NIST SP 800-171 (Rev.3) Compliance
NIST SP 800-171 (Rev. 3) establishes security requirements for protecting Controlled Unclassified Information (CUI)
in non-federal systems, mandating safeguards across access control, encryption, incident response,
and other critical areas to ensure compliance with federal cybersecurity standards.

In May 2024, the National Institute of Standards and Technology (NIST) released Special Publication 800-171 Revision 3 (Rev. 3), "Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations."
This update signifies a crucial evolution in the U.S. government's efforts to safeguard sensitive but unclassified information (CUI) when it resides in the systems of non-federal entities, particularly defense contractors and their supply chain. Rev. 3 is a direct response to the increasingly sophisticated cyber threats targeting the Defense Industrial Base (DIB) and aims to provide clearer, more effective, and streamlined security requirements.
Overview of NIST SP 800-171 (Rev. 3)
NIST SP 800-171 Rev. 3 provides a comprehensive set of security requirements designed to protect the confidentiality of Controlled Unclassified Information (CUI). CUI is government-created or -owned information that requires safeguarding or dissemination controls in accordance with law, regulation, or government-wide policy, but is not classified. Examples include technical drawings, research data, legal documents, and personal identifiable information (PII) handled for federal contracts.
The requirements in SP 800-171 Rev. 3 are logically organized into 17 security requirement families, a notable increase from the 14 families in Rev. 2. However, the total number of individual security requirements has been reduced from 110 to 97 due to streamlining, consolidation, and removal of redundancies. The framework focuses on a CUI enclave or the broader non-federal system where CUI is stored, processed, or transmitted.
Key changes and enhancements in Revision 3 include:
- Closer Alignment with NIST SP 800-53 Revision 5: This is a major overhaul. Rev. 3 directly aligns its security requirements with the Federal Information Processing Standard (FIPS) 200 and the moderate control baseline from NIST SP 800-53 Rev. 5, the robust catalog of security and privacy controls for federal information systems. This aims to provide clearer, more specific, and less ambiguous guidelines.
- New Security Requirement Families: Three new families have been added to enhance consistency with the 800-53B moderate control baseline:
- Planning (PL): Emphasizes system security plans, rules of behavior, and overall security planning.
- System and Services Acquisition (SA): Focuses on secure acquisition processes for systems, components, and services.
- Supply Chain Risk Management (SR): Addresses risks introduced through the supply chain, a critical area given the rise of supply chain attacks.
- Organization-Defined Parameters (ODPs): Rev. 3 introduces 49 ODPs, which allow for greater flexibility. Federal agencies can define specific values or criteria for certain controls, or if not defined, the non-federal organization can assign ODP values based on their risk assessment, leading to more tailored and relevant implementations.
- Elimination of "Basic" vs. "Derived" Requirements: This distinction from Rev. 2 has been removed, simplifying the structure and clarity of the requirements.
- Increased Specificity and Reduced Ambiguity: NIST has refined the language of the requirements to remove vague terms (like "periodically") and provide more concrete expectations, which should improve consistency in implementation and assessment.
- Enhanced Focus on Non-Human Identities: Rev. 3 acknowledges the growing role of applications, scripts, and service accounts in data flow and system interactions, and emphasizes their security as essential to protecting CUI.
- Emphasis on Documentation: Rev. 3 places a greater emphasis on comprehensive documentation of security controls, policies, and procedures, which is crucial for internal reviews and external assessments.
- Alignment with CMMC 2.0: Rev. 3's changes are designed to further align with the Cybersecurity Maturity Model Certification (CMMC) 2.0 Level 2 requirements, simplifying the compliance path for defense contractors.

Key Aspects of NIST SP 800-171 (Rev. 3) Compliance?
Achieving and maintaining compliance with NIST SP 800-171 Rev. 3 is a rigorous process that demands a high level of technical detail and continuous effort. Organizations must implement the 97 security requirements across 17 families.
Here's a breakdown of key technical aspects:
- System Boundary and CUI Scope Definition:
- Technical Details: Precisely identify the Controlled Unclassified Information (CUI) within your environment and define the system boundary that encompasses all components (people, processes, technology) that store, process, or transmit CUI, or provide security for such components. This forms the "CUI Enclave."
