EU ePrivacy Directive Compliance
The EU ePrivacy Directive (2002/58/EC, amended by 2009/136/EC) regulates privacy in electronic communications,
covering confidentiality, cookies, spam, and metadata protection, complementing
the GDPR for telecoms and online services.

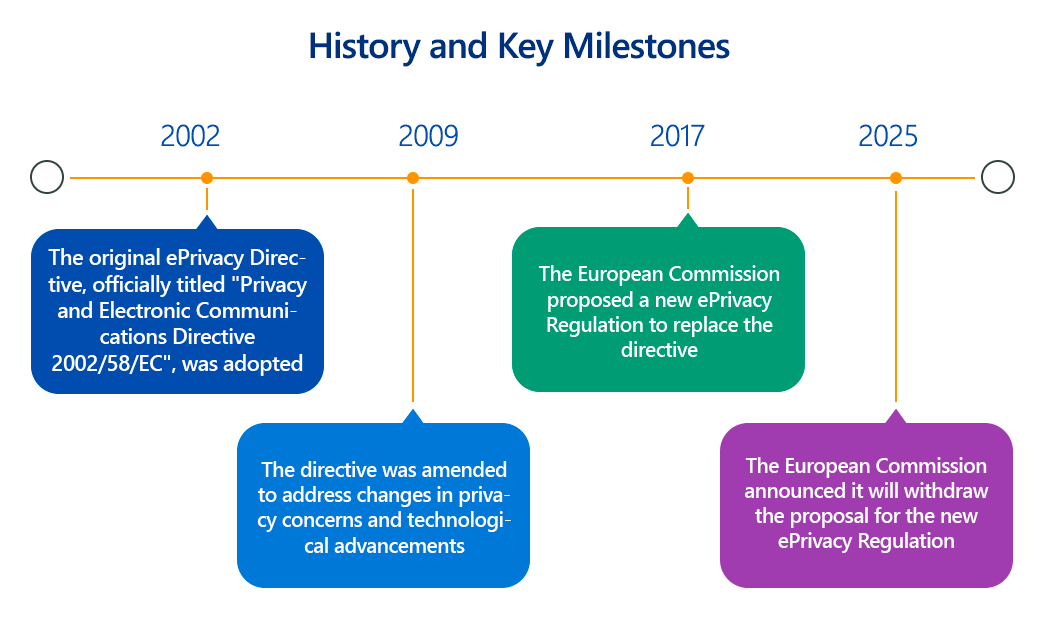
The European Union's digital landscape is governed by a dual regulatory framework for data protection: the comprehensive General Data Protection Regulation (GDPR) and the more specific ePrivacy Directive (Directive 2002/58/EC), often dubbed the "Cookie Law." While the long-awaited ePrivacy Regulation (ePR) was recently withdrawn in February 2025 due to a lack of consensus and outdated proposals, the ePrivacy Directive remains in force and continues to dictate rules for electronic communications and online tracking.
This article delves into the technical details of the EU ePrivacy Directive, its compliance requirements, and its crucial role in protecting online privacy.
Overview of EU ePrivacy Directive
The ePrivacy Directive (ePD) aims to ensure the confidentiality of electronic communications and protect the privacy of users in the electronic communications sector. It complements the GDPR by providing specific rules for:
- Confidentiality of Communications: Mandating that Member States ensure the confidentiality of communications and related traffic data (metadata like routing, timing, and location data). It generally prohibits interception, surveillance, or storage of communications by anyone other than the users without their consent.
- Cookies and Similar Technologies: Requiring websites to obtain prior, informed consent from users before storing or accessing information (like cookies, tracking pixels, device fingerprinting data) on their terminal equipment (e.g., computers, smartphones, tablets). Exceptions apply for "strictly necessary" cookies.
- Direct Marketing (Spam): Setting rules for unsolicited electronic communications for direct marketing purposes, generally requiring opt-in consent before sending marketing emails, SMS, or automated calls.
- Location Data and Traffic Data: Regulating the processing of location and traffic data generated by electronic communication services, generally requiring consent or anonymization.
- Security of Services: Obligating electronic communication service providers to implement appropriate technical and organizational measures to safeguard the security of their services and inform subscribers of any special risks.
It's crucial to remember that as a Directive, the ePD requires each EU Member State to transpose its provisions into national law. This has led to some variations in implementation and enforcement across the EU.
Key Aspects of EU ePrivacy Directive Compliance?
Technical compliance with the ePrivacy Directive is multifaceted, particularly concerning online tracking and direct marketing:
- Cookie Consent Management:
- Prior Consent: No non-essential cookies or tracking technologies (including pixels, local storage, device fingerprinting) should be placed on a user's device or accessed before explicit consent is obtained. This necessitates technical solutions that block scripts and trackers until consent is given.
