New York SHIELD Act Compliance
The New York SHIELD Act requires businesses that collect private data on New York residents to implement
reasonable cybersecurity safeguards and mandates timely breach notifications.

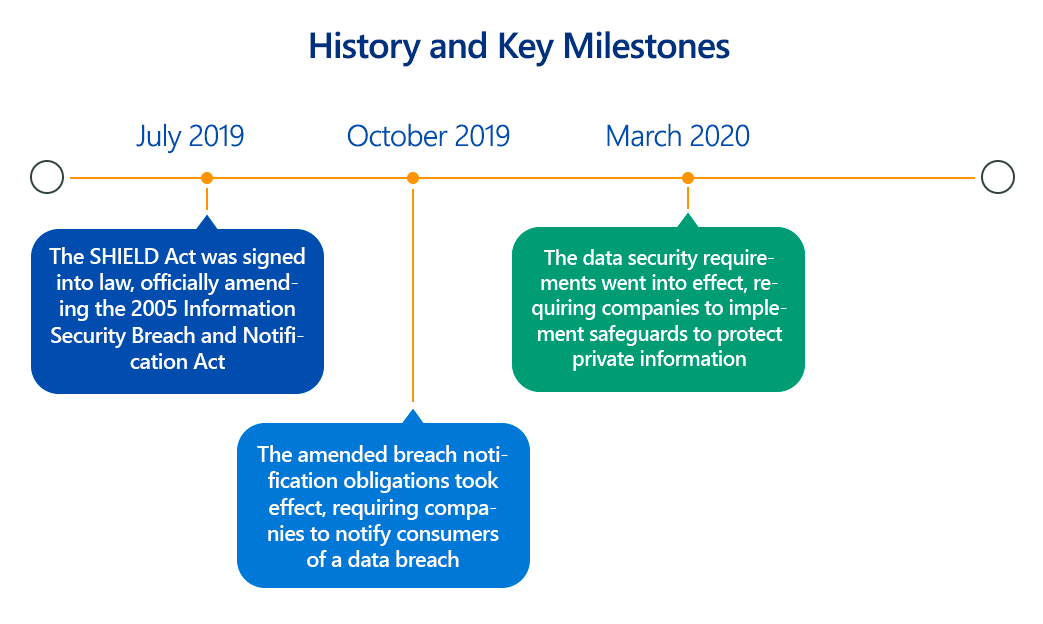
In an increasingly digitized world, data breaches pose a constant threat to personal privacy and financial security. Recognizing the need for stronger protections beyond existing laws, New York State enacted the Stop Hacks and Improve Electronic Data Security Act (SHIELD Act) in 2019.
This landmark legislation significantly expanded the scope of data protected, broadened the definition of a data breach, and most critically, mandated "reasonable security safeguards" for any entity handling the private information of New York residents.
Overview of New York SHIELD Act
The SHIELD Act amends New York's general business law and state technology law, aiming to modernize data security and breach notification requirements. Its core objectives are:
- Expand the definition of "private information": Moving beyond just financial data and Social Security numbers, it now includes a wider array of personal identifiers.
- Broaden the definition of a "data breach": It no longer requires acquisition of data, but now includes unauthorized access to computerized data, aligning with modern cyberattack methodologies where data may be viewed or altered without being explicitly exfiltrated.
- Mandate "reasonable security safeguards": This is a key departure, requiring businesses to proactively implement administrative, technical, and physical safeguards to protect private information.
- Extend extraterritorial reach: The Act applies to any person or business that owns or licenses computerized data that includes the private information of a New York resident, regardless of where the business is located.
Essentially, the SHIELD Act is New York's proactive measure to safeguard its residents from the ever-growing threat of identity theft and data misuse.
Key Aspects of New York SHIELD Act Compliance?
Compliance with the SHIELD Act revolves around two main pillars: strengthened data security and expanded breach notification.
- Enhanced Data Security Requirements (Reasonable Safeguards):
The Act requires "reasonable administrative, technical, and physical safeguards." While it doesn't prescribe specific technologies or methodologies, it provides illustrative examples.
