Health Insurance Portability and Accountability Act (HIPAA) Compliance
The Health Insurance Portability and Accountability Act (HIPAA) is a U.S. law that establishes
data privacy and security standards to protect patients' medical records and
other personal health information.

The digital transformation of healthcare has brought unprecedented efficiencies and advancements, but it also introduced significant challenges, particularly concerning the privacy and security of sensitive patient information.
Addressing these concerns, the U.S. Congress enacted the Health Insurance Portability and Accountability Act (HIPAA) in 1996. More than just a legal framework, HIPAA is a foundational pillar for safeguarding Protected Health Information (PHI) in an increasingly interconnected healthcare landscape.
Overview of Health Insurance Portability and Accountability Act (HIPAA)
HIPAA primarily aims to modernize the flow of healthcare information, stipulate how personally identifiable health information maintained by the healthcare and healthcare insurance industries should be protected from fraud and theft, and address limitations on healthcare insurance coverage. It's broadly divided into five titles, but Titles I and II are the most relevant to data privacy and security:
- Title I: Health Care Access, Portability, and Renewability: This section focuses on protecting health insurance coverage for workers and their families when they change or lose their jobs, limiting exclusions for pre-existing conditions.
- Title II: Administrative Simplification: This is the core of HIPAA's data security and privacy mandates. It requires the Department of Health and Human Services (HHS) to establish national standards for electronic healthcare transactions and national identifiers for providers, health plans, and employers. Crucially, it includes the Privacy Rule, the Security Rule, and the Breach Notification Rule.

Key Aspects of Health Insurance Portability and Accountability Act (HIPAA) Compliance
HIPAA compliance is multifaceted, encompassing administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and availability of PHI.
- The HIPAA Privacy Rule: This rule sets national standards for the protection of individually identifiable health information (PHI) by Covered Entities and Business Associates.
- Technical Details: The Privacy Rule dictates how PHI can be used (within an organization) and disclosed (shared outside an organization). It emphasizes the "minimum necessary" principle, meaning only the essential PHI required for a specific purpose should be used or disclosed. Patients are granted rights to access their medical records, request corrections, and obtain an accounting of disclosures. Technically, this translates to systems and processes that:
- Track and log all access to PHI.
- Implement granular access controls based on roles and responsibilities.
- Provide mechanisms for patients to request and receive their PHI securely (e.g., secure patient portals).
- Support the amendment of records upon patient request, with clear audit trails.
- Ensure proper de-identification or anonymization of data when PHI is not strictly necessary for research or public health.
- Technical Details: The Privacy Rule dictates how PHI can be used (within an organization) and disclosed (shared outside an organization). It emphasizes the "minimum necessary" principle, meaning only the essential PHI required for a specific purpose should be used or disclosed. Patients are granted rights to access their medical records, request corrections, and obtain an accounting of disclosures. Technically, this translates to systems and processes that:
- The HIPAA Security Rule: This rule specifically addresses the protection of Electronic Protected Health Information (ePHI). It mandates specific administrative, physical, and technical safeguards.
- Technical Safeguards: These are critical for securing ePHI and include:
- Access Control: Implementing technical policies and procedures to allow only authorized persons to access ePHI. This involves unique user IDs, emergency access procedures, automatic logoff, and encryption/decryption mechanisms.
- Audit Controls: Implementing hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI. This is crucial for detecting and responding to suspicious activities.
- Integrity: Implementing policies and procedures to ensure that ePHI has not been improperly altered or destroyed. This can involve checksums, digital signatures, and message authentication codes.
- Transmission Security: Implementing technical security measures to guard against unauthorized access to ePHI that is being transmitted over an electronic network. This requires encryption of ePHI when transmitted over open networks (e.g., TLS/SSL for web communications, VPNs).
- Person or Entity Authentication: Implementing procedures to verify that a person or entity seeking access to ePHI is the one claimed. Multi-factor authentication (MFA) is a common technical safeguard here.
- Physical Safeguards: These address the physical security of electronic information systems, equipment, and the facility itself. Examples include facility access controls, workstation security, and device and media controls (e.g., secure disposal of hardware).
- Administrative Safeguards: These are the backbone of a HIPAA compliance program, requiring organizations to:
- Conduct regular risk assessments to identify threats and vulnerabilities to ePHI.
- Implement risk management plans to mitigate identified risks.
- Develop and implement security policies and procedures.
- Provide security awareness and training for all workforce members.
- Establish contingency plans for data backup and disaster recovery.
- Manage workforce security (e.g., authorization, supervision, termination procedures).
- Technical Safeguards: These are critical for securing ePHI and include:
- The HIPAA Breach Notification Rule: This rule requires Covered Entities and Business Associates to notify affected individuals, the Secretary of HHS, and in some cases, the media, following a breach of unsecured PHI.