- Technical Implementation:
- Data Flow Diagrams (DFDs): Create detailed DFDs illustrating how CUI flows through your systems, where it's stored, and who accesses it.
- Asset Inventory: Maintain a comprehensive, up-to-date inventory of all hardware, software, applications, services, and cloud resources within the CUI enclave. Use automated asset discovery tools for continuous identification.
- Network Segmentation: Implement logical and/or physical network segmentation to isolate the CUI enclave from less secure general IT systems. This reduces the scope of the assessment and the attack surface.
- Access Control (AC):
- Technical Details: Implement controls to restrict access to CUI and systems processing CUI to authorized users, processes, and devices. This now includes specific requirements for non-human identities.
- Technical Implementation:
- Role-Based Access Control (RBAC): Implement granular RBAC to enforce least privilege access.
- Multi-Factor Authentication (MFA): Mandate MFA for all users accessing CUI systems, especially remote access and privileged accounts.
- Privileged Access Management (PAM): Deploy PAM solutions to manage, monitor, and control administrative and service accounts, including Just-In-Time (JIT) access.
- Least Privilege: Configure systems and applications to operate with the minimum necessary privileges to perform their functions.
- Non-Human Identity Management: Implement solutions for managing and securing API keys, service accounts, and other non-human identities, applying principles of least privilege and regular rotation.
- Awareness and Training (AT):
- Technical Details: Ensure all personnel handling CUI receive security awareness training and specialized training for their roles.
- Technical Implementation: Leverage Learning Management Systems (LMS) to deliver and track mandatory cybersecurity training, including phishing awareness simulations.
- Audit and Accountability (AU):
- Technical Details: Create, protect, and retain system audit logs to enable monitoring, analysis, and investigation of security incidents.
- Technical Implementation:
- Centralized Logging: Implement a Security Information and Event Management (SIEM) system to collect, aggregate, and analyze logs from all CUI-related systems, network devices, and applications.
- Log Retention: Configure systems for appropriate log retention periods as per requirements.
- Audit Log Review: Establish processes and tools for regular review of audit logs for suspicious activity.
- Configuration Management (CM):
- Technical Details: Establish and maintain secure baseline configurations for all system components and manage changes.
- Technical Implementation:
- Hardening Baselines: Implement and enforce industry-standard security configuration baselines (e.g., CIS Benchmarks, STIGs) using configuration management tools (e.g., Puppet, Ansible, Microsoft Endpoint Configuration Manager).
- Vulnerability Management: Implement continuous vulnerability scanning (internal and external) and penetration testing to identify misconfigurations and vulnerabilities.
- Change Management Process: Implement a formal change control process for all system configurations, ensuring security reviews are part of every change.
- Incident Response (IR):
- Technical Details: Develop and implement plans for detecting, analyzing, containing, eradicating, and recovering from cybersecurity incidents.
- Technical Implementation:
- Incident Response Plan (IRP): Develop a detailed IRP with clearly defined roles, responsibilities, and technical procedures.
- Forensic Capabilities: Ensure the availability of tools and expertise for digital forensics.
- Incident Response Drills: Conduct regular incident response exercises and simulations (e.g., tabletop exercises, purple teaming with Breach and Attack Simulation (BAS) tools) to test and refine the IRP.
- System and Information Integrity (SI):
- Technical Details: Identify, report, and correct system flaws and protect against malicious code.
- Technical Implementation:
- Patch Management: Implement a robust and automated patch management program to ensure timely application of security updates to all operating systems, applications, and firmware.
- Anti-Malware: Deploy and maintain Endpoint Detection and Response (EDR)/Extended Detection and Response (XDR) solutions across all CUI systems.
- Application Security Testing: Conduct Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) for custom applications that handle CUI. Implement Software Composition Analysis (SCA) to identify vulnerabilities in third-party libraries.
- Web Application Firewalls (WAFs): Deploy and configure WAFs for public-facing web applications handling CUI.
