Saudi Arabian Monetary Authority (SAMA) Cyber Security Framework (1.0) Compliance
The Saudi Arabian Monetary Authority (SAMA) Cyber Security Framework (1.0) establishes mandatory cybersecurity
controls for financial institutions in Saudi Arabia, covering risk management, data protection, incident
response, and governance to mitigate cyber threats and ensure regulatory compliance.

In an increasingly interconnected world, robust cybersecurity is not just a technological requirement but a strategic national imperative. The Kingdom of Saudi Arabia, recognizing the critical role of its financial sector in economic stability, established the Saudi Arabian Monetary Authority (SAMA) Cyber Security Framework (CSF) Version 1.0. Issued on May 1, 2017, and overseen by the Saudi Central Bank (formerly SAMA), this framework provides a comprehensive and mandatory set of controls and guidelines to safeguard the financial institutions within the Kingdom from evolving cyber threats.
The SAMA CSF aims to foster a resilient, secure, and trusted financial ecosystem, aligning with Saudi Vision 2030's ambitious digital transformation goals. For all entities operating under SAMA's purview, strict adherence to this framework is paramount, demanding sophisticated technical implementation and continuous oversight.
This article provides an in-depth exploration of the SAMA CSF 1.0, highlighting its technical requirements and outlining practical strategies for achieving and maintaining compliance.
Overview of Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
The SAMA Cyber Security Framework (CSF) Version 1.0 is a risk-based and principle-based regulatory framework specifically designed for the financial sector in Saudi Arabia. Its core objectives are to:
- Enhance Cybersecurity Resilience: Establish strong defenses against evolving cyber threats to ensure business continuity.
- Protect Financial Stability: Safeguard critical banking and financial systems from cyber risks.
- Promote Consistency: Provide a unified set of cybersecurity standards across the financial sector.
- Facilitate Compliance: Help organizations meet both national and international regulatory requirements.
- Strengthen Trust: Build confidence among consumers, investors, and stakeholders in the financial system's ability to protect sensitive data.
The framework is structured around five key domains:
- Cyber Security Governance: Focuses on establishing a clear governance structure, roles, responsibilities, and strategic alignment of cybersecurity with business objectives.
- Cyber Security Risk Management: Outlines processes for identifying, assessing, mitigating, and monitoring cybersecurity risks.
- Cyber Security Controls: Defines the technical and procedural measures to protect information assets. This is the most technically intensive domain.
- Cyber Security Resilience: Emphasizes the ability of organizations to withstand, respond to, and recover from cyber incidents.
- Third-Party Cyber Security: Addresses the cybersecurity risks associated with third-party vendors and service providers.
The SAMA CSF is designed to be adaptable, integrating best practices from globally recognized frameworks such as NIST CSF, ISO 27001, and PCI DSS, while tailoring them to the specific context of the Saudi financial sector.13 It also mandates a self-assessment and periodic reporting mechanism to SAMA to demonstrate compliance and maturity levels.

Key Aspects of Saudi Arabian Monetary Authority Cyber Security Framework (1.0) Compliance
Compliance with the SAMA CSF 1.0 involves the meticulous implementation of a comprehensive set of controls across its five domains. The "Cyber Security Controls" domain is particularly rich in technical requirements:
- Cyber Security Governance:
- Technical Detail: Establish a dedicated cybersecurity committee with defined responsibilities. Ensure the Chief Information Security Officer (CISO) possesses adequate qualifications and authority, with direct reporting lines to senior management or the board. Align the cybersecurity strategy with the organization's business objectives and overall risk appetite.
- Cyber Security Risk Management:
- Technical Detail: Implement a formal, continuous risk management process including regular risk assessments to identify, analyze, and prioritize cybersecurity risks to information assets (digital, physical, applications, networks, etc.). Maintain an updated risk register. Define and apply appropriate risk treatment plans, which often involve implementing specific technical controls. This requires tools for vulnerability scanning, penetration testing, and risk assessment platforms.
- Cyber Security Controls: This domain is the technical core and includes numerous sub-controls covering:
- Asset Management:
- Technical Detail: Maintain a comprehensive inventory of all information assets, including hardware, software, network devices, and data, with clear ownership and classification. Implement secure disposal procedures for assets containing sensitive information.
- Tooling: Asset discovery tools, CMDB (Configuration Management Database), data classification tools.
- Access Control:
- Technical Detail: Implement robust Identity and Access Management (IAM) systems. Enforce Multi-Factor Authentication (MFA) for all users, especially privileged and remote access. Implement Role-Based Access Control (RBAC) and the principle of least privilege (PoLP). Deploy Privileged Access Management (PAM) solutions to secure and monitor administrative accounts. Implement strict password policies and regular reviews of access rights.