- Administrative Safeguards: These relate to an organization's internal management practices and include:
- Technical Details: Designating one or more employees to coordinate the security program, identifying foreseeable internal and external risks (requiring technical risk assessments), assessing the sufficiency of current safeguards, training and managing employees in security practices (including technical security training), selecting service providers capable of maintaining appropriate safeguards (technical vendor risk assessments), and adjusting the security program in light of business changes or new circumstances.
- Technical Safeguards: These are the most technically demanding and involve:
- Technical Details:
- Assessing risks in network and software design: This requires thorough security architecture reviews, secure coding practices, and static/dynamic application security testing (SAST/DAST) for custom applications.
- Assessing risks in information processing, transmission, and storage: This necessitates robust data mapping, encryption of data at rest and in transit (e.g., AES-256 for storage, TLS 1.2+ for network communication), and secure key management.
- Detecting, preventing, and responding to attacks or system failures: Implementing intrusion detection/prevention systems (IDS/IPS), Security Information and Event Management (SIEM) solutions for centralized logging and anomaly detection, advanced malware protection, and a well-defined incident response plan.
- Regularly testing and monitoring the effectiveness of key controls, systems, and procedures: This specifically calls for ongoing vulnerability scanning and regular penetration testing of all systems that store, process, or transmit private information.
- Technical Details:
- Physical Safeguards: These relate to controlling physical access to systems and data.
- Technical Details: Assessing risks of information storage and disposal (e.g., secure data wiping protocols), detecting, preventing, and responding to intrusions (e.g., physical access controls like biometric scanners, surveillance systems), protecting against unauthorized access during or after collection, transportation, destruction, or disposal (e.g., secure chain of custody for physical media), and securely disposing of private information within a reasonable time after it's no longer needed (e.g., shredding, degaussing, cryptographic erasure).
- Administrative Safeguards: These relate to an organization's internal management practices and include:
- Expanded Definition of "Private Information":
The Act now defines "private information" as:
- Personal information (e.g., name, number, or other identifier) combined with:
- Social Security number.
- Driver's license number or non-driver identification card number.
- Account number, credit or debit card number, in combination with any required security code, access code, or password that would permit access to an individual's financial account.
- Biometric information (e.g., fingerprint, voice print, retina or iris image) used for authentication.
- A username or email address in combination with a password or security question and answer that would permit access to an online account.
- Crucially, effective March 21, 2025, the definition further expanded to include medical information and health insurance information.
- Personal information (e.g., name, number, or other identifier) combined with:
- Broadened Definition of "Breach of Security":
A "breach" now includes not just unauthorized acquisition of computerized data, but also unauthorized access that compromises the security, confidentiality, or integrity of private information. This means even if data isn't stolen, but an unauthorized party gained access, it could constitute a breach.
- Strengthened Breach Notification Requirements:
If a breach occurs, entities must notify affected New York residents "in the most expedient time possible and without unreasonable delay." Notification must also be provided to the New York Attorney General, the Department of State, and the New York State Police. The Act outlines specific content requirements for breach notices, including contact information for relevant state and federal agencies. Importantly, email notification is generally not permitted if the compromised information includes an email address and corresponding password.
