In current software development with evolving IT, old-school manual pen testing has trouble keeping up. Apps are always being released, infrastructure changes super-fast, and there are so many ways to get attacked. That's why we need Automated Penetration Testing. It uses cool tools and smart algorithms to quickly find weaknesses in apps, networks, and cloud setups. By automating the basic security checks, companies can have ongoing security checks. It speeds up fixes and keeps protection strong in a world that moves fast.
What Is Automated Penetration Testing?
Automated Penetration Testing uses software to automatically check apps, networks, and systems for security problems. Unlike manual pen testing, which depends on people to think like hackers, automated tools run set checks and exploit known issues without someone watching the scan. The goal is to quickly find common security holes, bad setups, and compliance issues, so you know where your security stands.
These tools use big lists of known problems, attack methods, and security rules to check systems. They can spot many issues, like common web app problems (like SQL Injection or Cross-Site Scripting), network setup mistakes, old software, and unsafe settings. While they don't think as creatively as a human tester, they're quick, reliable, and can check everything repeatedly.
Basically, automated pen testing is the start of a good security plan. It's a fast first check that finds a lot of common and easy-to-spot problems. By adding these automated checks into how you build and run things, you can catch problems early in the process when they're easier and cheaper to fix. This helps you release secure stuff faster and lowers risks.
Key Aspects of Automated Penetration Testing
Automated Penetration Testing has some key things that make it helpful for modern cybersecurity. First, speed and being able to check a lot of stuff is super important. Automated tools can check code, networks, or web apps faster and more consistently than people can. This speed means you can check often and regularly. This lets you add security to your quick building and running systems, so new problems are spotted as soon as they appear, without slowing things down.
Second, being consistent and able to do the same checks again and again is a must. Automated tests do the same checks every time. This cuts down on mistakes and makes sure no basic problem is missed. This is great for keeping a base level of security, watching how things get better over time, and proving you're following the rules. Because you can repeat scans, it's easy to test if new code messed anything up and brought back old problems.
Lastly, good coverage of known problems and spotting the first issues is key. Automated tools are great at finding common, easy-to-understand problems and setup mistakes by comparing systems to lists of known risks. They might not find complex problems or new hacks, but they're good at finding the easy targets that attackers go for first. By getting rid of these common problems, human security people can spend time on harder, more important security issues.
Why Is Automated Penetration Testing Important?
Automated Penetration Testing is getting more important because of how fast software building changes and how large IT systems are now. With continuous integration, where apps are updated all the time, manual pen tests can't keep pace. Automated testing is key because it makes security checks a regular thing. This lets companies add security checks right into how they build things. It makes sure new problems are found and fixed fast, often before the code is even live, which lowers the chance of attackers getting in.
Also, automated pen testing is key for making security scalable and cheap. Manually testing every app, network, or cloud setup is too expensive for most places. Automated tools can check everything repeatedly, security checks possible even for big and complicated setups. This lets security teams do more by focusing on bigger tasks, while the automated stuff handles the basic checks.
Beyond just being easier, automated pen testing helps with following rules and making security better. Lots of rules and laws need regular security checks. Automated tools give you a way to prove this, which helps you avoid fines and legal issues. By always finding and helping fix known problems, automated testing makes a stronger security setup, which lowers your risk and makes you safer from attacks.
How Does Automated Penetration Testing Work?
Automated Penetration Testing works by scanning, checking, then reporting using software to spot problems. It starts with setting things up. Security people set up the automated tool by naming the target IP, a network scan, authentication details if required, and the type of tests that must be done. Then, the tool begins to behave according to its code.
Next, the tool automatically finds and identifies weaknesses. For web apps, it crawls to see the structure while identifying all inputs, parameters, and functionalities. For networks, it checks ports and lists the services. As it behaves, it sends harmful tests. It looks at its responses, identifying indicators of weaknesses.
Lastly, the automated penetration testing tool creates a report of what it finds. This report has a list of problems identified, how bad they are, and details of where the problem was found. A lot of advanced tools also give tips on how to fix them to help developers and IT teams fix it fast. This faster feedback makes it easier to put into existing development and security ways.
Types of Automated Penetration Testing
Automated Penetration Testing isn't just one tool. It's a way of doing things that includes different methods, each good for checking different parts of a company's systems.
Static Application Security Testing (SAST) tools check an app's code without running it which is called white-box testing. SAST scanners find weak points by looking for mistakes in the code, like coding errors or bad patterns. They are good at finding problems like SQL injection or cross-site scripting (XSS) early on, while the code is being written. This makes them great for using with developer tools and automated build pipelines to improve security from the start.
Dynamic Application Security Testing (DAST) tools test a running web app from the outside, acting like a real attacker which is called black-box testing. DAST scanners explore the app, send bad data to its forms and APIs, and watch how the app responds to find weak points that show up when it's running, like problems with how sessions are managed or how users are logged in. DAST is good at finding issues that SAST might miss, especially those related to how the app works with its environment and backend systems. It can be used on any web app, no matter what technology it uses.