- Informed Consent: Users must be clearly and comprehensively informed about the types of cookies used, their purposes, and how their data will be processed. This information should be easily accessible (e.g., via a clear cookie banner and a detailed cookie policy).
- Granular Consent: Users should be given granular control over their cookie preferences, allowing them to accept or reject different categories of cookies (e.g., analytics, marketing, functional). Technical implementations of Consent Management Platforms (CMPs) must support this.
- Easy Withdrawal: It must be as easy for users to withdraw their consent as it was to give it. CMPs should facilitate this.
- Consent Logging: Organizations must technically log and maintain records of user consent to demonstrate compliance.
- Strictly Necessary Exception: Cookies solely for "the sole purpose of carrying out or facilitating the transmission of a communication over an electronic communications network" or "as strictly necessary in order to provide an information society service explicitly requested by the subscriber or user" do not require consent. Technical analysis is needed to accurately categorize cookies.
- Confidentiality of Communications:
- Encryption: Electronic communication service providers must use robust encryption technologies (e.g., TLS, end-to-end encryption) to safeguard the confidentiality and integrity of communications and related metadata.
- Access Controls: Strict technical controls to prevent unauthorized access, interception, or surveillance of electronic communications data.
- Logging and Monitoring: Systems to log access and detect unusual activity related to communications data.
- Direct Marketing Technical Controls:
- Opt-in Mechanisms: For email, SMS, and automated calling for direct marketing, technical systems must ensure that valid, prior opt-in consent is obtained and recorded, unless an exception (like the "soft opt-in" for existing customers for similar products/services) applies.
- Easy Opt-out: Every marketing communication must include a clear, easy, and free mechanism for recipients to opt out of future communications. Technical unsubscribe links and processes are essential.
- Suppression Lists: Maintaining and regularly updating technical suppression lists for individuals who have opted out.
- Security of Services (Article 4): Electronic communication service providers must implement appropriate technical and organizational measures to manage security risks to their networks and services. This includes:
- Vulnerability management and penetration testing.
- Incident response plans for security breaches affecting communications data.
- Measures to inform subscribers of specific security risks.
- Data Retention: Electronic communication service providers must technically ensure that traffic and location data are erased or anonymized when no longer needed for the purpose of transmission or billing, unless consent for longer retention is obtained.
Why Is EU ePrivacy Directive Compliance Important?
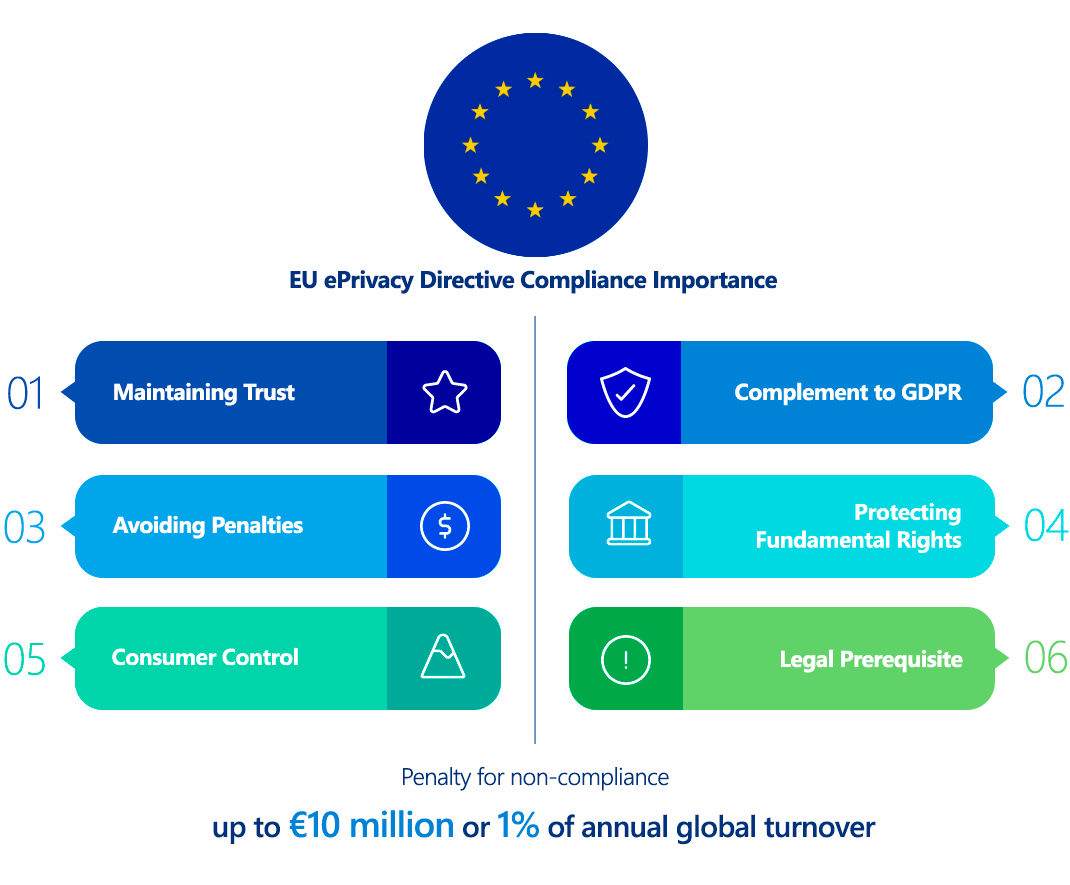
Compliance with the ePrivacy Directive is vital for several reasons:
- Protecting Fundamental Rights: It directly upholds the fundamental rights to privacy and protection of personal data enshrined in the EU Charter of Fundamental Rights.
