Take Your Shodan Asset Search to the Next Level
April 27, 2020How many Internet-exposed assets can Shodan find compared to an Attack Surface Management (ASM) solution? How did OSINT-based asset discovery technologies progress since 2018?
Views: 29.5k Read Time: 5 min.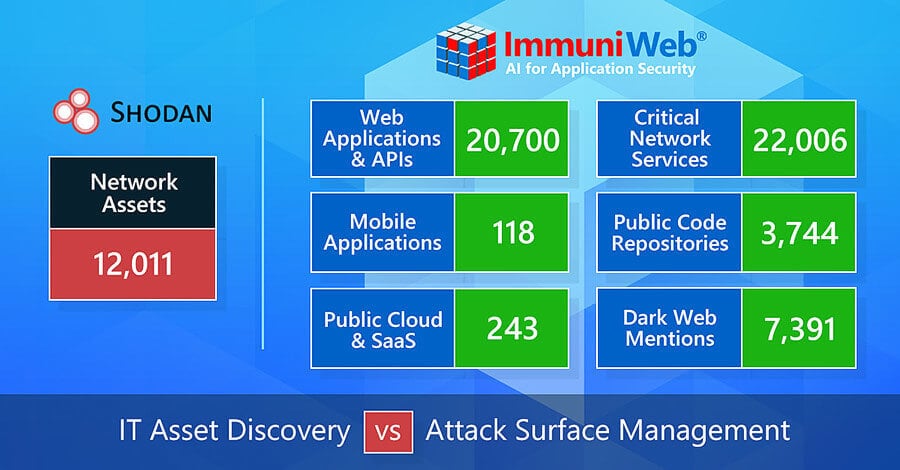
In 2020, an attack surface (also known as attack perimeter) is composed of a continuously growing number of interconnected IT and digital assets, convolutedly operated both from in-house and by third parties.
The longstanding problem of Shadow IT is now exacerbated by a rapid proliferation of public cloud, SaaS/PaaS platforms, IoT devices, and WFH infrastructure spurred by the coronavirus pandemic. Maintaining an up2date and holistic inventory of your Internet exposure is essential to prevent data breaches and ensure an effective cybersecurity strategy: you cannot protect what you cannot see.
The total number of exposed records in 2019 hit 15.1 billion according to a recent research by Risk Based Security.
A considerable number of these disastrous incidents and data breaches stem from unknown or abandoned assets, unprotected cloud and exposed databases, being a low-hanging fruit for cybercriminals.
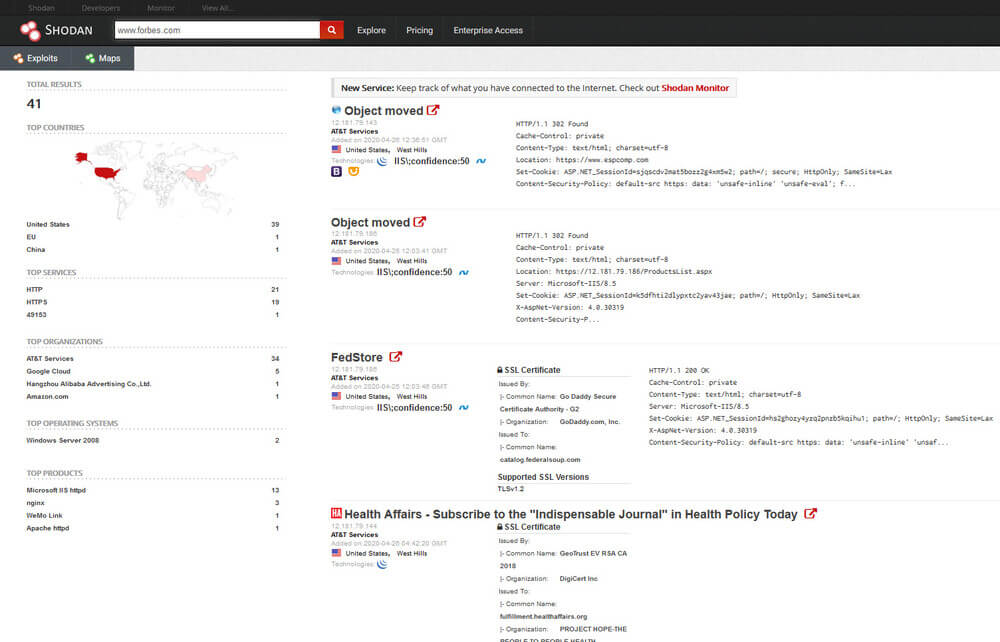
Shodan is a popular online search engine for Internet-connected servers and devices, based on OSINT (Open Source Intelligence). Many cybersecurity professionals use Shodan to detect Internet exposure of their organizations. Shodan says it crawls the entire Internet every week to give a global perspective of exposed devices and computers that are directly accessible from the Internet. For example, with Shodan you can easily find a specific model of a web camera in your city or within a provided network range. Shodan provides a limited free online search, and also offers paid subscriptions based on the monthly volume of search queries.