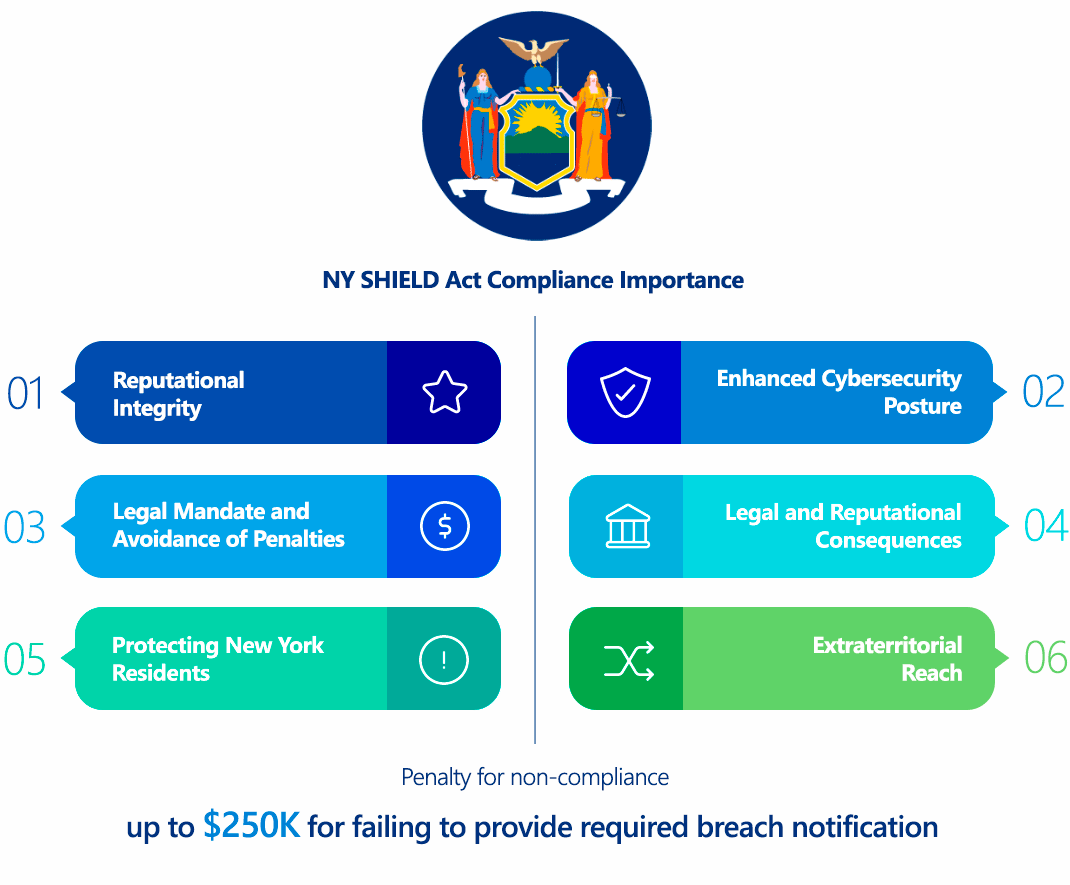
Why Is New York SHIELD Act Compliance Important?
Compliance with the SHIELD Act is critical for several reasons:
- Protecting New York Residents: At its core, the Act safeguards the privacy and security of sensitive information belonging to New York residents, mitigating the risks of identity theft and fraud.
- Legal Mandate and Avoidance of Penalties: It is a mandatory legal requirement. Non-compliance can lead to substantial financial penalties and legal action from the Attorney General.
- Enhanced Cybersecurity Posture: The requirement for "reasonable safeguards" forces organizations to adopt proactive and robust cybersecurity practices, which benefits overall security regardless of regulatory mandates. This means better protection against sophisticated cyberattacks.
- Reputational Integrity: Data breaches severely damage an organization's reputation and consumer trust. Adhering to the SHIELD Act demonstrates a commitment to data protection, helping to maintain customer loyalty and brand integrity.
- Extraterritorial Reach: Even if a business is not physically located in New York, if it handles the private information of even one New York resident, it must comply. This significantly broadens the Act's impact.
Who Needs to Comply with New York SHIELD Act?
The SHIELD Act applies broadly to any person or business that owns or licenses computerized data that includes the private information of a resident of New York.
This means the Act's reach is extensive and includes:
- Businesses physically located in New York State.
- Businesses located outside New York State but that collect, process, or store private information of New York residents.
- Organizations of virtually any size (though small businesses, defined as those with fewer than 50 employees, less than $3 million in gross annual revenue for the past three fiscal years, and less than $5 million in year-end total assets, have slightly more flexible "reasonable security" requirements).
The critical trigger is simply handling the "private information" of a New York resident in computerized form. This could include customer databases, employee records, website user data, and more.
