NIST SP 800-53 (Rev.5) Compliance
NIST SP 800-53 (Rev. 5) provides a comprehensive catalog of security and privacy controls for federal
information systems, helping organizations manage risks to data confidentiality, integrity, and
availability while addressing evolving threats and regulatory requirements.

In an increasingly complex and interconnected digital landscape, protecting information systems and the data they hold is paramount. The National Institute of Standards and Technology (NIST) Special Publication (SP) 800-53, Revision 5, serves as a cornerstone for robust cybersecurity and privacy practices, particularly for U.S. federal agencies and their contractors.
This comprehensive framework provides a catalog of security and privacy controls designed to mitigate a diverse set of threats and risks, from malicious attacks to human error and natural disasters.
Overview of NIST SP 800-53 (Rev. 5)
NIST SP 800-53 (Rev. 5), titled "Security and Privacy Controls for Information Systems and Organizations," represents a significant evolution in cybersecurity guidance. It moves beyond a compliance-centric approach to emphasize outcome-based security, focusing on achieving desired security and privacy objectives rather than merely checking off boxes.
Key technical enhancements in Rev. 5 include:
- Consolidated Control Catalog: Security and privacy controls are now fully integrated into a single, unified catalog. This streamlines implementation and management, recognizing the inherent overlap between security and privacy in protecting information.
- Emphasis on Supply Chain Risk Management (SCRM): A new control family dedicated to SCRM (SR) has been introduced. This addresses the growing recognition that supply chain vulnerabilities pose significant risks to organizational security, extending controls to assess and manage risks associated with third-party components, products, and services.
- Outcome-Based Control Statements: The language of control statements has been revised to focus on the desired security and privacy outcomes, making them more adaptable to various organizational roles, technologies, and environments. This shifts the emphasis from who is responsible to what needs to be achieved.
- Modernization of Controls: Controls have been updated to reflect the latest threat intelligence, evolving technologies (such as cloud and mobile), and emerging best practices. This ensures the framework remains relevant and effective in the face of a rapidly changing cyber threat landscape.
- Improved Content Relationships: Clarified relationships between requirements, measures, and security and privacy controls enhance understanding and facilitate enterprise-wide implementation within system engineering processes.
- Increased Flexibility and Tailoring: While providing comprehensive guidance, Rev. 5 is designed to be flexible. It offers guidance for tailoring controls to specific organizational needs, mission requirements, and risk tolerances, supported by a separate publication, NIST SP 800-53B, which houses control baselines for low, moderate, and high-impact systems.
- Integration of Privacy Controls: Privacy controls, previously in an appendix, are now embedded throughout the main catalog, highlighting their foundational role in information protection.
The controls are organized into 20 control families, each addressing a specific area of security and privacy, such as:
- AC - Access Control: Managing who can access what resources.
- AT - Awareness and Training: Ensuring personnel understand their security responsibilities.
- AU - Audit and Accountability: Tracking and reviewing system activities.
- CA - Assessment, Authorization, and Monitoring: Evaluating and continuously overseeing security controls.
- CM - Configuration Management: Securely managing system configurations.
- CP - Contingency Planning: Preparing for and recovering from security incidents.
- IA - Identification and Authentication: Verifying user identities.
- IR - Incident Response: Planning for and reacting to security incidents.
- MA - Maintenance: Securing system maintenance activities.
- MP - Media Protection: Protecting information on various media.
- PE - Physical and Environmental Protection: Securing physical facilities.
- PL - Planning: Developing security plans.
- PM - Program Management: Managing organization-wide security programs.
- PS - Personnel Security: Vetting and managing staff security.
- RA - Risk Assessment: Identifying and evaluating risks.
- SA - System and Services Acquisition: Securing procured systems and services.
- SC - System and Communications Protection: Protecting data in transit and at rest.
- SI - System and Information Integrity: Ensuring the accuracy and completeness of information.
- SR - Supply Chain Risk Management: Managing risks associated with the supply chain.
- PT - Privacy: Dedicated controls for privacy considerations (newly integrated).