ImmuniWeb® Discovery ASM leverages our award-winning OSINT and AI technologies to illuminate your external attack surface in a 24/7 mode. It rapidly detects, tests and scorecards your digital and IT assets accessible from the Internet, enhancing the visibility with a proactive monitoring of Dark Web and public Code Repositories for mentions of your company or its assets. Its continuous subscription is available at unbeatable fixed price, moreover, ImmuniWeb Discovery has no upper limit for the number of discoverable assets, manual rescans of your assets or detectable incidents. Being a production-safe and non-intrusive, it fits well for self-assessment and third-party risk scoring purposes. You can easily customize flexible alerts on any newly detected assets, incidents or other events in a few clicks on your dashboard.
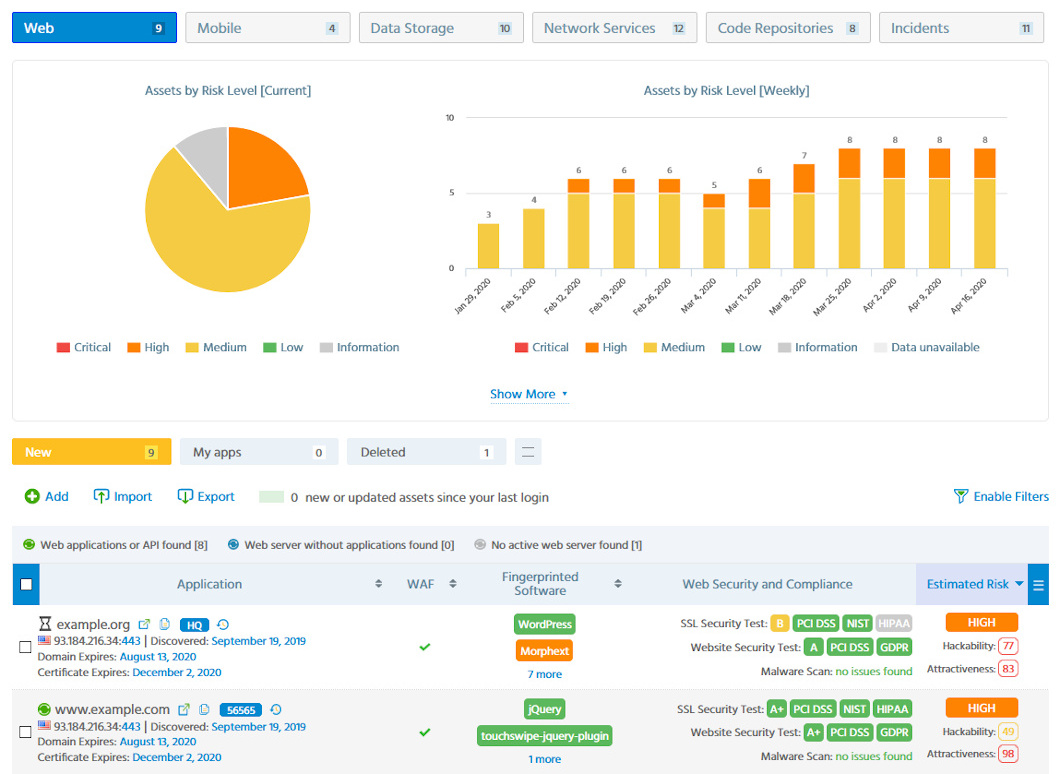
ImmuniWeb® Discovery ASM Dashboard
A couple of years ago, Attack Surface Management solutions were at the very beginning of a successful journey towards indispensability for corporate cyber resilience and threat defense programs, now being recommended by industry analysts from Gartner, IDC and Forrester. At that time, we released the very first version of ImmuniWeb Discovery, mainly focused on non-intrusive reconnaissance of web and mobile applications, offering the first run for free.
