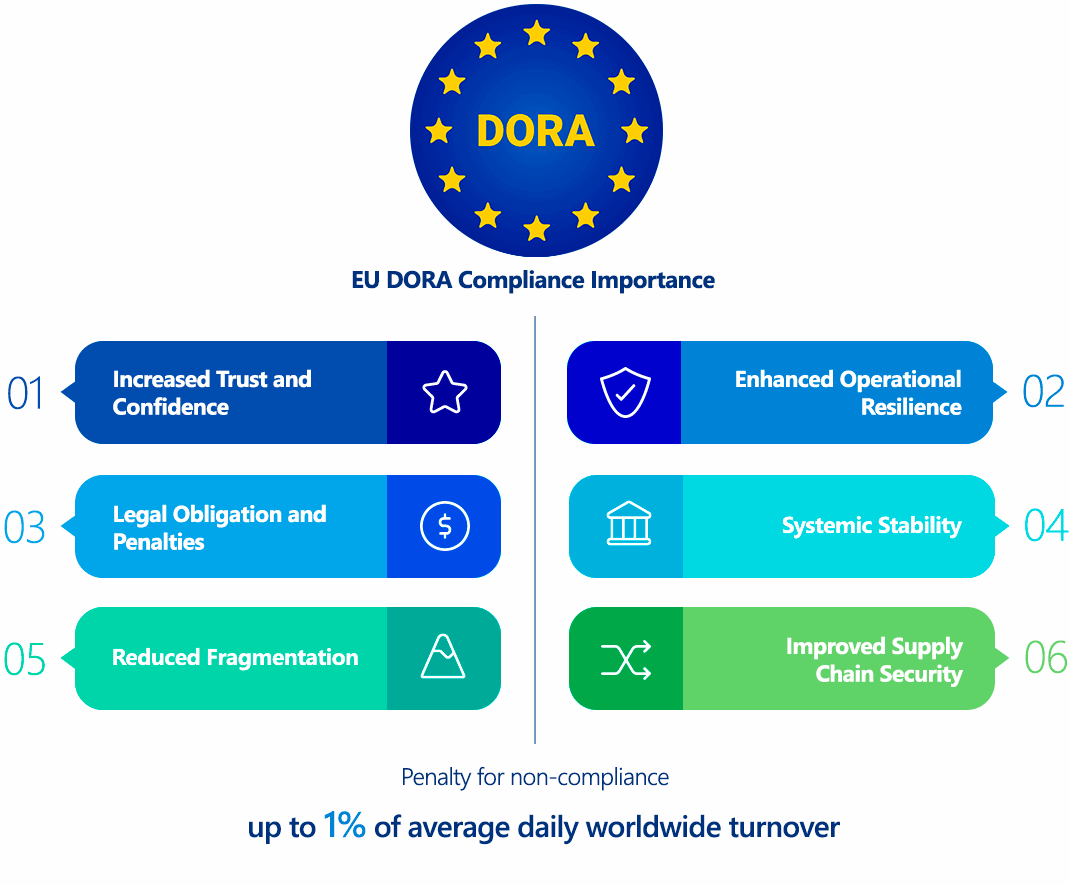
DORA compliance is of paramount importance for the financial sector for several reasons:
- Legal Obligation and Penalties: DORA is a binding regulation with significant financial penalties for non-compliance. These can range up to a percentage of global annual turnover, making it a serious financial risk. Furthermore, competent authorities can issue compliance orders, enforce audits, and even impose temporary bans on management if serious breaches occur.
- Systemic Stability: The financial sector's high degree of interconnectedness means that an ICT disruption in one entity can rapidly cascade, threatening the stability of the entire financial system. DORA aims to prevent such systemic risks by elevating the collective digital resilience.
- Enhanced Operational Resilience: By mandating a holistic and rigorous approach to ICT risk management, DORA compels financial entities to truly understand and strengthen their ability to withstand, respond to, and recover from digital disruptions, ultimately ensuring business continuity.
- Reduced Fragmentation: DORA replaces a patchwork of national regulations with a unified EU-wide framework, simplifying compliance for financial entities operating across multiple Member States and fostering a consistent baseline of security.
- Increased Trust and Confidence: Robust digital operational resilience builds trust among clients, investors, and the wider public in the financial services sector. Demonstrating compliance can be a competitive advantage.
- Improved Supply Chain Security: DORA's strong focus on third-party risk management addresses a critical vulnerability, as many financial entities rely heavily on external ICT service providers. This creates a stronger and more transparent digital supply chain for the sector.
Who Needs to Comply with EU Digital Operational Resilience Act (DORA)?
