Payment Card Industry Data Security Standard (PCI DSS) Compliance
PCI DSS is a global security standard that mandates strict controls for handling, processing, and storing
payment card data to prevent fraud and protect cardholder information through measures
like encryption, access controls, and regular security testing.

The Payment Card Industry Data Security Standard (PCI DSS) is a globally mandated set of security standards designed to ensure that all companies that process, store, or transmit credit card information maintain a secure environment. Established by the major credit card brands (Visa, MasterCard, American Express, Discover, and JCB) through the PCI Security Standards Council (PCI SSC), PCI DSS aims to reduce credit card fraud by increasing controls around cardholder data.
The latest version, PCI DSS v4.0, released in March 2022, reflects the evolving threat landscape and payment technologies. It emphasizes continuous security processes, enhanced validation methods, and greater flexibility for organizations to meet security objectives, moving away from a check-box approach to a more risk-based, proactive security posture. The transition period for v4.0 ended on March 31, 2024, with some "future-dated" requirements becoming mandatory on March 31, 2025.
Overview of Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS comprises 12 core requirements, categorized under six logically related goals:
Build and Maintain a Secure Network and Systems:
1. Install and maintain network security controls: This includes firewalls and routers to protect cardholder data.
2. Apply secure configurations to all system components: Do not use vendor-supplied defaults for system passwords and other security parameters.
Protect Cardholder Data:
3. Protect stored cardholder data: Minimize data storage and encrypt stored cardholder data.
4. Protect cardholder data with strong cryptography during transmission over open, public networks: Ensure data is encrypted while in transit.
Maintain a Vulnerability Management Program:
5. Protect all systems and networks from malicious software: Implement and regularly update anti-malware solutions.
6. Develop and maintain secure systems and software: Ensure applications and systems are secure by design and regularly patched.
Implement Strong Access Control Measures:
7. Restrict access to cardholder data by business need-to-know: Limit access to only those who require it for their job function.
8. Identify users and authenticate access to system components: Implement strong authentication methods.
9. Restrict physical access to cardholder data: Secure physical locations where cardholder data is stored or processed.
Regularly Monitor and Test Networks:
10. Log and monitor all access to system components and cardholder data: Implement robust logging and monitoring for all activity within the Cardholder Data Environment (CDE).
11. Test security of systems and processes regularly: Conduct regular vulnerability scans and penetration tests.
Maintain an Information Security Policy:
12. Support information security with organizational policies and programs: Establish and maintain comprehensive information security policies and procedures.
PCI DSS v4.0 introduced new requirements and expanded existing ones to address modern threats like e-skimming, phishing, and ransomware. Key changes include:
- Expanded Multi-Factor Authentication (MFA) requirements for all users accessing the Cardholder Data Environment (CDE), not just administrators.
- More granular requirements for network segmentation.
- New requirements for automated technical controls for payment page integrity.
- Increased emphasis on documented and assigned roles/responsibilities for security activities.
- More prescriptive guidance for customized approaches to compliance, requiring detailed risk analyses.
- Focus on continuous security and monitoring, rather than point-in-time compliance.

Key Aspects of Payment Card Industry Data Security Standard (PCI DSS) Compliance
PCI DSS compliance requires a significant technical undertaking, often impacting an organization's entire IT infrastructure and operational processes.
- Scoping the Cardholder Data Environment (CDE):
- Technical Details: The CDE encompasses all system components that store, process, or transmit Cardholder Data (CHD) or Sensitive Authentication Data (SAD), as well as any system components that could impact the security of the CDE. This includes applications, servers, databases, network devices, virtual components, and cloud environments.
- Technical Implementation: Requires detailed network diagrams, data flow diagrams illustrating where CHD enters, is stored, processed, and transmitted. Utilize network discovery tools and data mapping tools to identify all systems that interact with CHD. Network segmentation (e.g., VLANs, firewalls) is critical to isolate the CDE and reduce its scope, thereby reducing the compliance burden.
