New York DFS Cybersecurity Regulation Compliance
The New York DFS Cybersecurity Regulation (23 NYCRR 500) requires financial services companies regulated
by the New York Department of Financial Services to implement a robust cybersecurity program,
including risk assessments, policies, monitoring, and reporting of cybersecurity events.

Safeguarding Financial Data: A Deep Dive into the New York DFS Cybersecurity Regulation
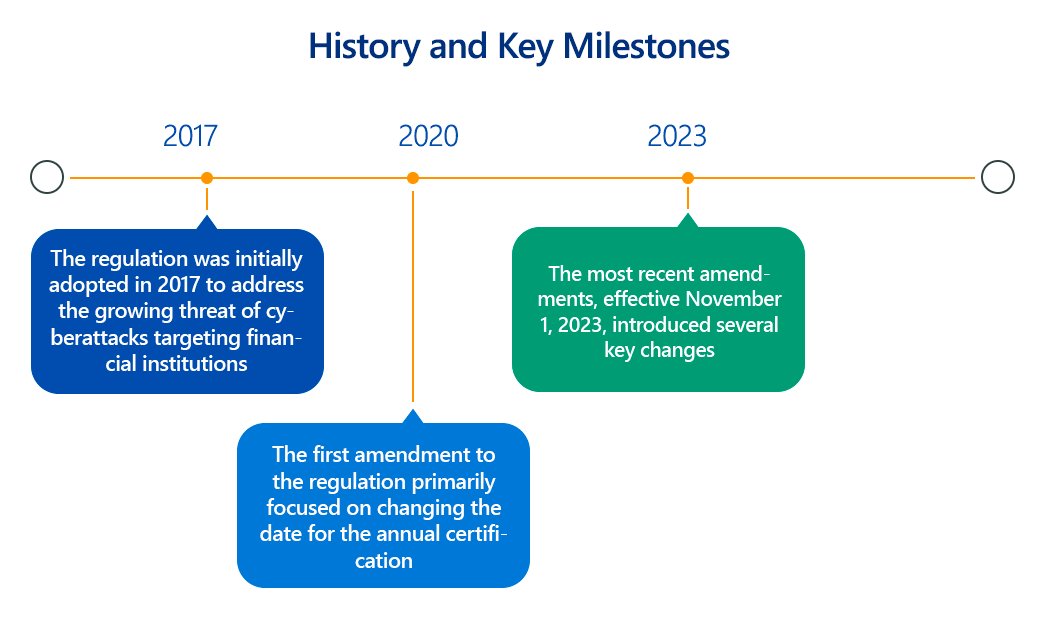
In an increasingly digital world, the financial services sector remains a prime target for sophisticated cyberattacks. Recognizing this critical threat, the New York Department of Financial Services (NYDFS) implemented a groundbreaking cybersecurity regulation, 23 NYCRR Part 500, in 2017. This regulation has since become a benchmark for robust cybersecurity practices, aiming to protect sensitive consumer data and ensure the integrity of financial institutions' information systems.
Overview of New York DFS Cybersecurity Regulation
The NYDFS Cybersecurity Regulation (23 NYCRR Part 500) establishes stringent cybersecurity requirements for financial services companies operating in New York. Its primary goal is to ensure the confidentiality, integrity, and availability of information systems and nonpublic information. The regulation mandates a comprehensive, risk-based approach to cybersecurity, requiring covered entities to develop and maintain a robust cybersecurity program tailored to their specific risk profile. This includes identifying and assessing internal and external cybersecurity risks, implementing defensive infrastructure, detecting and responding to cybersecurity events, and recovering from incidents.
Key Aspects of New York DFS Cybersecurity Regulation Compliance
Compliance with 23 NYCRR Part 500 involves several critical components, often with detailed technical requirements:
- Cybersecurity Program (Section 500.02): Covered entities must establish and maintain a cybersecurity program designed to protect information systems and nonpublic information. This program should be based on a thorough risk assessment and include processes for identifying, assessing, and mitigating risks.
- Cybersecurity Policy (Section 500.03): A comprehensive written cybersecurity policy is mandatory, outlining the entity's approach to cybersecurity. This policy should address key areas such as:
- Data Governance and Classification: Policies for categorizing and handling data based on sensitivity.