- File Integrity Monitoring (FIM): Implement FIM on critical system files to detect unauthorized modifications.
- Supply Chain Risk Management (SR) - New in Rev. 3:
- Technical Details: Establish a program to manage cybersecurity risks associated with the supply chain.
- Technical Implementation:
- Vendor Risk Assessments: Implement a robust vendor risk management program that includes security assessments of third-party service providers and suppliers who may handle or impact CUI. Use Third-Party Risk Management (TPRM) platforms for continuous monitoring.
- Contractual Flow-downs: Ensure appropriate security requirements are flowed down to subcontractors.
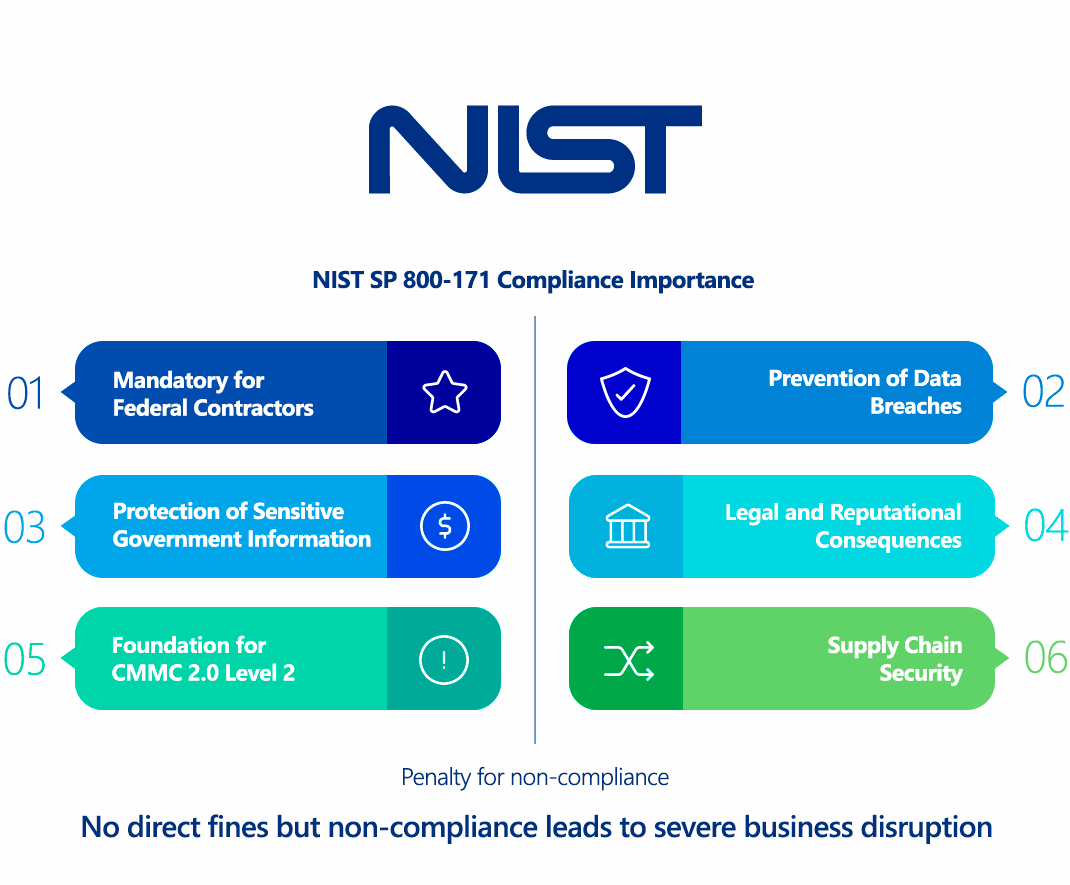
Why Is NIST SP 800-171 (Rev. 3) Compliance Important?