Besides app testing, Network Vulnerability Scanners are a common type of automated pen testing for infrastructure. These tools check network devices, servers, and computers for open ports, bad settings, old software, and known weak spots (CVEs). They help companies find weak spots in their network and internal areas. Also, Software Composition Analysis (SCA) tools are a special type that automatically finds known weak spots in third-party libraries and open-source parts used in apps, which helps with supply chain security. Each type is good at different things, and a good security plan usually uses a mix of these automated testing methods.
Components of Automated Penetration Testing
A good Automated Penetration Testing setup usually has a few important parts that work together to give a full and productive security check.
The most important part is the Scanning Engine. This is what actually finds the weak spots. For SAST, it checks the code. For DAST, it explores and messes with the app. For network scanners, it checks ports and services. This engine checks the target, tries different attack methods, and gathers data on how it responds, which is how it finds weak spots. How well this engine works, including if it can handle new technologies (like SPAs, APIs, and microservices), affects how well it scans.
Also, a big and updated Vulnerability Database or Knowledge Base is very important. This collection has a lot of known weak spots, common problems (like OWASP Top 10 and CWE), attack methods, and bad security settings. The scanning engine uses this database to figure out what the weak spots are, how serious they are, and what they mean. How good and up-to-date this database matters a lot, because it decides what weak spots the tool can find. It needs to be updated all the time to keep up with new threats.
Finally, the Reporting, Remediation Guidance, and Integration Module gives the results and ways to fix them. This part makes clear reports of the weak spots found, including how bad they are, what they mean, and often where they are located (like a line of code or a URL). Most importantly, it gives advice on how to fix the problems quickly. Modern automated testing tools can also connect to developer tools, build pipelines, bug trackers (like Jira), and other security platforms. This allows automated workflows and makes security a part of the whole process.
Automated Penetration Testing Helps
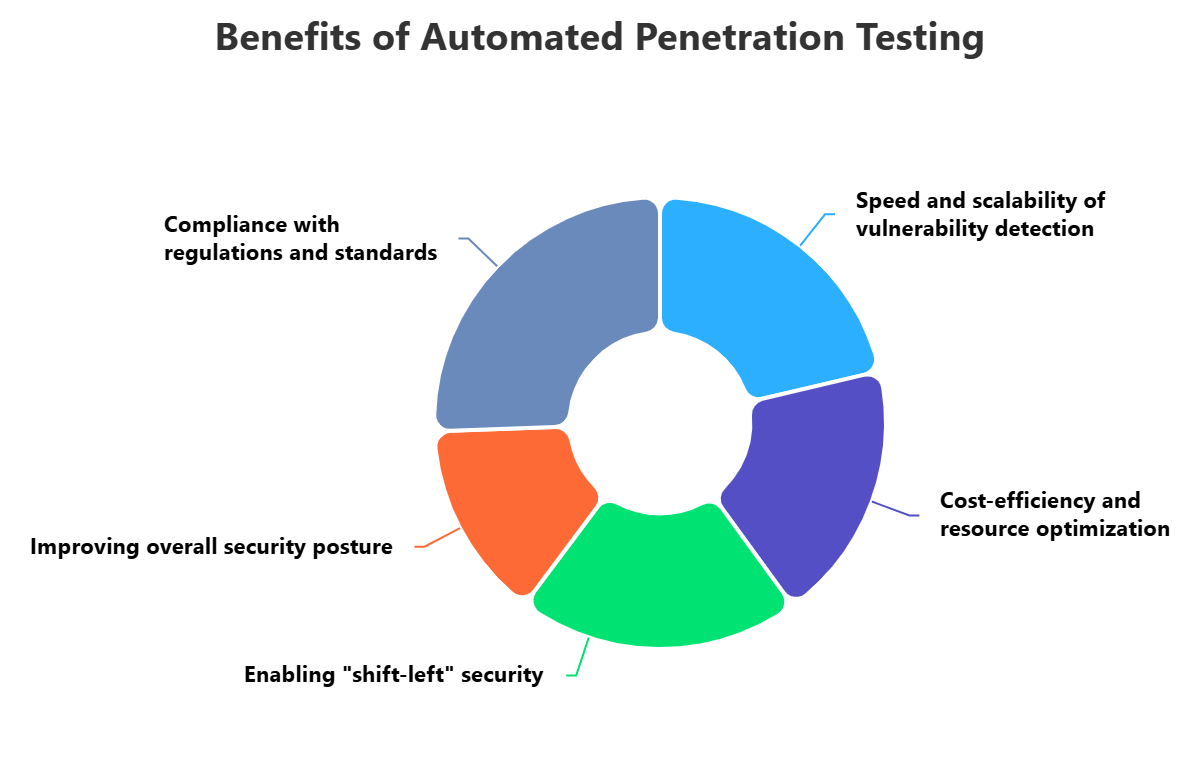
Using Automated Penetration Testing has many good points that greatly improve a company's security and how well it works. A main good point is how fast and well it finds weak spots. Automated tools can scan a lot of code, many apps, or big networks much faster and more reliably than doing it by hand. This speed allows regular security checks, even all the time, which lets companies find and fix weak spots faster, often in minutes or hours. This greatly reduces the time attackers have to cause problems.
