In today's digital-first world, software applications are the engines driving business innovation, customer engagement, and critical operations across every industry. From web and mobile apps to desktop software and intricate APIs, these applications handle vast amounts of sensitive data and facilitate countless transactions. However, their pervasive nature also makes them prime targets for cyber attackers, who constantly seek vulnerabilities to exploit for data breaches, financial fraud, and service disruptions. Application Penetration Testing emerges as an indispensable security discipline, proactively identifying and mitigating these weaknesses before malicious actors can exploit them, thereby safeguarding sensitive data and ensuring the integrity and availability of an organization's software assets.
What Is Application Penetration Testing?
Application Penetration Testing, often simply called "AppSec Pentesting" or "Pen Testing," is a simulated cyberattack conducted against a software application to identify security vulnerabilities, weaknesses, and potential flaws. Unlike automated vulnerability scanning, which relies on predefined signatures and patterns, penetration testing involves skilled ethical hackers who actively mimic the tactics, techniques, and procedures (TTPs) of real-world attackers. The process goes beyond merely finding bugs; it seeks to understand how these vulnerabilities could be exploited in a real-world scenario, what data could be compromised, and what the potential impact on the business might be. This comprehensive, human-led approach provides a deeper, more realistic insight into an application's security posture.
The scope of application penetration testing is broad and adaptable, encompassing various types of software. This includes web applications (e.g., e-commerce sites, online banking portals), mobile applications (iOS and Android), desktop applications, and Application Programming Interfaces (APIs). Testers examine everything from common vulnerabilities like SQL Injection, Cross-Site Scripting (XSS), and Broken Authentication to more complex business logic flaws, improper authorization schemes, insecure data exposure, and weaknesses in cryptographic implementations. The objective is to uncover any weakness that could be leveraged by an attacker to gain unauthorized access, manipulate data, disrupt services, or exfiltrate sensitive information.
Ultimately, application penetration testing provides an objective and actionable assessment of a software application's resilience against cyber threats. It moves beyond theoretical vulnerabilities to demonstrate practical exploitability, helping organizations prioritize risks and allocate resources effectively for remediation. By identifying and addressing security flaws before they are exploited, organizations can prevent costly data breaches, maintain regulatory compliance, preserve customer trust, and protect their brand reputation in an increasingly interconnected and threat-laden digital landscape, ensuring the long-term integrity of their software assets.
Key Aspects of Application Penetration Testing
Application Penetration Testing is characterized by several key aspects that differentiate it from other security assessments and contribute to its effectiveness in securing software. Firstly, it demands a deep understanding of diverse application technologies and common attack methodologies. Ethical hackers involved in AppSec pentesting must be intimately familiar with various programming languages, development frameworks, database systems, client-side technologies, and communication protocols. Crucially, they must possess expertise in exploiting vulnerabilities outlined in industry standards like the OWASP Top 10, as well as understanding more sophisticated, application-specific logic flaws that automated tools often miss.
Secondly, a significant aspect is the combination of automated tools and extensive manual expertise. While automated application security testing (AST) tools (SAST, DAST, SCA) can efficiently identify a wide range of common, known vulnerabilities, they often struggle with complex business logic flaws, multi-step attack scenarios, and subtle authorization bypasses. Skilled human penetration testers, using their creativity, analytical thinking, and understanding of attacker TTPs, can chain together seemingly minor vulnerabilities to achieve significant compromise, mimic user behavior, and explore the application's unique functionalities for weaknesses, providing a depth of analysis that automation alone cannot achieve.
Finally, contextual understanding and business logic analysis are paramount. An application penetration test is not just about finding technical bugs; it's about understanding the potential impact of those bugs within the context of the application's specific business function. Testers often analyze how a vulnerability could lead to financial fraud, data exfiltration of critical information, or disruption of core services. This deep understanding of the application's intended purpose, data flow, and user roles allows testers to identify and prioritize risks that are most relevant and damaging to the organization, leading to more actionable and impactful remediation advice.
Why Is Application Penetration Testing Important?