Compliance with NIST SP 800-171 Rev. 3 is not merely a recommendation; for many organizations, it is a mandatory requirement with significant legal, contractual, and financial implications. Its importance stems from several critical factors:
- Mandatory for Federal Contractors (DFARS Clause 252.204-7012): The primary driver for NIST SP 800-171 compliance is the Defense Federal Acquisition Regulation Supplement (DFARS) clause 252.204-7012. This clause mandates that defense contractors and subcontractors who handle Controlled Unclassified Information (CUI) must implement the security requirements outlined in NIST SP 800-171. Non-compliance can lead to loss of existing contracts and disqualification from future bids.
- Foundation for CMMC 2.0 Level 2: NIST SP 800-171 Rev. 3 forms the technical baseline for Cybersecurity Maturity Model Certification (CMMC) 2.0 Level 2. CMMC 2.0 is the Department of Defense's (DoD) new program to enforce cybersecurity standards across the Defense Industrial Base (DIB). Level 2, which requires adherence to NIST SP 800-171, will be a contractual requirement for many DoD contractors and subcontractors handling CUI. Proactive compliance with Rev. 3 is essential for CMMC readiness.
- Protection of Sensitive Government Information: CUI, while unclassified, is critical to national security and government operations. Compromise of CUI can lead to significant national security risks, economic espionage, and intellectual property theft. SP 800-171 directly addresses these risks by mandating specific safeguards.
- Prevention of Data Breaches and Cyber Attacks: Implementing the robust controls within SP 800-171 Rev. 3 significantly enhances an organization's overall cybersecurity posture. This reduces the likelihood and impact of data breaches, ransomware attacks, and other cyber incidents that can compromise CUI.
- Supply Chain Security: Rev. 3 places a greater emphasis on Supply Chain Risk Management (SR). This is crucial because a significant portion of cyberattacks originate from vulnerabilities within the supply chain. Compliance helps secure not just one organization, but the entire ecosystem of government contractors.
- Legal and Reputational Consequences: Beyond contract loss, non-compliance resulting in a CUI breach can lead to:
- Legal liabilities and lawsuits: From federal agencies or other affected parties.
- Whistleblower actions: Under the False Claims Act if contractors falsely claim compliance.
- Reputational damage: Severe harm to an organization's standing in the DIB and broader market, leading to loss of trust and future business.
- Streamlined Audits and Assessments: Having a well-documented and implemented security program aligned with NIST SP 800-171 Rev. 3 simplifies the process of external audits and assessments (e.g., CMMC assessments), reducing associated costs and time.
- Good Cyber Hygiene: Even for organizations not directly mandated, SP 800-171 represents a mature and comprehensive cybersecurity framework. Adopting its principles leads to better overall cyber hygiene, protecting all sensitive data, not just CUI.
In essence, for organizations dealing with the U.S. federal government, particularly the DoD, NIST SP 800-171 Rev. 3 compliance is non-negotiable for business continuity and safeguarding national interests.
Who Needs to Comply with NIST SP 800-171 (Rev. 3)?
NIST SP 800-171 Rev. 3 is specifically designed for and applies to non-federal organizations that process, store, or transmit Controlled Unclassified Information (CUI) on behalf of the U.S. federal government. This primarily includes:
- Department of Defense (DoD) Contractors and Subcontractors: This is the largest and most directly impacted group. If your organization has a contract with the DoD that includes DFARS clause 252.204-7012 (or similar clauses), you are required to implement NIST SP 800-171. This requirement flows down to all subcontractors in the supply chain that handle CUI related to the prime contract.
- Other Federal Agency Contractors and Subcontractors: While the DoD is the most prominent, other federal agencies may also mandate NIST SP 800-171 compliance for their contractors through similar clauses in their contracts. This includes agencies like NASA, GSA, and others.
- Research Institutions and Universities: Many academic institutions conducting research for federal agencies often handle CUI and therefore fall under the scope of NIST SP 800-171.
- Any Organization Handling CUI: Regardless of direct contractual mandates, any organization that becomes aware it is processing, storing, or transmitting CUI should consider implementing NIST SP 800-171 as a best practice to protect that sensitive government information and mitigate associated risks.
Key considerations for determining applicability:
- Do you handle CUI? This is the fundamental question. CUI is any information that the government marks or designates as CUI. It could include technical specifications, project plans, personal data, intellectual property, and more. If you receive data from a federal agency or another contractor, check if it's marked as CUI.