New York SHIELD Act vs GDPR Comparison
While both the New York SHIELD Act and the General Data Protection Regulation (GDPR) aim to protect personal data, they differ significantly in their scope, focus, and technical specificities:
| Aspect | New York SHIELD Act (U.S.) | GDPR (EU) |
|---|---|---|
| Scope | U.S. state-level; specific to "private information" of NY residents. Broader definition of "breach." | Supranational (EU); applies to all "personal data" of EU residents, globally. |
| Data Definition | "Private Information" (personal info + specific data elements like SSN, financial accounts with access codes, biometrics, email/password combos, medical/health insurance info). | "Personal Data" (broad, includes names, IP addresses, health data, genetic data, biometric data, etc.). |
| Legal Basis for Processing | Not explicitly addressed; focus is on safeguarding collected data. | Requires specific legal basis for processing (e.g., consent, contract, legitimate interest). |
| Consent | Not explicitly a core mechanism for data processing (focus on security), though general privacy principles apply. | Explicit, unambiguous consent often required for data processing, with clear right to withdraw. |
| Breach Notification | "Most expedient time possible and without unreasonable delay"; to NY AG, Dept. of State, State Police, and affected individuals. | Data controllers must notify supervisory authorities within 72 hours of becoming aware of a breach; individuals notified "without undue delay." |
| "Right to be Forgotten" | Not explicitly included. Data disposal tied to reasonable business need. | Yes, individuals can request deletion of their data under certain conditions. |
| Data Protection Officer (DPO) | No explicit DPO requirement; mandates "reasonable administrative safeguards" (e.g., designating security personnel). | Mandatory for organizations processing large-scale special categories of data (including health data) or systematic monitoring. |
| Cross-Border Data Transfer | Primarily focused on data protection within an organization's control, regardless of physical location. | Strict rules for transferring data outside the EU, requiring specific safeguards (e.g., Standard Contractual Clauses). |
| Penalties | Civil penalties for breach notification violations (up to $20 per instance, cap $250,000) and for failing to maintain reasonable safeguards (up to $5,000 per violation). Injunctive relief, restitution. | Higher, up to €20 million or 4% of annual global turnover, whichever is higher. |
| Security Framework | "Reasonable safeguards" (administrative, technical, physical) with illustrative examples; emphasis on risk assessment, testing, encryption, MFA for online access. | Principles-based, emphasizing "privacy by design" and "privacy by default," with general security principles but strong implied technical requirements. |
While GDPR is a broader privacy regulation covering all personal data with a strong focus on individual rights, the SHIELD Act is more narrowly focused on security and breach notification for a specific type of "private information" of New York residents. However, SHIELD's technical requirements for safeguarding data are quite specific and demand a robust security posture, making it a significant compliance challenge for many businesses.
How to Ensure New York SHIELD Act Compliance?
Achieving and maintaining SHIELD Act compliance requires a systematic and technically grounded approach:
- Conduct a Comprehensive Risk Assessment:
- Technical Action: Identify all systems, applications, and processes that collect, store, transmit, or process "private information" of New York residents. Perform detailed data mapping to understand data flows. Conduct vulnerability scans and penetration tests on all relevant systems (networks, web applications, mobile apps, databases) to identify technical weaknesses. Assess the likelihood and impact of identified risks. This feeds directly into the "identifying reasonably foreseeable internal and external risks" requirement.
- Implement Robust Technical Safeguards:
- Access Control: Implement Role-Based Access Control (RBAC) to enforce the principle of least privilege. Utilize Multi-Factor Authentication (MFA) for all internal and external access to systems containing private information, especially for online accounts (username/email + password). Implement strong password policies and automatic session timeouts.
- Encryption: Encrypt "private information" both at rest (e.g., full disk encryption, database encryption, encrypted cloud storage) and in transit (e.g., using TLS 1.2+ for web communications, secure VPNs for remote access). Ensure secure key management.
- Network Security: Deploy and configure firewalls, Intrusion Detection/Prevention Systems (IDS/IPS). Implement network segmentation to isolate sensitive data. Use Web Application Firewalls (WAFs) to protect web-facing applications.