Also, automated testing saves money and uses resources better. Doing full penetration tests by hand for every app or network change costs too much and takes too many resources. Automated tools do the normal, repeated checks, which lets skilled security experts focus on harder, more important security issues like flaws in how the business works or advanced attack simulations. This lets companies get the most out of their security budget and use their people better, covering more ground without spending more money.
Besides the benefits for how things work, automated pen testing helps make security a part of the process from the start and improves the overall security. By adding automated scans to the software development process and build pipelines, weak spots can be found and fixed much earlier, often as the code is being written. This stops flaws from getting into the final product, saves money on fixing them, and makes developers more aware of security. Regularly finding and fixing known weak spots builds a stronger security base, reducing the company's risk and making it more resistant to cyber threats.
Problems of Automated Penetration Testing
Even though it has many good points, Automated Penetration Testing also has problems that companies need to think about. One big problem is the chance of false positives and false negatives. Automated scanners can sometimes mark good code or settings as weak spots (false positives), which wastes developers' time on problems that don't exist. On the other hand, they might miss real weak spots (false negatives), especially complex flaws in how the business works or new attack methods. This can create a false sense of security and leave important flaws open.
Another big problem is that they don't really understand how the business works and what things mean in context. Automated tools are good at finding common weak spots and bad security settings. But they usually can't understand the unique business processes, specific login methods, or the intended use of an app. This means they often miss important flaws that use the app's normal functions in a way they weren't meant to be used (like skipping login by doing a specific series of valid actions). These complex weak spots that depend on the context usually need human intelligence and manual pen testing to find.
Finally, adding automated testing tools to different and quickly changing IT environments can be hard. Companies often use a mix of old systems, new cloud apps, and different development methods. Making sure automated scanners work well with different build pipelines, bug trackers, and security platforms across these mixed environments takes a lot of technical skill and ongoing work. Also, attack methods are always changing, so automated tools need to be updated and adjusted all the time to stay useful, which adds to the work needed to keep them running.
Best Practices for Automated Penetration Testing
To get the most out of automated penetration testing, companies should follow a few important tips. First, get automated scanning involved early. This shift-left idea is really important. Put SAST tools into developer tools and code storage for quick feedback, and add DAST and SCA tools into CI/CD systems to scan with each build or release. This makes sure problems are found and fixed as soon as possible, which greatly lowers the cost and risk of fixing them.
Second, use different kinds of automated testing methods for full protection. If you just depend on one kind of automated scan, you'll probably have big holes in your security. A good plan should include SAST for checking code, DAST for studying how things act when running, and SCA for watching out for problems in third-party parts. For infrastructure, you have to use network vulnerability scanners. This varied way makes sure many problems, from coding mistakes to runtime issues and known problems in libraries, are found across the whole area that could be attacked.
Last, keep adjusting and improving automated scanning setups to cut down on unimportant alerts and improve how correct they are, and add in manual testing. Check scan results often, decide what's most important based on real risk and what matters to the business, and give clear fixing advice to development and operations teams. It's vital to understand what automation can't do; tricky business logic problems and new ways of attacking still need human thinking. So, back up automated testing with regular, focused manual penetration tests to find complicated problems that automated tools can't, making sure you have a complete and strong security setup.
How ImmuniWeb Can Help with Automated Penetration Testing?
ImmuniWeb offers a powerful and comprehensive solution that significantly enhances an organization's Automated Penetration Testing capabilities through its unique, AI-driven, and human-verified approach. While ImmuniWeb's core offering is often described as "hybrid" penetration testing, its foundation includes highly sophisticated automated scanning that directly addresses the needs of automated testing. Their AI-powered Web Application Penetration Testing (WAPT) and Mobile Application Penetration Testing (MAPT) engines intelligently crawl, analyze, and test complex applications, including Single Page Applications (SPAs), APIs, and microservices, to discover a broad range of vulnerabilities. This intelligent automation provides rapid and accurate initial detection, which is the essence of effective automated testing.
ImmuniWeb's AI is designed to go beyond basic pattern matching, leveraging machine learning to identify more subtle vulnerabilities and reduce false positives, a common challenge in automated testing. This makes their automated component highly efficient and reliable. Furthermore, their platform supports continuous security testing, allowing organizations to integrate automated scans into their CI/CD pipelines, ensuring that new code changes are immediately assessed for security flaws. This seamless integration enables a true "shift-left" approach, providing developers with rapid feedback on vulnerabilities as they are introduced.
Beyond the automated scanning, ImmuniWeb's unique value proposition lies in its human-led validation and expert remediation guidance. While the AI performs the heavy lifting of automated discovery, certified ethical hackers meticulously review the findings, eliminating false positives and conducting manual exploitation to confirm true vulnerabilities. This hybrid model ensures that the "automated" findings are highly accurate and actionable, providing precise remediation advice that directly addresses the identified flaws. This combination of advanced automation and human verification ensures that organizations receive the most reliable and effective automated penetration testing results, leading to tangible security improvements.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