- Is there a DFARS (or similar agency) clause in your contract? This is the direct contractual driver. The presence of DFARS 252.204-7012 or similar clauses explicitly obligates compliance.
- Are you part of the supply chain? Even if you're a lower-tier subcontractor, if you handle CUI related to a federal contract, the requirements flow down to you.
It's crucial for organizations to proactively identify if they fall under this mandate and to understand the specific CUI they handle and its lifecycle within their systems.
NIST SP 800-171 (Rev. 3) vs GDPR Comparison
NIST SP 800-171 Rev. 3 and GDPR are both comprehensive frameworks related to data protection, but they have distinct purposes, scopes, and enforcement mechanisms. NIST SP 800-171 focuses on cybersecurity for specific government data, while GDPR is a broad legal framework for personal data privacy. They are complementary, especially when an organization handles CUI that also contains personal data of EU citizens.
| Aspect | NIST SP 800-171 Rev. 3 (Protecting CUI) | GDPR (General Data Protection Regulation) |
|---|---|---|
| Type of Framework/Law | Mandatory Federal Standard/Contractual Obligation for non-federal entities handling CUI. | Legally Binding Regulation in the EU. |
| Primary Focus | Confidentiality of CUI: Securing U.S. government-controlled unclassified information against cyber threats. | Data Privacy and Rights: Protecting the personal data and privacy rights of EU data subjects. |
| Scope of Data | Specifically targets Controlled Unclassified Information (CUI), regardless of whether it's personal data or not. | Broadly covers Personal Data (any information relating to an identified or identifiable natural person, including CUI if it contains PII). |
| Applicability | Applies to non-federal organizations (e.g., contractors, subcontractors) that process, store, or transmit CUI for U.S. federal agencies. | Applies globally to any entity processing personal data of EU residents, regardless of the entity's location. |
| Purpose | To safeguard sensitive government information crucial to national security and government operations. | To give individuals control over their personal data and harmonize data protection laws across the EU. |
| Legal Basis for Processing | Not directly addressed (focus is on security requirements for CUI). | Requires a specific legal basis (e.g., consent, contract, legitimate interest) for all data processing. |
| Data Subject Rights | No explicit individual rights over the data (as it's government CUI). | Grants extensive individual rights (e.g., right to access, rectification, erasure, portability, objection). |
| Technical Measures | Highly prescriptive with 97 specific security requirements across 17 families, derived from NIST SP 800-53 (e.g., specific requirements for access control, audit, configuration management, incident response). | Requires "appropriate technical and organizational measures" (Art. 32); generally less prescriptive on specific technical solutions, focusing on risk-appropriate security. |
| Breach Notification | Requires reporting CUI incidents to the contracting agency (e.g., DoD) within 72 hours. | Mandatory notification to supervisory authority within 72 hours; individuals notified "without undue delay" if high risk. |
| Third-Party Providers | Explicit and detailed requirements for managing supply chain risk and flowing down requirements to subcontractors. | Requires appropriate contracts and due diligence for processors. |
| Enforcement Authority | U.S. Federal Agencies (e.g., DoD) via contractual clauses (DFARS); CMMC 2.0 assessments. | Data Protection Authorities (DPAs) in each EU member state. |
| Penalties | Loss of contracts, inability to bid on federal work, potential legal action (e.g., False Claims Act), significant financial and reputational damage. | Significant fines (up to €20 million or 4% of global annual turnover, whichever is higher). |
| Relationship | Complementary: If an organization handles CUI that also contains personal data of EU citizens, it must comply with both. NIST SP 800-171 provides a robust set of security controls that can significantly help an organization meet the security obligations of GDPR's Article 32 ("Security of processing"). However, GDPR's scope is much broader, covering all personal data, emphasizing privacy-by-design, data minimization, consent, and a wide array of data subject rights, which are not directly addressed by SP 800-171. |
In essence, NIST SP 800-171 Rev. 3 is about ensuring the security of specific government information, while GDPR is about protecting the privacy rights of individuals concerning their personal data. Organizations handling both CUI and EU personal data will need a comprehensive strategy that addresses the stringent security requirements of SP 800-171 and the broader privacy mandates of GDPR.