In March 2018, we benchmarked our external asset discovery capacities versus those ones of Shodan. We conducted a non-intrusive asset discovery on the following well-known organizations coming from diversified vertical and horizontal niches:
|   |  |  |  |
We used the organization’s name and main website address as input to launch searches aimed to illuminate the organizations’ Internet exposure with the purpose to explore:
- (a) known knowns
- (b) known unknowns
- (c) unknown unknowns
We were pretty happy with the benchmarked results and pursued the continuous improvement of our technology. Today, following the strong progress of the global Attack Surface Management market and the concomitant increase of the modern threat landscape, we decided to repeat this experiment to measure the progress made.
Given that today ImmuniWeb Discovery detects a great variety of digital assets and items, and in order to keep the new comparison fair, we only counted IT assets such as network services and websites comparing the results with Shodan:
| External Network and Web Assets Discovery * | ||||
|---|---|---|---|---|
| 2018 | 2020 | |||
| Shodan | ImmuniWeb | Shodan | ImmuniWeb | |
| Forbes | 1 | 110 | 6 | 822 |
| OpenBSD | 5 | 112 | 10 | 285 |
| WWF | 10 | 28 | 4 | 212 |
| European Council | 613 | 3728 | 99 | 5820 |
| 1882 | 2309 | 11,892 | 35,928 | |
| Total Network Assets | 2511 | 6287 | 12,011 | 43,067 |
| * On top of this, ImmuniWeb has also detected 11,521 assets of other types | ||||
External network and web assets discoverable with Shodan and ImmuniWeb Discovery
This benchmark clearly delineates and differentiates Shodan and ImmuniWeb Discovery in a mutually beneficial way. Shodan provides a quick snapshot of some of your devices that are, or were, visible from the Internet, and gives technical details about them comparable to a handy NMAP scan. While ImmuniWeb Discovery is a comprehensive and multidimensional Attack Surface Management solution, delivering a helicopter view on the integrity of your digital and IT assets, threats and risks, security incidents and data leaks, in actionable, easily manageable and holistic manner.
Since 2018, in addition to the asset discovery capacities illustrated in the table above, we built a wide spectrum of new features and functionalities for ImmuniWeb Discovery, bolstering its OSINT reconnaissance and risk scoring capacities. Notable improvements are:
- Discovery of critical network infrastructure (e.g. containers and virtualization management software, network services such as SSH, FTP, VPN, RDP and VoIP infrastructure).
- Discovery of popular databases and related software (e.g. MongoDB, Elasticsearch, Oracle, SAP), public cloud (e.g. AWS, Azure, Google Cloud), external SaaS/PaaS solutions that process your data (e.g. Slack, Salesforce, Zoom) and IoT devices (e.g. CCTV cameras, smart printers).
- Non-intrusive Software Composition Analysis (SCA) for web and mobile applications, with over 200 major CMS and web frameworks, over 200,000 of their plugins and extensions, and over 165,000 versions of 7,500 external JS libraries.