- Access Controls: Procedures for managing and limiting access to information systems and nonpublic information based on the principle of least privilege. This includes technical controls like role-based access control (RBAC), user provisioning/de-provisioning, and periodic access reviews.
- Asset Inventory: Maintaining an up-to-date inventory of all information systems and data assets.
- Business Continuity and Disaster Recovery (BCDR) Planning: Detailed plans for maintaining critical operations and recovering from cybersecurity incidents, including data backup and restoration procedures.
- Customer Data Privacy: Specific policies to protect sensitive customer information.
- Chief Information Security Officer (CISO) (Section 500.04): Entities must designate a qualified CISO responsible for overseeing and implementing the cybersecurity program. The CISO must report at least annually to the entity's board of directors or senior governing body on the state of the cybersecurity program. For Class A companies (larger entities), an independent audit of the cybersecurity program is required.
- Penetration Testing and Vulnerability Assessments (Section 500.05):
- Penetration Testing: Annual penetration testing is required from both internal and external perspectives, conducted by qualified personnel. This involves simulating real-world attacks to identify exploitable vulnerabilities in systems, networks, and applications.
- Vulnerability Assessments: Regular automated scanning of information systems and manual reviews for systems not covered by automated scans. Identified vulnerabilities must be prioritized based on risk and promptly remediated.
- Audit Trail (Section 500.06): Covered entities must maintain audit trails designed to reconstruct financial transactions and security events. This includes logging and monitoring activity on information systems to detect and respond to cybersecurity events. Technical implementation involves robust logging mechanisms (e.g., SIEM solutions) that capture relevant event data (timestamps, user IDs, event types, source/destination IPs, etc.) and retain them for a specified period (three years as of recent amendments).
- Access Privileges (Section 500.07): Strict controls over user access privileges are mandated. This involves:
- Multi-Factor Authentication (MFA): Implementation of MFA for any individual accessing the covered entity's information systems, regardless of location, user type, or information sensitivity (subject to certain exceptions, especially for Class A companies). This often involves technical solutions like hardware tokens, biometrics, or mobile authenticator apps.
- Least Privilege: Ensuring users only have the minimum access necessary to perform their job functions.
- Periodic Reviews: Regular review of access privileges to ensure they remain appropriate and are promptly terminated upon role changes or departures.
- Application Security (Section 500.08): Procedures, guidelines, and standards for secure application development must be established and annually reviewed. This includes secure coding practices, vulnerability testing during the software development lifecycle (SDLC), and protection against common application-layer attacks (e.g., SQL injection, cross-site scripting).
- Risk Assessment (Section 500.09): Regular (at least annual, or following significant changes) risk assessments are crucial. These assessments must:
- Identify, estimate, and prioritize cybersecurity risks to operations, assets, individuals, and critical infrastructure.
- Incorporate threat and vulnerability analyses.
- Evaluate existing controls' effectiveness.
- Inform the cybersecurity program and policies.
- Third-Party Service Provider Security Policy (Section 500.11): Entities must implement a written policy to address risks associated with third-party service providers who access the entity's nonpublic information or information systems. This involves due diligence, contractual safeguards requiring appropriate security measures, and ongoing monitoring of vendor compliance.
- Encryption of Nonpublic Information (Section 500.15): Nonpublic information must be encrypted "at rest" and "in transit" when feasible. This requires technical solutions like full disk encryption, database encryption, and secure communication protocols (e.g., TLS/SSL). The feasibility is determined by the entity's risk assessment.
- Incident Response Plan (Section 500.16): A comprehensive incident response plan is required, detailing procedures for detecting, responding to, and recovering from cybersecurity events. This includes roles and responsibilities, communication protocols, containment strategies, eradication, recovery, and post-incident analysis.
- Notices to Superintendent (Section 500.17): Specific cybersecurity events, particularly those with a reasonable likelihood of materially harming the normal operations of the covered entity, must be reported to the NYDFS Superintendent within 72 hours. Extortion payments related to a cybersecurity event must be reported within 24 hours.
Why Is New York DFS Cybersecurity Regulation Compliance Important?
