NIST Cybersecurity Framework (CSF) 2.0 Compliance
The NIST Cybersecurity Framework (CSF) 2.0 provides a flexible, risk-based approach to managing cybersecurity
risks through core functions—Govern, Identify, Protect, Detect, Respond, and Recover—helping
organizations align security practices with business objectives and threat landscapes.

The digital landscape is constantly evolving, bringing with it new opportunities and increasingly sophisticated cyber threats.
To help organizations navigate this complex environment, the National Institute of Standards and Technology (NIST) released version 2.0 of its Cybersecurity Framework (CSF) in February 2024.
Building upon the success of its predecessor, CSF 2.0 offers a more comprehensive, flexible, and accessible approach to managing and reducing cybersecurity risks for organizations of all sizes and sectors, moving beyond its initial focus on critical infrastructure.
Overview of NIST Cybersecurity Framework (CSF) 2.0
The NIST CSF 2.0 is a voluntary, outcome-based framework that provides a common language and systematic approach for organizations to understand, assess, prioritize, and communicate their cybersecurity risks. It is designed to be highly adaptable and can be tailored to an organization's specific needs, risk tolerance, and existing cybersecurity practices.
The core of the CSF 2.0 is structured around six "Functions," which represent the high-level cybersecurity outcomes an organization aims to achieve. These functions are:
- Govern (GV) - New in CSF 2.0: This foundational function emphasizes the importance of establishing and maintaining an organization's cybersecurity risk management strategy, expectations, and policy. It ensures that cybersecurity activities are aligned with overall organizational objectives, legal and regulatory requirements, and risk appetite. It covers areas like organizational context, risk management strategy, roles and responsibilities, policy development, oversight, and cybersecurity supply chain risk management.
- Identify (ID): Developing an organizational understanding to manage cybersecurity risk to systems, people, assets, data, and capabilities. This includes asset management, business environment understanding, risk assessment, and supply chain risk management.
- Protect (PR): Implementing safeguards to limit or contain the impact of a potential cybersecurity event. This function covers identity management and access control, awareness and training, data security, information protection processes and procedures, and protective technology.
- Detect (DE): Identifying the occurrence of a cybersecurity event. This involves continuous monitoring for anomalies and events, and maintaining effective detection processes.
- Respond (RS): Taking action regarding a detected cybersecurity incident. This includes response planning, analysis, mitigation, and improvements based on lessons learned.
- Recover (RC): Restoring capabilities and services impaired due to a cybersecurity incident. This involves recovery planning, improvements, and effective communication with stakeholders during the recovery process.
Each Function is further broken down into Categories and Subcategories (also referred to as "cybersecurity outcomes"). For each Subcategory, NIST provides Implementation Examples and Informative References that map to other widely used cybersecurity standards, guidelines, and practices (e.g., ISO 27001, CIS Controls, NIST SP 800-53).
A key addition in CSF 2.0 is the emphasis on Organizational Profiles and Community Profiles. Organizational Profiles allow businesses to describe their current and target cybersecurity posture using the CSF Core, helping them prioritize efforts. Community Profiles are templates developed by specific sectors or communities to address shared cybersecurity interests and goals.

Key Aspects of NIST Cybersecurity Framework (CSF) 2.0 Compliance?
While "compliance" with NIST CSF 2.0 is not a strict legal mandate for most organizations (see "Who Needs to Comply?"), organizations "align" or "adhere" to the framework to improve their cybersecurity posture. Key technical aspects involved in this alignment include:
- Governance Integration (GV Function - New):
- Technical Details: Integrating cybersecurity risk management into the organization's overall governance and enterprise risk management (ERM). This requires establishing clear lines of authority, responsibility, and communication for cybersecurity, including for the supply chain.
- Technical Implementation:
- GRC Platforms: Utilize Governance, Risk, and Compliance (GRC) software to centralize risk management activities, map cybersecurity risks to business objectives, and track compliance with internal policies and external regulations.