- Maintaining Trust: Adhering to the ePrivacy Directive, particularly on cookie consent and direct marketing, builds trust with users, signaling respect for their privacy choices.
- Avoiding Penalties: Non-compliance can lead to significant fines and enforcement actions from national data protection authorities.
- Legal Prerequisite: It's a mandatory legal requirement for any organization operating in the EU digital space or targeting EU users.
- Complement to GDPR: It works in tandem with the GDPR, addressing specific areas not fully covered by the broader regulation, especially concerning unsolicited communications and the use of tracking technologies on terminal equipment.
- Consumer Control: It empowers individuals with greater control over their online experience and how their data is used for tracking and marketing purposes.
Who Needs to Comply with EU ePrivacy Directive?
The ePrivacy Directive's scope is broad and applies to:
- Providers of Publicly Available Electronic Communications Services: This includes traditional telecommunication companies (fixed and mobile telephony, SMS), Internet Service Providers (ISPs), and Over-the-Top (OTT) communication services (e.g., WhatsApp, Skype, Signal, email services like Gmail) that offer services to end-users in the EU.
- Website Operators: Any website that uses cookies or similar tracking technologies (pixels, fingerprinting, local storage) and has visitors from the EU/EEA, regardless of where the website itself is hosted.
- Businesses Engaged in Direct Marketing: Any organization sending unsolicited electronic communications (emails, SMS, automated calls) for direct marketing purposes to individuals in the EU/EEA.
Like the GDPR, the ePrivacy Directive has an extraterritorial effect, meaning it can apply to organizations located outside the EU/EEA if they process the data of individuals located within the EU/EEA, offer services to them, or monitor their behavior.
EU ePrivacy Directive vs. GDPR Comparison
The ePrivacy Directive and the GDPR are often discussed together because they are complementary, but they have distinct focuses:
| Feature | EU ePrivacy Directive | GDPR (General Data Protection Regulation) |
|---|---|---|
| Focus | Specific rules for privacy in electronic communications sector: confidentiality of communications, cookies/tracking, direct marketing (spam), traffic/location data. | Broader, horizontal data protection law covering all processing of personal data across all sectors. |
| Type of Law | Directive: Requires Member States to transpose into national law, leading to some variations. | Regulation: Directly applicable in all EU/EEA Member States without need for national transposition, ensuring uniformity. |
| Data Scope | Focuses on "electronic communications data" (content, metadata), and "information stored on terminal equipment" (e.g., cookies). Includes both natural and legal persons. | Focuses solely on "personal data" relating to identified or identifiable natural persons. |
| Consent | Opt-in consent generally required for non-essential cookies/tracking and unsolicited direct marketing. Specific requirements for cookies. | Defines standards for valid consent (freely given, specific, informed, unambiguous) as one of six lawful bases for processing personal data. |
| Confidentiality | Strong emphasis on the confidentiality of communications (Article 5) and associated metadata. | General principle of "integrity and confidentiality" (security) of personal data (Article 5(1)(f)). |
| Data Breach Notification | Requires electronic communication service providers to notify the relevant national authority of security breaches. | Mandatory notification of personal data breaches to the Supervisory Authority (within 72 hours) and data subjects (if high risk). |
| Sanctions | Determined by national laws (as it's a Directive), varying across Member States. Can be substantial. | Standardized high fines: up to €20 million or 4% of global annual turnover for serious infringements. |
| Relationship | Considered lex specialis (specific law) to the GDPR in its areas of focus. Where the ePD is more specific, it takes precedence. GDPR applies where ePD is silent or less specific. | The overarching data protection law. ePD complements it for specific electronic communication contexts. |
How to Ensure EU ePrivacy Directive Compliance?