- Network Security Controls (Requirement 1):
- Technical Details: Install and maintain firewalls and routers to protect the CDE. This includes restricting traffic, securing router configurations, and segmenting the CDE from other networks.
- Technical Implementation: Configure and manage Next-Generation Firewalls (NGFWs) with strict access control lists (ACLs) to control inbound and outbound traffic. Implement Intrusion Prevention Systems (IPS) to detect and block malicious network activity. Deploy network segmentation (e.g., physical separation, logical segmentation with VLANs and dedicated firewalls) to isolate the CDE from less secure networks. Regularly review firewall rules for effectiveness and necessity.
- Secure Configurations (Requirement 2):
- Technical Details: Eliminate vendor default passwords and security parameters for all system components. Implement secure hardening standards.
- Technical Implementation: Use configuration management tools (e.g., Ansible, Puppet, Chef, Group Policy Objects) to enforce secure baseline configurations (e.g., CIS Benchmarks) on all servers, workstations, network devices, and applications within the CDE. Implement automated vulnerability scanners to identify misconfigurations and unpatched systems.
- Protect Stored Cardholder Data (Requirement 3):
- Technical Details: Minimize storage of CHD and never store SAD after authorization. Encrypt stored CHD using strong cryptography. Mask PAN (Primary Account Number) when displayed.
- Technical Implementation:
- Data Minimization: Implement data retention policies and automated processes to securely delete CHD when no longer needed.
- Encryption at Rest: Utilize full disk encryption, database encryption (e.g., TDE - Transparent Data Encryption), or tokenization/point-to-point encryption (P2PE) solutions to render PAN unreadable if the data store is compromised.
- Key Management System (KMS): Implement a robust KMS to securely generate, store, distribute, and rotate encryption keys.
- Data Discovery Tools: Use tools to identify where CHD might be stored inadvertently across systems.
- Encrypt Data in Transit (Requirement 4):
- Technical Details: Encrypt CHD during transmission over open, public networks using strong cryptography.
- Technical Implementation: Enforce TLS 1.2 or higher for all web traffic involving CHD (HTTPS). Use secure VPNs for remote access and site-to-site connections transmitting CHD. Ensure secure protocols (e.g., SFTP, SSH) for data transfers.
- Malware Protection (Requirement 5):
- Technical Details: Protect all systems from malware and regularly update anti-malware software.
- Technical Implementation: Deploy Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) solutions on all systems within and connected to the CDE. Implement centralized anti-malware management systems that ensure regular updates and scans.
- Secure Systems and Software (Requirement 6):
- Technical Details: Develop and maintain secure systems and applications, including addressing common coding vulnerabilities and applying security patches.
- Technical Implementation:
- Patch Management: Implement an automated patch management system to ensure timely application of security patches to all operating systems, applications, and firmware.
- Secure Development Lifecycle (SSDLC): Integrate security into every phase of the software development lifecycle.
- Application Security Testing: Conduct Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) for custom applications that handle CHD. Use Software Composition Analysis (SCA) tools to identify vulnerabilities in third-party libraries.
- Web Application Firewalls (WAFs): Deploy and configure WAFs to protect web-facing applications from common web attacks (e.g., SQL injection, XSS).
- Access Controls (Requirement 7 & 8):
- Technical Details: Restrict access to CHD based on "need-to-know" and implement strong authentication, including Multi-Factor Authentication (MFA).
- Technical Implementation:
- Role-Based Access Control (RBAC): Implement granular RBAC to ensure users only have access to the specific data and systems required for their job function.
- Multi-Factor Authentication (MFA): Implement MFA for all access into the CDE, and for remote access by personnel to the CDE, including administrators (now mandatory for all users accessing CDE in v4.0). Use strong authentication methods (e.g., FIDO2, TOTP, smart cards).
- Privileged Access Management (PAM): Deploy PAM solutions to manage, monitor, and control highly privileged accounts (e.g., administrators, root accounts) accessing the CDE.