- Secure Development Lifecycle (SDLC): Integrate security into the development process for custom applications, including secure coding training, SAST (Static Application Security Testing), and DAST (Dynamic Application Security Testing).
- Patch Management: Implement a rigorous and timely patch management program for all operating systems, applications, and firmware to address known vulnerabilities.
- Logging and Monitoring: Enable comprehensive logging across all systems that handle private information. Implement a Security Information and Event Management (SIEM) system to aggregate, correlate, and analyze logs in real-time, facilitating detection of unauthorized access or suspicious activity.
- Secure Disposal: Implement technical procedures for the secure erasure or destruction of electronic media containing private information when it is no longer needed (e.g., NIST SP 800-88 guidelines for media sanitization).
- Establish a Robust Incident Response Plan:
- Technical Action: Develop a detailed, written incident response plan that includes technical steps for detecting, containing, eradicating, and recovering from data breaches. This involves forensic capabilities, secure communication channels for notification, and data reconstruction procedures. Conduct regular tabletop exercises to test the plan's effectiveness.
- Oversee Service Providers:
- Technical Action: Conduct thorough technical due diligence on all third-party vendors and service providers who have access to private information. Ensure they maintain "reasonable safeguards" and require contractual agreements (similar to Business Associate Agreements in HIPAA) that hold them accountable for data security.
- Provide Continuous Employee Training:
- Technical Action: Implement regular security awareness training for all employees, focusing on recognizing phishing attempts, secure data handling practices, password hygiene, and incident reporting procedures. Conduct simulated phishing exercises to test employee vigilance.
- Regular Testing and Monitoring of Safeguards:
- Technical Action: Beyond initial assessments, continuously monitor security controls. This includes regular vulnerability scans (at least every six months), ongoing penetration testing, and continuous monitoring of network and system activity to ensure safeguards remain effective against evolving threats.
- Maintain Documentation:
- Technical Action: Document all aspects of your information security program, including policies, procedures, risk assessments, test results, and incident response activities. This documentation is crucial for demonstrating compliance to the Attorney General.
Consequences of Non-Compliance with New York SHIELD Act
The penalties for non-compliance with the SHIELD Act can be significant:
- Civil Penalties for Notification Violations: For failing to provide required breach notifications in a timely manner, the Attorney General can seek civil penalties of up to $20 per instance of failed notification, with a maximum cap of $250,000.
- Civil Penalties for Safeguard Violations: For failing to maintain reasonable security safeguards, the Attorney General can seek civil penalties of up to $5,000 per violation.
- Injunctive Relief and Restitution: The Attorney General can also seek injunctive relief (court orders requiring specific actions to rectify non-compliance) and restitution for actual costs or losses incurred by affected individuals.
- Reputational Damage: Beyond direct financial penalties, a data breach resulting from non-compliance can cause severe reputational harm, leading to a loss of customer trust, negative publicity, and potential business disruption.
- Private Right of Action (Indirect): While the SHIELD Act itself doesn't create a direct private right of action for individuals to sue for a breach, a breach resulting from a failure to implement "reasonable safeguards" could still form the basis for common law claims (e.g., negligence) by affected individuals.
How ImmuniWeb Helps Comply with New York SHIELD Act?
ImmuniWeb's AI-powered Application Security Testing (AST) and Attack Surface Management (ASM) platform provides a comprehensive suite of tools that directly address the technical requirements of the New York SHIELD Act:
ImmuniWeb conducts deep API penetration testing, uncovering vulnerabilities like insecure endpoints, broken authentication, and data leaks, ensuring compliance with OWASP API Security Top 10.
Automated AI-driven scans detect misconfigurations, excessive permissions, and weak encryption in REST, SOAP, and GraphQL APIs, providing actionable remediation insights.
ImmuniWeb provides Application Penetration Testing services with our award-winning ImmuniWeb® On-Demand product.
