EU NIS 2 Directive Compliance
The EU NIS2 Directive strengthens cybersecurity risk management and reporting obligations for critical and
important entities across various sectors to enhance resilience against cyber threats
and ensure a high common level of security across the EU.

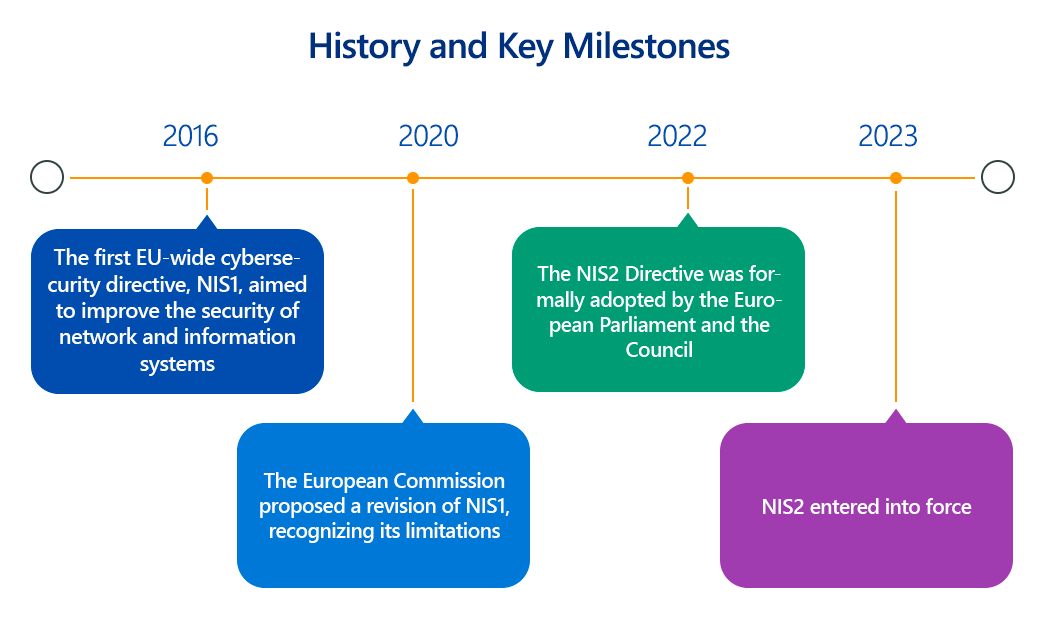
The European Union's Directive on measures for a high common level of cybersecurity across the Union (NIS2 Directive), which replaced its predecessor (NIS1) on October 17, 2024, is a cornerstone of the EU's cybersecurity strategy.
It aims to significantly enhance the overall cybersecurity posture of critical sectors and digital service providers throughout the EU, fostering a more resilient digital landscape in the face of escalating cyber threats. This article delves into the technical mandates of NIS2, its importance, scope, and how organizations can achieve compliance.
Overview of the EU NIS2 Directive
NIS2 represents a comprehensive overhaul and expansion of the original NIS Directive from 2016. Its primary objective is to harmonize cybersecurity requirements and enforcement measures across all EU Member States, ensuring a high common level of cyber resilience. The Directive broadens the scope of entities covered, introduces more stringent cybersecurity risk management and incident reporting obligations, and strengthens supervisory and enforcement powers for national authorities.
Key pillars of NIS2 include:
- Expanded Scope: Significantly increases the number and types of entities that must comply, moving beyond traditional critical infrastructure to include a wider array of "essential" and "important" sectors.
- Stricter Risk Management Requirements: Mandates specific baseline cybersecurity measures that entities must implement to manage risks to their network and information systems.
- Enhanced Incident Reporting: Establishes clearer and more prescriptive requirements for reporting significant cybersecurity incidents to national Computer Security Incident Response Teams (CSIRTs) or competent authorities.
- Supply Chain Security: Places greater emphasis on managing cybersecurity risks within the supply chain, requiring entities to assess the security practices of their direct suppliers and service providers.
- Accountability of Management: Introduces provisions for holding management bodies accountable for cybersecurity risk management, including potential personal liability.
- Improved Cooperation: Fosters stronger cooperation and information sharing between Member States and relevant authorities (e.g., ENISA, CSIRTs).