- Identity and Access Management (IAM): Centralize user provisioning and de-provisioning, and conduct regular access reviews.
- Physical Security (Requirement 9):
- Technical Details: Restrict physical access to CDE systems and data.
- Technical Implementation: Implement electronic access control systems, video surveillance, and visitor logging for facilities housing CDE components. Secure physical media containing CHD.
- Logging and Monitoring (Requirement 10):
- Technical Details: Implement detailed logging for all access to system components and CHD, and regularly review logs for suspicious activity.
- Technical Implementation: Deploy a Security Information and Event Management (SIEM) system to collect, aggregate, correlate, and analyze logs from all systems within and connected to the CDE. Configure real-time alerts for suspicious events. Implement File Integrity Monitoring (FIM) to detect unauthorized changes to critical system files.
- Regular Testing (Requirement 11):
- Technical Details: Conduct regular vulnerability scans and penetration tests.
- Technical Implementation:
- Internal & External Vulnerability Scans: Perform quarterly internal and external vulnerability scans by a PCI SSC Approved Scanning Vendor (ASV) for external scans.
- Penetration Testing: Conduct annual internal and external penetration tests (or after significant changes) by a qualified internal resource or third party. These tests should simulate real-world attacks.
- Web Application Penetration Testing: Specifically test web applications for vulnerabilities (e.g., OWASP Top 10).
- Information Security Policy (Requirement 12):
- Technical Details: Establish, document, and disseminate a comprehensive information security policy.
- Technical Implementation: This requires thorough documentation of all technical controls, procedures, incident response plans, and security awareness training programs. Implement security awareness training platforms for employees.
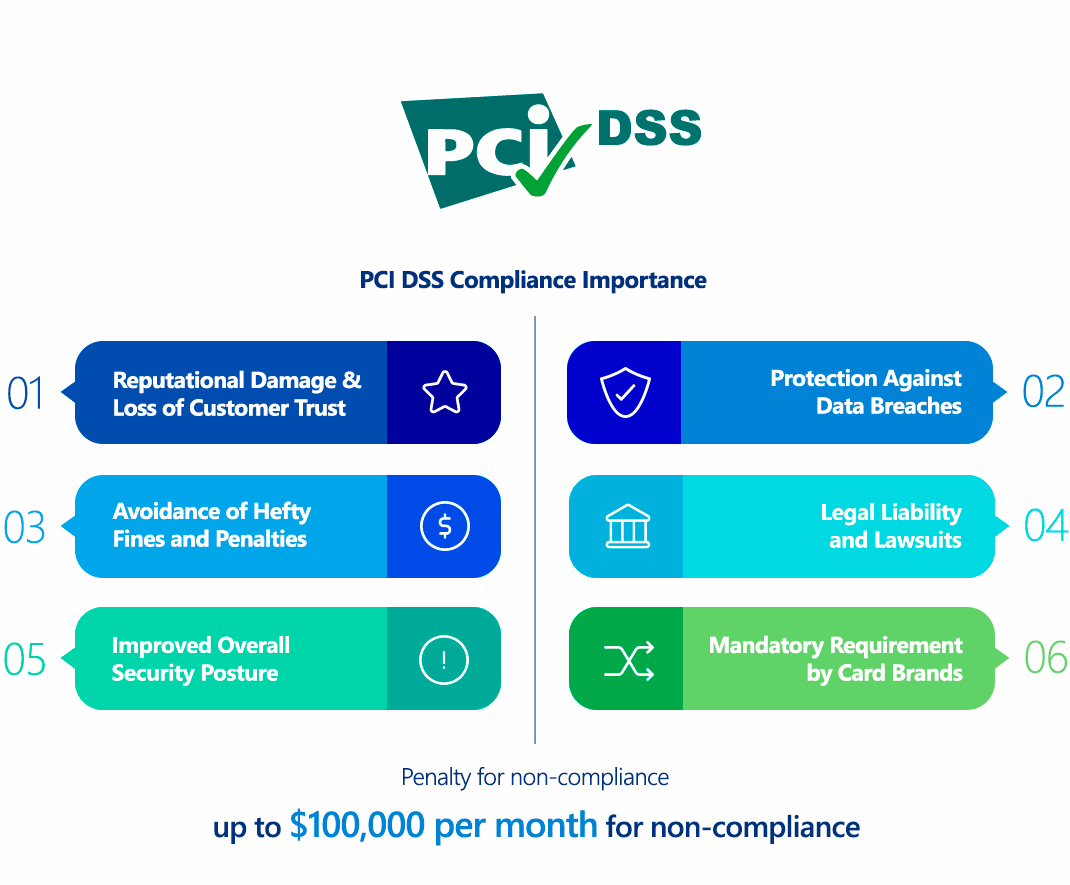
Why Is Payment Card Industry Data Security Standard (PCI DSS) Compliance Important?
