Hong Kong Personal Data Privacy Ordinance (PDPO) Compliance
The Hong Kong Personal Data Privacy Ordinance (PDPO), enacted in 1996 and amended over time, is the city's
primary data protection law, governing the collection, use, and security of personal
data under six Data Protection Principles (DPPs).

The digital landscape of Hong Kong is governed by the Personal Data (Privacy) Ordinance (PDPO), a comprehensive and technology-neutral law designed to protect individuals' personal data. Enacted in 1995 and notably amended in 2012 and 2021, the PDPO serves as the cornerstone of data privacy in the region, impacting both private and public sector organizations.
Overview of PDPO
The PDPO sets out a framework for the responsible collection, holding, processing, and use of personal data. Its core is built upon six Data Protection Principles (DPPs), which guide data users (similar to data controllers in other jurisdictions) in handling personal information. These principles are:
- DPP1: Purpose and Manner of Collection: Personal data must be collected lawfully and fairly, for a specific and lawful purpose, and should be necessary but not excessive. Data subjects must be informed about the purpose of collection and potential data transfers.
- DPP2: Accuracy and Duration of Retention: Personal data must be accurate, up-to-date, and retained only for as long as necessary to fulfill the purpose for which it was collected.
- DPP3: Use of Personal Data: Personal data can only be used for the purpose it was collected or a directly related purpose, unless explicit and voluntary consent is obtained for new uses.
- DPP4: Data Security: Data users must take all practicable steps to safeguard personal data from unauthorized or accidental access, processing, erasure, loss, or use, considering factors like data type and potential harm. This includes implementing appropriate technical and organizational measures.
- DPP5: Openness: Data users must be transparent about their personal data policies and practices, including the types of data they hold and their main purposes of use.
- DPP6: Data Access and Correction: Data subjects have the right to access and request correction of their personal data held by data users.
The 2021 amendments notably introduced new offenses for doxxing and empowered the Privacy Commissioner for Personal Data (PCPD) with enhanced enforcement powers, including the ability to issue cessation notices and prosecute offenders. While a mandatory data breach notification mechanism is still under consideration, the PCPD strongly recommends voluntary notification.

Key Aspects of PDPO Compliance
Achieving PDPO compliance requires a holistic approach, encompassing both legal and technical considerations. Key aspects include:
- Data Inventory and Mapping: Organizations must identify and document all personal data they collect, process, and store. This involves understanding data flows within the organization, from collection points to storage, processing, and eventual deletion.
- Consent Management: Implementing robust mechanisms for obtaining, managing, and documenting explicit and voluntary consent from data subjects, especially for direct marketing or using data for purposes beyond the original collection.
- Privacy Policies and Notices: Developing clear, concise, and easily accessible privacy policies that explain how personal data is collected, used, and protected. These policies should align with DPP1 and DPP5.
- Data Security Measures (DPP4): This is where technical details become critical. Organizations must implement "all practicable steps" to secure personal data. This broadly includes:
- Access Controls: Implementing strong authentication mechanisms (e.g., multi-factor authentication, strong password policies), role-based access control (RBAC), and the principle of least privilege to restrict data access to authorized personnel only. This extends to granular controls over databases, applications, and operating systems.
- Encryption: Encrypting personal data both in transit (e.g., using Transport Layer Security/Secure Sockets Layer (TLS/SSL) for web communications, VPNs for remote access) and at rest (e.g., encrypting databases, file systems, and storage volumes using AES-256 or similar strong algorithms). Key management is crucial here.
- Network Security: Deploying robust firewalls, intrusion detection/prevention systems (IDS/IPS), and regularly patching network devices, operating systems, and applications to prevent unauthorized access and cyberattacks. Network segmentation and micro-segmentation can further isolate critical data.
- Application Security: Conducting regular security testing (e.g., penetration testing, vulnerability scanning, static/dynamic application security testing (SAST/DAST)) for web and mobile applications to identify and remediate vulnerabilities (e.g., OWASP Top 10) that could lead to data breaches. Secure API development and management are also vital.
- Data Minimization and Retention: Designing systems and processes to collect only necessary data (DPP1) and implementing automated data retention policies to erase data when it's no longer required, in accordance with DPP2 and Section 26 of the PDPO. This often involves secure data sanitization techniques.
- Backup and Recovery: Implementing robust backup and disaster recovery plans to ensure data availability and integrity in case of data loss, corruption, or system failures. Regular testing of these plans is essential.
- Incident Response Plan: Developing and regularly testing a comprehensive data breach incident response plan to promptly detect, contain, investigate, and assess the risk of harm to affected individuals, and if necessary, notify relevant parties (PCPD and affected individuals).