- Defined Roles & Responsibilities: Clearly document cybersecurity roles (e.g., CISO, Security Architect, Security Operations Analyst) and their technical responsibilities, ensuring accountability for specific technical controls (e.g., firewall management, vulnerability patching).
- Cybersecurity Supply Chain Risk Management (C-SCRM): Implement tools and processes for continuous monitoring and assessment of third-party vendor security postures (e.g., vendor risk assessment platforms, security ratings services) as per GV.SC (Cybersecurity Supply Chain Risk Management).
- Comprehensive Asset Identification and Risk Assessment (ID Function):
- Technical Details: A deep understanding of all organizational assets (hardware, software, data, personnel, facilities) and their criticality to business operations. This includes identifying vulnerabilities, threats, and assessing inherent and residual risks.
- Technical Implementation:
- Automated Asset Discovery: Deploy tools for continuous discovery and inventory of all IT assets across on-premise, cloud, and hybrid environments. This includes network devices, servers, workstations, virtual assets, and applications (ID.AM Asset Management).
- Vulnerability Management Program: Implement continuous vulnerability scanning for networks, operating systems, and applications. Integrate Penetration Testing (internal, external, web, mobile, API) to identify exploitable weaknesses. These activities directly support ID.RA Vulnerability Identification and ID.RA Risk Assessment.
- Threat Intelligence Platforms: Integrate external threat intelligence feeds to understand the evolving threat landscape relevant to your assets and industry (ID.RA External Threats).
- Robust Protective Measures (PR Function):
- Technical Details: Implementing technical safeguards to prevent or limit the impact of cybersecurity incidents.
- Technical Implementation (Examples):
- Access Management: Implement strong Identity and Access Management (IAM) systems. Enforce Multi-Factor Authentication (MFA) for all critical systems and remote access. Implement Privileged Access Management (PA) to control and monitor administrative accounts (PR.AA Identity Management, Authentication, and Access Control).
- Data Security: Implement encryption for data at rest (e.g., disk encryption, database encryption) and in transit (e.g., TLS 1.3 for web traffic). Deploy Data Loss Prevention (DLP) solutions to prevent unauthorized exfiltration of sensitive information (PR.DS Data Security).
- Secure Configurations & Patch Management: Automate patch management processes. Use configuration management tools to enforce and maintain secure baselines for all system components (PR.IP Information Protection Processes and Procedures, PR.MA Maintenance).
- Protective Technology: Deploy and configure Next-Generation Firewalls (NGFWs), Intrusion Prevention Systems (IPS), Web Application Firewalls (WAFs), and Endpoint Detection and Response (EDR)/Extended Detection and Response (XDR) solutions (PR.PT Protective Technology). Implement network segmentation.
- Effective Detection Capabilities (DE Function):
- Technical Details: Establishing processes and technologies to identify cybersecurity events in a timely manner.
- Technical Implementation:
- Security Information and Event Management (SIEM): Deploy a SIEM system to collect, aggregate, and correlate security logs from across the entire IT environment. Configure rules and alerts for real-time anomaly detection and threat identification (DE.CM Security Continuous Monitoring, DE.AE Anomalies and Events).
- Intrusion Detection Systems (IDS): Implement IDS to monitor network traffic and system activity for suspicious patterns.
- User and Entity Behavior Analytics (UEBA): Use UEBA tools to detect unusual user or system behavior that might indicate a compromise.
- Swift Incident Response and Recovery (RS & RC Functions):
- Technical Details: Developing and testing plans for responding to and recovering from cybersecurity incidents.
- Technical Implementation:
- Incident Response Playbooks: Develop detailed, technically oriented playbooks for various incident types (e.g., ransomware, data breach, denial-of-service).
- Forensic Tools: Ensure availability of digital forensic tools and expertise for post-incident analysis (RS.AN Analysis).
- Backup and Recovery Systems: Implement robust, tested backup and disaster recovery solutions to ensure critical data and systems can be restored quickly and reliably (RC.RP Recovery Planning). Regularly test recovery procedures.
