Saudi Arabia Personal Data Protection Law (PDPL) Compliance
The Saudi Arabian Personal Data Protection Law (PDPL) regulates the processing of personal data to protect individuals'
privacy rights by imposing obligations on entities handling such data, including obtaining consent,
ensuring security, and granting data subjects specific rights.

The Kingdom of Saudi Arabia, in its ambitious pursuit of a digital economy aligned with Vision 2030, has enacted a landmark piece of legislation: the Personal Data Protection Law (PDPL). Fully enforced as of September 14, 2024, after an initial grace period, the PDPL marks a pivotal shift in how personal data is handled across both public and private sectors in the Kingdom. It is designed to empower individuals with greater control over their information and ensure that organizations adhere to robust standards for data processing, aiming to build trust in Saudi Arabia's burgeoning digital landscape.
The PDPL introduces comprehensive requirements for data collection, processing, storage, and transfer, demanding significant technical and organizational adjustments from any entity handling the personal data of Saudi residents. For businesses operating within or targeting the Saudi market, understanding and meticulously implementing the technical nuances of the PDPL is no longer optional, but a legal and strategic imperative.
This article provides a detailed technical overview of the Saudi Arabian PDPL, outlining its key provisions, compliance requirements, and the profound implications for data management and cybersecurity.
Overview of Saudi Arabia Personal Data Protection Law (PDPL)
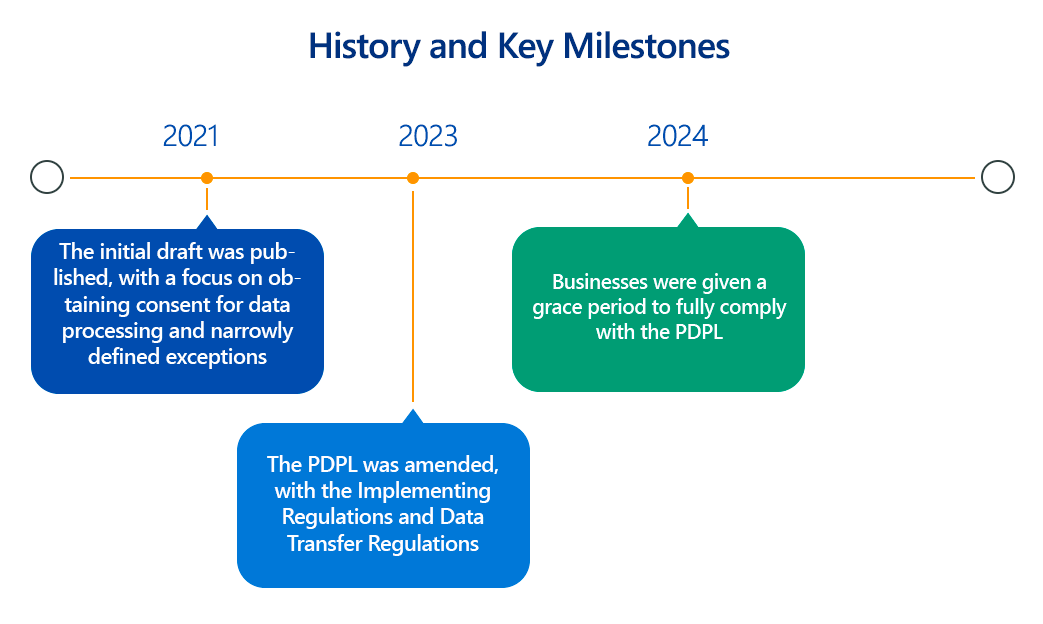
The Personal Data Protection Law (PDPL), promulgated by Royal Decree M/19 in 2021 and overseen by the Saudi Authority for Data and Artificial Intelligence (SDAIA), is Saudi Arabia's first comprehensive data privacy regulation. Its core objective is to protect the privacy of individuals' personal data and to regulate the entire lifecycle of data processing activities.
The PDPL is built on several fundamental principles, akin to global privacy frameworks:
- Lawfulness, Fairness, and Transparency: Personal data must be processed lawfully, fairly, and transparently, with individuals informed about the purposes of collection and use.