PCI DSS compliance is not merely a technical checklist; it's a critical business imperative for any entity handling payment card data. Its importance stems from several key factors:
- Mandatory Requirement by Card Brands: PCI DSS is not a law, but a contractual obligation imposed by the major payment card brands (Visa, MasterCard, American Express, Discover, JCB). Acquiring banks (the banks that process credit card transactions for merchants) are responsible for ensuring their merchants comply. Failure to comply can result in the termination of card processing privileges.
- Protection Against Data Breaches and Fraud: The primary goal of PCI DSS is to protect sensitive cardholder data from compromise. By implementing the robust security controls mandated by the standard, organizations significantly reduce their risk of data breaches, which can lead to massive financial losses due identity theft, fraud, and remediation costs.
- Avoidance of Hefty Fines and Penalties: Non-compliance can result in substantial monthly fines levied by acquiring banks, ranging from $5,000 to $100,000 per month, depending on the volume of transactions and the duration of non-compliance. These fines are often passed down from the payment brands. In the event of a breach, additional per-cardholder fines (e.g., $50-$90 per affected customer) and forensic audit costs can be imposed.
- Reputational Damage and Loss of Customer Trust: A data breach resulting from non-compliance can severely damage an organization's reputation. News of a breach erodes customer trust, leading to customer attrition, negative media attention, and a significant blow to brand image, which can take years to recover from.
- Legal Liability and Lawsuits: While PCI DSS isn't a law, non-compliance in the event of a breach can strengthen legal cases against the organization. Affected individuals, banks, and other entities may pursue lawsuits for damages resulting from stolen cardholder data.
- Improved Overall Security Posture: Even beyond the specific requirements, the disciplined approach mandated by PCI DSS encourages organizations to adopt a comprehensive and proactive cybersecurity strategy. This spills over into protecting other sensitive business data and intellectual property.
- Business Continuity: Robust security measures, including incident response planning and regular testing, contribute to greater business resilience and continuity in the face of cyber threats.
In essence, PCI DSS compliance is about safeguarding customer trust, avoiding severe financial penalties, maintaining the ability to process card payments, and protecting the very foundation of your business operations in the digital economy.
Who Needs to Comply with Payment Card Industry Data Security Standard (PCI DSS)?
The PCI DSS applies to all entities that store, process, or transmit cardholder data (CHD) and/or sensitive authentication data (SAD), regardless of their size or the volume of transactions. This broad scope includes:
- Merchants: Any business that accepts credit or debit card payments for goods or services. This ranges from small retail shops and e-commerce websites to large multinational corporations.
- Service Providers: Organizations that handle CHD on behalf of other entities. Examples include:
- Payment gateways and processors
- Hosting providers that host CDEs
- Managed security service providers (MSSPs) that manage security for CDEs
- Call centers that handle card information over the phone
- Cloud service providers (CSPs) if they store, process, or transmit CHD.
- Acquiring Banks: Financial institutions that process credit or debit card payments on behalf of merchants. They are responsible for ensuring their merchants are PCI DSS compliant.