NIS2 classifies in-scope entities into two categories based on their criticality and size:
- Essential Entities: Generally larger entities in highly critical sectors (e.g., energy, transport, banking, healthcare, digital infrastructure, public administration). They face proactive and ex-ante supervision, with stricter enforcement measures and higher potential fines.
- Important Entities: Mid-sized entities in critical or other important sectors (e.g., postal and courier services, waste management, food production, manufacturing, digital providers). They are subject to ex-post supervision, meaning oversight typically occurs after an incident or indication of non-compliance.
Key Aspects of EU NIS2 Directive Compliance
For organizations falling under the NIS2 Directive, compliance necessitates the implementation of robust technical and organizational measures:
- Cybersecurity Risk Management (Article 21):
- Technical Detail: Entities must adopt an "all-hazards approach" to managing risks to the security of their network and information systems. This involves comprehensive risk assessments that identify, analyze, and prioritize threats (e.g., ransomware, phishing, insider threats, DDoS, physical disruptions) and vulnerabilities.
- Mandatory Measures (Minimum List): The Directive mandates the implementation of specific measures, including:
- Incident Handling: Technical procedures for detection, analysis, containment, eradication, recovery, and post-incident review. This involves security information and event management (SIEM) systems, endpoint detection and response (EDR), and robust logging infrastructure.
- Business Continuity and Crisis Management: Technical plans for backup management, disaster recovery, and crisis management to ensure continuity of essential services during and after an incident. This includes defining Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO).
- Supply Chain Security: Technical and organizational measures to ensure the security of the supply chain, including assessing the cybersecurity practices of direct suppliers and service providers. This may involve contractual security clauses, security audits, and adherence to supply chain security frameworks.
- Security in Network and Information Systems Acquisition, Development, and Maintenance: Implementing secure by design principles, secure coding practices (e.g., OWASP Top 10 mitigation), configuration management, change management, and regular security testing (e.g., penetration testing, vulnerability scanning) throughout the software development lifecycle (SDLC).
- Vulnerability Handling and Disclosure: Establishing procedures for identifying, documenting, and remediating vulnerabilities, including a coordinated vulnerability disclosure (CVD) policy and timely application of security patches.
- Policies and Procedures on the Use of Cryptography and Encryption: Technical policies on the appropriate use of strong cryptographic algorithms (e.g., AES-256 for symmetric data at rest, TLS 1.2+ for data in transit) and key management practices.
- Human Resources Security, Access Control, and Asset Management: Implementing robust identity and access management (IAM) systems, multi-factor authentication (MFA) for critical systems, least privilege principles, and secure asset inventories (hardware and software).
- Multi-Factor Authentication (MFA) and Secure Communications: Mandating MFA or continuous authentication solutions where appropriate. Ensuring secured voice, video, and text communications, and secured emergency communication systems (e.g., encrypted communication channels).
- Incident Reporting (Article 23):
- Technical Detail: Strict timelines and requirements for notifying significant cybersecurity incidents to the relevant CSIRT or competent authority.
- Process:
- Early Warning (within 24 hours): Initial notification indicating if the incident appears malicious or unlawful.
- Incident Notification (within 72 hours): Update on the incident, including a preliminary assessment of its severity and impact.
- Final Report (within one month): Detailed report on the incident, its root cause, impact, and mitigation measures taken.
- Entities may also be required to notify recipients of their services if the incident is likely to adversely affect the provision of those services.
- Governance and Accountability (Article 20):
- Technical Detail: Management bodies are explicitly required to approve and oversee cybersecurity risk management measures. This includes ensuring adequate cybersecurity training for management and employees.
- National Cybersecurity Strategies: Member States must develop national cybersecurity strategies that include policies on supply chain security, vulnerability management, and cybersecurity education and awareness.
Why Is EU NIS2 Directive Compliance Important?