Application Penetration Testing is of paramount importance in today's digital landscape due to the critical role software applications play in almost every aspect of business and the ever-present threat of cyberattacks. With applications serving as the primary gateway for customer interactions, data exchange, and internal operations, they are a lucrative target for cybercriminals. Without robust security validation through penetration testing, organizations risk exposing sensitive customer data, financial information, intellectual property, and proprietary business logic to exploitation, leading to devastating data breaches and significant financial and operational losses that can cripple an enterprise.
Furthermore, the continuous evolution of cyber threats and the rapid pace of modern software development necessitate constant security vigilance. New vulnerabilities are discovered daily, and agile development cycles often mean that security considerations can be overlooked in the rush to deploy new features. Application penetration testing provides a crucial and proactive mechanism to identify these newly introduced flaws, as well as long-standing weaknesses, before malicious actors can discover and exploit them. It acts as a critical safety net, helping to ensure that applications remain secure throughout their lifecycle, even with frequent updates and changes, by providing a realistic assessment of their resilience.
Beyond direct threat mitigation, application penetration testing is also vital for regulatory compliance and building customer trust. Many industry regulations and data privacy laws (e.g., GDPR, HIPAA, PCI DSS, DORA) explicitly mandate regular security assessments, including penetration testing, for applications handling sensitive data. Failing to conduct such tests can result in hefty fines, legal repercussions, and a significant blow to an organization's reputation. By proactively investing in application penetration testing, organizations demonstrate a commitment to protecting user data, fostering greater confidence and trust, which is invaluable for sustained business success and brand loyalty in a competitive market.
How Does Application Penetration Testing Work?
Application Penetration Testing typically follows a structured methodology, often starting with a reconnaissance and information gathering phase. In this initial step, the penetration testers gather as much information as possible about the target application without direct interaction, often mimicking an external attacker. This can involve analyzing public-facing information, identifying technologies used, enumerating subdomains or APIs, studying publicly available documentation, and understanding the application's functionality. The goal is to build a comprehensive understanding of the application's architecture, its potential attack surface, and common entry points before launching any direct attacks.
Following reconnaissance, the core of the testing involves vulnerability analysis and exploitation. Testers utilize a combination of manual techniques, specialized tools, and their deep understanding of application vulnerabilities to identify security flaws. This includes examining inputs for injection vulnerabilities (SQL, XSS, command injection), testing authentication and authorization mechanisms for bypasses, analyzing session management, scrutinizing data handling and encryption, and exploring business logic for exploitable flaws. If a vulnerability is found, testers will attempt to exploit it in a controlled manner to confirm its severity and determine the extent of potential compromise (e.g., gaining unauthorized access, exfiltrating data, escalating privileges).
Finally, the process culminates in reporting and remediation guidance. Once vulnerabilities are identified and their exploitability confirmed, the penetration testers meticulously document their findings. This comprehensive report includes detailed descriptions of each vulnerability, steps to reproduce it, its severity (e.g., CVSS score), and its potential business impact. Crucially, the report also provides actionable recommendations for remediation, often with specific code examples, configuration changes, or architectural improvements. This report serves as a roadmap for the development and security teams to prioritize and address the identified security flaws, strengthening the application's defenses and improving its overall security posture.
Types of Application Penetration Testing
Application Penetration Testing can be broadly categorized into different types based on the level of information provided to the testing team, each offering unique insights into an application's security posture.
Black Box Testing, also known as external testing or "zero-knowledge" testing, simulates an attack from an external hacker with no prior knowledge of the application's internal structure, source code, or infrastructure. Testers interact with the application solely through its public-facing interfaces, just as a real-world attacker would. This type of testing is valuable for assessing the application's external attack surface, identifying easily discoverable vulnerabilities, and understanding what a determined outsider could achieve without any privileged information. It provides a realistic view of an attacker's initial reconnaissance and exploitation efforts.