- Technical Details: Organizations need robust incident response plans that technically allow for:
- Rapid detection and containment of breaches.
- Forensic analysis to determine the scope and nature of the breach.
- Secure communication channels for notification.
- Maintenance of detailed records of all breach incidents and remediation efforts.
- Technical Details: Organizations need robust incident response plans that technically allow for:
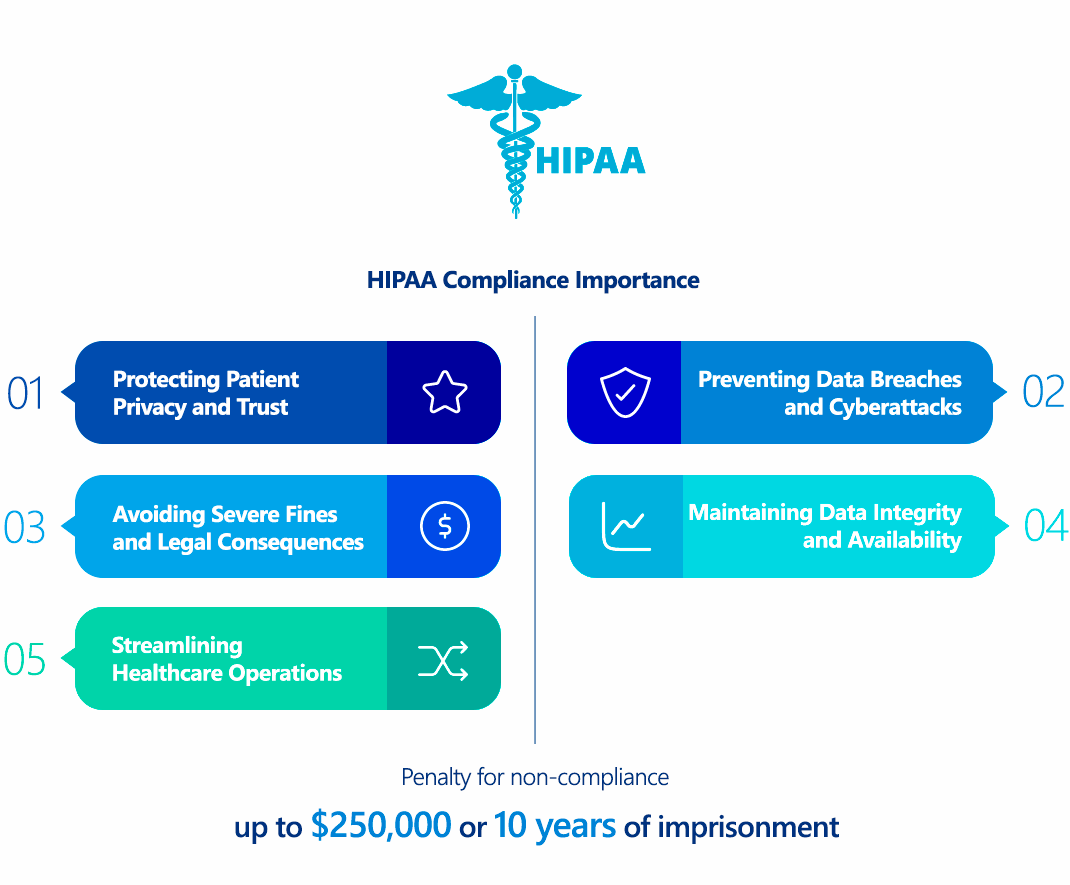
Why Is Health Insurance Portability and Accountability Act (HIPAA) Compliance Important?
HIPAA compliance is paramount for several critical reasons:
- Protecting Patient Privacy and Trust: At its core, HIPAA ensures patients' sensitive health information is protected, fostering trust in healthcare providers and the healthcare system. Without these protections, individuals might be hesitant to share vital health details, impacting the quality of care.
- Preventing Data Breaches and Cyberattacks: By mandating strong security safeguards, HIPAA reduces the likelihood and impact of data breaches. This protection is crucial as ePHI is highly valuable to cybercriminals for identity theft, fraud, and ransomware attacks.
- Maintaining Data Integrity and Availability: The Security Rule's focus on integrity ensures that ePHI remains accurate and unaltered, which is vital for effective patient care. Availability ensures that authorized healthcare professionals can access patient data when and where needed, especially in emergencies.
- Avoiding Severe Penalties and Legal Consequences: Non-compliance can lead to substantial financial penalties, civil lawsuits, and even criminal charges. Reputational damage from a breach can be long-lasting and severe, eroding public trust and patient loyalty.