- Actionable risk scoring, composed of Hackability and Attractiveness Scores, that assess and measure how technically hackable and how attractive an asset is for cybercriminals by leveraging Big Data and Deep Learning. Named the best practical usage of AI/Machine Learning at SC Awards Europe 2018.
- Monitoring of public Code Repositories (e.g. GitHub, GitLab) for leaked source code, or for malicious scripts and exploits targeting your organization or abusing its intellectual property.
- Monitoring of Dark Web, including underground marketplaces, hacking forums, IRC channels, Pastebin and social network for credentials theft, compromised systems or stolen data.
- Monitoring of ongoing phishing campaigns, cybersquatting and typosquatting of domain names and social network accounts.
- Monitoring for IoC (Indicator of Compromise) of your digital assets, coming from over 50 public and private threat intelligence feeds.
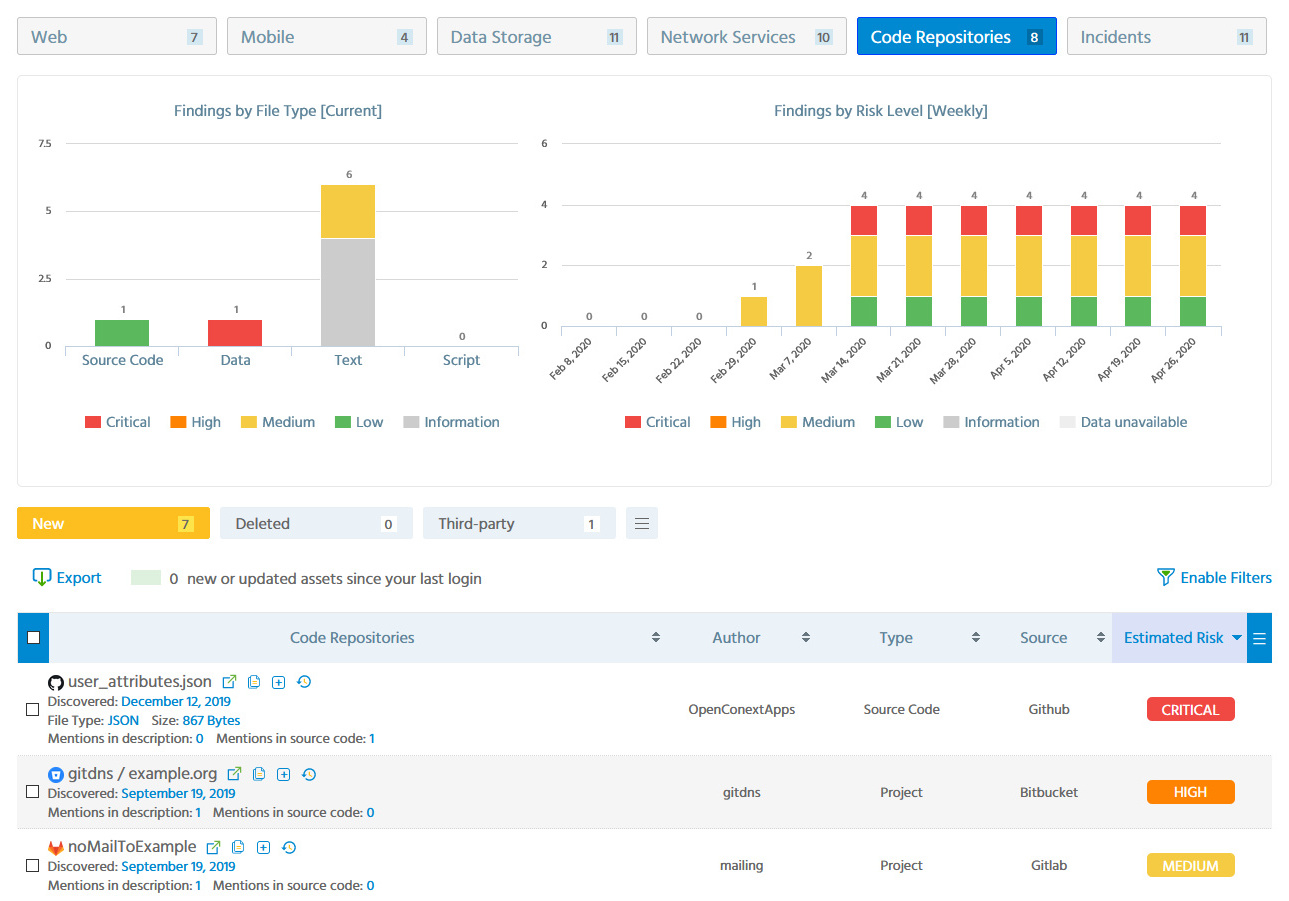
Public Code Repositories Monitoring with ImmuniWeb® Discovery
Ilia Kolochenko, CEO & Founder at ImmuniWeb, says: “Attack Surface Management has become a multidimensional service, it’s not enough anymore just to discover your own assets.