Conversely, White Box Testing, also known as internal testing or "full-knowledge" testing, involves providing the penetration testers with full access to the application's source code, architecture diagrams, server configurations, and sometimes even access to development or staging environments. This allows for a much deeper and more comprehensive analysis of the application's security, as testers can scrutinize the code for hidden vulnerabilities, insecure coding practices, logical flaws, and cryptographic weaknesses that might not be apparent from an external perspective. White box testing is particularly effective for identifying complex, subtle vulnerabilities and ensuring adherence to secure coding guidelines, often leading to more thorough findings.
A common hybrid approach is Gray Box Testing, where testers are given some limited knowledge of the application's internal workings, such as access to certain functionalities, test user accounts, or partial documentation, but not full access to the source code. This approach aims to simulate an attack from a malicious insider or a compromised legitimate user, providing a more realistic assessment of potential threats from individuals with some level of authorized access. The choice of testing type depends on the specific security objectives, the maturity of the application, and the resources available, often combining the efficiency of black box with the depth of white box.
Components of Application Penetration Testing
A thorough application penetration testing engagement relies on the meticulous examination of several critical components that collectively contribute to the security of a software application.
The first and most fundamental component is the application code and logic itself. Testers meticulously analyze the application's codebase (either directly in white-box testing or indirectly through dynamic interaction) for common vulnerabilities like injection flaws (SQL, command, LDAP, XSS), insecure direct object references (IDOR), and security misconfigurations. Beyond common vulnerabilities, a deep dive into the application's unique business logic is performed to uncover flaws in its specific functionalities, such as incorrect authorization, race conditions, or flawed workflow processes that could be exploited to gain unauthorized access or manipulate data. This component is where the majority of critical findings often reside.
Secondly, the APIs and backend services that the application interacts with are crucial components. Modern applications heavily rely on Application Programming Interfaces (APIs) to communicate with backend databases, microservices, and other external systems. Testers scrutinize these APIs for vulnerabilities, including broken authentication, improper authorization, excessive data exposure, and insufficient input validation, which could allow an attacker to bypass front-end security controls and directly compromise backend systems or data stores. The security of these underlying services is paramount to the overall application security, as they often expose critical business logic.
Finally, the authentication, authorization, and session management mechanisms are vital components that are rigorously tested. This involves evaluating how users are authenticated (e.g., password policies, multi-factor authentication implementation, secure credential storage), how their permissions are managed (e.g., role-based access control, horizontal/vertical privilege escalation), and how user sessions are handled securely (e.g., session token generation, expiration, invalidation, protection against session fixation). Weaknesses in these areas can allow attackers to impersonate legitimate users, gain unauthorized access to functionalities or data, or maintain persistence within the application environment, making them a primary focus of application penetration testing.