- Breach and Attack Simulation (BAS): Utilize BAS tools to proactively test the effectiveness of detection and response controls against simulated attacks, identifying gaps before a real incident occurs.
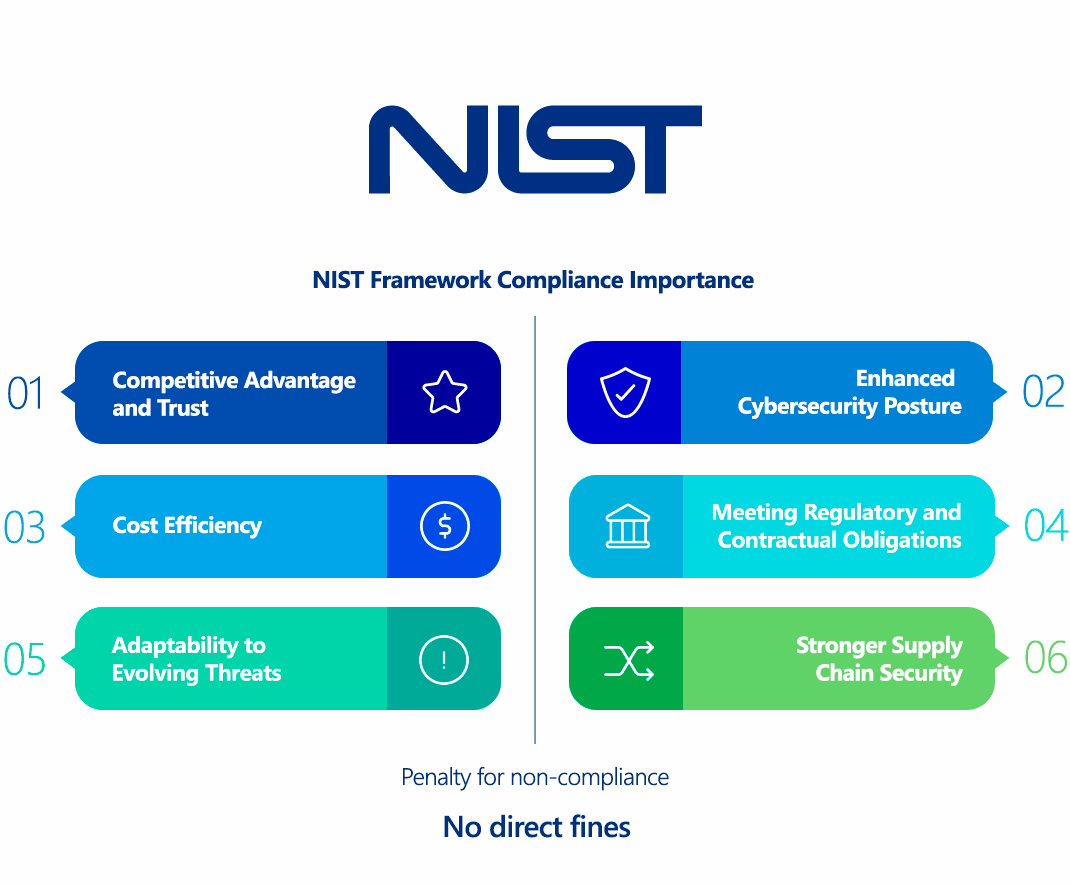
Why Is NIST Cybersecurity Framework (CSF) 2.0 Compliance Important?
Adopting and aligning with NIST CSF 2.0 is crucial for several compelling reasons, extending beyond a mere technical exercise:
- Holistic Risk Management: CSF 2.0 provides a comprehensive, risk-based approach that helps organizations understand, prioritize, and manage cybersecurity risks in alignment with business objectives. This moves cybersecurity from a purely technical concern to a strategic business imperative. The new Govern function specifically elevates this aspect.
- Enhanced Cybersecurity Posture: By systematically implementing the framework's outcomes, organizations build more resilient and effective cybersecurity programs, making them better equipped to prevent, detect, respond to, and recover from cyberattacks. This directly reduces the likelihood and impact of data breaches and other security incidents.