- Streamlining Healthcare Operations: By standardizing electronic transactions and promoting secure data exchange, HIPAA aims to improve efficiency and reduce administrative burdens across the healthcare industry.
Who Needs to Comply with Health Insurance Portability and Accountability Act (HIPAA)?
HIPAA compliance is not universal; it applies specifically to:
- Covered Entities (CEs): These are organizations directly involved in healthcare that transmit health information electronically in connection with certain transactions. This includes:
- Health Plans: Health insurance companies, HMOs, Medicare, Medicaid, etc.
- Healthcare Clearinghouses: Entities that process nonstandard health information into a standard format or vice versa.
- Healthcare Providers: Any provider (e.g., doctors, hospitals, clinics, dentists, pharmacies) who electronically transmits health information for certain transactions (e.g., claims, eligibility inquiries, referral authorizations).
- Business Associates (BAs): These are persons or entities that perform functions or activities on behalf of, or provide services to, a Covered Entity that involves the use or disclosure of PHI. Examples include billing companies, cloud service providers storing ePHI, IT service providers, legal firms, and consultants.
- Business Associate Subcontractors: Any subcontractor of a Business Associate that creates, receives, maintains, or transmits PHI on behalf of the Business Associate is also subject to HIPAA compliance.
Crucially, Business Associate Agreements (BAAs) are legally required contracts between Covered Entities and Business Associates (and between BAs and their subcontractors) that outline the permissible uses and disclosures of PHI and the security responsibilities of the BA.
Health Insurance Portability and Accountability Act (HIPAA) vs GDPR Comparison
While both HIPAA and the General Data Protection Regulation (GDPR) are comprehensive data protection laws, they differ significantly in scope, focus, and technical requirements:
| Feature | HIPAA (U.S.) | GDPR (EU) |
|---|---|---|
| Scope | U.S.-focused, specific to Protected Health Information (PHI) and healthcare industry. | Global, applies to all personal data of EU residents, regardless of industry. |
| Data Definition | PHI: Identifiable health information (medical records, billing, demographics). | Personal Data: Broader, includes names, IP addresses, location, genetic, biometric data, etc. |
| Consent | Allows implied consent for treatment, payment, and healthcare operations. Explicit consent often required for other uses (e.g., marketing). | Explicit, unambiguous consent generally required for data processing, with clear right to withdraw. |
| Breach Notification | Covered Entities must notify affected individuals within 60 days of discovery; HHS and media for larger breaches. | Data controllers must notify supervisory authorities within 72 hours of becoming aware of a breach. |
| "Right to be Forgotten" | Not explicitly included. Medical records are generally retained. | Yes, individuals can request deletion of their data under certain conditions. |
| Data Protection Officer (DPO) | Not explicitly required, though a Security Official is mandated. | Mandatory for organizations processing large-scale special categories of data (including health data). |
| Cross-Border Data Transfer | Primarily focuses on domestic data handling. | Strict rules for transferring data outside the EU, requiring specific safeguards (e.g., Standard Contractual Clauses). |
| Penalties | Tiered civil monetary penalties up to $1.5 million per violation per year; criminal penalties up to $250,000 and 10 years imprisonment. | Higher, up to €20 million or 4% of annual global turnover, whichever is higher. |
| Security Framework | Flexible, risk-based approach with mandated administrative, physical, and technical safeguards. | Risk-based, emphasizes "privacy by design" and "privacy by default," with specific technical requirements like encryption. |
For organizations handling data from both U.S. and EU residents, compliance often necessitates adopting the stricter requirements of GDPR (e.g., consent, breach notification timelines) while ensuring adherence to HIPAA's specific healthcare-focused rules.
How to Ensure Health Insurance Portability and Accountability Act (HIPAA) Compliance?
Achieving and maintaining HIPAA compliance is an ongoing process that requires a strategic and technical approach:
- Conduct a Comprehensive Risk Assessment and Management:
- Technical Action: Systematically identify all ePHI across your organization (at rest and in transit). Conduct thorough vulnerability scans, penetration testing, and architectural reviews of all systems handling ePHI (e.g., EHR systems, cloud storage, network infrastructure, mobile applications). Identify potential threats (e.g., malware, unauthorized access, insider threats) and vulnerabilities (e.g., weak encryption, misconfigured firewalls, unpatched software). Assess the likelihood and impact of each risk. Develop a detailed risk management plan to mitigate identified risks, prioritizing based on severity.
- Implement Robust Technical Safeguards:
- Access Control: Implement role-based access control (RBAC) systems with least privilege principles. Use strong, unique passwords and enforce multi-factor authentication (MFA) for all access to ePHI, especially for remote access. Implement automatic logoff for workstations and systems.