- Purpose Limitation: Data must be collected only for specific, explicit, and legitimate purposes and not processed further in a manner incompatible with those purposes.
- Data Minimization: Only personal data that is necessary for the specified purposes should be collected.
- Accuracy: Personal data must be accurate, complete, and kept up-to-date.
- Storage Limitation: Personal data should not be retained longer than necessary for the purposes for which it was collected, unless legally required.
- Security: Appropriate technical and organizational measures must be implemented to protect personal data from loss, misuse, unauthorized access, disclosure, alteration, or destruction.
- Accountability: Data controllers are responsible for demonstrating compliance with the PDPL.
The PDPL defines "personal data" broadly as "any data, regardless of its source or form, that may lead to identifying an individual specifically, or that may directly or indirectly make it possible to identify an individual." This includes names, ID numbers, addresses, contact details, financial information, photos, videos, and "sensitive personal data" (e.g., racial or ethnic origin, religious beliefs, health data, genetic or biometric data, criminal records), which is subject to stricter controls.
Key Aspects of Saudi Arabia Personal Data Protection Law (PDPL) Compliance
PDPL compliance mandates a holistic approach, integrating legal frameworks with robust technical infrastructure and processes. Key technical aspects include:
- Lawful Basis for Processing & Consent Management:
- Technical Detail: The primary lawful basis is explicit consent, especially for sensitive personal data and direct marketing. Organizations must implement Consent Management Platforms (CMPs) on websites and applications to capture, record, and manage explicit, granular consent (opt-in by default). Consent withdrawal mechanisms must be as easy as giving consent. Other lawful bases include necessity for contract performance, legal obligations, vital interests, or public interest.
- Tooling: CMPs, privacy preference centers.
- Transparency and Privacy Notices:
- Technical Detail: Organizations must provide clear, concise, and easily accessible privacy policies/notices to data subjects before data collection. These notices must detail the purpose of collection, types of data, legal basis, data storage and destruction methods, identities of recipients, data subject rights, and contact information for the data controller/DPO.
- Tooling: Website privacy policy generators, legal notice management systems.
- Data Subject Rights (DSRs) Fulfillment:
- Technical Detail: The PDPL grants data subjects rights including the right to know (information), access, rectification, erasure (right to be forgotten), and data portability. Organizations must establish secure, efficient processes (e.g., a dedicated online portal or email address) to receive, verify, and respond to DSR requests within a specified timeframe (typically 30 days). This requires robust data discovery and indexing capabilities.
- Tooling: Data Subject Access Request (DSAR) automation platforms, data discovery and mapping tools.
- Data Minimization and Storage Limitation:
- Technical Detail: Design systems and processes to collect only the minimum personal data required for stated purposes. Implement automated data lifecycle management policies that securely delete or anonymize personal data once its retention period expires, unless legally obligated otherwise. Data discovery and classification are crucial here.
- Tooling: Data lifecycle management tools, data classification solutions.
- Security Measures (Organizational, Administrative, and Technical): This is a critical technical pillar.
- Technical Detail: Implement state-of-the-art technical and organizational measures to protect personal data from loss, misuse, unauthorized access, disclosure, alteration, or destruction. This includes:
- Encryption: Strong encryption for data at rest (databases, file systems, cloud storage) and in transit (TLS/SSL for web, VPNs, secure protocols). Secure key management (KMS, HSMs).
- Access Controls: Robust Identity and Access Management (IAM), Multi-Factor Authentication (MFA) for all users (especially privileged access), Role-Based Access Control (RBAC), and the principle of least privilege (PoLP). Privileged Access Management (PAM) solutions.
- Network Security: Firewalls (including Web Application Firewalls - WAFs), Intrusion Detection/Prevention Systems (IDS/IPS), network segmentation, and DDoS mitigation.
- Application Security: Secure Software Development Lifecycle (SSDLC) practices, regular Static (SAST) and Dynamic (DAST) Application Security Testing, and penetration testing for all applications processing personal data.
- Vulnerability Management & Patching: Continuous vulnerability scanning, regular penetration testing, and timely application of security patches for operating systems, software, and hardware.