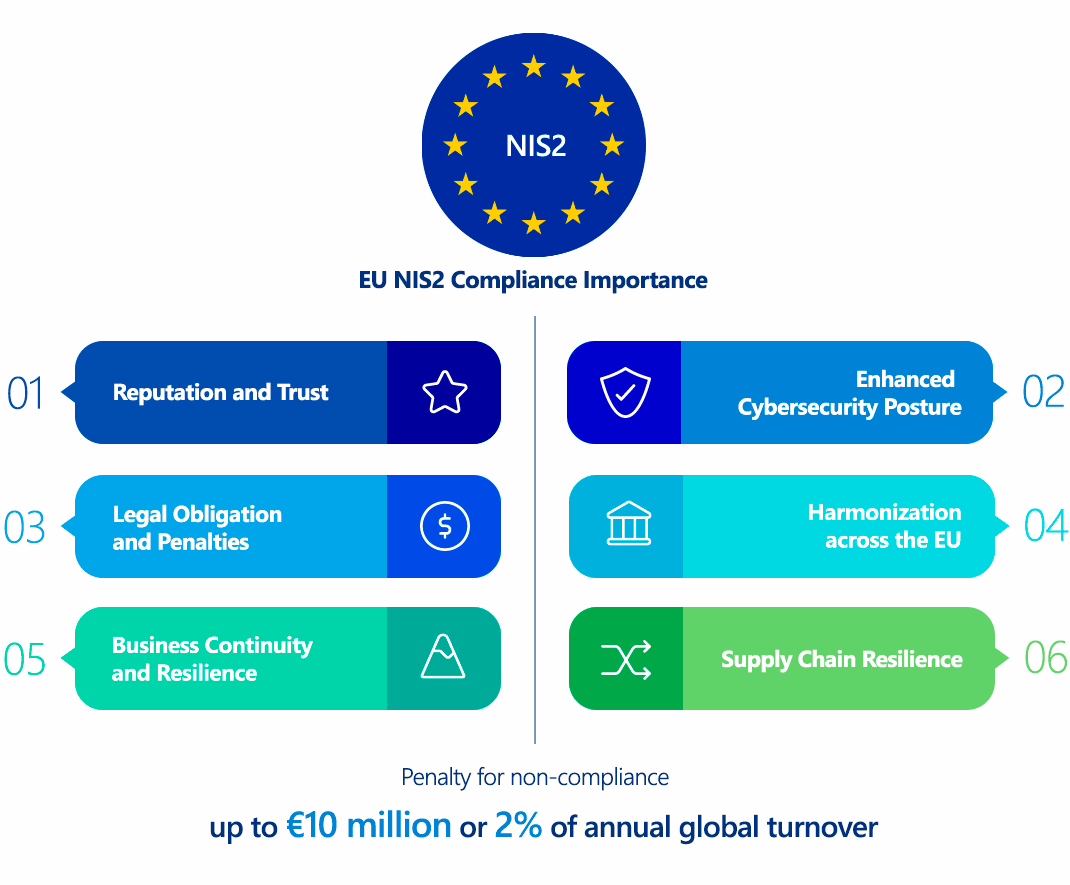
Compliance with NIS2 is paramount for several reasons:
- Legal Obligation and Penalties: Failure to comply can result in significant administrative fines (up to €10 million or 2% of global annual turnover for Essential Entities, and up to €7 million or 1.4% for Important Entities). Non-monetary penalties can also be imposed, including compliance orders, mandatory security audits, and public notification of non-compliance. Management bodies can also be held personally liable.
- Enhanced Cybersecurity Posture: The Directive compels organizations to adopt a proactive and systematic approach to cybersecurity, leading to a higher overall level of resilience against cyberattacks. This protects not only the organization but also the critical services it provides to the wider economy and society.
- Business Continuity and Resilience: By mandating robust business continuity and incident response plans, NIS2 helps organizations minimize downtime and impact in the event of a cyber incident, ensuring the continued provision of essential services.
- Reputation and Trust: Adherence to NIS2 demonstrates a commitment to strong cybersecurity, building trust with customers, partners, and regulators. This can be a significant competitive differentiator in an increasingly digital and interconnected world.
- Supply Chain Resilience: The focus on supply chain security strengthens the overall cybersecurity ecosystem, as vulnerabilities in one part of the chain can have cascading effects.
- Harmonization across the EU: By establishing a common baseline, NIS2 reduces fragmentation and inconsistencies in cybersecurity requirements across Member States, simplifying compliance for organizations operating across borders.
Who Needs to Comply with the EU NIS2 Directive?
NIS2 significantly expands the scope of entities covered compared to NIS1. It applies to medium-sized and large entities (generally 50+ employees or €10M+ annual revenue) operating in the following sectors, divided into "Essential" and "Important" categories:
Essential Entities:
- Energy: Electricity, district heating and cooling, oil, gas, hydrogen.
- Transport: Air, rail, water, road.