- Tooling: IAM platforms, MFA solutions, PAM tools, directory services.
- Cryptography:
- Technical Detail: Mandate strong encryption algorithms (e.g., AES-256) for data at rest (database encryption, disk encryption) and data in transit (e.g., TLS 1.2+ for web communication, VPNs for internal and external connections). Securely manage encryption keys using Hardware Security Modules (HSMs) or robust Key Management Systems (KMS).
- Tooling: Encryption software, HSMs, KMS.
- Communication Security:
- Technical Detail: Implement network segmentation, firewalls (including Web Application Firewalls - WAFs), Intrusion Detection Systems (IDS), and Intrusion Prevention Systems (IPS). Secure network configurations and protocols. Implement secure remote access solutions (e.g., VPNs with strong encryption and MFA). Protect against Denial of Service (DoS) attacks.
- Tooling: Network security appliances, WAFs, IDS/IPS, DDoS mitigation solutions, network vulnerability scanners.
- System Acquisition, Development, and Maintenance:
- Technical Detail: Integrate security into the Software Development Lifecycle (SSDLC). Conduct security requirements engineering. Perform static (SAST) and dynamic (DAST) application security testing, and penetration testing for all applications. Implement secure coding guidelines. Ensure robust patch management and vulnerability management processes for all systems and applications.
- Tooling: SAST/DAST tools, vulnerability management platforms, patch management systems.
- Operations Security:
- Technical Detail: Implement comprehensive logging and monitoring of all security-relevant events across IT infrastructure. Deploy Security Information and Event Management (SIEM) systems for centralized log collection, correlation, and real-time alerting. Conduct regular vulnerability assessments and penetration tests. Implement robust data backup and recovery procedures. Ensure up-to-date anti-malware and Endpoint Detection and Response (EDR) solutions.
- Tooling: SIEM, EDR, anti-malware solutions, backup and recovery software.
- Physical Security:
- Technical Detail: Implement physical access controls (e.g., biometric, access cards), CCTV monitoring, environmental controls (temperature, humidity, fire suppression) for data centers and critical infrastructure.
- Asset Management:
- Cyber Security Resilience:
- Technical Detail: Develop and regularly test comprehensive incident response plans (IRPs) that cover detection, analysis, containment, eradication, recovery, and post-incident review. Establish Business Continuity Management (BCM) and Disaster Recovery (DR) plans with defined Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO) for critical systems.
- Tooling: Incident response platforms, BCDR testing tools.
- Third-Party Cyber Security:
- Technical Detail: Conduct thorough cybersecurity risk assessments of all third-party vendors and service providers, especially those with access to sensitive data or critical systems. Implement contractual agreements (e.g., data processing agreements) that mandate adherence to SAMA CSF controls. Regularly monitor third-party compliance.
- Tooling: Vendor risk management platforms.
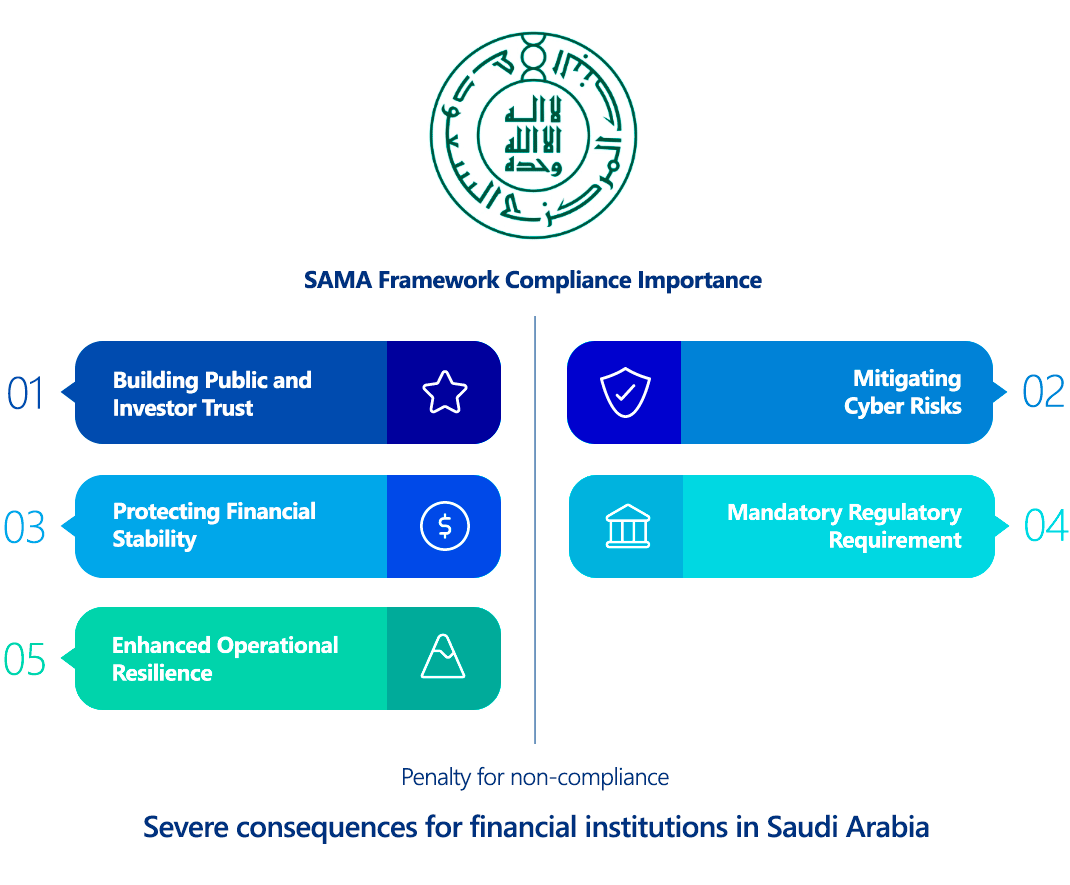
Why Is Saudi Arabian Monetary Authority Cyber Security Framework (1.0) Compliance Important?
Compliance with the SAMA CSF 1.0 is not merely a regulatory obligation; it is a fundamental pillar for the stability and competitiveness of Saudi Arabia's financial sector:
- Mandatory Regulatory Requirement: It's a non-negotiable directive from the central bank. Non-compliance can lead to severe penalties and operational disruptions.
- Protecting Financial Stability: The framework directly addresses the unique and elevated cyber threats faced by financial institutions. By establishing a baseline of robust security, it safeguards the integrity of financial transactions, customer data, and the overall stability of the Saudi economy.
- Mitigating Cyber Risks: The SAMA CSF provides a structured and systematic approach to identifying, assessing, and mitigating a wide array of cyber risks, from sophisticated nation-state attacks to common malware and insider threats. This proactive stance reduces the likelihood and impact of successful cyberattacks.
- Building Public and Investor Trust: Adherence to a strong cybersecurity framework demonstrates a commitment to protecting sensitive information and maintaining operational resilience. This builds confidence among customers, investors, and international partners, fostering a trusted financial environment.
- Aligning with National Vision 2030: The framework supports Saudi Vision 2030's digital transformation goals by ensuring that technological advancements in the financial sector are underpinned by robust security, encouraging innovation without compromising safety.
- Enhanced Operational Resilience: The focus on cybersecurity resilience, incident management, and business continuity ensures that financial institutions can withstand and rapidly recover from cyber incidents, minimizing downtime and financial losses.
- Strengthening Saudi Arabia's Global Financial Standing: By adopting and enforcing a comprehensive cybersecurity framework, Saudi Arabia reinforces its position as a secure and reliable hub for financial services on the global stage.
Who Needs to Comply with Saudi Arabian Monetary Authority Cyber Security Framework (1.0)?
The SAMA CSF 1.0 has a clearly defined scope of applicability. It is mandatory for all SAMA-regulated entities, which primarily include:
- All Banks operating in Saudi Arabia: This includes both local and international banks.
- All Insurance and Reinsurance Companies operating in Saudi Arabia.
- All Financing Companies in Saudi Arabia.
- Credit Bureaus in Saudi Arabia.
- Financial Market Infrastructure (FMI) entities.
Furthermore, the framework's Third-Party Cyber Security domain extends its reach to:
- Third-party service providers that interact with or provide services to SAMA-regulated entities, especially those that process, store, or transmit sensitive data or manage critical systems on behalf of these entities (e.g., cloud computing providers, IT service outsourcing companies, vendors, suppliers). These third parties are contractually obligated to adhere to relevant aspects of the SAMA CSF.
Saudi Arabian Monetary Authority Cyber Security Framework (1.0) vs GDPR Comparison
While both the SAMA CSF 1.0 and GDPR aim to enhance security and protect data, their primary focus, scope, and approach differ significantly:
- SAMA CSF 1.0: A cybersecurity framework focused on the overall security and resilience of financial institutions and their information assets (including but not limited to personal data). It's a security standard.
- GDPR: A data protection regulation focused on the privacy rights of individuals and the protection of their "personal data." It's a privacy law.