- Logging and Monitoring: Centralized logging of security events, Security Information and Event Management (SIEM) systems for real-time threat detection and analysis, and Endpoint Detection and Response (EDR) solutions.
- Data Loss Prevention (DLP): Solutions to prevent unauthorized exfiltration of sensitive personal data.
- Backup and Disaster Recovery: Secure, encrypted backups and robust disaster recovery plans to ensure data availability and integrity.
- Tooling: Encryption solutions, IAM/MFA/PAM tools, firewalls, WAFs, IDS/IPS, vulnerability scanners, penetration testing tools, SAST/DAST, SIEM, EDR, DLP.
- Technical Detail: Implement state-of-the-art technical and organizational measures to protect personal data from loss, misuse, unauthorized access, disclosure, alteration, or destruction. This includes:
- Data Breach Notification:
- Technical Detail: Organizations must notify SDAIA "within 72 hours" of a data breach. If the breach poses a "significant risk" to the personal data of data subjects, immediate notification to affected individuals is mandatory. This requires a well-defined and regularly tested incident response plan (IRP).
- Tooling: SIEM for rapid detection, incident response platforms.
- Cross-Border Data Transfer:
- Technical Detail: Strict conditions apply to transferring personal data outside Saudi Arabia. Transfers are generally permitted only to countries with "adequate" levels of data protection (as determined by SDAIA), or if specific mechanisms like binding corporate rules or standard contractual clauses are in place, and explicit consent is obtained from the data subject for that transfer. Organizations must conduct Transfer Impact Assessments (TIAs).
- Tooling: Data mapping tools for identifying transfer flows, legal review platforms for contractual clauses.
- Data Protection Officer (DPO) and Record of Processing Activities (RoPA):
- Technical Detail: While not always mandatory for all entities, organizations processing personal data on a large scale or sensitive data are highly encouraged (or may be required by implementing regulations) to appoint a DPO. All organizations must maintain a detailed Record of Processing Activities (RoPA).
- Tooling: GRC platforms, privacy management software for RoPA.
- Data Protection Impact Assessments (DPIAs):
- Technical Detail: Organizations must conduct DPIAs for any products or services that involve processing personal data and pose a high risk to data subjects' privacy, especially those available to the public. These assessments must detail the processing activities, risks, and proposed mitigation measures.
- Tooling: DPIA automation software.
- Registration with SDAIA:
- Technical Detail: Many controllers (especially public entities or those whose main activity is personal data processing) are required to register in the National Controllers Register with SDAIA.
Why Is Saudi Arabia Personal Data Protection Law (PDPL) Compliance Important?