DORA has a broad scope, covering a wide array of financial entities and, significantly, their critical ICT third-party service providers. The regulation applies to:
Financial Entities (approx. 20 types):
- Credit institutions (banks)
- Payment institutions
- Electronic money institutions
- Investment firms
- Crypto-asset service providers (CASPs) and issuers of asset-referenced tokens and e-money tokens
- Central securities depositories
- Central counterparties
- Trading venues
- Trade repositories
- Insurance and reinsurance undertakings
- Insurance intermediaries, reinsurance intermediaries, and ancillary insurance intermediaries
- Institutions for occupational retirement provisions
- Managers of alternative investment funds
- Management companies
- Data reporting service providers
- Crowdfunding service providers
- Securitisation repositories
ICT Third-Party Service Providers:
- Any natural or legal person providing ICT services (including digital and data services) to financial entities.
- This includes cloud computing service providers, data analytics services, software providers, data centers, and managed service providers.
- Critical ICT Third-Party Service Providers (CTPPs) will be subject to a dedicated EU oversight framework, directly supervised by a "Lead Overseer" designated by the European Supervisory Authorities (ESAs).
DORA's extra-territorial reach means it applies to ICT third-party service providers established outside the EU if they provide services to financial entities within the EU.
EU Digital Operational Resilience Act (DORA) vs. GDPR Comparison
While both DORA and GDPR are foundational EU regulations that address digital risks and protection, they have distinct focuses and scopes:
| Feature | EU Digital Operational Resilience Act (DORA) | GDPR |
|---|---|---|
| Primary Focus | Ensuring the digital operational resilience of financial entities and their ICT third-party service providers against all ICT-related disruptions. | Protecting personal data and privacy for individuals, regardless of the sector or technology. |
| Scope | Applies specifically to the financial sector and its ICT supply chain. Focuses on the continuity and security of critical financial services. | Applies to any organization that processes personal data of EU residents, across all sectors. Focuses on data subjects and their rights (e.g., access, rectification, erasure). |
| Technicalities | Mandates specific technical measures for ICT risk management (e.g., comprehensive risk assessments, TLPT, secure development, incident handling, business continuity, supply chain security, strong authentication, encryption). | Requires "appropriate technical and organizational measures" to protect personal data (e.g., encryption of personal data, pseudonymization, data minimization, access controls, regular security testing, data protection by design). |
| Incident Reporting | Reporting of major ICT-related incidents (impacting financial services or systems) to competent authorities. | Reporting of personal data breaches (compromising personal data) to Data Protection Authorities (DPAs) and, in high-risk cases, to affected individuals. |
| Overlaps | If an ICT-related incident (DORA scope) results in the compromise of personal data, it will likely also constitute a personal data breach under GDPR. DORA's strong emphasis on ICT security directly supports GDPR compliance by providing the operational resilience necessary to protect personal data. | GDPR's requirement for data security necessitates robust cybersecurity measures, many of which are explicitly mandated by DORA for financial entities. DORA helps financial entities implement the necessary controls to meet GDPR's security obligations for personal data. |
| Penalties | Up to a percentage of global annual turnover (exact amounts in RTS/ITS), with potential daily fines for CTPPs. | Up to €20 million or 4% of global annual turnover. |
In essence, DORA is a sector-specific regulation for finance that builds upon general cybersecurity principles (like those found in NIS2) to ensure operational continuity, while GDPR is a cross-sectoral regulation focused specifically on the protection of personal data. For financial entities, compliance with DORA will significantly contribute to their ability to meet the security requirements under GDPR.
How to Ensure EU Digital Operational Resilience Act (DORA) Compliance?
Achieving DORA compliance demands a comprehensive, integrated, and continuous effort across an organization's ICT landscape. Here's a technical roadmap:
- DORA Gap Analysis and Impact Assessment:
- Technical Step: Conduct a detailed assessment of your existing ICT risk management framework, incident management processes, resilience testing capabilities, and third-party risk management against DORA's requirements.
- Technical Detail: Identify all critical ICT systems, applications, and infrastructure supporting critical or important functions. Map data flows, dependencies, and interconnections. Use risk assessment methodologies to identify gaps in your current security controls (e.g., unpatched systems, weak authentication, lack of network segmentation, insufficient encryption, outdated incident response plans, limited visibility into third-party risks). Prioritize gaps based on their potential impact on operational resilience and DORA compliance.
- Establish a Robust ICT Risk Management Framework:
- Technical Step: Design and implement a holistic framework encompassing identification, protection, detection, response, and recovery.
- Technical Detail:
- Identification: Implement IT asset management (ITAM) and configuration management databases (CMDBs) to maintain a comprehensive, real-time inventory of all hardware, software, and services. Conduct regular threat intelligence gathering to understand emerging cyber threats relevant to your sector.
- Protection & Prevention: Deploy advanced security technologies: Next-generation firewalls, Web Application Firewalls (WAFs), Intrusion Detection/Prevention Systems (IDS/IPS), Data Loss Prevention (DLP) solutions, robust Endpoint Detection and Response (EDR) or eXtended Detection and Response (XDR) platforms. Implement Network Access Control (NAC) and Micro-segmentation to restrict lateral movement. Enforce strong cryptographic controls (e.g., FIPS 140-2 validated modules for encryption, secure key management using HSMs). Implement Secure Software Development Lifecycle (SSDLC) practices for all in-house developed applications, including secure coding standards, regular code reviews, and automated security testing (SAST, DAST, IAST).