The award-winning ImmuniWeb® AI Platform for Application Security Posture Management (ASPM) helps aggressively and continuously discover an organization's entire digital footprint, including hidden, unknown, and forgotten web applications, APIs, and mobile applications.
ImmuniWeb continuously discovers and monitors exposed IT assets (web apps, APIs, cloud services), reducing blind spots and preventing breaches via real-time risk scoring.
ImmuniWeb provides Automated Penetration Testing services with our award-winning ImmuniWeb® Continuous product.
Simulates advanced attacks on AWS, Azure, and GCP environments to identify misconfigurations, insecure IAM roles, and exposed storage, aligning with CIS benchmarks.
Automates detection of cloud misconfigurations, compliance gaps (e.g., PCI DSS, HIPAA), and shadow IT, offering remediation guidance for a resilient cloud infrastructure.
Combines AI-powered attack simulations with human expertise to test defenses 24/7, mimicking real-world adversaries without disrupting operations.
Runs automated attack scenarios to validate security controls, exposing weaknesses in networks, apps, and endpoints before attackers exploit them.
Provides ongoing, AI-augmented pentesting to identify new vulnerabilities post-deployment, ensuring proactive risk mitigation beyond one-time audits.
Prioritizes and remediates risks in real time by correlating threat intelligence with asset vulnerabilities, minimizing exploit windows.
Monitors dark web, paste sites, and hacker forums for stolen credentials, leaked data, and targeted threats, enabling preemptive action.
The award-winning ImmuniWeb® AI Platform for Data Security Posture Management helps continuously discover and monitor an organization's internet-facing digital assets, including web applications, APIs, cloud storage, and network services.
Scans underground markets for compromised employee/customer data, intellectual property, and fraud schemes, alerting organizations to breaches.
Tests iOS/Android apps for insecure data storage, reverse engineering risks, and API flaws, following OWASP Mobile Top 10 guidelines.
Automates static (SAST) and dynamic (DAST) analysis of mobile apps to detect vulnerabilities like hardcoded secrets or weak TLS configurations.
Identifies misconfigured firewalls, open ports, and weak protocols across on-premises and hybrid networks, hardening defenses.
Delivers scalable, subscription-based pentesting with detailed reporting and remediation tracking for agile security workflows.
Detects and expedites takedowns of phishing sites impersonating your brand, minimizing reputational damage and fraud losses.
Assesses vendors’ security posture (e.g., exposed APIs, outdated software) to prevent supply chain attacks and ensure compliance.
Simulates advanced persistent threats (APTs) tailored to your industry, testing detection/response capabilities against realistic attack chains.
Manual and automated tests uncover SQLi, XSS, and business logic flaws in web apps, aligned with OWASP Top 10 and regulatory standards.
Performs continuous DAST scans to detect vulnerabilities in real time, integrating with CI/CD pipelines for DevSecOps efficiency.
By leveraging ImmuniWeb's comprehensive security testing and attack surface management capabilities, organizations can systematically identify vulnerabilities, implement and validate robust technical safeguards, and demonstrate their commitment to protecting the private information of New York residents, thereby achieving and maintaining SHIELD Act compliance.
List of authoritative resources
Meet Regulatory Requirements with ImmuniWeb® AI Platform

ImmuniWeb can also help to comply with other data protection laws and regulations:
Europe
EU GDPR
EU DORA
EU NIS 2
EU Cyber Resilience Act
EU AI Act
EU ePrivacy Directive
UK GDPR
Swiss FADP
Swiss FINMA Circular 2023/1
North & South America
Middle East & Africa
Qatar Personal Data Privacy Protection Law
Saudi Arabia Personal Data Protection Law
Saudi Arabian Monetary Authority Cyber Security Framework (1.0)
South Africa Protection of Personal Information Act
UAE Information Assurance Regulation (1.1)
UAE Personal Data Protection Law
Asia Pacific
Australia Privacy Act
Hong Kong Personal Data Privacy Ordinance
India Digital Personal Data Protection Act
Japan Act on the Protection of Personal Information
Singapore Personal Data Protection Act