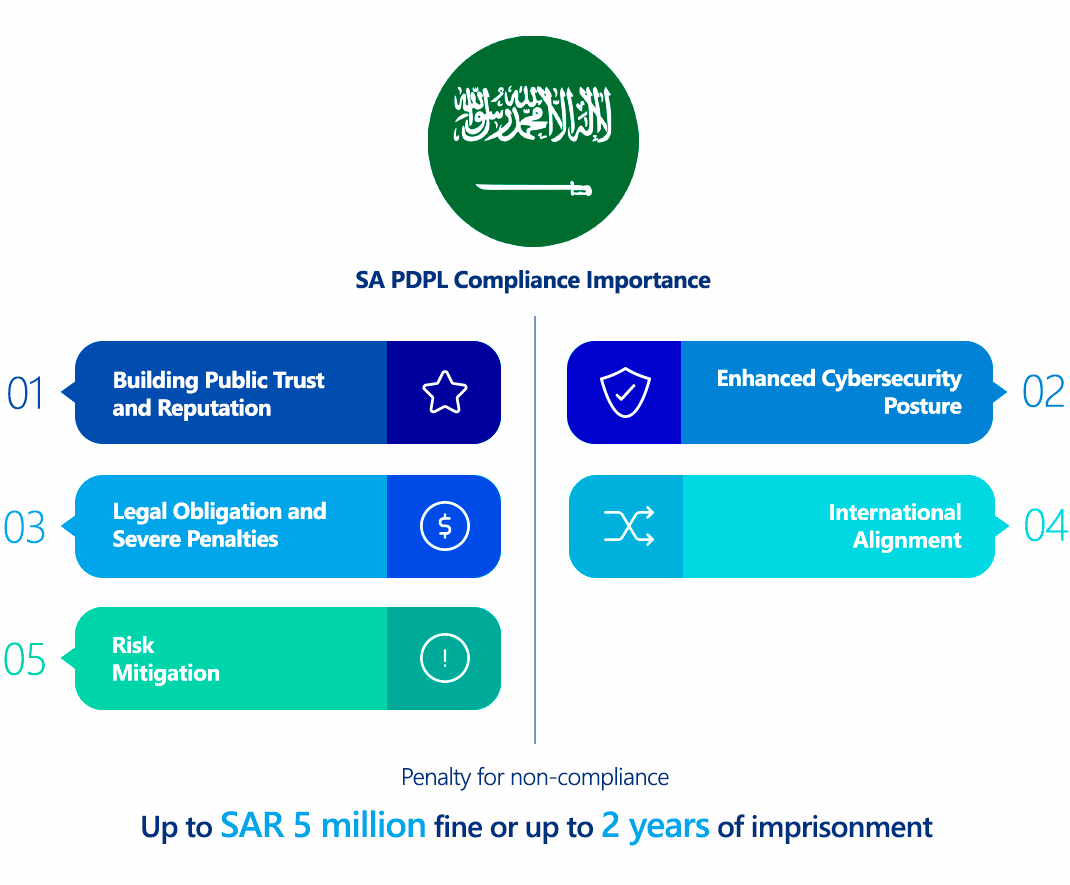
PDPL compliance is critical for organizations operating in or engaging with Saudi Arabia for several reasons:
- Legal Obligation and Severe Penalties: The PDPL carries significant penalties for non-compliance, including administrative fines of up to SAR 5 million (approximately USD 1.3 million) for general violations, which can be doubled for repeat offenses. For unauthorized disclosure or publication of sensitive personal data with intent to harm or for personal gain, penalties can include imprisonment for up to two years and/or a fine of up to SAR 3 million (approximately USD 800,000).
- Building Public Trust and Reputation: In an increasingly privacy-aware world, demonstrating adherence to data protection laws is crucial for building and maintaining trust with customers, partners, and employees. Non-compliance leading to data breaches or privacy incidents can severely damage an organization's reputation and lead to a loss of market share.
- Facilitating Digital Transformation and Investment: The PDPL is a cornerstone of Saudi Vision 2030, which aims to transform the Kingdom into a digital, data-driven economy. Robust data protection fosters a secure environment for innovation, cloud computing, and AI, attracting foreign investment and enabling seamless digital services.
- Enhanced Cybersecurity Posture: The stringent security requirements of the PDPL compel organizations to implement strong technical and organizational cybersecurity measures. This inherently strengthens defenses against cyber threats, making organizations more resilient to attacks.
- Risk Mitigation: Compliance helps organizations systematically identify, assess, and mitigate risks associated with data processing, reducing the likelihood of costly data breaches, legal disputes, and regulatory enforcement actions.
- International Alignment: While having unique aspects, the PDPL shares many principles with global privacy standards like GDPR. Compliance with PDPL helps align Saudi Arabian businesses with international best practices, facilitating international data transfers and commerce.
Who Needs to Comply with Saudi Arabia Personal Data Protection Law (PDPL)?
The PDPL has a broad scope, covering virtually any entity that processes personal data related to individuals within Saudi Arabia:
- Any public or private entity in Saudi Arabia: This includes all businesses, government agencies, non-profits, and any other organization operating within the Kingdom.
- Any entity located outside Saudi Arabia if they process the personal data of individuals residing in Saudi Arabia, regardless of the means of processing (automated or non-automated). This grants the PDPL extraterritorial reach.
Key considerations:
- The law applies to the data of both living and deceased individuals if it could lead to identifying them or a family member.
- It covers both "personal data" and "sensitive personal data", with the latter requiring additional safeguards.