- Issuing Banks: Financial institutions that issue credit or debit cards to consumers.
- Payment Brands: Visa, MasterCard, American Express, Discover, and JCB, who jointly developed and maintain the PCI DSS.
Levels of Compliance:
The specific validation requirements (e.g., Self-Assessment Questionnaire - SAQ, or Report on Compliance - ROC) and the frequency of external scans often depend on the volume of transactions an entity processes annually. Merchants are typically categorized into four levels:
- Level 1: Merchants processing over 6 million card transactions annually.
- Level 2: Merchants processing 1 million to 6 million transactions annually.
- Level 3: Merchants processing 20,000 to 1 million e-commerce transactions annually.
- Level 4: Merchants processing fewer than 20,000 e-commerce transactions or up to 1 million non-e-commerce transactions annually.
While smaller merchants (Levels 3 and 4) may be able to use a Self-Assessment Questionnaire (SAQ) to validate compliance, they are still obligated to meet all 12 requirements of PCI DSS. Regardless of size or volume, if you touch cardholder data, you must comply.
Payment Card Industry Data Security Standard (PCI DSS) vs GDPR Comparison
PCI DSS and GDPR are both crucial for data protection but address different aspects and have distinct scopes and objectives. They are complementary rather than mutually exclusive.
| Aspect | PCI DSS (Payment Card Industry Data Security Standard) | GDPR (General Data Protection Regulation) |
|---|---|---|
| Type of Standard/Law | Industry Standard (mandated by card brands via contract). | Legally Binding Regulation in the EU. |
| Primary Focus | Payment Card Security: Protecting the confidentiality, integrity, and availability of cardholder data. | Data Privacy and Rights: Protecting the personal data and privacy rights of EU data subjects. |
| Scope of Data | Specifically targets Cardholder Data (CHD) and Sensitive Authentication Data (SAD). | Broadly covers Personal Data (any information relating to an identified or identifiable natural person). |
| Applicability | Applies globally to any entity that stores, processes, or transmits cardholder data. | Applies globally to any entity processing personal data of EU residents, regardless of the entity's location. |
| Purpose | To prevent credit card fraud and ensure secure payment transactions. | To give individuals control over their personal data and harmonize data protection laws across the EU. |
| Legal Basis for Processing | Not directly addressed (focus is on security). | Requires a specific legal basis (e.g., consent, contract, legitimate interest) for all data processing. |
| Data Subject Rights | No explicit individual rights over their data. | Grants extensive individual rights (e.g., right to access, rectification, erasure, portability, objection). |
| Technical Measures | Highly prescriptive with 12 detailed requirements and hundreds of sub-requirements (e.g., specific encryption standards, penetration testing frequency). | Requires "appropriate technical and organizational measures" (Art. 32); generally less prescriptive on specific technical solutions. |
| Breach Notification | Requires immediate notification to payment brands and potentially others. | Mandatory notification to supervisory authority within 72 hours; individuals notified "without undue delay" if high risk. |
| Third-Party Providers | Explicit and detailed requirements for managing third-party service provider security. | Requires appropriate contracts and due diligence for processors. |
| Enforcement Authority | Payment card brands, enforced through acquiring banks. | Data Protection Authorities (DPAs) in each EU member state. |
| Penalties | Monthly fines ($5,000 - $100,000+), per-record breach fines, loss of card processing privileges. | Significant fines (up to €20 million or 4% of global annual turnover, whichever is higher). |
| Relationship | Complementary: PCI DSS focuses on securing a specific type of personal data (payment card data). Compliance with PCI DSS helps to satisfy many of the security requirements of GDPR, especially Article 32. However, GDPR's scope is much broader, covering all personal data and emphasizing privacy rights beyond security. An organization processing EU cardholder data must comply with both. |
In essence, PCI DSS is a specific security framework for financial transactions, while GDPR is a broad privacy law for all personal data. An organization compliant with PCI DSS will have a strong foundation for managing the security of personal data, but it will still need to implement GDPR's principles around individual rights, consent, transparency, and broader data lifecycle management.