- Banking: Credit institutions.
- Financial Market Infrastructures: Trading venues, central counterparties.
- Health: Healthcare providers, EU reference laboratories, pharmaceutical companies.
- Drinking Water: Water suppliers.
- Wastewater: Wastewater management.
- Digital Infrastructure: DNS service providers, TLD name registries, cloud computing service providers, data centre service providers, content delivery network providers, managed service providers, managed security service providers
- ICT Service Management (B2B): Managed service providers and managed security service providers.
- Public Administration: Central and regional public administration.
- Space: Operators of ground-based infrastructure.
Important Entities:
- Postal and Courier Services.
- Waste Management.
- Manufacture, Production, and Distribution of Chemicals.
- Production, Processing, and Distribution of Food.
- Manufacturing: Manufacturers of medical devices, computer, electronic, optical products, electrical equipment, machinery, motor vehicles, other transport equipment.
- Digital Providers: Online marketplaces, online search engines, social networking service platforms.
- Research: Research organizations.
Exemptions: Micro and small entities (fewer than 50 employees AND less than €10M turnover) are generally excluded, except in specific cases where they are deemed critical by a Member State or provide unique services.
The Directive has extra-territorial reach, meaning it applies to entities established outside the EU if they offer services within the Union.
EU NIS2 Directive vs. GDPR Comparison
Both NIS2 and GDPR are pivotal EU legislations aimed at safeguarding digital rights and security, but they focus on different aspects:
| Feature | EU NIS2 Directive | GDPR |
|---|---|---|
| Primary Focus | Enhancing the cybersecurity resilience of network and information systems for critical services and digital providers. | Protecting personal data and privacy for individuals. |
| Scope | Applies to specific sectors and types of entities deemed "essential" or "important" for the economy and society. Focuses on the security of the systems themselves. | Applies to any organization that processes personal data of EU residents, regardless of sector or size (with micro-enterprise exceptions). Focuses on data subjects and their rights. |
| Technicalities | Mandates specific cybersecurity measures: risk management, incident handling, supply chain security, network security, access control (MFA), cryptography, vulnerability management. | Requires appropriate technical and organizational measures to protect personal data (e.g., encryption, pseudonymization, data minimization, access controls, regular security testing). |
| Incident Reporting | Reporting of significant cybersecurity incidents (impacting service availability, integrity, confidentiality) to CSIRTs/competent authorities. | Reporting of personal data breaches to Data Protection Authorities (DPAs) and, in high-risk cases, to affected individuals. |
| Overlaps | Strong cybersecurity (NIS2) is a prerequisite for protecting personal data (GDPR). A NIS2 incident, if it leads to unauthorized access or loss of personal data, will likely also be a GDPR breach. | GDPR's requirements for data security often necessitate the implementation of cybersecurity measures that align with NIS2's mandates. NIS2 helps organizations establish the technical controls needed for GDPR compliance. |
| Penalties | Up to €10M or 2% of global annual turnover (Essential); up to €7M or 1.4% (Important). | Up to €20M or 4% of global annual turnover. |
In essence, NIS2 mandates the "how" of securing the critical digital infrastructure, while GDPR dictates the "what" of protecting personal data regardless of where or how it's processed. Organizations handling personal data within NIS2-scoped services must comply with both, with NIS2 providing the framework for the underlying system security necessary to uphold GDPR's privacy principles.
How to Ensure EU NIS2 Directive Compliance?
Achieving NIS2 compliance requires a strategic and multi-faceted approach, encompassing technical, organizational, and governance aspects:
- Scope Assessment and Categorization:
- Technical Step: Thoroughly assess your organization's activities and services to determine if it falls under the scope of NIS2 (Essential or Important entity).
- Technical Detail: Analyze company size (employees, turnover), sector, and the criticality of services provided to identify applicable obligations. This may involve mapping critical systems and services that, if disrupted, would have a significant impact.
- Conduct Comprehensive Risk Analysis and Management:
- Technical Step: Implement a robust cybersecurity risk management framework aligned with international standards (e.g., ISO/IEC 27001, NIST Cybersecurity Framework).
- Technical Detail: Conduct detailed threat modeling and vulnerability assessments for all in-scope network and information systems. This involves identifying specific technical risks like unpatched software, misconfigurations, weak authentication, insecure APIs, and network vulnerabilities. Prioritize risks based on likelihood and impact, and implement proportionate technical controls. Regularly review and update risk assessments (e.g., annually or after significant system changes).