- Improved Communication and Collaboration: The CSF provides a common language for cybersecurity, facilitating better communication between technical teams, business leaders, and external stakeholders (e.g., suppliers, regulators, customers). This shared understanding fosters a stronger security culture across the organization.
- Adaptability to Evolving Threats: CSF 2.0 is designed to be flexible and adaptable, recognizing that the threat landscape is constantly changing. It encourages continuous improvement and allows organizations to tailor its outcomes to address new technologies (e.g., AI, quantum computing) and emerging threats.
- Meeting Regulatory and Contractual Obligations (Indirectly): While voluntary, many regulations (e.g., HIPAA, GDPR, various state privacy laws) and contractual agreements (especially with federal agencies or large enterprises) either explicitly reference NIST CSF or require similar security controls. Adhering to CSF 2.0 provides a strong foundation for meeting these diverse compliance requirements, streamlining audit processes.
- Stronger Supply Chain Security: With the elevated focus on Cybersecurity Supply Chain Risk Management (C-SCRM) in CSF 2.0, organizations can better assess and manage the cybersecurity risks introduced by their third-party vendors and partners. This is crucial given the increasing prevalence of supply chain attacks.
- Competitive Advantage and Trust: Demonstrating adherence to a widely recognized and respected framework like NIST CSF 2.0 builds trust with customers, partners, and investors. It signals a commitment to robust cybersecurity, which can be a significant differentiator in the market.
- Cost Efficiency: Proactive risk management and prevention, guided by the CSF, can lead to significant cost savings by reducing the likelihood and impact of costly cyber incidents, regulatory fines, and reputational damage.
- Support for All Organization Types: CSF 2.0 explicitly broadens its applicability beyond critical infrastructure, making it a valuable tool for small businesses, non-profits, and organizations across all industries.
Who Needs to Comply with NIST Cybersecurity Framework (CSF) 2.0?
It's important to clarify that NIST CSF 2.0 is a voluntary framework of best practices, not a legal mandate for most organizations. However, its widespread adoption and growing influence mean that many organizations effectively need to align with it due to various factors:
- U.S. Federal Agencies: While the original CSF was primarily for critical infrastructure, U.S. federal agencies are increasingly directed to adopt the CSF for managing their cybersecurity risks, making it a de facto standard within the government.
- Organizations Doing Business with the U.S. Government: Companies that contract with or are part of the supply chain for U.S. federal agencies (especially those handling Controlled Unclassified Information - CUI, which often falls under NIST SP 800-171 and CMMC) frequently find that alignment with NIST CSF is a prerequisite or a strong recommendation to demonstrate adequate cybersecurity posture.
- Critical Infrastructure Organizations: Though CSF 2.0 expands beyond, it remains highly relevant for organizations operating in critical infrastructure sectors (e.g., energy, water, communications, healthcare, financial services) as it directly addresses their unique challenges and regulatory landscapes.
- Organizations Seeking to Improve Cybersecurity Posture: Any organization, regardless of size or industry, that wants a structured, systematic, and recognized approach to managing cybersecurity risks can benefit from adopting the CSF. This includes small and medium-sized businesses (SMBs) who may lack extensive cybersecurity resources but still face significant threats.
- Organizations Addressing Specific Regulations: While not a compliance standard itself, the NIST CSF provides a strong foundation for meeting the security requirements of various regulations and laws. Organizations subject to regulations like HIPAA, GDPR, state data privacy laws (e.g., CCPA), or industry-specific standards (e.g., PCI DSS) can leverage the CSF to build out their security programs and demonstrate compliance.
- Organizations Concerned about Reputation and Trust: In today's threat landscape, demonstrating a robust cybersecurity posture is crucial for maintaining customer trust and stakeholder confidence. Adhering to a respected framework like NIST CSF can be a significant differentiator.
- Organizations Managing Significant Cybersecurity Risks: Any organization that stores, processes, or transmits sensitive data (e.g., PII, intellectual property, financial data) or relies heavily on IT systems for its operations should consider implementing the CSF to manage its inherent cybersecurity risks effectively.