How to Ensure Payment Card Industry Data Security Standard (PCI DSS) Compliance?
Ensuring PCI DSS v4.0.1 compliance is a multifaceted and continuous effort, requiring dedicated resources, ongoing monitoring, and robust technical controls.
- Define and Scope the Cardholder Data Environment (CDE):
- Technical Action: This is the most critical first step. Accurately identify all systems, networks, applications, and processes that store, process, or transmit Cardholder Data (CHD) or Sensitive Authentication Data (SAD). This includes point-of-sale (POS) systems, e-commerce platforms, databases, network devices, virtual machines, cloud instances, and even physical documents.
- Use network scanning tools, data discovery tools, and network segmentation analysis to precisely map your CDE. The smaller and more isolated your CDE, the easier and less costly compliance will be. Implement network segmentation (e.g., VLANs, firewalls) to isolate the CDE from the rest of your corporate network.
- Implement and Maintain Network Security Controls (Req. 1):
- Technical Action: Deploy and configure firewalls and routers at all entry and exit points of the CDE. Define and enforce strict firewall rules that restrict traffic to only what is absolutely necessary for business operations. Regularly review and update these rules. Utilize Intrusion Prevention Systems (IPS) to actively block malicious traffic.
- Apply Secure Configurations (Req. 2):
- Technical Action: Remove all vendor default passwords and settings on all system components in the CDE (servers, network devices, applications, POS devices). Implement and enforce secure hardening baselines (e.g., CIS Benchmarks) using configuration management tools (e.g., Ansible, Puppet, PowerShell DSC) to automate consistent security configurations. Regularly audit configurations for deviations.
- Protect Stored Cardholder Data (Req. 3):
- Technical Action: Minimize data retention of CHD. Implement data encryption at rest for all stored CHD using strong cryptography (e.g., AES-256 for databases, file systems). Consider tokenization or Point-to-Point Encryption (P2PE) solutions to minimize the storage of raw PAN. Never store SAD (CVV2, PIN data). Implement a secure Key Management System (KMS) to manage encryption keys.
- Encrypt Data in Transit (Req. 4):
- Technical Action: Ensure all transmission of CHD over public networks (e.g., internet) uses strong cryptographic protocols like TLS 1.2 or higher for web traffic (HTTPS) and secure VPNs for other transmissions. Disable older, vulnerable protocols (e.g., SSL/TLS 1.0/1.1).
- Protect from Malware (Req. 5):
- Technical Action: Deploy Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) solutions on all systems within and connected to the CDE. Ensure anti-malware is kept up-to-date with the latest signatures and performs regular scans.
- Develop and Maintain Secure Systems and Software (Req. 6):
- Technical Action: Implement a robust patch management program that promptly applies security patches to all operating systems, applications, and network devices. Integrate security testing into your software development lifecycle (SDLC) for custom applications (e.g., SAST, DAST, SCA tools). Deploy and configure Web Application Firewalls (WAFs) for all public-facing web applications in the CDE.
- Implement Strong Access Controls (Req. 7 & 8):
- Technical Action: Implement Role-Based Access Control (RBAC) to limit access to CHD based on documented "business need-to-know." Ensure unique user IDs for all individuals. Implement Multi-Factor Authentication (MFA) for all access to the CDE and for remote access by personnel to the CDE. Deploy Privileged Access Management (PAM) solutions to secure, monitor, and manage administrative and service accounts.
- Restrict Physical Access (Req. 9):
- Technical Action: Implement physical security measures such as surveillance cameras, access control systems (e.g., badge readers), and strict visitor policies for areas housing CDE components.
- Log and Monitor All Access (Req. 10):
- Technical Action: Implement comprehensive logging across all system components within and connected to the CDE. Deploy a Security Information and Event Management (SIEM) system to centralize, correlate, and analyze logs in real-time. Configure automated alerts for suspicious activities, unauthorized access attempts, and system configuration changes. Implement File Integrity Monitoring (FIM) to detect unauthorized changes to critical files.