How to Ensure NIST SP 800-171 (Rev. 3) Compliance?
Ensuring NIST SP 800-171 Rev. 3 compliance is a continuous and systematic process that requires commitment from leadership, dedicated resources, and a robust cybersecurity program.
- Understand Your CUI and Define the Scope:
- Technical Action: The absolute first step. Work with your federal agency partner to identify all Controlled Unclassified Information (CUI) you receive, generate, or handle.
- Data Mapping: Create detailed data flow diagrams illustrating the lifecycle of CUI within your organization – where it is stored, processed, transmitted, and by whom (users, applications).
- System Boundary Definition: Isolate the systems, applications, and networks that process, store, or transmit CUI into a "CUI Enclave." Implement network segmentation (e.g., VLANs, dedicated firewalls, logical separation) to minimize the scope of your compliance efforts. This reduces the number of systems that need to meet all 97 controls.
- Conduct a Comprehensive Gap Analysis:
- Technical Action: Perform a thorough assessment of your current security controls against each of the 97 requirements in NIST SP 800-171 Rev. 3 (and the accompanying assessment guide, SP 800-171A Rev. 3).
- Tools: Utilize GRC (Governance, Risk, and Compliance) platforms or specialized NIST 800-171 assessment tools to track your compliance status, identify gaps, and manage the remediation process.
- Develop a System Security Plan (SSP) and Plan of Action and Milestones (POA&M):
- Technical Action:
- SSP: Document how your organization meets each of the 97 requirements. This includes detailed descriptions of your security policies, procedures, and technical configurations. This is a living document and must be updated regularly.
- POA&M: For any identified gaps or deficiencies, create a POA&M document outlining the specific actions to be taken, responsible parties, resources required, and target completion dates for remediation.
- Tools: Word processors, spreadsheets, or GRC platforms can be used for SSP and POA&M documentation.
- Technical Action:
- Implement and Remediate Controls (The Technical Work):
- This is where most of the hands-on technical work occurs, aligning with the 17 families:
- Access Control (AC): Implement least privilege, RBAC, MFA, and PAM solutions. Secure non-human identities (API keys, service accounts).
- Audit and Accountability (AU): Deploy a SIEM system for centralized logging and log analysis. Ensure proper log retention.
- Configuration Management (CM): Enforce secure baseline configurations (e.g., CIS Benchmarks) using configuration management tools. Implement robust patch management.
- Identification and Authentication (IA): Implement strong password policies, MFA for all users and non-human identities accessing CUI, and secure authentication protocols.
- Incident Response (IR): Develop and test an Incident Response Plan (IRP). Conduct regular IR drills using scenarios relevant to CUI.
- System and Information Integrity (SI): Deploy EDR/XDR solutions. Implement Web Application Firewalls (WAFs) for web apps handling CUI. Perform application security testing (SAST, DAST) for custom applications. Implement File Integrity Monitoring (FIM).
- Supply Chain Risk Management (SR) - New in Rev. 3: Implement vendor risk assessment processes and use Third-Party Risk Management (TPRM) platforms to assess and monitor supplier security postures.
- Planning (PL) - New in Rev. 3: Develop and document comprehensive security plans, policies, and procedures that guide all aspects of CUI protection.
- System and Services Acquisition (SA) - New in Rev. 3: Integrate security requirements into your system and software acquisition processes (e.g., secure coding, vulnerability assessments of acquired software).
- And all other control families (AT, MA, MP, PS, PE, RA, SA, SC)
- This is where most of the hands-on technical work occurs, aligning with the 17 families:
- Conduct Continuous Monitoring and Testing:
- Technical Action: Compliance is not a one-time event. Regularly monitor your systems and controls to ensure they remain effective.
- Tools:
- Vulnerability Scanners: Conduct regular internal and external vulnerability scans.
- Penetration Testing: Perform annual (or more frequent) penetration tests on your CUI enclave, including web application, mobile, and API penetration testing.