Here's a comparison of their key aspects:
| Feature | SAMA CSF 1.0 | GDPR (General Data Protection Regulation) |
|---|---|---|
| Primary Objective | To enhance cybersecurity resilience and manage cyber risks for financial stability and national security. | To protect the personal data and privacy rights of individuals (data subjects). |
| Scope of Data | All information assets (digital, physical, applications, networks, systems), with emphasis on critical and sensitive data. | "Personal data" (identifiable information about a natural person) and "special categories of personal data." |
| Applicability | Mandatory for SAMA-regulated financial entities and their relevant third-party service providers within KSA. | Broad extraterritorial scope; applies to any entity processing EU residents' personal data, regardless of location. |
| Control Type | Highly prescriptive with detailed technical and management controls across 5 domains and 188 sub-controls. | Principles-based, requiring "appropriate technical and organizational measures" for security, with less specific mandates on individual controls. |
| Governance | Mandates specific governance structures (e.g., CISO role, cybersecurity committee). | Requires a DPO (under specific conditions) and emphasizes accountability, but less prescriptive on overall corporate cybersecurity governance structure. |
| Risk Management | Central to the framework; requires formal risk assessments and continuous monitoring. | Requires risk assessments for data processing activities, and DPIAs for high-risk processing. |
| Incident Response | Detailed requirements for incident management, including detection, containment, and recovery. | Mandatory data breach notification within 72 hours to supervisory authority and, if high risk, to affected individuals. |
| Data Subject Rights | Focus is on protecting the data itself, not explicitly on data subject rights beyond general security and availability. | Extensive data subject rights (access, rectification, erasure, portability, objection, etc.). |
| Cross-Border Transfers | Not a primary focus, but general security principles imply secure handling of data regardless of location. Specific data residency rules may exist outside the CSF. | Strict rules for international transfers of personal data (e.g., adequacy decisions, SCCs, BCRs, consent). |
| Regulatory Body | Saudi Central Bank (SAMA). | Independent Supervisory Authorities in each EU member state, coordinated by the European Data Protection Board (EDPB). |
| Penalties | Administrative actions, operational suspension, potential legal/criminal liability, reputational damage, license amendments/revocation (specific fines often not publicly detailed for CSF non-compliance directly, but severe). | Significant financial penalties (up to €20 million or 4% of global annual turnover). |
Technical Implications of the Comparison:
Organizations aiming for SAMA CSF compliance will find themselves implementing many of the "appropriate technical and organizational measures" that GDPR broadly requires for personal data protection. However, SAMA CSF's focus on operational resilience for financial services will likely necessitate more granular and specific controls around:
- OT/ICS Security: For financial infrastructure with operational technology components.
- Specific Network & Infrastructure Hardening: Beyond general best practices, with prescribed security architectures.
- More Rigorous Testing Cycles: Including more frequent and comprehensive penetration testing and red teaming.
- Business Continuity and Disaster Recovery: Highly detailed RPO/RTO targets and robust testing schedules are crucial.
- Third-Party Oversight: More stringent requirements for auditing and contractually binding third parties to security standards.
While GDPR focuses on the "what" (protecting personal data and rights), SAMA CSF focuses more on the "how" (implementing a robust security program across all information assets within a critical sector). Compliance with both requires a layered, integrated, and well-documented security strategy.
How to Ensure Saudi Arabian Monetary Authority Cyber Security Framework (1.0) Compliance?
Achieving and maintaining SAMA CSF 1.0 compliance is a rigorous, ongoing endeavor that requires significant technical investment and organizational commitment:
- Conduct a Comprehensive Gap Analysis and Risk Assessment:
- Technical Detail: Compare your current cybersecurity posture against each of the 188 controls in the SAMA CSF. Identify all critical information assets and conduct a thorough risk assessment to determine the applicability of "risk-dependent" controls. Document current security controls, gaps, and an action plan for remediation.
- Establish Robust Cyber Security Governance:
- Technical Detail: Define and document a clear cybersecurity governance structure, roles, and responsibilities, ensuring CISO alignment with board-level oversight. Develop a comprehensive cybersecurity strategy aligned with business objectives. Implement policies and procedures covering all SAMA CSF domains.
- Implement Strong Cyber Security Controls (Technical Implementation): This is the most demanding phase.
- Access Control:
- Technical Detail: Implement enterprise-wide IAM solutions with mandatory MFA for all systems, especially cloud access, administrative interfaces, and remote access. Deploy PAM for all privileged accounts. Enforce least privilege and regular access reviews.