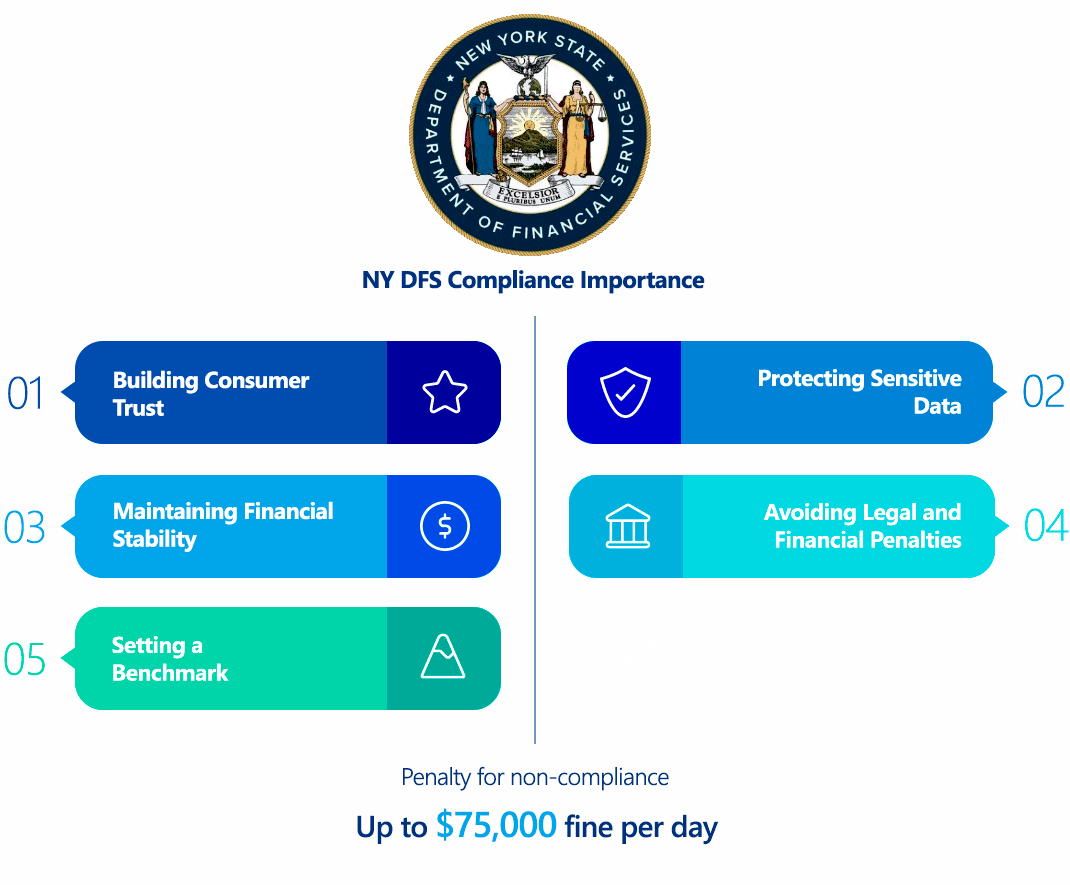
Compliance with the NYDFS Cybersecurity Regulation is paramount for several reasons:
- Protecting Sensitive Data: The primary objective is to safeguard sensitive financial and personal data of consumers, preventing data breaches and their severe consequences.
- Maintaining Financial Stability: Cyberattacks on financial institutions can have systemic impacts, disrupting markets and eroding public trust. The regulation strengthens the cybersecurity posture of these institutions, contributing to overall financial stability.
- Avoiding Legal and Financial Penalties: Non-compliance can lead to significant financial penalties, legal actions, and reputational damage.
- Building Consumer Trust: Adherence to robust cybersecurity standards demonstrates a commitment to protecting customer information, fostering greater confidence in financial services.
- Setting a Benchmark: The NYDFS regulation has served as a model for other regulatory bodies globally, raising the bar for cybersecurity excellence in the financial sector.
Who Needs to Comply with New York DFS Cybersecurity Regulation?