In essence, while direct "compliance" is primarily for federal entities, the NIST CSF 2.0 serves as a universally applicable blueprint for effective cybersecurity risk management, making it highly relevant for virtually any organization serious about protecting its digital assets.
NIST Cybersecurity Framework (CSF) 2.0 vs GDPR Comparison
NIST CSF 2.0 and GDPR are both vital frameworks in the realm of information security and data protection, but they serve different primary purposes and have distinct scopes. NIST CSF 2.0 is a voluntary risk management framework for cybersecurity, while GDPR is a legally binding regulation for data privacy. However, they are highly complementary.
| Aspect | NIST CSF 2.0 (Cybersecurity Framework) | GDPR (General Data Protection Regulation) |
|---|---|---|
| Type of Framework/Law | Voluntary Framework of best practices for cybersecurity risk management. | Legally Binding Regulation for data privacy in the EU. |
| Primary Focus | Cybersecurity Risk Management: Protecting the confidentiality, integrity, and availability (CIA) of all types of information systems and data against cyber threats. | Data Privacy and Rights: Protecting the personal data and privacy rights of EU data subjects. |
| Scope of Data | Applies to all information and systems within an organization's scope. | Applies specifically to personal data (information about an identifiable individual). |
| Legal Status | Best practice guidelines; adoption is voluntary unless specified by contract or agency policy. | Law with extraterritorial reach; compliance is mandatory if processing EU personal data. |
| Risk Management | Comprehensive risk-based approach across all cybersecurity domains (Govern, Identify, Protect, Detect, Respond, Recover). | Requires risk assessment (DPIA) for high-risk processing of personal data, and appropriate "technical and organizational measures" for security. |
| Technical Controls | Provides outcomes and implementation examples across 6 functions, covering a broad range of technical and organizational controls. Less prescriptive on exact implementation, more on outcomes. | Requires "appropriate technical and organizational measures" (Art. 32); less prescriptive on how to implement specific controls, focusing on the result (data protection). |
| Data Subject Rights | No explicit individual rights (focused on organizational cybersecurity posture). | Grants extensive individual rights (e.g., access, erasure, portability, objection). |
| Accountability | Emphasizes governance and accountability for cybersecurity risk management (new Govern function). | Emphasizes accountability (Data Protection Officer, Records of Processing Activities). |
| Breach Notification | Requires a Respond function for incident management and communication. | Mandatory 72-hour notification for personal data breaches to supervisory authorities and individuals (if high risk). |
| Purpose | To help organizations understand, manage, and reduce cybersecurity risks. | To standardize data protection laws across the EU and protect data subjects' rights and privacy. |
| Enforcement | No direct enforcement body for general adoption. Compliance is often a contractual requirement. | Data Protection Authorities (DPAs) in each EU member state. |
| Penalties | No direct fines for non-compliance with the framework itself. Consequences are indirect (e.g., loss of contracts, increased breach risk). | Significant fines (up to €20M or 4% of global annual turnover). |
| Relationship | Highly Complementary: NIST CSF 2.0 provides a strong, flexible framework for establishing and maintaining the robust cybersecurity posture necessary to meet many of GDPR's "technical and organizational measures" for security (Article 32). An organization adhering to CSF 2.0 will have a solid foundation for GDPR compliance, particularly concerning data protection through security. However, GDPR's scope is broader, encompassing privacy principles, data subject rights, and legal bases for processing, which extend beyond CSF's primary cybersecurity focus. |
In essence, NIST CSF 2.0 helps you build the secure house, while GDPR dictates how you manage the personal information inside that house and the rights of the people whose information it is. An organization handling EU personal data will likely leverage NIST CSF 2.0's guidance to implement the technical security controls required by GDPR, but will also need to address GDPR's specific privacy principles and individual rights.
How to Ensure NIST Cybersecurity Framework (CSF) 2.0 Compliance?