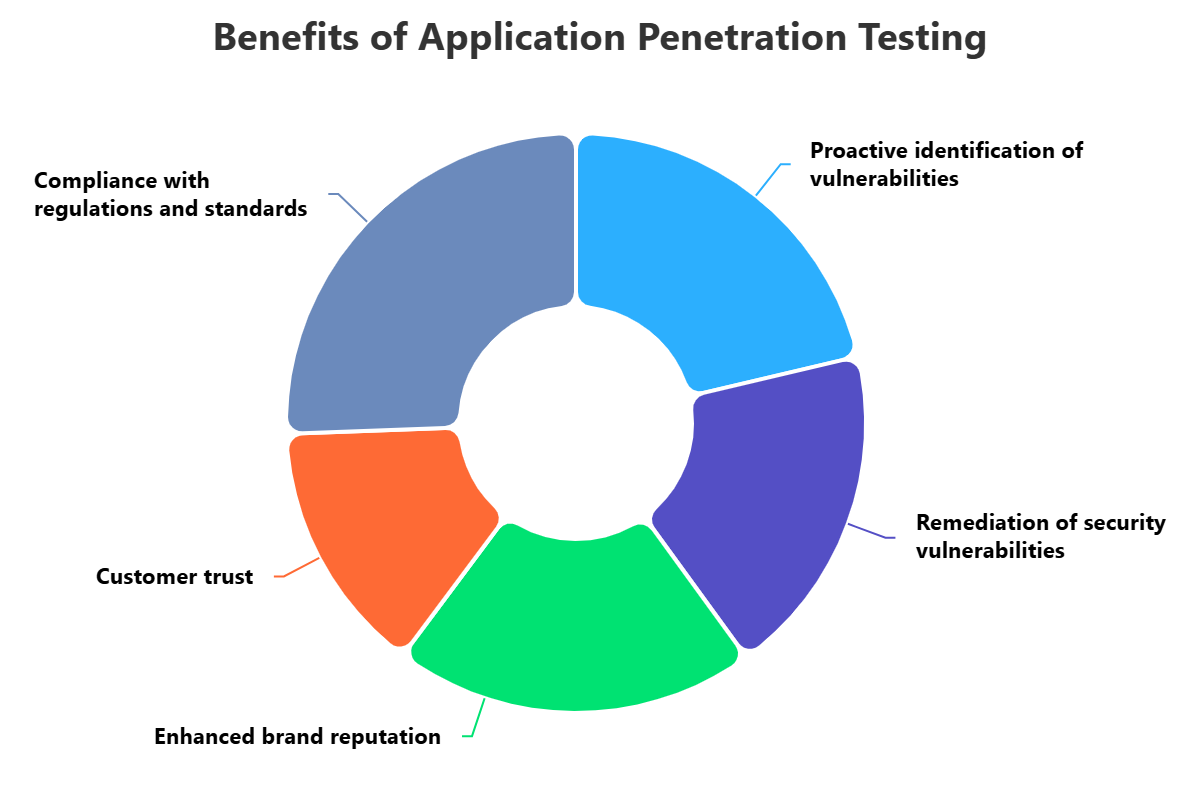
Benefits of Application Penetration Testing
The benefits of regularly conducting application penetration testing are extensive and crucial for any organization developing and deploying software. A primary advantage is the proactive identification and remediation of security vulnerabilities before they can be exploited by malicious actors. By simulating real-world attacks, organizations can uncover weaknesses that automated scanners might miss, allowing them to patch systems, reconfigure applications, and strengthen controls. This significantly reduces the likelihood and impact of a successful cyberattack, which often translates to preventing costly data breaches, reputational damage, and financial losses, protecting the organization's bottom line.
Furthermore, application penetration testing helps organizations ensure compliance with stringent industry regulations and standards. Many data protection laws (e.g., GDPR, HIPAA, CCPA) and industry-specific frameworks (e.g., PCI DSS, ISO 27001, DORA) explicitly mandate regular security assessments, including penetration testing, for applications handling sensitive data. Performing these tests provides verifiable evidence of due diligence, helping organizations meet their compliance obligations, avoid hefty fines, and maintain necessary certifications, which is increasingly important for business continuity and market standing.
Beyond direct security improvements and compliance, robust application penetration testing also contributes to enhanced brand reputation and customer trust. In an era where data breaches are becoming increasingly common and publicly reported, users are highly conscious of the security of their online interactions and the safety of their data. By actively investing in comprehensive security testing, organizations demonstrate a strong commitment to protecting user data and privacy, fostering greater confidence in their applications and services. This trust can translate into increased user adoption, loyalty, and a stronger competitive advantage in the marketplace, safeguarding the long-term success of digital initiatives.
Challenges of Application Penetration Testing
Despite its critical importance, application penetration testing presents several inherent challenges that organizations and testers must navigate. One significant hurdle is the rapid pace of modern software development and continuous deployment (CI/CD). Applications are frequently updated with new features and functionalities, often on a daily or weekly basis. Conducting thorough manual penetration tests for every new release can be time-consuming and expensive, making it difficult to maintain a consistent security testing cadence that keeps up with agile development cycles without becoming a bottleneck or delaying releases.
Another major challenge is the complexity of modern application architectures and their underlying ecosystems. Today's applications are often built with intricate microservices, rely heavily on numerous third-party APIs, integrate with various cloud services, and utilize diverse front-end and back-end technologies. This complexity makes it challenging for testers to understand the entire attack surface, map data flows accurately, and identify vulnerabilities that span multiple components or rely on obscure interdependencies, requiring a wide range of specialized skills, tools, and a deep understanding of the entire system.