The NYDFS Cybersecurity Regulation applies to "Covered Entities," which are defined as any person operating under a license, registration, charter, certificate, permit, accreditation, or similar authorization under New York's Banking Law, Insurance Law, or Financial Services Law. This broadly includes:
- Banks (state-chartered and private)
- Foreign banks licensed to operate in New York
- Insurance companies and brokers
- Mortgage companies
- Licensed lenders
- Trust companies
- Service contract providers
- Investment advisors and financial planners
- Health insurers
Exemptions: Limited exemptions exist for smaller organizations meeting specific criteria, such as:
- Fewer than 10 employees (including independent contractors).
- Less than $5 million in gross annual revenue from New York operations over the past three years.
- Less than $10 million in year-end total assets.
Even if an entity qualifies for a limited exemption, certain core requirements like maintaining a basic cybersecurity program, overseeing third-party vendors, managing access controls, and submitting annual filings and incident reports generally still apply.
New York DFS Cybersecurity Regulation vs GDPR Comparison
While both the NYDFS Cybersecurity Regulation and the GDPR (General Data Protection Regulation) aim to protect data, they differ significantly in scope, focus, and enforcement.
| Aspect | NYDFS Cybersecurity Regulation (23 NYCRR Part 500) | GDPR (General Data Protection Regulation) |
|---|---|---|
| Scope | Applies to financial services institutions regulated by NYDFS operating in New York. Focuses on the security of information systems and nonpublic financial information. | Applies to any organization, anywhere in the world, that processes the personal data of EU residents. Broader focus on personal data privacy rights across all sectors. |
| Focus | Primarily a cybersecurity regulation, mandating specific technical and administrative controls to protect IT systems and data. | A data privacy regulation, focusing on the rights of data subjects regarding their personal data, including consent, access, rectification, and erasure. |
| Data Definition | "Nonpublic Information" - private financial information and information technology systems. | "Personal Data" - any information relating to an identified or identifiable natural person. Broader and more encompassing. |
| Technical Detail | Provides more prescriptive technical requirements (e.g., specific requirements for MFA, encryption, penetration testing frequency). | Sets out principles for data protection (e.g., "data protection by design and by default") but is less prescriptive on technical implementation, allowing flexibility. |
| Breach Notification | 72-hour notification to NYDFS Superintendent for significant events; 24-hour for extortion payments. | 72-hour notification to the supervisory authority for personal data breaches, where feasible, unless the breach is unlikely to result in a risk to individuals' rights and freedoms. |
| Enforcement/Penalties | Daily fines ($2,500-$75,000 per day for non-compliance, with recent settlements in the millions). Enforcement by NYDFS. | Hefty fines (up to €20 million or 4% of annual global turnover, whichever is higher). Enforced by Data Protection Authorities in EU member states. |
| CISO Requirement | Mandates the designation of a CISO. | Does not explicitly mandate a CISO but requires organizations to designate a Data Protection Officer (DPO) in certain cases. |
In essence, while NYDFS focuses on strengthening the cybersecurity defenses of a specific, high-risk sector, GDPR is a broader privacy regulation that emphasizes individual data rights and the responsible handling of personal data across all industries. However, there is significant overlap in best practices, as robust cybersecurity is a prerequisite for data privacy.
How to Ensure New York DFS Cybersecurity Regulation Compliance?
Ensuring NYDFS compliance requires a systematic and ongoing effort. Key technical and administrative steps include:
- Conduct Comprehensive Risk Assessments:
- Technical: Utilize frameworks like NIST Cybersecurity Framework or ISO 27001. Identify critical assets (databases, applications, network devices), conduct vulnerability scanning (e.g., Nessus, OpenVAS), and analyze network architecture for weaknesses. Perform threat modeling to understand potential attack vectors.
- Administrative: Document risk assessment methodologies, criteria for evaluating identified risks, and processes for risk mitigation or acceptance.
- Develop and Implement a Robust Cybersecurity Program and Policies:
- Technical: Implement security controls such as firewalls, intrusion detection/prevention systems (IDS/IPS), endpoint detection and response (EDR) solutions, and security information and event management (SIEM) systems for centralized logging and analysis of security events. Define and enforce strong password policies (e.g., minimum length, complexity, regular changes).
- Administrative: Formalize written policies covering all aspects of 23 NYCRR Part 500, including data governance, access control, incident response, third-party risk management, and data retention. Obtain senior management or board approval for these policies.