Ensuring alignment with NIST CSF 2.0 is a strategic and ongoing journey that involves integrating cybersecurity into the organization's fabric. Here's how to approach it with technical details:
- Understand Your Organizational Context and Scope (GV.OC):
- Technical Action: Identify all information systems, data types, business processes, and external dependencies. Understand the legal, regulatory, and contractual requirements relevant to your data and operations.
- Tools: Utilize IT asset management (ITAM) systems, data classification tools, and network discovery tools to create a comprehensive inventory of your digital and physical assets. Map data flows to understand where sensitive information resides and how it's processed.
- Establish Robust Governance (GV Function):
- Technical Action: Define clear cybersecurity roles, responsibilities, and authorities across the organization (e.g., CISO, system owners, data custodians). Implement a cybersecurity risk management strategy that aligns with the organization's overall enterprise risk management framework.
- Tools: Use GRC platforms to document policies, track responsibilities, manage risk registers, and monitor overall cybersecurity program performance. Implement vendor risk management (VRM) solutions to assess and monitor the cybersecurity posture of your supply chain partners (GV.SC).
- Perform Comprehensive Asset Identification and Risk Assessment (ID Function):
- Technical Action: Continuously identify and classify all assets (hardware, software, data, personnel, facilities). Conduct thorough risk assessments to identify vulnerabilities, threats, and potential impacts.
- Tools:
- Automated Asset Discovery & Inventory: Implement tools for continuous discovery of all network-connected devices, applications, and cloud resources.
- Vulnerability Management: Deploy continuous vulnerability scanners (for networks, systems, and applications). Integrate penetration testing (web, mobile, API, network, cloud) as part of your regular security assessment program.
- Threat Intelligence Platforms: Subscribe to and integrate threat intelligence feeds to understand the latest threats and vulnerabilities relevant to your industry and assets.
- Risk Management Tools: Use dedicated risk management software to document risks, assess their likelihood and impact, and track mitigation efforts.
- Implement and Maintain Protective Safeguards (PR Function):
- Technical Action: Deploy and configure technical controls to protect your systems and data.
- Tools:
- Identity & Access Management (IAM) & Multi-Factor Authentication (MFA): Implement robust IAM systems. Mandate MFA for all critical systems and remote access. Deploy Privileged Access Management (PAM) solutions for administrative accounts (PR.AA).
- Data Security: Implement encryption-at-rest (e.g., full disk encryption, database encryption) and encryption-in-transit (e.g., TLS 1.3 for all web traffic, secure VPNs). Deploy Data Loss Prevention (DLP) solutions (PR.DS).
- Configuration Management & Patch Management: Automate patch management across all systems. Use configuration management tools (e.g., Puppet, Ansible) to enforce secure baseline configurations (PR.IP, PR.MA).
- Network & Endpoint Security: Deploy Next-Generation Firewalls (NGFWs), Intrusion Prevention Systems (IPS), Web Application Firewalls (WAFs). Implement network segmentation. Install Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) solutions (PR.PT).
- Secure Software Development Lifecycle (SSDLC): Integrate security into development processes using Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) tools for custom applications (PR.IP).
- Establish Robust Detection Capabilities (DE Function):
- Technical Action: Implement systems to detect cybersecurity events and anomalies in real-time.
- Tools:
- Security Information and Event Management (SIEM): Deploy a SIEM system to centralize log collection, correlate events, and generate alerts for suspicious activities from all relevant sources (e.g., firewalls, servers, applications, cloud logs).
- User and Entity Behavior Analytics (UEBA): Use UEBA tools to detect anomalous user or system behavior.
- Continuous Monitoring: Implement tools for continuous monitoring of network traffic, system configurations, and security events (DE.CM, DE.AE).
- Develop and Practice Incident Response and Recovery (RS & RC Functions):
- Technical Action: Create and regularly test incident response plans (IRP) and disaster recovery plans (DRP).
- Tools:
- Incident Response Platforms (IRP): Use platforms to manage incident workflows, communication, and evidence collection.