Key Aspects of NIST SP 800-53 (Rev. 5) Compliance
Achieving compliance with NIST SP 800-53 (Rev. 5) involves a structured and continuous effort. Key aspects include:
- Risk-Based Approach: Compliance is not a static checklist. Organizations must conduct thorough risk assessments to identify and prioritize risks based on their likelihood and potential impact. This guides the selection and tailoring of controls.
- System Security Plans (SSPs): Developing comprehensive SSPs that document how an organization's systems meet the applicable controls.
- Continuous Monitoring: Implementing ongoing monitoring of security controls and system activities to detect and respond to incidents in real-time. This includes regular reviews and periodic audits to ensure continued effectiveness.
- Collaboration and Buy-in: Securing commitment from senior leadership and fostering interdepartmental collaboration are crucial for successful implementation and cultural adoption of security practices.
- Documentation: Maintaining detailed documentation of all security policies, procedures, and control implementations is essential for demonstrating compliance and facilitating audits.
- Tailoring and Baselines: Utilizing the provided control baselines (low, moderate, high impact) and tailoring guidance to select controls appropriate for the specific system's impact level and the organization's unique risk environment.
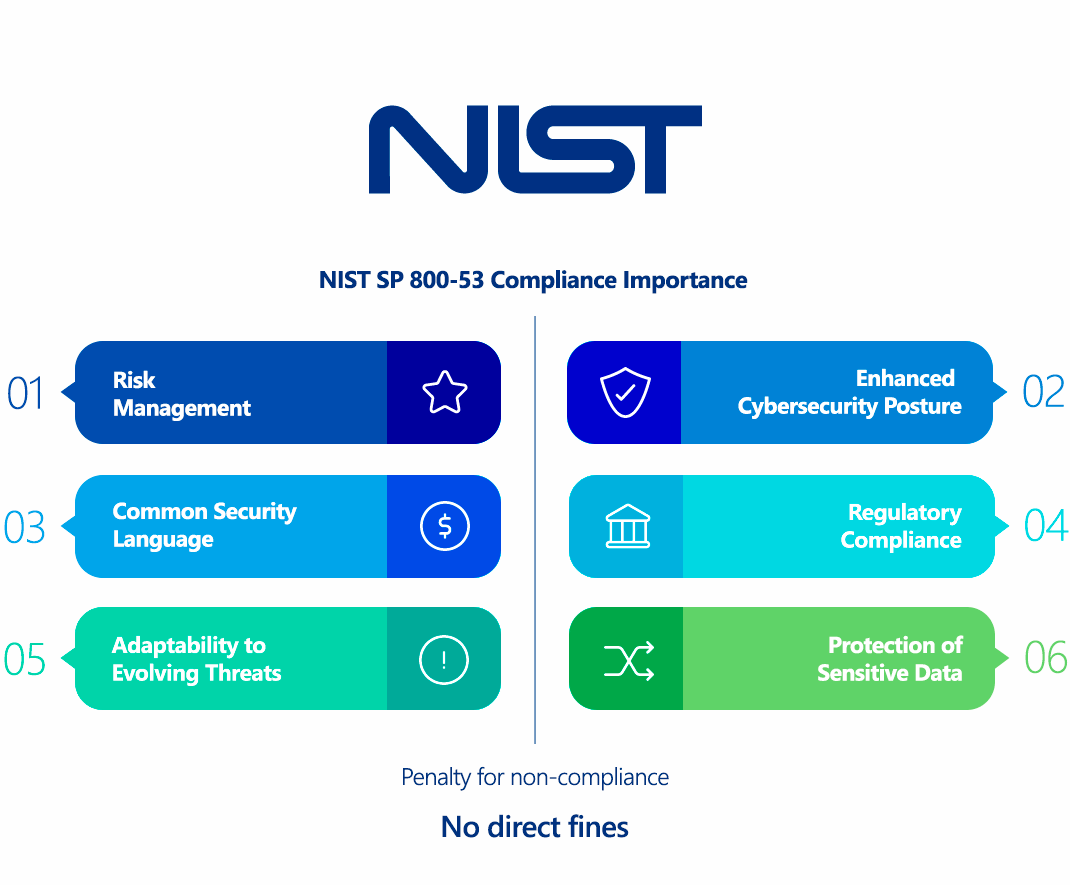
Why Is NIST SP 800-53 (Rev. 5) Compliance Important?