A perfectly secure web application can be easily and invisibly hacked if a supplier with privileged access is breached and its credentials are offered on the Dark Web.
Likewise, if your software developer accidentally exposes the source code of your application on GitHub, all your application security efforts are ruined. Hence, asset discovery has to be augmented with continuous monitoring of Internet resources and the Dark Web to ensure comprehensive, informed and risk-based cybersecurity.
We are grateful to our customers and partners for their valuable feedback and new feature requests. Continuous improvement and relentless innovation are the DNA of ImmuniWeb, we work hard to timely respond to rapidly evolving threat landscape. Even more cool features are coming soon, please stay tuned.”
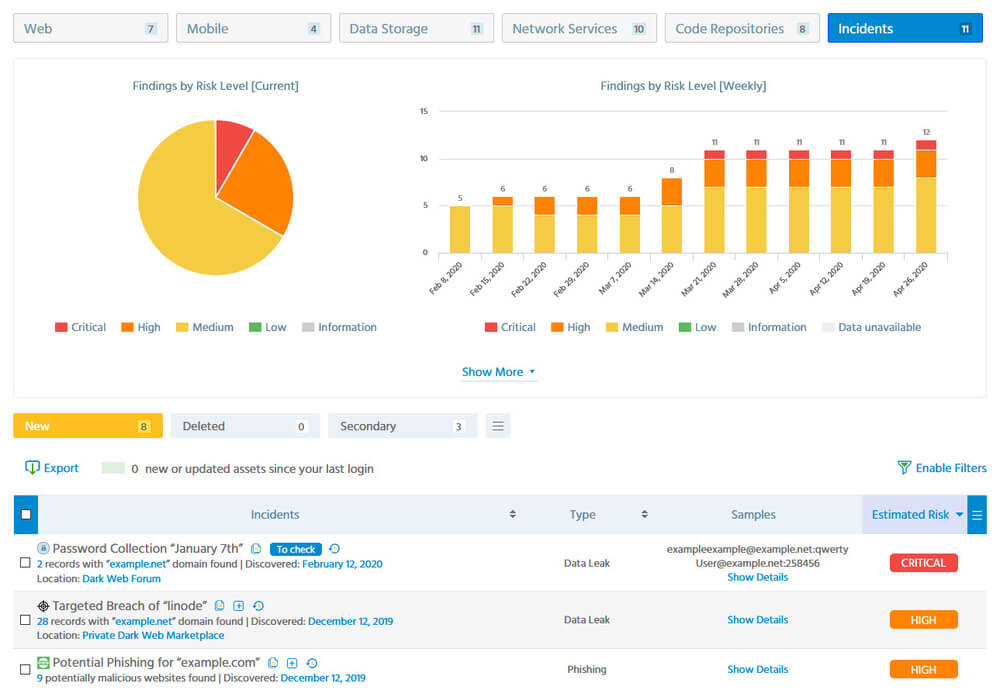
Dark Web and Incidents Monitoring with ImmuniWeb® Discovery
As illustrated above, both Shodan and ImmuniWeb Discovery have their targeted audience. This sustainable co-existence is similar to pentesting tools used by bug bounty hunters or internal auditors, and premium penetration testing services consumed by organizations with mature cybersecurity and risk management programs to expand and intensify their internal testing capacities.