Finally, the difficulty in detecting sophisticated business logic flaws and multi-stage attack scenarios remains a significant challenge for purely automated tools. While automated scanners excel at identifying common, pattern-based vulnerabilities, they often struggle with understanding the unique business logic of a specific application. This means they might miss authorization bypasses unique to a specific workflow, complex financial manipulation flaws, or multi-step attack chains that require human intelligence, creativity, and persistent effort to uncover, highlighting the irreplaceable value of skilled human penetration testers and the need for a hybrid approach.
Best Practices for Application Penetration Testing
To ensure the maximum benefit and successful execution of application penetration testing, organizations should adhere to several key best practices. Firstly, define a clear and comprehensive scope and objectives before initiating any test. This includes identifying the specific applications or APIs to be tested, the type of testing (black, white, or gray box), the desired outcomes (e.g., discover specific vulnerability types, test a particular business flow), and any in-scope third-party integrations. A well-defined scope ensures that the testing effort is focused, all critical areas are covered, and relevant results are obtained, preventing wasted resources.
Secondly, integrate application penetration testing into a continuous security lifecycle, adopting a "shift-left" approach. Instead of conducting one-off tests just before deployment, incorporate security testing at various stages, from design and development (e.g., through secure code reviews and early DAST/SAST) to post-deployment. This continuous feedback loop helps identify vulnerabilities early when they are less expensive and easier to fix, rather than discovering them just before or after a release, which can lead to costly delays, rework, and increased risk, thereby accelerating secure software delivery.
Finally, prioritize findings based on actual risk and provide actionable remediation guidance. A long list of vulnerabilities without context can be overwhelming. Penetration test reports should clearly categorize findings by severity (e.g., CVSS score), exploitability, and potential business impact. Crucially, they should provide specific, detailed, and actionable recommendations for remediation, often including code examples or configuration steps. Fostering strong communication and collaboration between the security team and development teams is also essential to ensure that vulnerabilities are understood, prioritized, and efficiently addressed, leading to measurable security improvements and a stronger overall application security posture.
How ImmuniWeb Can Help with Application Penetration Testing?
ImmuniWeb offers powerful and comprehensive solutions for Application Penetration Testing, ImmuniWeb On-Demand, ImmuniWeb MobileSuite, and ImmuniWeb Continuous, leveraging its innovative approach that combines AI-driven automation with expert human intelligence. Their award-winning hybrid application security testing (AST) solutions are designed to cover a broad spectrum of application types, including web applications, mobile applications (iOS and Android), and APIs. The AI engine intelligently crawls and analyzes complex applications, including Single Page Applications (SPAs) and microservices, to discover a wide range of vulnerabilities, providing rapid initial insights and optimizing the overall testing process.
What truly differentiates ImmuniWeb's offering is the subsequent human-led penetration testing and validation. After the AI's intelligent analysis, ImmuniWeb's team of certified ethical hackers meticulously reviews the findings, conducts manual exploitation attempts, and performs deep dives into complex business logic vulnerabilities. This critical human element is indispensable for uncovering sophisticated flaws, chaining together seemingly minor issues to achieve significant compromise, and identifying unique application-specific weaknesses that purely automated tools often miss, thereby ensuring a highly thorough, accurate, and realistic security assessment.
Furthermore, ImmuniWeb's platform is designed for actionable intelligence and seamless integration into development workflows. Their penetration test reports are clear, concise, and developer-friendly, providing detailed vulnerability descriptions, reproduction steps, and specific, prioritized remediation advice, often with code snippets for direct implementation. The platform also supports continuous testing and can integrate with existing CI/CD pipelines and bug tracking systems, enabling a "shift-left" security approach. This unique hybrid methodology ensures that organizations not only identify a broad spectrum of application vulnerabilities but also receive the precise guidance needed to efficiently fix them, significantly enhancing their overall application security posture and accelerating secure software delivery.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.