- Logging and Monitoring: Implementing comprehensive logging of all system and data access activities, and continuously monitoring these logs for suspicious patterns or security incidents. Security Information and Event Management (SIEM) systems can centralize and analyze logs.
- Data Subject Rights Management: Establishing clear procedures for handling data access requests (DSARs) and requests for data correction (DPP6) in a timely and secure manner. This often requires secure portals or defined communication channels for data subjects.
- Third-Party Risk Management: Ensuring that any third-party data processors (e.g., cloud service providers, IT vendors) engaged by the data user also comply with PDPO requirements, typically through robust contractual agreements, due diligence, security audits, and ongoing monitoring.
- Employee Training: Regularly training employees on data privacy best practices, the importance of PDPO compliance, and their specific responsibilities in handling personal data, including recognizing and reporting security incidents.
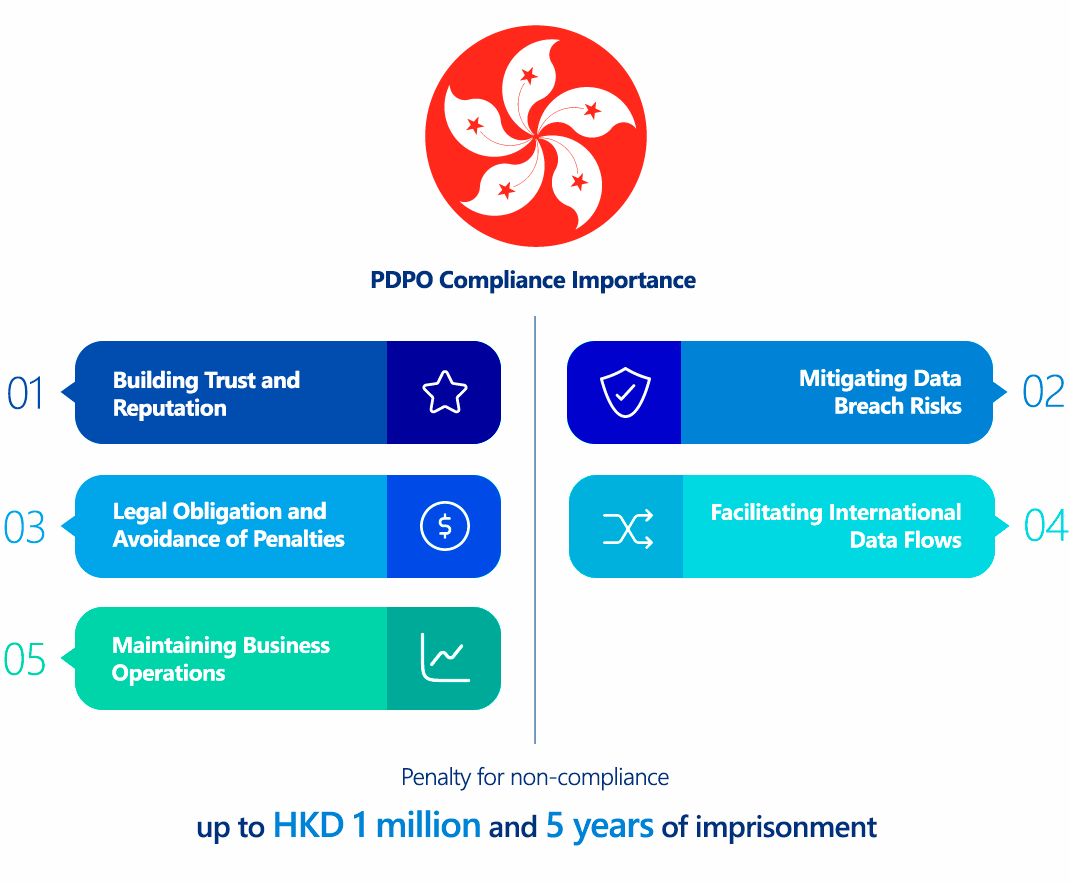
Why is PDPO Compliance Important?
PDPO compliance is crucial for several reasons:
- Legal Obligation and Avoidance of Penalties: Non-compliance can lead to significant fines, imprisonment, and legal action. The PCPD has the power to issue enforcement notices, which if not complied with, can result in criminal penalties (fines up to HKD 100,000 and two years' imprisonment for repeat offenses). Offenses like doxxing carry even higher penalties (up to HKD 1 million and five years' imprisonment).
- Building Trust and Reputation: Demonstrating a commitment to data privacy fosters trust with customers, partners, and the public, enhancing an organization's reputation and competitive advantage.
- Mitigating Data Breach Risks: Robust compliance measures, particularly technical security controls, significantly reduce the likelihood and impact of data breaches, which can be costly in terms of financial losses, reputational damage, and legal liabilities.