- Forensic Tools: Ensure availability of tools for digital forensics and malware analysis.
- Backup & Disaster Recovery Solutions: Implement robust, isolated, and regularly tested backup and disaster recovery systems.
- Breach and Attack Simulation (BAS): Periodically use BAS tools to simulate real-world attacks and test the effectiveness of your detection, response, and recovery controls in a safe environment. This identifies weaknesses in your IRP and DRP before a real incident (RS.RP, RC.RP).
- Maintain Documentation and Continuous Improvement:
- Technical Action: Document your current state ("Current Profile") and your desired future state ("Target Profile") against the CSF 2.0 Subcategories. Identify gaps and develop an action plan. Regularly review and update your CSF implementation based on new threats, technologies, and organizational changes.
- Tools: GRC platforms are excellent for managing this documentation, tracking progress, and facilitating audits.
Consequences of Non-Compliance with NIST Cybersecurity Framework (CSF) 2.0
As NIST CSF 2.0 is a voluntary framework for most organizations, there are no direct fines or legal penalties specifically for "non-compliance" with the CSF itself. However, the indirect consequences of not aligning with a robust framework like CSF can be severe and far-reaching:
- Increased Cybersecurity Risk: The most direct consequence is a significantly higher risk of successful cyberattacks, data breaches, and other security incidents. Without a structured approach to risk management, organizations are more vulnerable to known and emerging threats.
- Financial Losses from Breaches: A cybersecurity incident resulting from a weak security posture (often indicated by a lack of adherence to frameworks like CSF) can lead to:
- Costly forensic investigations.
- Ransom payments (in the case of ransomware).
- Data recovery and system restoration costs.
- Legal fees and potential settlements from affected parties.
- Credit monitoring services for impacted individuals.
- Significant operational disruption and lost revenue.
- Regulatory Fines and Legal Consequences (Indirect): While the CSF itself doesn't impose fines, many mandatory regulations (e.g., GDPR, HIPAA, state data breach notification laws, financial regulations) require organizations to implement "reasonable" or "appropriate" security measures. If a breach occurs and it's found that the organization did not implement such measures (which often align with CSF guidance), then significant fines and legal action can follow from these other regulations.
- Loss of Business Opportunities: Many government contracts, particularly in the U.S., and large enterprise partnerships increasingly require vendors and suppliers to demonstrate a strong cybersecurity posture, often by aligning with NIST standards (like CSF or SP 800-171). Non-alignment can lead to automatic disqualification from lucrative opportunities.
- Reputational Damage and Loss of Trust: A data breach or a public display of weak cybersecurity practices can severely damage an organization's reputation. This erodes customer trust, stakeholder confidence, and can lead to a significant loss of market share and brand value, which can be very difficult and expensive to rebuild.
- Higher Insurance Premiums: Cyber insurance providers evaluate an organization's cybersecurity maturity when determining premiums and coverage. A lack of adherence to recognized frameworks like CSF can lead to higher premiums or even denial of essential cyber insurance coverage.
- Difficulty Attracting Talent: In today's cybersecurity-conscious world, top talent may be hesitant to join organizations perceived as having weak security practices, further hindering efforts to strengthen defenses.
In essence, while you won't get a "NIST CSF fine," failing to implement a robust cybersecurity program guided by a framework like CSF 2.0 is a self-inflicted wound that significantly increases business risk and can have devastating consequences in the event of a cyber incident.
How ImmuniWeb Helps Comply with NIST Cybersecurity Framework (CSF) 2.0?
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides a unique and powerful set of capabilities that directly support organizations in achieving and demonstrating alignment with numerous technical outcomes across multiple functions of the NIST Cybersecurity Framework (CSF) 2.0.
Here's how ImmuniWeb specifically assists with CSF 2.0 alignment:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By integrating ImmuniWeb's platform, organizations can gain robust, continuous technical assurance across their attack surface and applications, which directly translates into stronger alignment with the outcomes of the NIST CSF 2.0, ultimately leading to a more mature and resilient cybersecurity program.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