Exemptions (limited):
The PDPL generally does not apply to:
- Personal data processed for personal or household use.
- Processing for official security, judicial, or intelligence purposes by public entities, provided specific conditions and safeguards are met.
- Processing for public health purposes, provided specific conditions are met.
- Processing for scientific, research, or statistical purposes, with proper anonymization or aggregation.
Saudi Arabia Personal Data Protection Law (PDPL) vs GDPR Comparison
The Saudi PDPL shares foundational principles with the EU's GDPR, often considered a global benchmark. However, there are significant differences in specifics, particularly in certain technical implementations and nuances.
| Feature | Saudi Arabia PDPL (Personal Data Protection Law) | GDPR (General Data Protection Regulation) |
|---|---|---|
| Primary Focus | Comprehensive data privacy law protecting personal data of individuals in KSA, aiming to build trust and support digital transformation. | Comprehensive data privacy law protecting the personal data and privacy rights of individuals in the EU/EEA. |
| Scope of "Personal Data" | Any data identifying a natural person directly or indirectly (name, ID, contact, financial, photos, videos, etc.), also covers deceased individuals. Includes "Sensitive Personal Data." | Any information relating to an identified or identifiable natural person. Includes "Special Categories of Personal Data." |
| Territorial Scope | Applies to processing by any entity in KSA, and entities outside KSA if they process personal data of individuals residing in KSA. | Broad extraterritorial scope; applies to processing of EU/EEA residents' personal data by entities inside or outside the EU/EEA if related to offering goods/services or monitoring behavior within the EU/EEA. |
| Lawful Basis | Primarily explicit consent. Other bases: contract necessity, legal obligation, vital interests, public interest. Cannot rely on "legitimate interest" for sensitive data. | Primarily consent. Other bases: contract necessity, legal obligation, vital interests, public task, legitimate interest of the controller (subject to balancing test). |
| Consent Standard | Requires explicit consent for most processing, especially sensitive data and marketing. Must be clear, specific, informed, and easy to withdraw. Opt-in for direct marketing. | Requires "freely given, specific, informed, and unambiguous" consent, typically through an affirmative action (opt-in). Explicit consent needed for sensitive data. Withdrawal must be as easy as giving consent. |
| Data Subject Rights | Right to know/information, access, rectification, erasure (deletion), and data portability. Right to object to direct marketing. | Right to be informed, access, rectification, erasure ("right to be forgotten"), restriction of processing, data portability, objection, and rights in relation to automated decision-making and profiling. Broader set of rights overall. |
| Data Protection Officer (DPO) | Encouraged/mandated under specific conditions (e.g., large-scale processing, sensitive data). Implementing Regulations specify criteria and responsibilities. | Mandatory for public authorities, or where core activities involve large-scale systematic monitoring or processing of special categories of data. |
| Data Protection Impact Assessment (DPIA) | Mandatory for high-risk processing activities, especially for public-facing products/services. Implementing Regulations detail requirements. | Mandatory for processing "likely to result in a high risk to the rights and freedoms of natural persons." Detailed requirements for content and process. |
| Cross-Border Transfers | Strict; generally only to "adequate" countries (approved by SDAIA) or with explicit data subject consent AND specific transfer mechanisms (e.g., binding clauses) and Transfer Impact Assessment (TIA). Emphasis on data localization. | Permitted to "adequate" countries, under Standard Contractual Clauses (SCCs), Binding Corporate Rules (BCRs), or other derogations (e.g., explicit consent for specific transfers). Requires Transfer Impact Assessments (TIAs) for transfers outside adequacy decisions. |
| Data Breach Notification | Controller must notify SDAIA within 72 hours of discovery. If high risk to data subject, immediate notification to data subject. | Controller must notify supervisory authority within 72 hours of discovery. Data subjects notified "without undue delay" if high risk. |
| Regulatory Authority | Saudi Authority for Data and Artificial Intelligence (SDAIA). | Independent Supervisory Authorities in each EU member state, coordinated by the European Data Protection Board (EDPB). |
| Penalties | Fines up to SAR 5 million (doubled for repeat offenses). Imprisonment up to 2 years and/or SAR 3 million fine for sensitive data disclosure. | Fines up to €20 million or 4% of global annual turnover, whichever is higher. |
Technical Implications of Differences:
- Explicit Consent Focus: PDPL's stronger emphasis on explicit consent for most processing, particularly for direct marketing, requires more sophisticated and user-friendly CMPs and robust record-keeping of consent.