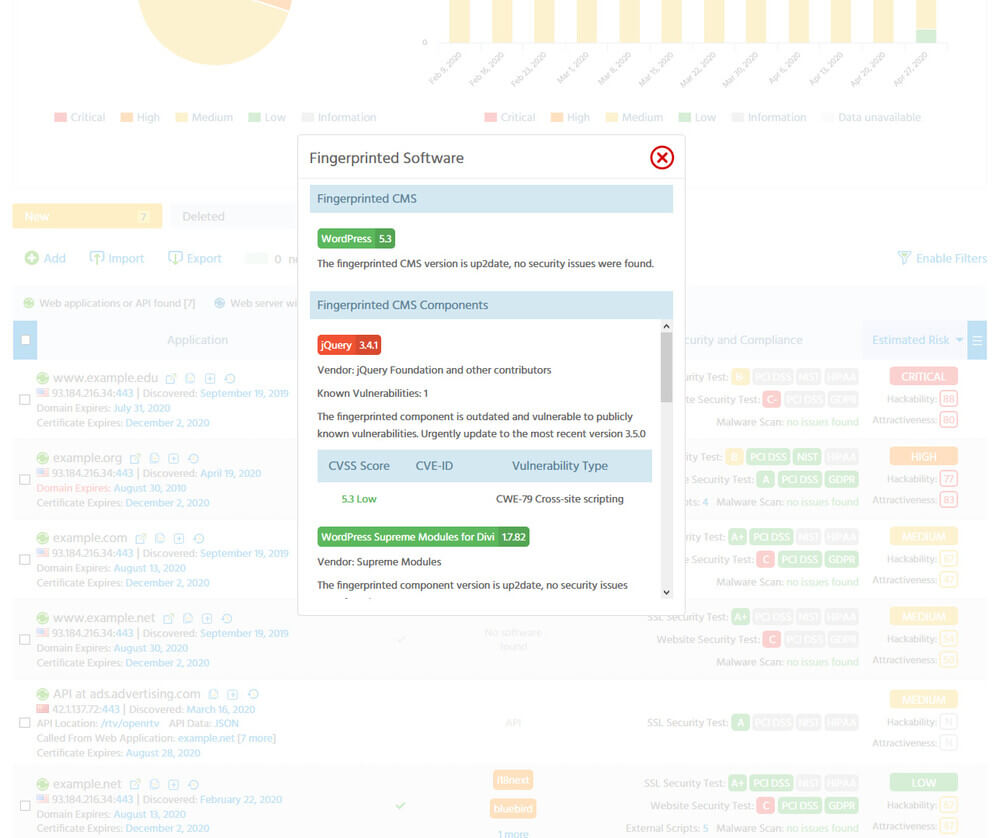
Software Composition Analysis (SCA) with ImmuniWeb® Discovery
Therefore, if your organization currently uses Shodan, it may be a good idea to enhance it with ImmuniWeb Discovery. If you are not yet using any solution to explore your Internet-exposed assets, you may start playing with Shodan as your first step towards asset visibility, and eventually consider upgrading to ImmuniWeb Discovery once you are ready to take your cybersecurity resilience to the next level.
What’s next:
- Follow ImmuniWeb on Twitter and LinkedIn
- Explore Attack Surface Management by ImmuniWeb® Discovery
- Explore DevSecOps-enabled Application Penetration Testing by ImmuniWeb
- Request a demo, quote or special price