- Cryptography:
- Technical Detail: Mandate end-to-end encryption for all sensitive data in transit (TLS 1.3 for web, IPsec VPNs, encrypted messaging). Implement robust encryption for data at rest (database encryption, full disk encryption, encrypted backups). Utilize HSMs or KMS for secure key generation and management.
- Communication Security:
- Technical Detail: Implement multi-layered firewalls (network, host, WAF). Deploy IDS/IPS on network perimeters and critical internal segments. Implement robust DDoS mitigation. Utilize secure network architecture principles (e.g., zero trust, micro-segmentation).
- System Acquisition, Development, and Maintenance:
- Technical Detail: Embed security into your DevSecOps pipeline. Implement SAST and DAST early and continuously. Conduct regular penetration tests before deploying new applications or significant changes. Ensure automated patch management and vulnerability scanning across all systems.
- Operations Security:
- Technical Detail: Deploy a comprehensive SIEM system for centralized logging, real-time threat detection, and correlation. Integrate with EDR/XDR solutions for endpoint visibility and response. Implement advanced anti-malware solutions. Automate security tasks where possible.
- Data Backup and Recovery:
- Technical Detail: Implement redundant, encrypted backups with offsite storage. Regularly test backup integrity and recovery procedures to meet defined RPO/RTOs.
- Access Control:
- Develop Robust Incident Response and Business Continuity Plans:
- Technical Detail: Create and regularly test a detailed Incident Response Plan (IRP) that outlines clear roles, responsibilities, communication protocols, and technical steps for detection, containment, eradication, and recovery. Develop and test Business Continuity Plans (BCP) and Disaster Recovery Plans (DRP) to ensure continuous operation of critical financial services.
- Implement Strong Third-Party Risk Management:
- Technical Detail: Establish a process for cybersecurity due diligence of all third-party vendors. Ensure robust contractual agreements that mandate compliance with relevant SAMA CSF controls. Implement continuous monitoring of third-party security postures.
- Conduct Regular Awareness and Training:
- Technical Detail: Implement mandatory, role-based cybersecurity awareness training for all employees, including senior management. Include phishing simulations and social engineering awareness.
- Continuous Monitoring, Audit, and Improvement:
- Technical Detail: Implement mechanisms for continuous monitoring of security controls' effectiveness. Conduct regular internal and external audits, including penetration testing and red teaming exercises, to identify new vulnerabilities and assess the maturity of your cybersecurity posture against the SAMA CSF's six maturity levels. Submit required self-assessments and reports to SAMA.
Consequences of Non-Compliance with Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
Non-compliance with the SAMA CSF 1.0 can lead to severe consequences for financial institutions in Saudi Arabia:
- Regulatory Sanctions and Directives: SAMA (now the Saudi Central Bank) has the authority to impose various regulatory actions, including formal warnings, directives to implement corrective action plans, and increased scrutiny.
- Operational Restrictions or Suspension: In severe cases of non-compliance, SAMA can impose restrictions on an institution's operations, suspend certain business activities, or even, in extreme circumstances, revoke its operating license, leading to complete cessation of business.
- Significant Financial Penalties: While specific fine amounts for CSF non-compliance may not be as publicly detailed as in some other regulations, SAMA has broad powers to impose penalties that can be substantial and proportionate to the severity and impact of the non-compliance.
- Reputational Damage and Loss of Trust: Non-compliance, especially if it leads to a cyber incident or data breach, can severely tarnish an institution's reputation, erode customer trust, and lead to a significant loss of market share, impacting investor confidence and business relationships.
- Legal and Criminal Liabilities: Depending on the nature and severity of the security lapse, and if it results in fraud, data theft, or other cybercrimes, individuals (including senior management) and the institution itself could face legal proceedings, civil lawsuits, and even criminal prosecution under Saudi Arabian laws.
- Increased Audit Burden: Non-compliant entities are likely to face more frequent and intensive audits from SAMA, consuming significant internal resources and diverting focus from core business activities.
How ImmuniWeb Helps Comply with Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform offers crucial technical capabilities that directly support organizations in meeting the stringent requirements of the SAMA CSF 1.0, particularly within the Cyber Security Controls and Cyber Security Resilience domains, as well as underpinning the Risk Management and Third-Party Cyber Security aspects.
Here's how ImmuniWeb assists with technical SAMA CSF compliance:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By leveraging ImmuniWeb's capabilities, financial institutions in Saudi Arabia can establish a robust technical foundation for SAMA CSF 1.0 compliance. This proactive, intelligence-driven approach helps them systematically identify and mitigate cybersecurity risks, streamline their incident response, enhance their overall security posture, and confidently demonstrate their adherence to the Saudi Central Bank's stringent cybersecurity requirements.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