- Data Portability Nuances: While PDPL grants a right to data portability, its practical implementation and scope might be narrower than GDPR's, which often implies interoperable formats.
- Cross-Border Transfers & TIAs: The PDPL's strict requirements for international data transfers, including the need for SDAIA approval for mechanisms and explicit TIAs, necessitate thorough legal and technical assessments of data flows and recipient countries' data protection postures. Data localization may be preferred where possible.
- No "Legitimate Interest" for Sensitive Data: This eliminates a common GDPR lawful basis for sensitive data, requiring organizations to primarily rely on explicit consent, which has direct implications for data collection and processing workflows.
How to Ensure Saudi Arabia Personal Data Protection Law (PDPL) Compliance?
Achieving and maintaining PDPL compliance is an ongoing journey that requires deep understanding, technical expertise, and continuous effort:
- Appoint a DPO and Register with SDAIA (if applicable):
- Technical Detail: Designate an individual or team as the Data Protection Officer (DPO) (or equivalent internal privacy lead). Ensure the DPO has sufficient knowledge of IT systems, data processing activities, and cybersecurity. Register the organization with the National Controllers Register on SDAIA's platform if required (e.g., for public entities or those whose main activity is personal data processing).
- Conduct a Comprehensive Data Inventory and Mapping:
- Technical Detail: Identify and document all personal data collected, processed, stored, and shared within your organization (including sensitive personal data). Map data flows, data retention periods, legal bases for processing, and who has access. This forms the foundation for all other compliance efforts.
- Tooling: Data discovery and classification tools, data mapping software, privacy management platforms.
- Implement Robust Consent Management:
- Technical Detail: Deploy a user-friendly, auditable CMP on all relevant digital interfaces (websites, mobile apps) to collect explicit, granular consent. Ensure consent records are timestamped, easily retrievable, and that withdrawal mechanisms are prominently displayed and simple to use.
- Tooling: OneTrust, Cookiebot, TrustArc, or custom-built CMPs.
- Develop and Publish Clear Privacy Policies:
- Technical Detail: Draft comprehensive and accessible privacy notices/policies for all data collection points, detailing all information required by the PDPL. Ensure these policies are regularly reviewed and updated to reflect changes in data processing activities.
- Strengthen Security Safeguards (Technical Controls): This is paramount for PDPL compliance.
- Technical Detail:
- Encryption: Implement strong encryption for all personal data, both at rest (e.g., database encryption, full disk encryption, encrypted cloud storage buckets) and in transit (e.g., TLS 1.2+ for all web services, secure VPNs, encrypted APIs). Employ secure key management practices (KMS, HSMs).
- Access Management: Deploy robust IAM solutions. Mandate MFA for all users, particularly for administrative access and remote connections. Implement RBAC and PoLP. Use PAM tools to manage and monitor privileged accounts.67 Regularly review and revoke unnecessary access.
- Network Security: Deploy and configure firewalls (network and application layer), IDS/IPS, and WAFs. Implement network segmentation to isolate sensitive data. Protect against DDoS attacks.
- Application Security: Integrate security into the SSDLC. Conduct regular SAST and DAST on all applications processing personal data. Perform penetration testing prior to deployment and after significant changes.
- Vulnerability & Patch Management: Implement a continuous vulnerability management program. Ensure timely patching of all operating systems, applications, and network devices.
- Security Monitoring & Logging: Deploy a SIEM system to centralize logs, detect anomalies, and alert on potential security incidents in real-time. Integrate with EDR/XDR solutions.
- Data Loss Prevention (DLP): Implement DLP solutions to prevent unauthorized egress of personal data.
- Secure Backups & DR: Establish and regularly test secure, encrypted backup and disaster recovery procedures.