- Maintaining Business Operations: Data breaches can disrupt business operations, leading to downtime, loss of revenue, and complex recovery efforts. Compliance helps ensure business continuity.
- Facilitating International Data Flows: As data increasingly flows across borders, demonstrating strong data protection practices, such as PDPO compliance, can facilitate partnerships and trade with jurisdictions that have similar privacy laws, potentially simplifying data transfer agreements.
Who Needs to Comply with PDPO?
The PDPO applies broadly to "data users" who control the collection, holding, processing, or use of personal data in or from Hong Kong. This includes:
- All private and public sector organizations operating in Hong Kong, regardless of their size or industry.
- Organizations that process personal data of individuals in Hong Kong, even if the processing occurs outside Hong Kong, as long as the data user is based in Hong Kong.
- Data Processors are not directly regulated under the PDPO. However, data users are obligated to ensure, through contractual or other means, that their data processors comply with the relevant data retention and security requirements (DPP2 and DPP4).
There are limited exemptions, such as for data held for domestic or recreational purposes, or for certain employment-related data under specific conditions.
PDPO vs GDPR Comparison
While both the PDPO and the EU's General Data Protection Regulation (GDPR) aim to protect personal data, they have notable differences, particularly in their technical implications:
| Feature | Hong Kong PDPO | EU GDPR |
|---|---|---|
| Territorial Scope | Applies to data users who control data in or from Hong Kong. Limited extraterritoriality based on data user's control in HK. | Broader extraterritoriality: applies to controllers/processors offering goods/services to EU data subjects or monitoring their behavior, regardless of establishment. |
| Data Processor Obligations | Data processors are not directly regulated. Data users must ensure, via contract or other means, processors comply with DPP2 & DPP4. | Data processors have direct obligations (e.g., security, record-keeping, breach notification, DPO where applicable) and can be held liable. |
| Mandatory Breach Notification | No mandatory breach notification (as of current effective provisions), but PCPD strongly recommends voluntary notification. | Mandatory notification to supervisory authority within 72 hours of becoming aware of a breach, unless unlikely to result in a risk to individuals' rights and freedoms. Notification to data subjects required if high risk. |
| Sensitive Data Categories | No specific concept of "sensitive personal data," though PCPD provides guidance for certain data types (e.g., ID card numbers). | Defines "special categories of personal data" (e.g., health, racial origin, political opinions, sexual orientation) with stricter processing conditions. |
| Data Subject Rights | Rights of access and correction (DPP6). No explicit right to erasure ("right to be forgotten") or data portability. | Comprehensive rights including access, rectification, erasure, restriction of processing, data portability, and objection to processing. |
| Accountability Principle | Implicit in DPPs, particularly DPP4, requiring "all practicable steps" for security. Less explicit on "privacy by design" and "privacy by default." | Explicit "accountability" principle. Requires "data protection by design and by default," mandating proactive integration of privacy into systems and processes. |
| Data Protection Officer (DPO) | No mandatory DPO requirement, but PCPD encourages designation of a responsible person. | Mandatory DPO for public authorities, or organizations performing large-scale systematic monitoring or processing of special categories of data. |
| Cross-Border Data Transfers | Section 33 restricts cross-border transfers to jurisdictions with "comparable protection," but this section is not yet in force. Transfers generally permitted. | Stricter rules: transfers allowed to "adequate" countries, with appropriate safeguards (e.g., Standard Contractual Clauses (SCCs), Binding Corporate Rules (BCRs)), or specific derogations. |
| Penalties | Fines and imprisonment for non-compliance with enforcement notices, doxxing, and direct marketing offenses. Fines up to HKD 1 million. | Significantly higher administrative fines (up to €20 million or 4% of annual global turnover, whichever is higher) for serious infringements. Private right of action for data subjects. |
| Technical Measures Focus | "All practicable steps" for security (DPP4). Focus on reasonable measures given the context and potential harm. | More prescriptive on technical and organizational measures (Art. 32), including encryption, pseudonymization, resilience of systems, and regular testing. Emphasizes risk-based approach. |
From a technical perspective, organizations aiming for GDPR compliance will often find themselves largely compliant with PDPO's technical security requirements, as GDPR's standards are generally more stringent. However, specific nuances like data retention policies and the absence of a mandatory breach notification in PDPO (for now) require careful attention.
How to Ensure PDPO Compliance?
Ensuring PDPO compliance is an ongoing process that requires commitment from all levels of an organization. Here are key steps with technical considerations:
- Conduct a Comprehensive Data Audit and Inventory:
- Technical: Utilize data discovery tools to locate all personal data across systems (databases, file servers, cloud storage, endpoints). Map data flows, identifying where data is collected, stored, processed, and transmitted. Classify data by sensitivity.