NIST SP 800-53 (Rev. 5) compliance offers numerous benefits, extending beyond mere regulatory adherence:
- Enhanced Security Posture: The framework provides a comprehensive and systematic approach to cybersecurity, helping organizations build more resilient and secure information systems capable of withstanding diverse threats.
- Risk Management: It strengthens an organization's risk management processes by providing a robust catalog of controls to address identified vulnerabilities and reduce the likelihood and impact of security incidents.
- Regulatory Compliance: For federal agencies, compliance is mandated by the Federal Information Security Modernization Act (FISMA). For contractors, it's often a contractual requirement. Adherence also assists in meeting other regulations like HIPAA, SOX, and increasingly, GDPR.
- Protection of Sensitive Data: The controls are designed to safeguard various types of information, including sensitive government data and Personally Identifiable Information (PII).
- Common Security Language: It provides a standardized language for discussing, implementing, and evaluating security controls, improving communication among security teams, executives, and external partners.
- Adaptability to Evolving Threats: Regular revisions ensure the controls remain current with emerging risks, technologies, and legal requirements, ensuring continuous effectiveness.
Who Needs to Comply with NIST SP 800-53 (Rev. 5)?
- U.S. Federal Government Agencies: Compliance is mandatory for all federal agencies to protect their information systems and data, as stipulated by FISMA.
- Government Contractors: Organizations that contract with the U.S. federal government and handle federal information or operate federal information systems are often contractually required to comply with NIST SP 800-53 (Rev. 5).
- Private Organizations (Voluntary Adoption): While not legally mandated for most private-sector entities, NIST SP 800-53 is widely regarded as a leading cybersecurity framework. Many private organizations voluntarily adopt its guidelines as a benchmark to enhance their security posture, manage risk, and demonstrate a commitment to robust cybersecurity, especially if they handle sensitive data or aim to do business with the government.
NIST SP 800-53 (Rev. 5) vs. GDPR Comparison
While both NIST SP 800-53 (Rev. 5) and the General Data Protection Regulation (GDPR) aim to protect data, they have distinct focuses and scopes:
| Feature | NIST SP 800-53 (Rev. 5) | GDPR |
|---|---|---|
| Primary Focus | Security and privacy controls for information systems and organizations. Focuses on the confidentiality, integrity, and availability (CIA triad) of information. | Protection of personal data and privacy rights of EU citizens. Focuses on how personal data is collected, processed, stored, and used. |
| Scope | Primarily U.S. federal information systems and organizations. Applicable to all types of information. | Any organization, regardless of location, that processes the personal data of individuals residing in the European Union. |
| Nature | A comprehensive framework and catalog of controls that are flexible and customizable. | A regulation with specific legal requirements and obligations. |
| Data Breach Reporting | Provides controls for incident response, but no specific timeframe for breach notification. | Mandates reporting data breaches to supervisory authorities within 72 hours of becoming aware, and to affected individuals without undue delay if there's a high risk to their rights and freedoms. |
| Consent | Does not explicitly require consent for data processing. | Requires explicit consent for processing personal data, especially for sensitive data. |
| Individual Rights | Addresses privacy controls, but GDPR offers more detailed rights for data subjects (e.g., right to access, rectification, erasure, portability). | Grants extensive rights to data subjects regarding their personal data. |
| Penalties | Consequences typically involve loss of contracts, Authority to Operate (ATO) revocation, and reputational damage for non-compliance. | Significant fines (up to 4% of annual global turnover or €20 million, whichever is higher) for non-compliance. |
Despite their differences, they are complementary. Organizations subject to GDPR can leverage NIST SP 800-53 controls to establish the robust technical and organizational security measures required by GDPR, particularly in areas like access control, encryption, incident response, and data breach preparation.