- Tooling: Extensive range of cybersecurity products as listed in the "Key Aspects" section.
- Technical Detail:
- Establish a Robust Data Subject Rights (DSR) Fulfillment Process:
- Technical Detail: Develop a secure portal or automated system for data subjects to submit DSR requests. Implement workflows to efficiently locate, retrieve, rectify, delete, or port personal data in response to verified requests within the 30-day timeframe.
- Tooling: DSAR automation platforms, data governance tools.
- Formulate a Data Breach Response Plan:
- Technical Detail: Create a comprehensive incident response plan specifically for personal data breaches. This plan must include clear procedures for detection (e.g., via SIEM alerts), assessment, containment, eradication, recovery, and post-incident review. Crucially, it must detail the notification process for SDAIA (within 72 hours) and affected data subjects (immediately if high risk), including the information required in such notifications.
- Tooling: Incident response platforms.
- Manage Third-Party Risks:
- Technical Detail: Conduct thorough cybersecurity due diligence on all third-party vendors and service providers that process personal data on your behalf. Implement robust data processing agreements (DPAs) that contractually obligate vendors to adhere to PDPL requirements, including security safeguards and audit rights.
- Tooling Vendor risk management platforms.
- Conduct DPIAs and TIAs:
- Technical Detail: Systematically perform DPIAs for high-risk processing activities. For cross-border data transfers, conduct comprehensive TIAs, assessing the destination country's data protection adequacy and implementing appropriate transfer mechanisms (e.g., SDAIA-approved clauses) and explicit consent.
- Tooling: DPIA/TIA templates, GRC platforms.
- Provide Employee Training and Awareness:
- Technical Detail: Implement mandatory, ongoing training for all employees on PDPL principles, data handling policies, security best practices, and incident reporting procedures. Phishing simulations and security awareness campaigns are essential.
- Tooling: LMS platforms with privacy and cybersecurity modules.
- Continuous Monitoring and Auditing:
- Technical Detail: PDPL compliance is an ongoing process. Implement continuous monitoring of security controls, conduct regular internal and external audits (including penetration testing and compliance assessments), and utilize findings to continuously improve your data protection posture.
- Tooling: GRC solutions for compliance tracking, audit management software.
Consequences of Non-Compliance with Saudi Arabia Personal Data Protection Law (PDPL)
The penalties for non-compliance with the PDPL are substantial and can have severe repercussions for organizations:
- Administrative Fines:
- General violations: Up to SAR 5 million (approximately USD 1.3 million)
- Repeat offenses: The fine amount can be doubled.
- Imprisonment: For serious offenses, particularly the unauthorized disclosure or publication of sensitive personal data with the intent to cause harm or achieve personal gain, individuals can face imprisonment for up to two years.
- Confiscation of Funds: Funds obtained as a result of a violation may be confiscated.
- Reputational Damage: Data breaches and public enforcement actions will severely damage an organization's brand, erode customer trust, and lead to negative media coverage and a significant loss of business.
- Civil Claims for Compensation: Affected data subjects have the right to seek compensation for damages incurred due to PDPL violations.
- Corrective Actions and Operational Directives: SDAIA can issue directives requiring organizations to implement specific corrective measures or cease certain processing activities. Failure to comply can lead to further penalties.
- Increased Scrutiny and Audit Burden: Non-compliant entities are likely to face more frequent and intensive audits from SDAIA, consuming significant internal resources and disrupting normal business operations.
How ImmuniWeb Helps Comply with Saudi Arabia Personal Data Protection Law (PDPL)
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides robust technical capabilities that directly support organizations in meeting the stringent "Security Safeguards" (technical and organizational measures) and "Data Breach Notification" requirements of the Saudi Arabia PDPL, while also contributing to data inventory, risk management, and accountability.
Here's how ImmuniWeb assists with technical PDPL compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By integrating ImmuniWeb into their security and privacy programs, organizations can significantly enhance their technical capabilities to meet the demanding requirements of the Saudi Arabian PDPL, thereby protecting personal data, reducing regulatory risks, and building trust in the digital economy.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