- Breach and Attack Simulation (BAS): Continuously test the effectiveness of your security controls and detection capabilities against simulated attacks.
- Security Information and Event Management (SIEM): Continuously review and alert on security events.
- Attack Surface Management (ASM): Continuously discover and monitor your external attack surface for unknown assets or new vulnerabilities.
- Documentation and Evidence Collection:
- Technical Action: Maintain thorough documentation of all policies, procedures, technical configurations, audit logs, assessment results, and remediation actions. This evidence is critical for demonstrating compliance to auditors.
- Ongoing Training and Awareness:
- Technical Action: Continuously train your personnel on their roles and responsibilities in protecting CUI.
Consequences of Non-Compliance with NIST SP 800-171 (Rev. 3)
The consequences of failing to comply with NIST SP 800-171 Rev. 3 (and by extension, the associated DFARS clauses and CMMC requirements) can be severe and detrimental to an organization's operations and financial viability. These are not merely recommendations; they are enforceable contractual obligations.
- Loss of Government Contracts and Business Opportunities:
- Contract Termination: The most direct and immediate threat. Federal agencies, especially the DoD, can terminate existing contracts if a contractor or subcontractor is found to be non-compliant or fails to protect CUI.
- Inability to Bid on Future Contracts: Non-compliance will disqualify organizations from bidding on new federal contracts that involve CUI, effectively shutting them out of a significant market segment. This is particularly true with the phased implementation of CMMC 2.0, where an organization's CMMC certification level (based on NIST SP 800-171) will be a mandatory go/no-go criterion for contract awards.
- Financial Penalties and Legal Action:
- False Claims Act (FCA) Violations: If an organization falsely claims compliance with NIST SP 800-171 requirements in its System Security Plan (SSP) or other documentation, it can be liable under the False Claims Act. Penalties for FCA violations can be substantial, including treble damages (three times the amount of the government's damages) plus significant per-claim penalties.
- Breach-Related Costs: In the event of a CUI breach resulting from non-compliance, the organization will incur significant costs:
- Forensic Investigation: Mandatory and expensive investigations by approved forensic firms.
- Remediation: Costs to fix the vulnerabilities and strengthen security.
- Legal Fees: Defense costs against potential lawsuits.
- Reputational Damage Control: Public relations efforts to mitigate negative press.
- Lost Revenue: Due to operational disruption or loss of business.
- Specific Fines/Penalties (Agency-Dependent): While NIST SP 800-171 doesn't have direct fines, specific agencies or the government may impose penalties as part of contractual breaches or regulatory actions stemming from the failure to protect CUI.
- Reputational Damage and Loss of Trust:
- A public acknowledgment of non-compliance or a CUI breach can severely tarnish an organization's reputation within the DIB and the broader industry. This leads to a loss of trust from government partners, other contractors, and even commercial clients.
- It can make it difficult to attract and retain skilled employees, particularly cybersecurity professionals.
- Increased Scrutiny and Audits:
- Organizations with a history of non-compliance or CUI incidents will likely face more frequent and rigorous audits and assessments from federal agencies or third-party assessors (like CMMC Third-Party Assessment Organizations - C3PAOs). This can be a significant drain on resources.
- Operational Disruption:
- A CUI breach can lead to significant operational downtime, impacting your ability to deliver services or products, fulfill contracts, and continue business as usual.
In summary, non-compliance with NIST SP 800-171 Rev. 3 is a direct path to severe business disruption, significant financial penalties, legal liabilities, and lasting damage to an organization's reputation, especially for those in the federal supply chain.
How ImmuniWeb Helps Comply with NIST SP 800-171 (Rev. 3)?
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform directly addresses several key technical requirements within NIST SP 800-171 Rev. 3, particularly those related to vulnerability management, application security, continuous monitoring, and supply chain risk.
Here's how ImmuniWeb can significantly aid compliance efforts:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By integrating ImmuniWeb's comprehensive security testing and monitoring solutions, organizations can not only identify and remediate vulnerabilities but also generate the necessary evidence and documentation to demonstrate robust technical controls and satisfy a significant portion of their NIST SP 800-171 Rev. 3 compliance requirements.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