- Test Security Regularly (Req. 11):
- Technical Action: Conduct quarterly external vulnerability scans by a PCI SSC Approved Scanning Vendor (ASV). Perform quarterly internal vulnerability scans. Conduct annual penetration tests (internal and external) and web application penetration tests (for public-facing web apps in the CDE) by qualified personnel or third parties. Test network segmentation controls at least annually.
- Maintain an Information Security Policy (Req. 12):
- Technical Action (Support): Develop and implement comprehensive cybersecurity policies and procedures, including an incident response plan (IRP). Conduct regular security awareness training for all personnel. Document all security controls, processes, and test results thoroughly to provide evidence for assessments and audits.
Consequences of Non-Compliance with Payment Card Industry Data Security Standard (PCI DSS)
The consequences of PCI DSS non-compliance can be severe, impacting an organization financially, operationally, and reputationally. These penalties are typically imposed by the acquiring bank (your merchant bank) on behalf of the payment brands.
- Financial Penalties/Fines:
- Monthly Fines: Acquiring banks can levy monthly fines ranging from $5,000 to $100,000 per month for non-compliance. The amount depends on the volume of transactions processed and the duration of non-compliance. These fines are often passed down from the card brands.
- Per-Cardholder Fines: In the event of a data breach, organizations may face additional fines ranging from $50 to $90 per affected cardholder. These costs can quickly escalate to millions of dollars for larger breaches.
- Forensic Investigation Costs: Following a breach, a mandatory forensic investigation by a PCI SSC-approved QSA (Qualified Security Assessor) or PFI (PCI Forensic Investigator) is required to determine the cause and scope of the incident. These investigations are expensive, often costing tens of thousands to hundreds of thousands of dollars.
- Fraud Losses: The non-compliant organization may be liable for the fraudulent transactions that occur as a result of a data breach.
- Credit Monitoring Costs: Affected cardholders may need to be provided with credit monitoring services, which can be a significant expense.
- Loss of Card Processing Privileges:
- The most significant consequence is the termination of your ability to process credit and debit card payments. If an organization cannot process card transactions, its business operations can be severely impacted or even cease.
- Reputational Damage and Loss of Customer Trust:
- News of a data breach and subsequent non-compliance can cause irreparable damage to an organization's brand and public image. This leads to a loss of customer confidence, potential customer churn, and difficulty attracting new business. Recovery from reputational damage can take years.
- Legal Liability and Lawsuits:
- Non-compliance can expose organizations to lawsuits from affected cardholders, banks, and other third parties. While PCI DSS itself is not a law, a breach stemming from non-compliance can lead to civil litigation.
- Organizations may also face investigations and penalties from state and federal regulatory bodies if the breach involves protected personal data (e.g., under state data breach notification laws or FTC regulations).
- Increased Audit Requirements:
- Organizations that have experienced a breach or demonstrated non-compliance may be subjected to more frequent and stringent compliance validation requirements, including mandatory quarterly ASV scans and annual on-site assessments by a QSA.
- Higher Insurance Premiums:
- Cyber insurance providers may increase premiums or deny coverage to organizations with a history of non-compliance or breaches.
In summary, ignoring PCI DSS compliance is a high-stakes gamble that can result in catastrophic financial losses, operational shutdown, and a devastating blow to an organization's standing in the market.
How ImmuniWeb Helps Comply with Payment Card Industry Data Security Standard (PCI DSS)?
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides robust technical capabilities that directly support organizations in meeting numerous PCI DSS requirements.
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By integrating ImmuniWeb's solutions, organizations can gain a comprehensive and continuously updated view of their technical security posture, efficiently identify and remediate vulnerabilities, test their incident response capabilities, and effectively manage third-party risks – all essential components for achieving and maintaining ISO 27001:2022 certification.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