- Implement Mandatory Baseline Security Measures (Technical):
- Technical Step: Systematically implement the ten minimum security measures outlined in Article 21 of NIS2.
- Technical Detail:
- Incident Handling: Deploy SIEM, EDR, intrusion detection/prevention systems (IDS/IPS), and establish automated alerting. Develop runbooks for incident response, including forensic capabilities.
- Business Continuity: Implement redundant systems, regularly test backups (e.g., using secure offsite storage, immutable backups), and conduct disaster recovery drills.
- Supply Chain Security: Implement secure development and acquisition policies for software and hardware. Conduct security assessments (e.g., penetration tests, code reviews) of critical third-party components and services. Contractually mandate security requirements for suppliers.
- Secure System Acquisition, Development, and Maintenance: Adopt a Secure SDLC (SSDLC) with integrated security testing (SAST, DAST, IAST) throughout the development pipeline. Implement patch management processes for all software and hardware components.
- Vulnerability Management: Establish a formal vulnerability management program, including regular scanning (internal/external), penetration testing, and a clear patching cadence. Implement a vulnerability disclosure program.
- Cryptography and Encryption: Enforce strong encryption for data at rest and in transit (e.g., full disk encryption, database encryption, TLS 1.2+ for network communications). Implement robust key management practices (e.g., hardware security modules - HSMs).
- Access Control and MFA: Implement least privilege access models. Deploy MFA for all remote access and access to critical internal systems. Utilize strong password policies and continuous authentication where appropriate. Implement robust asset management systems.
- Secure Communications: Ensure all internal and external critical communications (voice, video, text) are encrypted and authenticated.
- Establish Robust Incident Reporting Procedures:
- Technical Step: Develop a clear incident response plan with defined roles, responsibilities, and communication channels.
- Technical Detail: Implement systems for rapid incident detection, classification, and initial assessment. Ensure technical capabilities for gathering and preserving incident-related data for reporting and forensic analysis. Define clear internal and external (to CSIRTs/competent authorities) notification timelines and content.
- Strengthen Governance and Accountability:
- Technical Step: Engage top management in cybersecurity oversight.
- Technical Detail: Provide regular cybersecurity awareness training for all employees and specialized training for IT and management teams. Integrate cybersecurity risk into enterprise risk management frameworks.
- Regular Audits and Reviews:
- Technical Step: Conduct periodic internal and external cybersecurity audits and effectiveness evaluations of implemented measures.
- Technical Detail: This includes security assessments, penetration tests, and compliance audits to verify adherence to NIS2 requirements and identify areas for continuous improvement.
Consequences of Non-Compliance with the EU NIS2 Directive
Non-compliance with NIS2 carries significant repercussions:
- Administrative Fines:
- Essential Entities: Up to €10 million or 2% of the entity's total worldwide annual turnover for the preceding financial year, whichever is higher.
- Important Entities: Up to €7 million or 1.4% of the entity's total worldwide annual turnover for the preceding financial year, whichever is higher.
- Non-Monetary Sanctions: National authorities can impose various non-financial measures, including:
- Binding instructions on specific cybersecurity measures.
- Mandatory security audits.
- Compliance orders requiring remediation of violations.
- Temporary bans on providing services or engaging in certain activities.
- Orders to notify the organization's customers of significant cybersecurity risks.
- Management Liability: Members of management bodies can be held liable for breaches of cybersecurity risk management obligations, potentially including temporary bans from management roles in cases of repeated violations.
- Reputational Damage: Non-compliance and security incidents can severely damage an organization's reputation, erode customer trust, and impact business relationships.
- Operational Disruption: Inadequate cybersecurity can lead to severe operational disruptions, service outages, and significant financial losses due to recovery efforts, regulatory fines, and potential legal claims.
How ImmuniWeb Helps Comply with the EU NIS2 Directive
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides robust technical capabilities that directly support organizations in achieving and maintaining compliance with several critical aspects of the EU NIS2 Directive.
Here's how ImmuniWeb specifically aids NIS2 compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
In essence, ImmuniWeb acts as a critical technical enabler for NIS2 compliance, particularly for the rigorous cybersecurity risk management, vulnerability handling, and secure development mandates that form the core of the Directive.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