How to Ensure NIST SP 800-53 (Rev. 5) Compliance?
Ensuring compliance with NIST SP 800-53 (Rev. 5) is an ongoing process involving several key steps:
- Understand the Framework: Thoroughly familiarize yourself with the 20 control families and the individual controls within each.
- Conduct a Gap Analysis and Risk Assessment:
- Assess your current security posture against the NIST SP 800-53 requirements.
- Identify gaps and prioritize them based on risk likelihood and impact.
- Determine the appropriate security control baseline (low, moderate, or high) for your systems.
- Develop a System Security Plan (SSP): Document how each control is implemented and how it addresses identified risks. This plan should be a living document, updated as your systems and environment change.
- Implement Controls: Deploy the necessary technical, operational, and management controls. This could involve configuring systems, updating policies, providing training, and establishing monitoring processes. Examples include:
- Implementing strong access controls (least privilege, multi-factor authentication).
- Establishing robust incident response plans.
- Implementing continuous vulnerability scanning and penetration testing.
- Securing network communications and system configurations.
- Developing comprehensive employee security awareness training programs.
- Continuous Monitoring and Assessment:
- Regularly monitor the effectiveness of implemented controls.
- Conduct periodic security assessments and audits to identify weaknesses and ensure ongoing compliance.
- Establish processes for real-time detection and response to security incidents.
- Documentation and Reporting: Maintain meticulous records of all compliance activities, including risk assessments, control implementations, monitoring results, and any incidents or remediation efforts.
- Leverage Automation: Utilize security automation tools for continuous monitoring, configuration management, vulnerability scanning, and incident response to improve efficiency and accuracy.
- Training and Awareness: Regularly train all personnel on their security responsibilities and the organization's security policies and procedures.
Consequences of Non-Compliance with NIST SP 800-53 (Rev. 5)
For organizations mandated to comply, non-compliance with NIST SP 800-53 (Rev. 5) can lead to significant consequences:
- Loss of Authority to Operate (ATO) Federal agencies and their contractors may lose their ATO, which permits them to operate an information system. This can halt operations and lead to significant financial losses.
- Loss of Government Contracts Contractors found non-compliant may face contract termination and be barred from bidding on future government contracts.
- Financial Penalties While NIST itself doesn't impose direct fines, non-compliance with underlying mandates like FISMA can lead to penalties and legal action.
- Reputational Damage Non-compliance and resulting security incidents can severely damage an organization's reputation, eroding trust with stakeholders, clients, and partners.
- Increased Risk of Cyberattacks and Data Breaches The most direct consequence is an increased vulnerability to cyberattacks, leading to data breaches, system outages, and intellectual property theft.
- Legal and Civil Liabilities Data breaches resulting from negligence or non-compliance can lead to costly lawsuits, regulatory investigations, and other legal liabilities.
How ImmuniWeb Helps Comply with NIST SP 800-53 (Rev. 5)?
While the original prompt requested information on how "ImmuniWeb helps comply with NIST SP 800-53 (Rev. 5)", ImmuniWeb primarily focuses on Application Security Testing (AST), including DAST, SAST, IAST, and API security testing, along with Attack Surface Management (ASM) and Dark Web Monitoring. While these services are crucial components of a robust cybersecurity program and can indirectly support various NIST SP 800-53 controls (especially those related to System and Information Integrity (SI), System and Communications Protection (SC), and Incident Response (IR) by identifying vulnerabilities), ImmuniWeb does not offer a direct, holistic compliance platform specifically tailored to manage the entire NIST SP 800-53 framework.
A comprehensive NIST SP 800-53 compliance solution typically involves:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
While ImmuniWeb's offerings significantly strengthen an organization's security posture by identifying and helping remediate application-layer vulnerabilities, their direct contribution to full NIST SP 800-53 compliance would be within the technical implementation of specific security controls, particularly those related to secure development, vulnerability management, and incident detection. For complete compliance management, organizations typically leverage dedicated Governance, Risk, and Compliance (GRC) platforms or engage specialized cybersecurity consulting firms.
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