- Encryption: Encrypt ePHI both in transit (e.g., TLS 1.2+ for web traffic, secure VPNs for internal networks) and at rest (e.g., full disk encryption, database encryption, cloud storage encryption like AES-256). Securely manage encryption keys.
- Audit Controls: Enable comprehensive logging on all systems, applications, and network devices that interact with ePHI. Implement a Security Information and Event Management (SIEM) system to aggregate, correlate, and analyze logs in real-time, detecting suspicious activities and potential breaches. Regularly review audit logs.
- Integrity Controls: Implement data integrity checks (e.g., checksums, digital signatures) to detect unauthorized alteration or destruction of ePHI. Ensure robust backup and recovery procedures are in place.
- Network Security: Deploy and properly configure firewalls, intrusion detection/prevention systems (IDS/IPS), and secure network segmentation to protect ePHI from external and internal threats. Regularly scan for and remediate network vulnerabilities.
- Develop and Implement Comprehensive Policies and Procedures:
- Technical Action: Document clear policies for data handling, access management, incident response, data retention, and disposal. Develop detailed technical procedures for configuring security controls, managing user accounts, performing backups, and responding to security incidents.
- Provide Regular Workforce Training and Awareness:
- Technical Action: Train all employees on HIPAA regulations, organizational policies, and specific technical security measures (e.g., recognizing phishing attempts, proper handling of secure credentials, reporting suspicious activities). Conduct regular phishing simulations and security awareness campaigns.
- Secure Business Associate Agreements (BAAs):
- Technical Action: Ensure all third-party vendors and service providers who handle PHI on your behalf sign a BAA. Technically, this involves vetting their security posture, conducting vendor risk assessments, and ensuring their systems and practices align with HIPAA requirements.
- Establish a Robust Breach Notification and Incident Response Plan:
- Technical Action: Develop a detailed incident response plan that includes clear steps for identification, containment, eradication, recovery, and post-incident analysis of a security breach. This plan should define roles and responsibilities, communication protocols, and technical procedures for forensic investigation and data recovery. Implement systems for rapid and secure notification of affected individuals and regulatory bodies.
- Regular Audits and Continuous Monitoring:
- Technical Action: Conduct periodic internal and external audits of your HIPAA compliance efforts. Perform continuous monitoring of your network, systems, and applications for security events and vulnerabilities. This includes regular vulnerability scanning, penetration testing, and security posture assessments.
Consequences of Non-Compliance with Health Insurance Portability and Accountability Act (HIPAA)
The consequences of HIPAA non-compliance can be severe, encompassing financial, legal, and reputational damages:
- Financial Penalties: The Office for Civil Rights (OCR) categorizes violations into tiers, with fines varying based on the level of negligence:
- Tier 1 (Unknowing): $137 to $68,928 per violation (maximum $1.5 million per year for identical violations).
- Tier 2 (Reasonable Cause): $1,379 to $68,928 per violation (maximum $1.5 million per year).
- Tier 3 (Willful Neglect - Corrected): $13,787 to $68,928 per violation (maximum $1.5 million per year).
- Tier 4 (Willful Neglect - Uncorrected): Minimum $68,928 per violation (maximum $1.5 million per year).
- Criminal Penalties: Individuals who knowingly obtain or disclose PHI in violation of HIPAA can face significant fines (up to $250,000) and imprisonment (up to 10 years), especially if the intent is for personal gain, commercial advantage, or malicious harm.
- Civil Lawsuits: Patients whose PHI has been compromised may pursue civil lawsuits against the non-compliant entity, leading to substantial damages and legal fees.
- Reputational Damage: Data breaches and HIPAA violations often result in negative publicity, loss of patient trust, and damage to an organization's public image. This can lead to decreased patient enrollment, loss of business partnerships, and difficulties in hiring and retaining staff.
- Corrective Action Plans (CAPs): The OCR often mandates CAPs, requiring organizations to implement specific measures to address compliance deficiencies, which can be resource-intensive and costly.
- Exclusion from Medicare/Medicaid: In severe cases, non-compliant entities may be excluded from participation in federal healthcare programs.
How ImmuniWeb Helps Comply with Health Insurance Portability and Accountability Act (HIPAA)?
Many cybersecurity and compliance solutions exist to help organizations navigate the complexities of HIPAA. ImmuniWeb, with its AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform, offers a comprehensive suite of services that can significantly bolster an organization's HIPAA compliance posture, particularly concerning the technical safeguards of the Security Rule:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
In conclusion, HIPAA is an evolving and critical regulation that underscores the fundamental importance of protecting patient health information. By understanding its core principles, implementing robust technical safeguards, fostering a culture of compliance, and leveraging advanced security solutions like ImmuniWeb, healthcare organizations can effectively mitigate risks, build patient trust, and avoid the severe consequences of non-compliance in the digital age.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