Ensuring ePrivacy Directive compliance requires a dedicated focus on consent, technical controls, and transparent practices:
- Comprehensive Cookie Audit:
- Identify All Cookies & Trackers: Use a robust website scanner to detect all first-party and third-party cookies, tracking pixels, scripts, and other technologies that store or access information on user devices.
- Categorize Cookies: Classify each identified cookie/tracker based on its purpose (e.g., strictly necessary, functional, analytics, marketing, social media).
- Implement a Compliant Consent Management Platform (CMP):
- Pre-Consent Blocking: Ensure the CMP technically blocks all non-essential cookies and tracking scripts from loading before the user gives consent.
- Clear Consent Banner: Display a prominent, user-friendly cookie banner or pop-up upon a user's first visit.
- Granular Choice: Provide options for users to accept all, reject all, or manage their preferences for different cookie categories. No pre-ticked boxes for non-essential cookies.
- Informative Cookie Policy: Link to a clear, comprehensive, and easily accessible cookie policy that details all cookies used, their purposes, retention periods, and third-party providers.
- Easy Withdrawal: Ensure users can easily revisit and change their cookie preferences at any time (e.g., via a "Cookie Settings" link in the footer).
- Consent Logging: The CMP must record and store proof of consent for audit purposes (e.g., timestamp, user ID, specific choices).
- Review Direct Marketing Practices:
- Opt-in for New Contacts: Implement technical mechanisms (e.g., double opt-in forms) to obtain clear, affirmative consent before sending marketing communications to new subscribers.
- "Soft Opt-in" Compliance: If relying on the "soft opt-in" for existing customers, ensure their contact details were obtained during a sale/negotiation of a sale, the marketing is for similar products/services, and an easy opt-out was provided at the time of collection and in every subsequent communication.
- Mandatory Opt-out: Ensure all marketing emails/SMS have a clear, functional, and free unsubscribe link or mechanism.
- Suppression List Management: Use automated systems to manage suppression lists effectively.
- Strengthen Confidentiality for Communications Providers:
- Encryption by Default: Implement strong encryption protocols (e.g., HTTPS, TLS, E2EE where applicable) for all electronic communications and related data.
- Access Control & Network Security: Apply robust network security measures, intrusion detection, and strict access controls to communications infrastructure and data.
- Data Retention Policies: Develop and technically enforce policies for anonymizing or deleting traffic and location data when no longer needed, in line with ePD requirements.
- Regular Audits and Assessments:
- Periodically audit your website for new cookies/trackers.
- Regularly review direct marketing consent processes.
- Conduct security assessments (e.g., penetration tests) for electronic communication services.
- Employee Training: Ensure staff involved in website management, marketing, and electronic communications understand their obligations under the ePrivacy Directive.
Consequences of Non-Compliance with EU ePrivacy Directive
Since the ePrivacy Directive is implemented through national laws, the exact penalties vary by Member State. However, non-compliance can lead to significant consequences:
- Financial Penalties: National Data Protection Authorities (DPAs) can impose substantial fines. While the ePD itself doesn't set specific figures like the GDPR, many Member States have aligned their ePrivacy penalties with GDPR levels. For instance, in some countries, violations of ePD rules (especially cookie or spam rules) could lead to fines comparable to the lower tier of GDPR fines (e.g., up to €10 million or 2% of annual global turnover).
- Reputational Damage: Publicized non-compliance, particularly for widespread cookie violations or spam, can severely damage brand reputation and customer trust.
- Enforcement Actions: DPAs can issue warnings, reprimands, enforcement notices (requiring specific corrective actions), and even temporary or permanent bans on data processing activities.
- Civil Claims: Individuals may have the right to claim compensation for damages suffered due to ePD violations.
- Loss of Business: Companies may lose customers or face difficulties acquiring new ones if they are perceived as not respecting privacy or engaging in unsolicited marketing.
How ImmuniWeb Helps Comply with EU ePrivacy Directive?
While ImmuniWeb primarily focuses on cybersecurity and attack surface management, its capabilities indirectly and directly support compliance with several technical aspects of the EU ePrivacy Directive:
Here's how ImmuniWeb specifically aids EU ePrivacy Directive compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
While ImmuniWeb doesn't directly provide a Consent Management Platform (CMP) for direct cookie consent, its robust security testing and attack surface management capabilities lay the essential technical foundation for compliant implementation of ePrivacy Directive requirements, particularly around the secure and transparent use of tracking technologies and the confidentiality of electronic communications.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