- Detection: Deploy Security Information and Event Management (SIEM) systems with comprehensive log aggregation and correlation capabilities. Implement Security Orchestration, Automation, and Response (SOAR) platforms for automated response to detected threats. Establish 24/7 security monitoring capabilities (e.g., Security Operations Center - SOC).
- Response & Recovery: Develop detailed, technically precise incident response playbooks for various scenarios (e.g., ransomware, data breach, DDoS). Implement automated backup and recovery solutions with validated RTOs/RPOs. Regularly test failover and disaster recovery procedures in isolated environments.
- Implement Comprehensive Incident Management and Reporting:
- Technical Step: Establish clear internal procedures for managing ICT-related incidents from detection to resolution and reporting.
- Technical Detail: Define technical criteria for incident classification based on DORA's materiality thresholds (once finalized). Implement automated alert systems to notify relevant teams and stakeholders immediately upon detection of a significant event. Develop clear data collection procedures for incident information required for DORA reporting (e.g., technical details of compromise, impact analysis, mitigation steps taken). Ensure systems are in place to generate the required initial, intermediate, and final reports within the stipulated timelines.
- Develop a Robust Digital Operational Resilience Testing Program:
- Technical Step: Design and execute a multi-layered testing program.
- Technical Detail:
- Basic Testing: Conduct regular automated and manual vulnerability assessments, penetration tests, and configuration audits across all ICT systems. Perform scenario-based testing to simulate various disruption events (e.g., power outages, network failures, DDoS attacks).
- Threat-Led Penetration Testing (TLPT): For critical entities, engage qualified and independent TLPT providers (red teams) to conduct advanced simulations based on relevant threat intelligence (e.g., TIBER-EU framework). Ensure that CTPPs participate in these tests where their services support critical functions. Remediate all identified weaknesses and demonstrate continuous improvement.
- Strengthen ICT Third-Party Risk Management:
- Technical Step: Implement a rigorous framework for managing ICT third-party risks throughout the entire lifecycle.
- Technical Detail: Conduct thorough technical due diligence of prospective ICT third-party service providers, assessing their cybersecurity posture, operational resilience capabilities, and compliance with DORA requirements. Include specific ICT security clauses, audit rights (including remote audit capabilities), and detailed SLAs in contracts. Maintain a centralized, continuously updated "Register of Information" for all ICT service contracts, including critical function identification and sub-contracting details. Develop and test technical exit strategies for critical services to ensure seamless migration or continuity in case of provider failure. Actively monitor the cybersecurity performance and incident history of critical third parties.
- Facilitate Information Sharing:
- Technical Step: Establish mechanisms for secure and responsible information sharing.
- Technical Detail: Participate in relevant industry-specific Information Sharing and Analysis Centers (ISACs) or trusted communities. Implement secure platforms for exchanging cyber threat intelligence, indicators of compromise (IoCs), and defensive techniques, ensuring appropriate anonymization or aggregation where necessary.
Consequences of Non-Compliance with the EU Digital Operational Resilience Act (DORA)
The penalties for DORA non-compliance are severe and designed to act as a strong deterrent:
- Significant Administrative Fines: While specific maximum fines are to be detailed in Level 2 measures (RTS/ITS), they are expected to be substantial, potentially reaching a percentage of a company's global annual turnover, similar to GDPR. For critical ICT third-party providers, Lead Overseers can impose daily penalty payments for non-compliance with their recommendations, up to 1% of the provider's average daily worldwide turnover in the preceding financial year, for a maximum of six months.
- Supervisory Measures and Intervention: Competent authorities can impose a range of non-monetary sanctions, including:
- Ordering financial entities or CTPPs to take specific measures to address deficiencies.
- Requiring mandatory security audits or expert reviews.
- Suspending or prohibiting the use of certain ICT services or products.
- Issuing public statements identifying non-compliant entities.
- Reputational Damage: Non-compliance and, more importantly, operational disruptions due to a lack of resilience, can severely damage a financial entity's reputation, erode client trust, and lead to a loss of business.
- Operational Disruption and Financial Losses: The primary consequence of insufficient resilience is the actual disruption of services, leading to direct financial losses, recovery costs, and potential liabilities from affected clients or market participants.
- Increased Scrutiny and Audits: Non-compliant entities will likely face increased scrutiny, more frequent audits, and more burdensome reporting requirements from regulators.
How ImmuniWeb Helps Comply with the EU Digital Operational Resilience Act (DORA)
ImmuniWeb, with its AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform, provides crucial technical capabilities that directly support financial entities in achieving and maintaining compliance with several key aspects of the EU DORA, particularly concerning ICT risk management, digital operational resilience testing, and secure system development.
Here's how ImmuniWeb specifically aids DORA compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
In conclusion, ImmuniWeb acts as a powerful technical enabler for DORA compliance, particularly in the critical areas of continuous ICT risk assessment, robust security testing, and secure development practices, all of which are fundamental to achieving the digital operational resilience mandated by the Act.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