- Organizational: Document the purpose for collecting each type of data, its retention period, and who has access.
- Develop and Implement Robust Privacy Policies and Procedures:
- Organizational: Create clear, transparent privacy policies (website, internal) that adhere to DPP1 and DPP5. Establish internal procedures for data handling, consent management, and data subject rights requests.
- Technical: Implement privacy-enhancing technologies (PETs) like anonymization or pseudonymization where appropriate to minimize identifiable data. Ensure website and application forms clearly capture consent and link to privacy policies.
- Strengthen Data Security Measures (DPP4):
- Access Control Systems: Implement Identity and Access Management (IAM) solutions with multi-factor authentication (MFA) for all critical systems. Enforce least privilege access (e.g., using role-based access control (RBAC) and attribute-based access control (ABAC)). Regularly review and revoke access as needed.
- Encryption: Deploy end-to-end encryption for data in transit (TLS 1.2+ for web/API, VPNs, secure file transfer protocols) and encryption at rest for databases, storage, and backups. Implement robust key management systems.
- Network and Endpoint Security: Utilize firewalls, Web Application Firewalls (WAFs), intrusion prevention systems (IPS), and endpoint detection and response (EDR) solutions. Maintain up-to-date antivirus/anti-malware software. Segment networks to isolate sensitive data.
- Vulnerability Management: Implement a continuous vulnerability scanning and patch management program for all software, operating systems, and network devices. Conduct regular penetration testing (internal and external) and security audits of applications and infrastructure.
- Secure Software Development Lifecycle (SSDLC): Integrate security into every phase of software development, from design to deployment, including secure coding practices, code reviews, and security testing.
- Data Minimization and Retention Automation: Design systems to collect only necessary data fields. Implement automated data deletion policies and mechanisms to securely erase data beyond its retention period (e.g., cryptographic shredding, degaussing).
- Physical Security: Secure physical access to data centers and hardware storing personal data.
- Establish a Data Breach Response Plan:
- Technical: Develop and test an incident response plan that includes procedures for detection, containment, eradication, recovery, and post-incident analysis. Implement security information and event management (SIEM) systems for real-time threat detection.
- Organizational: Clearly define roles and responsibilities, communication protocols (internal, PCPD, affected individuals), and legal review processes.
- Manage Third-Party Risks:
- Organizational: Conduct thorough due diligence on all third-party vendors and data processors. Include PDPO-specific clauses in contracts, obligating them to adhere to data protection principles, particularly DPP4.
- Technical: Implement vendor security assessments, monitor their security posture, and ensure appropriate data processing agreements are in place.
- Provide Regular Employee Training:
- Organizational: Conduct mandatory and recurring data privacy and security awareness training for all employees, emphasizing their roles and responsibilities under PDPO. Include phishing awareness and secure data handling practices.
Consequences of Non-Compliance
The PCPD is actively enforcing the PDPO, and the consequences of non-compliance can be severe:
- Enforcement Notices: The PCPD can issue enforcement notices directing data users to take specific actions to remedy or prevent a contravention of the PDPO.
- Criminal Penalties:
- Non-compliance with an Enforcement Notice: A first conviction carries a maximum fine of HKD 50,000 and two years' imprisonment. Subsequent convictions can lead to a fine of HKD 100,000 and two years' imprisonment, with daily fines for continuing offenses.
- Doxxing Offenses (since 2021): Criminal offenses for disclosing personal data without consent to cause harm. Maximum penalty: HKD 1 million fine and five years' imprisonment. Non-compliance with a cessation notice related to doxxing carries similar fines and imprisonment.
- Direct Marketing Offenses: Non-compliance with direct marketing requirements can result in fines up to HKD 1 million and five years' imprisonment, especially if personal data is transferred for gain.
- Civil Liability: Data subjects who suffer damage (including injury to feelings) due to a PDPO contravention can seek compensation through civil proceedings.
- Reputational Damage: Data breaches and non-compliance can severely damage an organization's reputation, leading to loss of customer trust, business, and competitive standing.
- Business Disruption: Investigations, legal proceedings, and the aftermath of a breach can significantly disrupt business operations.
How ImmuniWeb Helps Comply with PDPO?
ImmuniWeb, with its AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform, can significantly assist organizations in achieving and maintaining PDPO compliance, particularly concerning the technical requirements of DPP4 (Data Security).
Here's how ImmuniWeb's offerings contribute:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By integrating ImmuniWeb's AI-driven security testing and monitoring solutions, organizations can gain a clear, continuous view of their cybersecurity posture, proactively identify and mitigate risks to personal data, and demonstrate "all practicable steps" taken to comply with the technical requirements of Hong Kong's PDPO.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