- Implement Strong Access Controls:
- Technical: Deploy MFA for all access to information systems (especially for Class A companies). Implement Least Privilege principles through granular access permissions and regular review of user roles and entitlements. Utilize identity and access management (IAM) solutions.
- Administrative: Establish clear procedures for user onboarding, offboarding, and role changes to ensure timely access adjustments.
- Encrypt Nonpublic Information:
- Technical: Implement strong encryption (e.g., AES-256) for nonpublic information at rest (e.g., disk encryption, database encryption, cloud storage encryption) and in transit (e.g., TLS/SSL for network communications, VPNs). Establish robust key management standards (e.g., FIPS 140-2 compliant hardware security modules - HSMs).
- Administrative: Develop policies for data classification to identify all nonpublic information requiring encryption.
- Conduct Regular Penetration Testing and Vulnerability Assessments:
- Technical: Engage independent third parties for annual penetration tests. Automate vulnerability scanning tools for continuous monitoring. Prioritize remediation based on risk score (e.g., CVSS).
- Administrative: Maintain detailed documentation of all testing activities, identified vulnerabilities, and remediation efforts.
- Develop and Test an Incident Response Plan (IRP):
- Technical: Implement tools for incident detection (e.g., SIEM, EDR), forensic analysis, and data recovery.
- Administrative: Create a detailed IRP with clear roles, responsibilities, communication protocols (internal and external, including NYDFS notification), containment strategies, eradication steps, recovery procedures, and post-incident review. Conduct tabletop exercises and simulations regularly to test the plan's effectiveness.
- Manage Third-Party Risk:
- Technical: Conduct security assessments of third-party vendors (e.g., security questionnaires, on-site audits). Implement secure data transfer protocols.
- Administrative: Establish a written third-party service provider security policy. Include contractual obligations for cybersecurity safeguards, right-to-audit clauses, and clear data protection requirements.
- Provide Cybersecurity Training and Awareness:
- Technical: Train personnel on recognizing and reporting phishing attempts, social engineering tactics (including AI-enabled attacks), and other cybersecurity threats.
- Administrative: Develop and implement a regular cybersecurity awareness training program for all employees.
- Maintain Comprehensive Documentation and Annual Certification:
- Administrative: Document all cybersecurity policies, procedures, risk assessments, test results, incident reports, and training records. Submit an annual Certification of Compliance to the NYDFS by April 15th, or an Acknowledgment of Noncompliance with a remediation timeline.
- Monetary Penalties: Under New York Banking Law, penalties for non-compliance can be substantial. Fines can start at $2,500 per day for each day of non-compliance. If a "pattern" of non-compliance is determined, the fine can increase to $15,000 per day. For "knowing and willful" violations, the daily fine can jump to $75,000. Recent enforcement actions have resulted in multi-million dollar penalties.
- Enforcement Actions: The NYDFS actively investigates and pursues violations, leading to public enforcement actions and settlements.
- Reputational Damage: Non-compliance and subsequent data breaches can severely damage an entity's reputation, eroding customer trust and leading to a loss of business.
- Legal Liability: Entities may face civil lawsuits from affected individuals or other parties for damages resulting from data breaches or cybersecurity failures.
- Operational Disruptions: Non-compliance often indicates weaknesses in cybersecurity, making an entity more susceptible to cyberattacks that can disrupt operations, lead to downtime, and incur significant recovery costs.
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
Consequences of Non-Compliance with New York DFS Cybersecurity Regulation
Non-compliance with the NYDFS Cybersecurity Regulation carries significant consequences, designed to deter negligence and encourage robust security practices:
How ImmuniWeb Helps Comply with New York DFS Cybersecurity Regulation?
ImmuniWeb offers a suite of AI-powered and human-verified solutions that can significantly assist organizations in achieving and maintaining compliance with the NYDFS Cybersecurity Regulation:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By leveraging a blend of advanced AI and human intelligence, ImmuniWeb provides a holistic approach to cybersecurity, enabling financial institutions to not only meet the stringent technical requirements of the NYDFS Cybersecurity Regulation but also to proactively enhance their overall security posture in the face of evolving cyber threats.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
